Identity and Access Management - CompTIA Security+ SY0-701 - 4.6
1/14
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
15 Terms
Identity and Access Management (IAM)
Application are available anywhere
- Desktop, browser, mobile device, etc
Data can be located anywhere
- Cloud storage, private data centers, etc
Many different application users
- Employees, vendors, contractors, customers
Give the right permissions to the right people at the right time
- Prevent unauthorized access
Identity and Access Management Cont
Identity lifecycle management
- Every entity (human and non-human) gets a digital identity
Access control
- An entity only gets access to what they need
Authentication and authorization
- Entities must prove they are who they claim to be
Identity governance
- Track an entity's resource access
- May be a regulatory requirement
Provisionsing/de-provisioning user accounts
The user account creation process
- And the account removal process
Provisioning and de-provisioning occurs for certain events
- Hiring, transfers, promotions, job separation
Account details
- Name, attributes, group permissions, other permissions
An important part of the IAM process
- An initial checkpoint to limit access
- Nobody gets Administrator access
Permission assignments
Each entity gets limited permissions
- Just enough to do their job
- Group assignments are common
Storage and files can be private to that user
- Even if another person is using the same computer
No privileged access to the operating system
- Specifically not allowed on a user account
Identity Proofing
• I could be anyone
- The IAM process should confirm who I am
• Resolution
- Who the system thinks you are
• Validation
- Gathering information from the user
(password, security questions, etc.)
• Verification / Attestation
- Passport, in-person meeting, etc.
- Automated verification is also an option
Gaining access
Single Sign On (SSO)
• Provide credentials one time
- Get access to all available or assigned resources
- No additional authentication required
• Usually limited by time
- A single authentication can work for 24 hours
- Authenticate again after the timer expires
• The underlying authentication infrastructure must
support SSO
- Not always an option
LDAP (Lightweight Directory Access Protocol)
Protocol for reading and writing directories
• An organized set of records, like a phone directory
• X.500 specification was written by the International
Telecommunications Union (ITU)
• DAP ran on the OSI protocol stack
• LDAP is lightweight, and uses TCP/IP (tcp/389 and
udp/389)
• LDAP is the protocol used to query and update an
X.500 directory
• Used in Windows Active Directory, Apple
OpenDirectory, Novell eDirectory, etc.
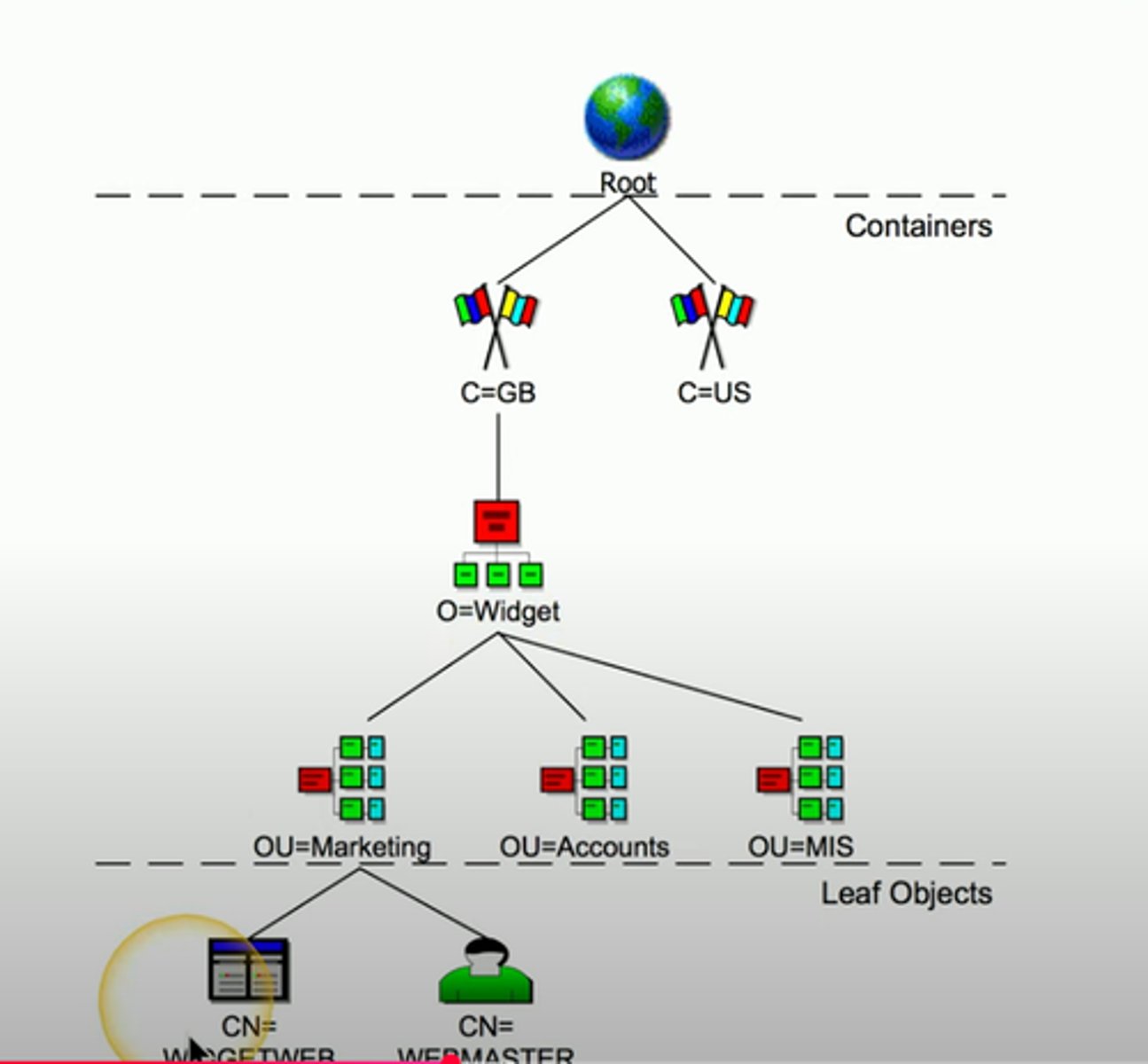
X.500 Distinguished Names
Attribute= Value Pairs
Most specific attribute is listed first
- This may be similar to the way you already think
CN=WIDGETWEB, OU= Marketing, O=Widget, L=London, ST= London, C= GB, DC = Widget, DC=com
X.500 Directory Information Tree
Hierarchical Structure
- Builds a tree
Container objects
- Country, organizaiton, organizational units
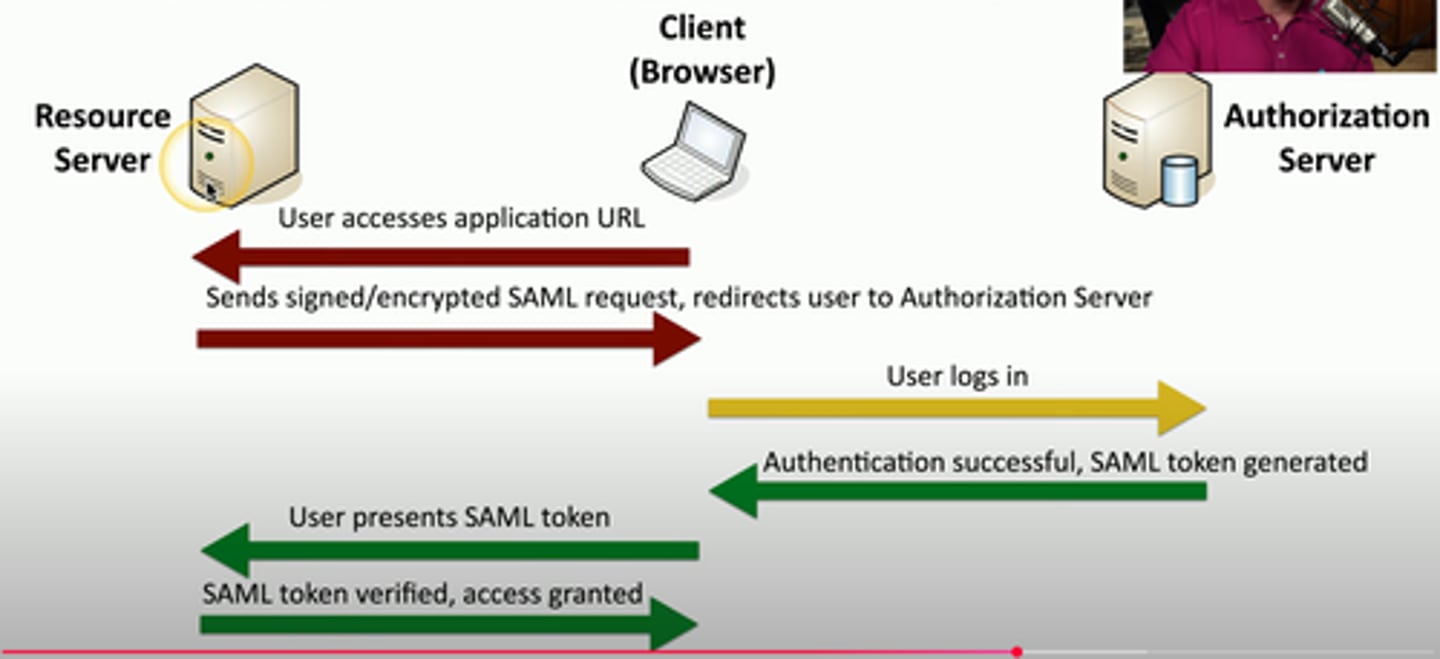
Security Assertion Markup Language (SAML)
Open standard for authentication and authorization
- You can authenticate through a 3rd party to gain access
- One standard does it all, sort of
Not originally designed for mobile apps
- This has been SAML's largest roadblock
The SAML authentication flow
Identity provider (idp) = provides authentication
Sp = service provider for user/principal.
Rp = relying party leverages idp to provide authentication services
OAuth
Authorization framework
- Determines what resources a user will be able to access
Created by Twitter, Google, and many others
- Significant industry support
Not an authentication protocol
- OpenID Connect handles the single sign-on authentication
- OAuth provides authroization between applications
Federation
Provide network access to others
- Not just employees - Partners, suppliers, customers, etc
- Provides SSO and more
3rd party can establish a federated network
- Authenticate and authorize between the two organizations
- Login with your Facebook credentials
The 3rd party must establish a trust relationship
- And the degree of the trust
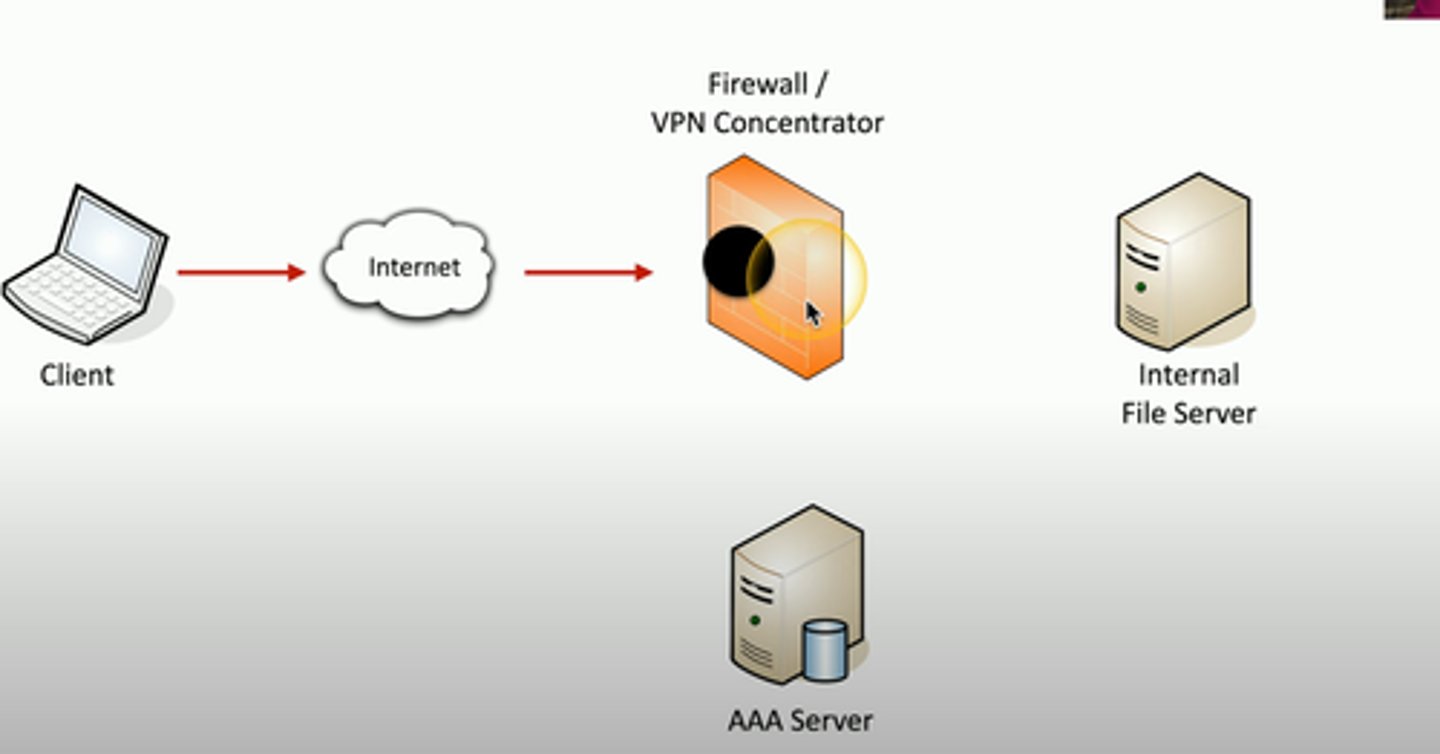
Interoperability
Many different ways to communicate with an authentication server
- More than a simple login process
Often determined by what is at hand
- VPN concentrator can talk to a LDAP server
- We have an LDAP server
A new app uses OAuth
- Need to allow authentication API access
The ineroperability is dependent on the environment