Chapter 8 - Securing Information Systems
1/63
Earn XP
Description and Tags
made to slide 35
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
64 Terms
What is Security?
Policies, procedures, and technical measures used to prevent unauthorized access, alteration, theft, or physical damage to information systems
What is Controls?
Methods, policies, and organizational procedures that ensure safety of organization’s assets; accuracy and reliability of its accounting records; and operational adherence to management standards
What is Internet Vulerabilities?
Network open to anyone, size means abuses can have wide impact; corporate networks linked to Internet more vulnerable; E-mail, IM, and P2P increase vulnerability
How can Email open you to internet vulnerabilities?
attachments with malicious software; can be used to transmit trade secrets, confidential data
How can IM open you to internet vulnerabilities?
back door into a secure network
How can P2P open you to internet vulnerabilities?
can transmit malicious software, expose corporate data
What does “malware” stand for?
Malicious software designed to damage, disrupt, or gain unauthorized access to systems
What is a computer virus?
A type of malware that attaches to a host file/program and spreads when the host is executed
How do viruses typically spread?
Through infected files, downloads, email attachments, and removable media
What is a worm?
Self‑replicating malware that spreads across networks without needing a host file
Key difference between a virus and a worm?
Viruses require a host file; worms spread independently
What is a “drive‑by download”?
Malware installed automatically when a user visits a compromised website
How do downloads spread malware?
Users install infected software or files, often unknowingly
Why are email attachments a common malware vector?
Users often trust familiar senders and open attachments without verifying authenticity
What makes mobile devices vulnerable to malware?
App store sideloading, insecure Wi‑Fi, outdated OS versions, and social engineering
How does malware spread on social networks?
Through malicious links, fake profiles, compromised accounts, and clickbait posts
How are Employees Internal Threats?
Security threats often originate inside an organization; inside knowledge; sloppy security procedures; social engineering; both end users and information systems specialists are sources of risk
What causes software vulnerabilities in commercial software?
Bugs and flaws in program code; zero‑defect software is impossible, so defects can create openings for attackers
What is a zero‑day vulnerability?
A software flaw unknown to the vendor, exploited by attackers before a patch is available
How are software vulnerabilities addressed?
Through patches and patch management; however, even hardware (e.g., microprocessors) can have vulnerabilities like Spectre and Meltdown
What are HIPAA?
Medical security and privacy rules and procedures
What is the Gramm-Leach-Bliley Act?
Requires financial institutions to ensure the security and confidentiality of customer data
What is the Sarbanes-Oxley Act?
Imposes responsibility on companies and their management to safeguard the accuracy and integrity of financial information that is used internally and released externally
What is Electronic evidence?
Evidence for white collar crimes often in digital form; proper control of data can save time and money when responding to legal discovery request
What is Computer forensics?
Scientific collection, examination, authentication, preservation, and analysis of data from computer storage media for use as evidence in court of law; recovery of ambient data
What are general controls in Information Systems Controls?
Govern design, security, and use of computer programs and security of data files in general throughout organization
What are application controls in Information Systems Controls?
Controls unique to each computerized application; Input controls, processing controls, output controls
What is Risk Assessment?
Determines the level of risk to firm if specific activity or process is not properly controlled
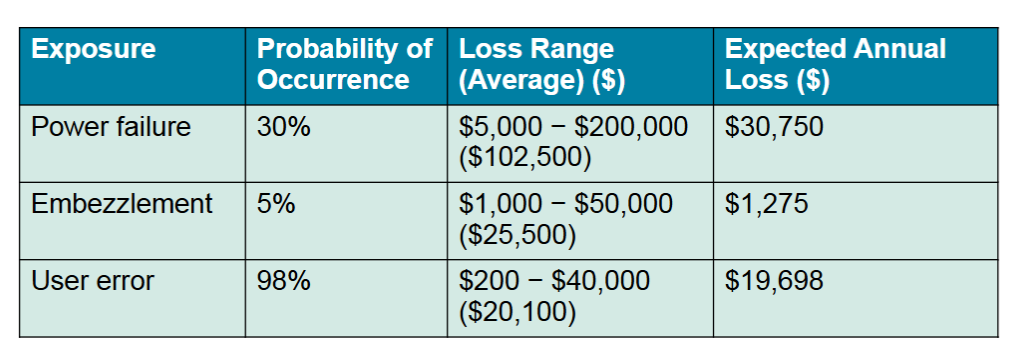
What does this image represent?
Online Order Processing Risk Assessment
What is Security Policy?
Ranks information risks, identifies security goals and mechanisms for achieving these goals; drives other policies
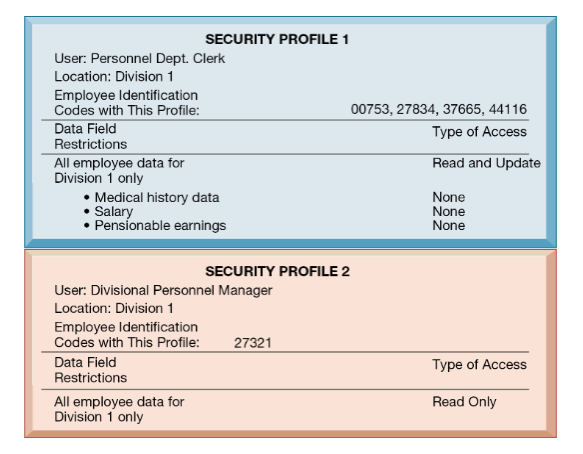
What does this image represent?
Access Rules for a Personnel System
What is Disaster recovery planning?
Devises plans for restoration of disrupted services
What is Business continuity planning?
Focuses on restoring business operations after disaster
What do both disaster recovery and business continuity planning need to do?
Need to identify firm’s most critical systems - business impact analysis to determine impact of an outage; management must determine which systems restored first
What are information systems audits?
Examines firm’s overall security environment as well as controls governing individual information systems
What are security audits?
Review technologies, procedures, documentation, training, and personnel; may even simulate disaster to test responses
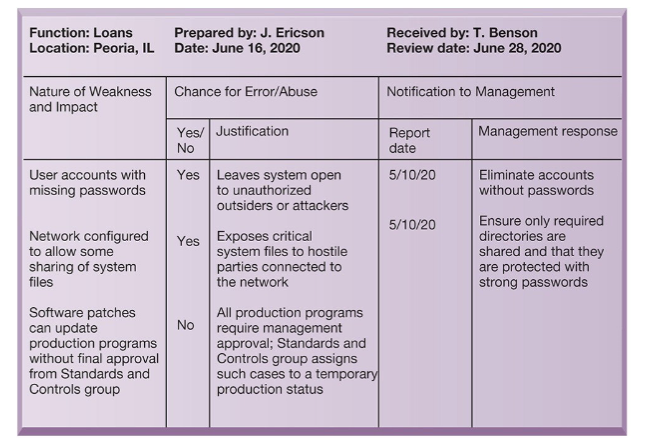
What does this image represent?
Sample Auditor’s List of Control Weaknesses
What are some examples of Tools and Technologies for Safeguarding Information Systems?
Identity management software; Authentication; Firewall; Intrusion detection system; antimalware and antispyware software; unified threat management (UTM) systems
What is Identity management software?
Automates keeping track of all users and privileges; Authenticates users, protecting identities, controlling access
What is authentication?
Password systems; Tokens; Smart cards; Biometric authentication; TFA
What is a firewall?
Combination of hardware and software that prevents unauthorized users from accessing private networks
What is packet filtering?
Packet filtering is a network security technique used by routers and firewalls to control traffic by examining packet header information (source/destination IP, ports, protocol, direction) and allowing or blocking packets based on predefined rules
What is an intrusion detection system?
Monitors hot spots on corporate networks to detect and deter intruders
What is antimalware and antispyware software?
Checks computers for presence of malware and can often eliminate it as well; requires continual updating