IGCSE Computer Science C2
1/30
Earn XP
Description and Tags
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
31 Terms
Describe the structure of a data packet.
1) header (IP addresses, packet number, size),
Consists of:
IP addresses of sender and receiver
Packet number
Sequence number of the packet (for correct reassembly at destination)
Size of packet (ensures receiving data has received all data)
2) payload (actual data),
Consists of:
The actual data being sent in the packet
3) trailer (end-of-packet marker and error check)
.Consists of:
Method of identifying end of packet (allows each packet to be separated as they travel from sending to receiving station)
An error checking method
Describe the process of packet switching.
Data is broken down into packets to be transmitted
Each packet takes its own route
A router controls the route a packet takes (using destination IP address in header)
Router selects the shortest path available
Packets may arrive out of order at destination
Once the last packet has arrived, packets are reordered (using packet number in header)
If packet is missing/corrupted, it is requested
Describe how data is transmitted between devices.
Data is transmitted over wired or wireless media using:
serial or parallel methods and
simplex, half-duplex, or full-duplex directions.
Explain simplex transmission with an example.
Data flows in one direction only (e.g., computer to printer).
Explain half-duplex transmission with an example.
Data flows both ways, but NOT at the same time
(e.g., walkie-talkie).
Explain full-duplex transmission with an example.
Data flows both ways simultaneously
(e.g., broadband connection).
Describe serial data transmission.
Better for long distances (telephone lines) |
Cheaper option |
Used when size of data transmitted is small |
Slower option |
Easier to synchronise as there is only one data stream |
Describe parallel data transmission.
Better for short distances (internal circuits) |
Expensive (more hardware required) |
Used when speed is necessary |
Faster than serial |
Asynchronous due to skew between bits |
Explain the advantages of serial transmission.
Reliable over long distances
Less interference
Cheaper
Fewer errors.
Explain the disadvantages of parallel transmission.
Prone to interference
Only used over short distances
Skew between bits.
Describe the role of USB in data transmission.
Universal serial bus (USB)
A form of serial data transmission
Widely used standard for transmitting data between devices
Operates asynchronously
Most common type of input/output port found on computers
Allows both half- duplex and full- duplex data transmission
e.g. of devices that use USB: Keyboards, mice, video cameras, printers, phones...
State two benefits of USB.
Has become an industry standard |
Can support different transmission rates |
No need for external power source |
Notifies transmitter to re transmit data if any errors have occurred |
State one drawback of USB.
Limited to 5m cables
Older versions may not be supported
Slower than Ethernet.
Explain the need to check for errors during data transmission.
Data may become corrupted, lost, or changed due to interference
Describe how a parity check works.
Can be even or odd
Checks whether data has been changed or corrupted
Based on number of 1-bits in a byte of data
Sender and receiver must agree before transmission whether they are using odd or even parity
Number of 1s are counted
If parity is incorrect, error is detected
Describe how a checksum is used.
Determines if data has been corrupted or altered
Transmitted with the data
Value is recalculated after transmission
Values are compared after transmission to check for errors
Describe how an echo check works.
Involves transmitting the received data back to the sender
Sender checks the data to see if any errors occurred during transmission
This method isn’t reliable as an error could have occurred when the sender transmits the data or when the receiver transmits the data
If an error does occur the sender will retransmit the data
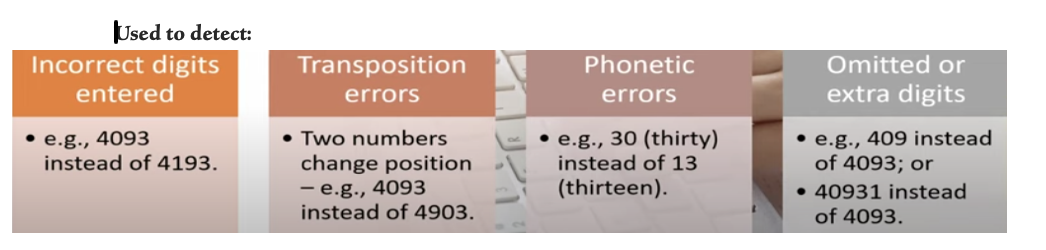
Describe how a check digit is used.
The last digit included in a code or other identification number
Commonly caused by mistyping and scanning errors
Calculated from all the other digits in the code
Digit is added to the data
2 common types of methods: ISBN 13 and MODULO 11
Commonly used with:
International standard book numbers (ISBN)
Bar codes
Vehicle Identification numbers (VIN)
Describe how ARQ (Automatic Repeat Request) works.
A protocol that notifies the sender that an error has occurred and that the data received in incorrect
Once data is sent, a timer is started
It works as follows:
Sender sends a block of data
Receiving computer then sends back an acknowledgement
When sender receives acknowledgement, it sends another block of data
Error detected --> receiver sends a negative acknowledgement transmission to indicate the data is corrupted
No error detected --> receiver sends a positive acknowledgement transmission meaning the data is correct
Receiver does not send any acknowledgement transmission --> timeout occurs sender waits before automatically resending the data
This process is continuous until all data has been received and acknowledged correctly
Explain the purpose of encryption.
A method of scrambling data before being transmitted across a network
Helps to protect the contents from unauthorised access by making data meaningless
Important on both wired and wireless networks, more critical on wireless networks (data transmitted over radio waves --> easy to intercept)
Encrypted using encryption algorithm and a key
Key used to decrypt cypher text and transmitted separately
Define plaintext and ciphertext.
Plaintext is the original readable data (name for data before it is encrypted ).
Ciphertext is the encrypted version that looks meaningless without a key (name for data after it is encrypted).
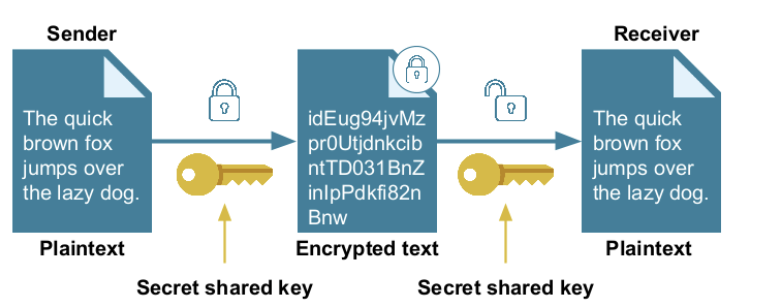
Describe how symmetric encryption works.
Uses an encryption key.
The same key is used to encrypt and decrypt the encoded message.
One method is called the Caesar Cipher.
If a hacker gains access to the key, then they can decrypt intercepted information
The secret key can be shared with the receiver without sending it electronically
Process:
Plain text is encrypted into cypher text using the encryption key.
The encryption key and the cypher text are sent separately to the receiver.
At the receiver, the encryption key is used to decrypt the cypher text into plain text.
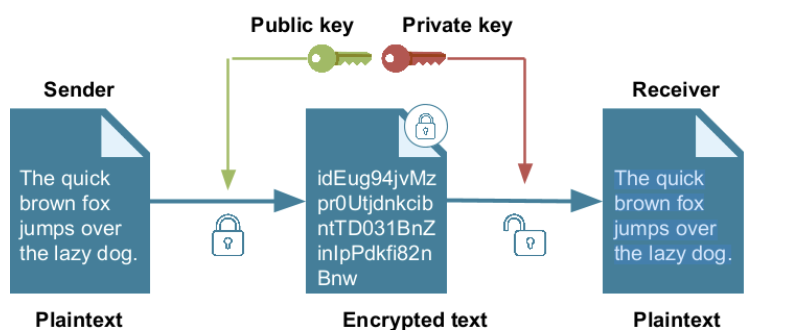
Describe how asymmetric encryption works.
1. When a message is ciphered ready for transmission by a sender, the receiver will generate a pair of keys, a public key and a private key.
2. The public key is shared with any device that might wish to send a message to the receiver.
3. The sender will then use the receiver’s public key to encrypt the message the message.
4. When the receiving device obtains the message, it then has to use the private key to decipher the message.
Compare symmetric and asymmetric encryption.
Symmetric: Fast, simple, but less secure (same key used).
Asymmetric: Slower, more secure (uses public/private key pair), harder to compromise.
Explain one advantage of packet switching.
It uses multiple routes for transmission, reducing network congestion and making efficient use of bandwidth.
Explain why packet switching might cause delays.
Packets may arrive out of order and require reassembly; missing or corrupted packets must be re-requested, causing delay.
State one advantage of full-duplex transmission over half-duplex.
Full-duplex allows data to be sent and received simultaneously, increasing efficiency and speed.
Explain why parallel transmission is only suitable over short distances.
Bits sent simultaneously over multiple wires can arrive at different times (bit skew), causing errors over long distances.
Explain why ARQ is useful in data transmission.
ARQ uses acknowledgements and timeouts to ensure that data is correctly received; if no response is received, the data is automatically resent.
Explain how asymmetric encryption improves security.
The public key encrypts the data, but only the private key can decrypt it, ensuring that only the intended recipient can read the message
Explain the differences between public and private keys
Public key | Private key |
Both created by receiver | |
Different but mathematically related | |
Accessible by anyone | Kept secret by receiver |
Used to encrypt data | Used to decrypt data |
Cannot be used to decrypt a message | Never shared |