BTE exam 2
1/71
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
72 Terms
Artificial intelligence
technology that enables
computers and machines to
simulate human learning,
comprehension, problem solving,
decision making, creativity and
autonomy.
Timeline
1950s: The turing test and early ai, 1956: The Dartmouth Conference, 1960s-70s: symbolic AI and Expert Systems, 1980s: AI winter and neural networks, 1980-1990: Resurgence and machine learning, 2000-2010: AI in everyday life, 2020s: Ethical AI and generative AI
1950s Turing Test
a method that tests a machine's ability to exhibit human-like responses and intelligence. It has popularly been used as a benchmark testing method to assess the development of artificial intelligence (AI) systems.
Expert Systems
A computer program that uses artificial-intelligence methods to solve problems within a specialized domain that ordinarily requires human expertise. The first expert system was developed in 1965 by Edward Feigenbaum and Joshua Lederberg of Stanford University in California, U.S. DENDRAL, as their expert system was later known, was designed to analyze chemical compounds.
Example of Expert Systems
Knowledge Base: Stores medical information, including symptoms, diseases, and treatments. • Inference Engine: Applies rules to analyze user input and generate diagnoses • User Interface: Allows patients to answer questions and receive recommendations. • Takeaway: Simulates a human doctor’s reasoning and advice.
Machine Learning
uses algorithms and models to learn from data and make predictions or decisions without being explicitly programmed for each task.
Machine Learning supervised
trains models on labeled data to predict outputs for new inputs. • Example: Email spam detection. A model is trained on a dataset of emails labeled as “spam” or “not spam.” When a new email arrives, the model uses patterns learned from the labeled data to predict whether it’s spam or not.
machine learning unsupervised
uses unlabeled data to find natural groupings and patterns. • Example: Spotify uses unsupervised learning to group songs into clusters based on audio features (like tempo, rhythm, and genre). These clusters help generate playlists such as “Discover Weekly,” even without explicit user ratings.
Reinforcement learning
learns through interaction and feedback to maximize rewards and minimize penalties. • Example: Self-driving cars use reinforcement learning to navigate roads. The car receives rewards for safe driving actions (staying in the lane, stopping at red lights) and penalties for unsafe ones (swerving, collisions). Over time, the system learns to drive more safely and efficiently.
Zillows $500 million AI mistake
Zillow launched a house-flipping venture called Zillow Offers as part of its iBuying strategy,
intending to use data and algorithms to purchase homes, renovate them, and sell them for
profit.
What went wrong?
• Zillow’s AI-driven model misjudged the housing market during 2021-2022, leading the company
to overestimate home values.
• $500 million loss was incurred as Zillow ended up paying more than the homes were worth,
and it became impossible to sell them at a profit.
the Consequences
• Massive Sell-Off: Zillow had to sell around 7,000 homes at a loss to recoup some of the costs.
• Shutting Down the Program: By November 2021, Zillow completely shut down its home-buying
business, laying off 25% of its workforce.
Deep learning
A subset of Machine Learning that uses artificial neural networks with multiple layers to simulate the complex decision-making processes of the human brain
Applications of deep learning
Image Recognition, Speech Recognition Natural Language Processing (NLP): Autonomous Vehicles
Generative AI
a subset of DL focused on creating new content.
Prompting techniques
Zero-shot: asking the model to complete a task with no prior examples,
One-shot: Providing the model with one example to learn from.
Few-shot: Giving the model multiple examples to learn from.
Role: Assigning a persona to the model to influence its style, tone, and focus.
Prompt chaining: Engaging in a back and forth conversation with the AI.
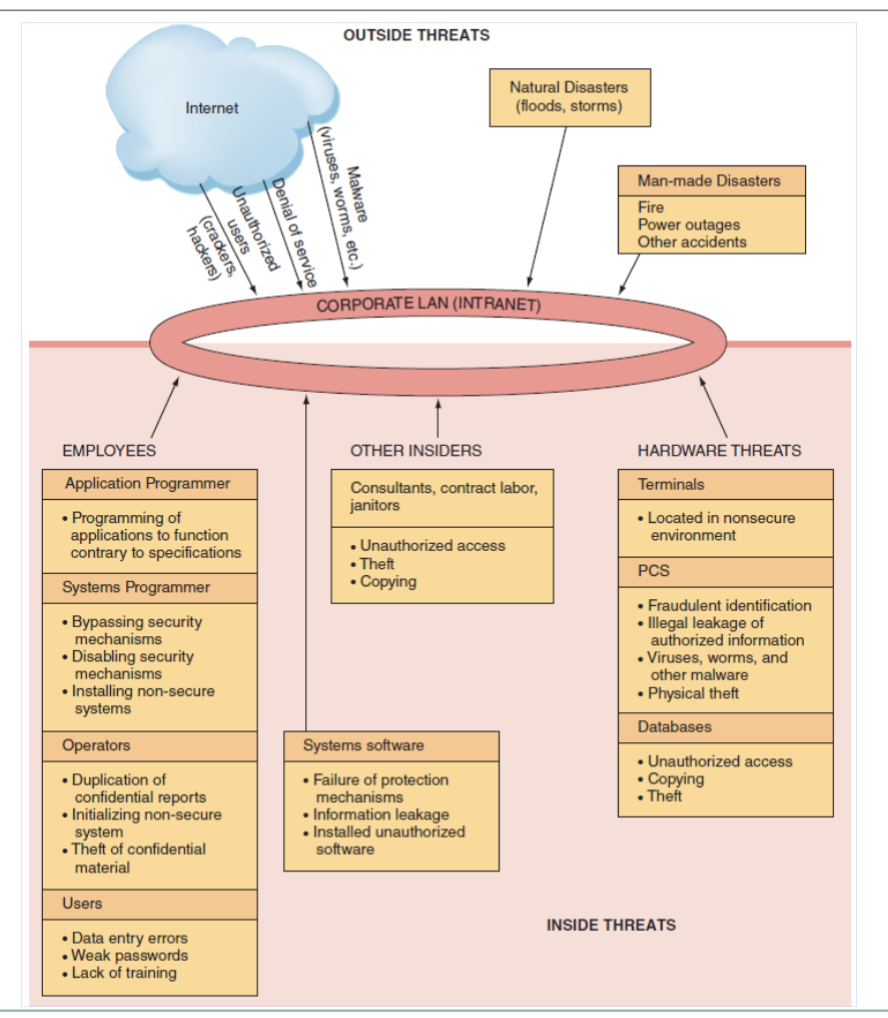
Information security human errors
Higher level employees + greater access privileges = greater
threat
• Two areas pose significant threats
– Human Resources
– Information Systems
• Other areas of threats:
– Contract Labor, consultants, janitors, & guards
Common examples of human errors
Carelessness with laptops
– Losing or misplacing laptops, leaving them in taxis, and so on.
• Carelessness with computing devices
– Losing or misplacing these devices, or using them carelessly so that malware is introduced into an
organization’s network.
• Opening questionable e-mails
– Opening e-mails from someone unknown, or clicking on links embedded in e-mails
• Careless Internet surfing
– Accessing questionable Web sites; can result in malware and/or alien software being introduced into the
organization’s network.
• Poor password selection and use
– Choosing and using weak passwords
Carelessness with one’s office
– Leaving desks and filing cabinets unlocked when employees go home at
night; not logging off the company network when leaving the office for any
extended period of time.
• Carelessness with discarded equipment
– Discarding computer hardware without completely wiping the memory.
• Careless monitoring of environmental hazards
– These hazards, which include dirt, dust, humidity, and static electricity, are
harmful to the operation of computing equipment.
SCADA attack
are used to monitor or to control chemical, physical, and transport processes such as those used in oil refineries, water and sewage treatment plants, electrical generators, and nuclear power plants.
Cyberterrorism and CyberwarfareMalicious
Malicious acts in which attackers use a target’s computer systems, particularly via the Internet, to cause physical, real-world harm or severe disruption, often to carry out a political agenda.
Software Attacks
(Remote Attacks Requiring User Action)
Virus, Worm, Phishing Attack, Spear Phishing Attack
Software Attacks
(Remote Attacks Needing No User Action)
Denial of Service Attack
Distributed Denial of Service Attack
Denial of Service Attack
An attacker sends so many information requests to a target computer system that the target cannot handle them successfully and typically crashes (ceases to function).
Distributed Denial of Service Attack
An attacker first takes over many computers, typically by using malicious soft ware. These computers are called zombies or bots. The attacker uses these bots—which form a botnet—to deliver a coordinated stream of information requests to a target computer, causing it to crash.
Software Attacks
(Attacks by a Programmer Developing a System)
trojan horse, back door, logic bomb
Trojan horse
Software programs that hide in other computer programs and reveal their designed behavior only when they are activated.
Back Door
Typically a password, known only to the attacker, that allows him or her to access a computer system at will, without having to go through any security procedures (also called a trap door).
Logic Bomb
A segment of computer code that is embedded within an organization’s existing computer programs and is designed to activate and perform a destructive action at a certain time or date.
Outside threats diagram
Defense mechanism diagram
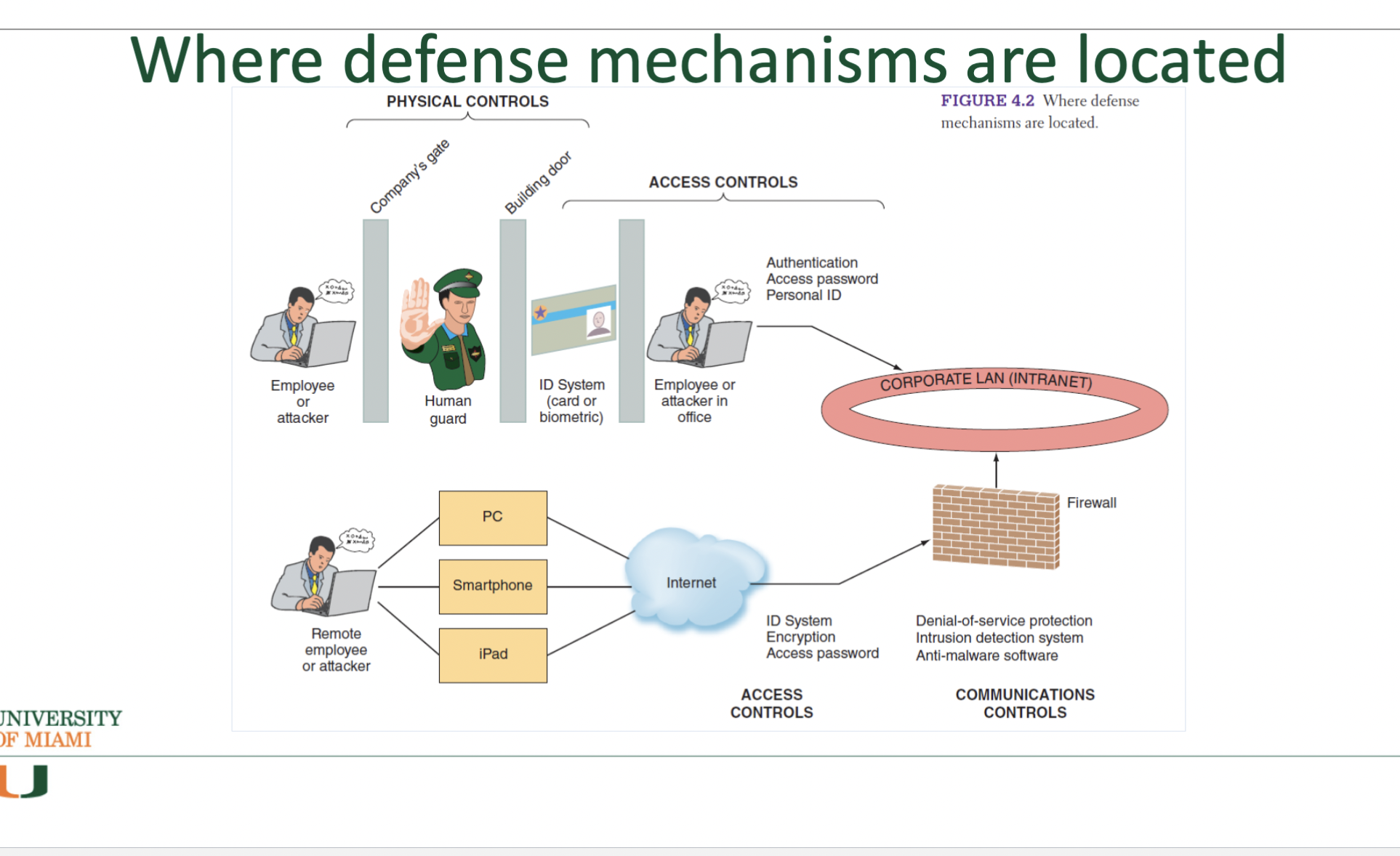
Acess controls slide 1
(restrict unauthorized individuals from using information resources and involve two major
functions: authentication and authorization
• Authentication (confirms the identity of the person requiring access)
– Something the user is
– Something the user has
– Something the user does
•– Something the user knows
Access controls slide 2
restrict unauthorized individuals from using information resources and involve two major
functions: authentication and authorization. Firewalls, Anti-malware Systems, Encryption.
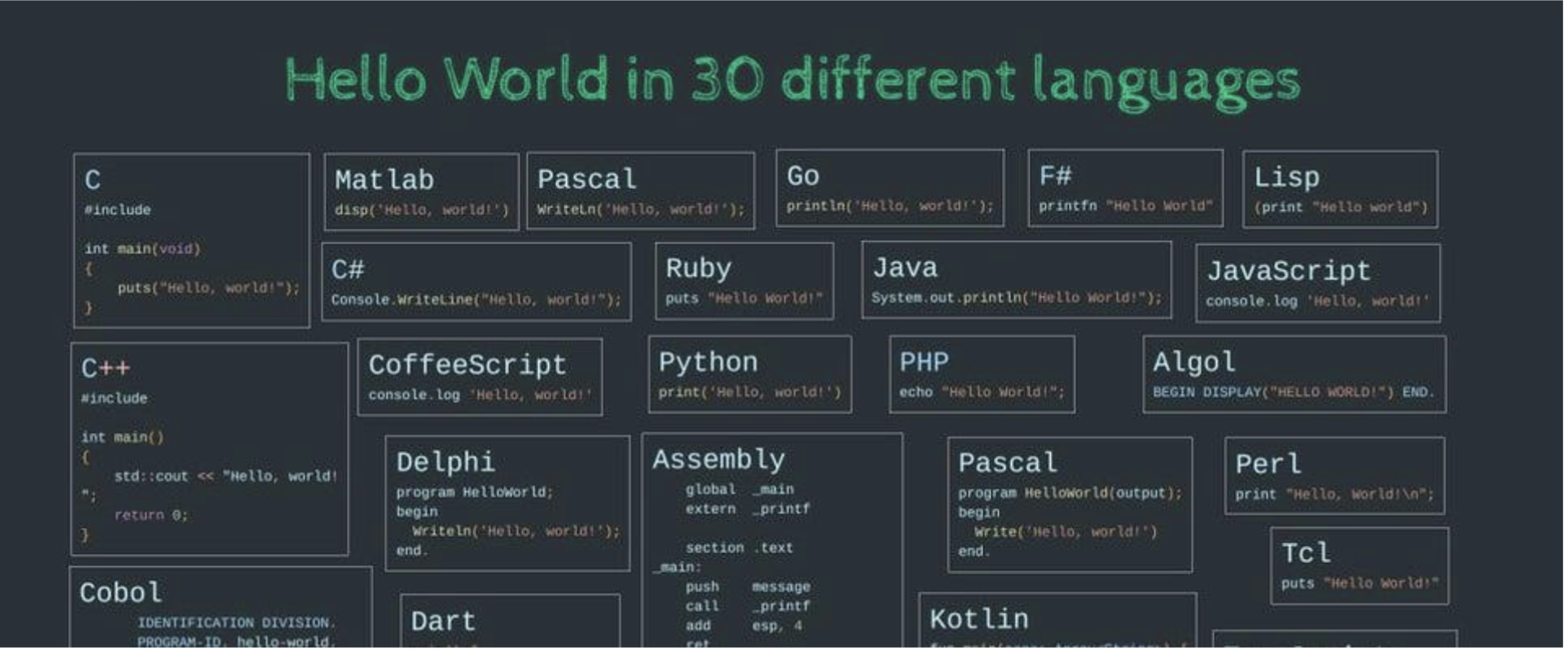
Programming language
is a computer language engineered to create a standard form of commands. – These commands can be interpreted into a code understood by a machine.
Syntax
Programming in C++
IDEs are very user friendly
• Compiler identifies the syntax errors and also suggests how to correct
them
• Build or Rebuild is a simple command that links the object code with the
resources used from the IDE
Design an algorithm to find the perimeter and area of a rectangle
✓ The perimeter and area of the rectangle are given by the following formulas:
perimeter = 2 * (length + width)
area = length * width
Logic flow for execution
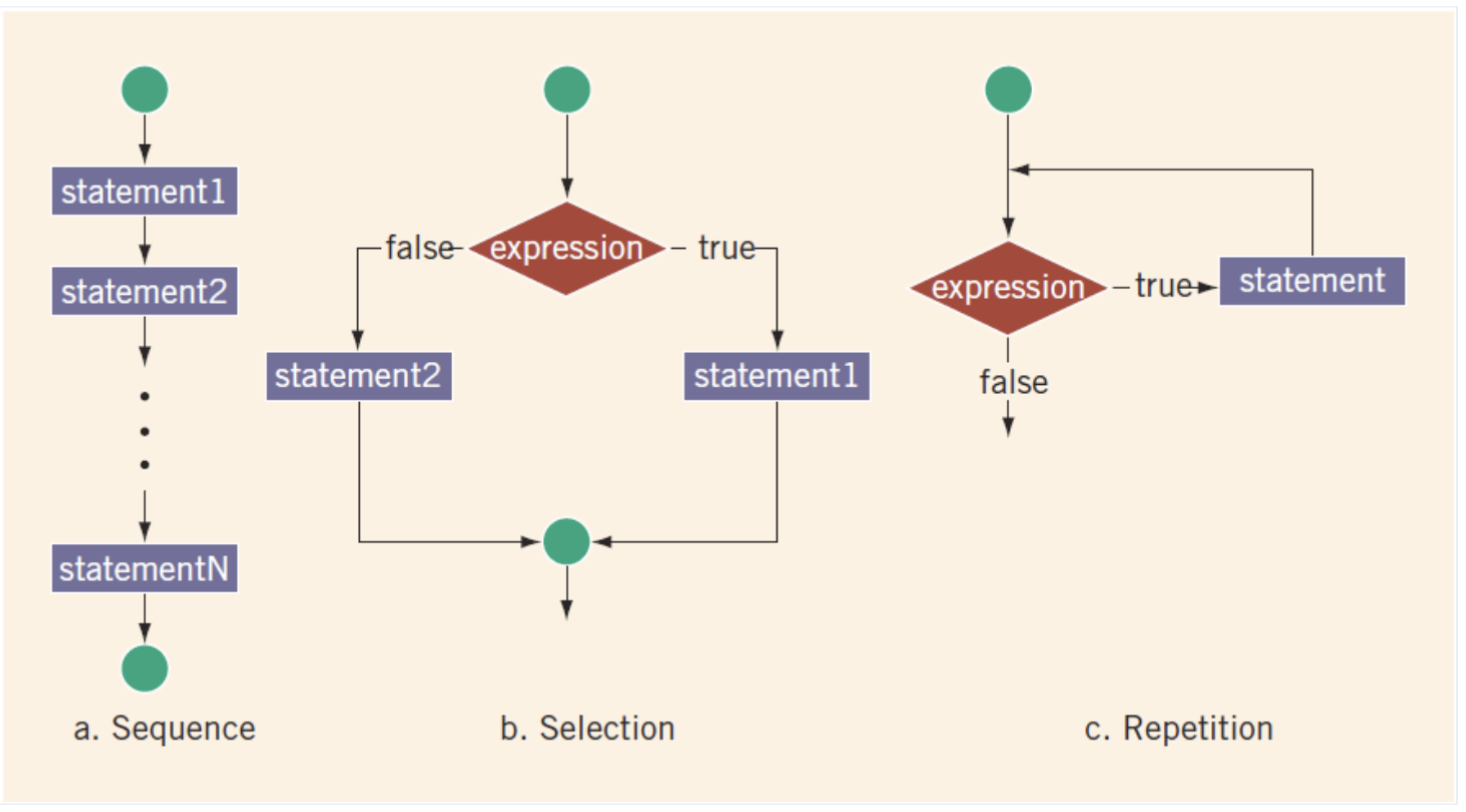
Flowchart symbols
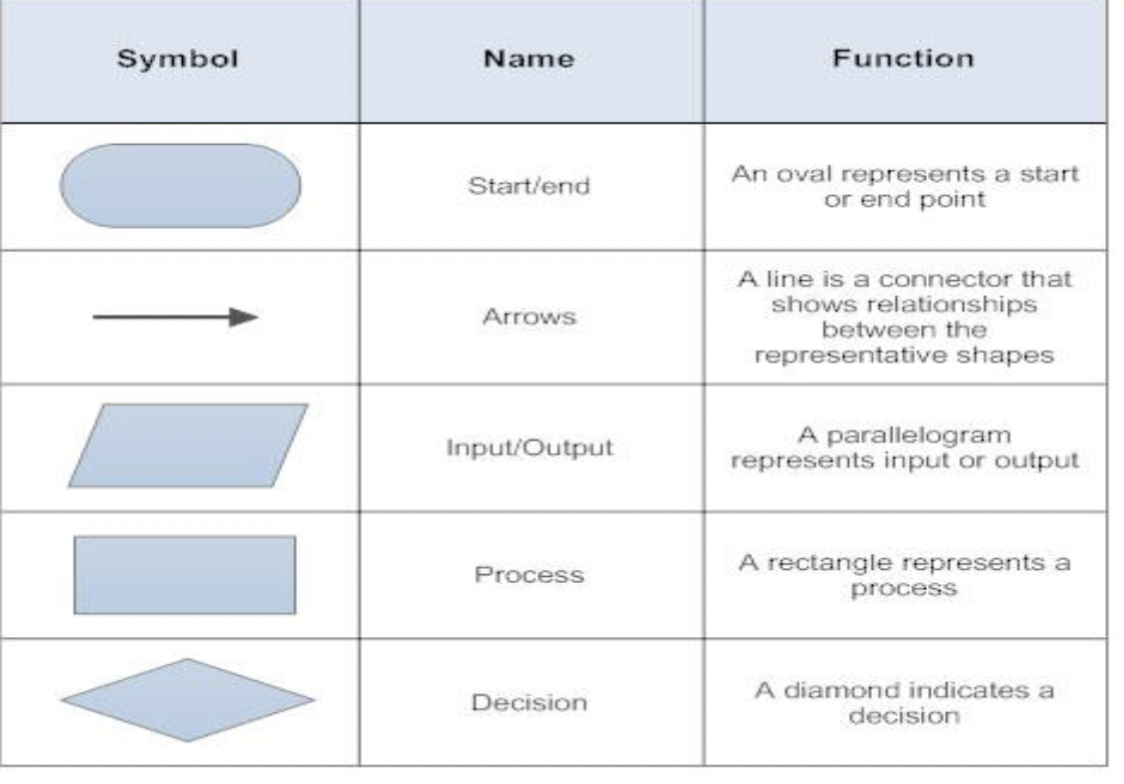
Image Recognition
Used in applications like facial recognition and medical imaging.
Speech Recognition
Powers virtual assistants like Siri and Alexa.
Natural Language Processing (NLP)
NLP enables computers to understand and interpret human language, both written and spoken (chatbots, language translations, sentiment analysis)
Autonomous Vehicles
Helps in navigation and decision-making for self-driving cars.
Oval
represents a start or end point
line
a connector that shows relationships between the representative shapes
parallelogram
represents input or output
rectangle
represents a process
Diamond
indicates a decision
Something the user is
also known as biometrics, examines a person’s innate physical characteristics (e.g., fingerprint
scans, palm scans, retina scans, iris recognition, and facial recognition).
Something the user has
regular identification (ID) cards, smart ID cards, and tokens.
Something the user does
includes voice and signature recognition.
– Something the user knows
• includes passwords and passphrases
Virus
Segment of computer code that performs malicious actions by attaching to another computer program.
Worm
Segment of computer code that performs malicious actions and will replicate, or spread, by itself (without requiring another computer program).
Phishing Attack
use deception to acquire sensitive personal information by masquerading as official- looking e-mails or instant messages.
Spear Phishing attack
the perpetrators find out as much information about an individual as possible to improve their chances that phishing techniques will obtain sensitive, personal information.
Firewalls
a system that prevents a specific type of information from moving between untrusted networks, such as the Internet, and private networks, such as your company’s network.
Anti-malware Systems
software packages that attempt to identify and eliminate viruses and worms, and other malicious software.
Encryption
the process of converting an original message into a form that cannot be read by anyone except the intended receiver.
OpenClaw
open-source personal AI agent that interacts with tools and software • Capabilities: Autonomous multi-step task execution, Uses tools (browser, APIs, applications), Reasoning Loop (Observe -> think -> act). Example: Plans a trip, books flights and sends you the itinerary
Cryptography
converts data into a format that is unreadable for an unauthorized user, allowing it to be transmitted without unauthorized entities decoding it back into a readable format
Cryptocurrency
is a digital currency that uses cryptography for security measures.
BLOCKCHAIN
A methodology • Identity of members is known • Permissioned network • Transactions are secret or Permission viewing • Virtual Signing • Handles many types of assets • Selective endorsement
BITCOIN
A blockchain application • Anonymity is important • Anyone can participate • Transactions are viewable by all members of the network • Based on Public-Private Keys • A cryptocurrency • Based on Proof of Work
“The chasm”
a gap between visionary early adopters and the pragmatic majority. Crossing the chasm requires securing a specific niche.
Gartner Hype Cycle
Separate hype from the real drivers of a technology's commercial promise. Helps get educated on an emerging technology within the context of the industry and individual appetite for risk
Innovation Trigger (GHC)
A potential technology breakthrough kicks things off. Early proof-of-concept stories and media interest trigger significant publicity. Often no usable products exist, and commercial viability is unproven.
Peak of Inflated Expectations (GHC)
Early publicity produces several success stories — often accompanied by scores of failures. Some companies take action; many do not.
Trough of Disillusionment (GHC)
Interest wanes as experiments and implementations fail to deliver. Producers of the technology shake out or fail. Investments continue only if the surviving providers improve their products to the satisfaction of early adopters.
Slope of Enlightenment (GHC)
More instances of how that technology can benefit the enterprise start to crystallize and become more widely understood. Second- and third-generation products appear from technology providers. More enterprises fund pilots; conservative companies remain cautious.
Plateau of Productivity (GHC)
Mainstream adoption starts to take off. Criteria for assessing provider viability are more clearly defined. The technology's broad market applicability and relevance are clearly paying off.
Magic Quadrant
Provides a competitive graphical positioning of four types of technology providers in markets where growth is high, and provider differentiation is distinct
Leaders (MQ)
execute well against their current vision and are well-positioned for tomorrow.
Visionaries (MQ)
understand where the market is going or have a vision for changing market rules but do not yet execute well.
Niche Players (MQ)
focus successfully on a small segment or are unfocused and do not out-innovate or outperform others.
Challengers
execute well today or may dominate a large segment but do not demonstrate an understanding of market direction.