2.8 Data security and integrity processes
1/70
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
71 Terms
What is the CIA triad?
Confidentiality, Integrity, and Availability of data which describe the key main aspects of security and integrity of data.
Data Confidentiality
Ensures that data is only accessible to authorised individuals (Protected by encryption, access controls, and authentication)
Data Integrity
Ensures data remains accurate, complete, and consistent. (Protected by validation, version control, hashing, and checksums)
Data availability
Ensures systems and data are accessible when needed. (Protected by backups, and disaster recovery management)
What are the CIA problems that can arise during the online updating of files?
Concurrent access (two users edit leading to data incosistency as one is overwritten) lead to data mismatch
Unauthroised acess
Partial updates due to system failure (power cuts lead to incomplete transactions)
Malware altering records (Viruses or ransomeware)
Data interception (man in the middle)
Deletion of files (accidental or deliberate)
Data corruption
What are some key file integrity issues?
Concurrent access
Lost and partial updates of files
Data corruption
What are key security riks for data
Unauthorised access, mainpulation, reading, or copying files
File corruption
Deletion of files
What is an external Risk to data?
Risks from users outiside of the company
Social engineering
Natural disasters
Phishing
DDos attacks
Malware
Man in the middle attacks
What are internal risks?
Risks from inside the company such as:
Employee error
Disgruntled employees
What are technical risks?
Risks to the systems techical aspect such as:
Hardware failure
Power outages
Software bugs
Network failure
Disk corruption
What is malicious damage?
Deliberate action intended to harm, steal, or disrupt data. Such as:
Malware altering data
Insiders deliberately deleting records (like a disgruntled employee)
DDoS attack
Data theft from phishing or spyware
What is accidental damage?
Unintentional actions that can result in data loss, corruption, or inaccessibility. such as:
Employee overwirting a file
Power failure
Software bugs
Misconfigured backups
What would be some causes of accidental damage?
Lack of staff training
Accidental deletion
Fatigue/stress (overworked staff)
Faulty hardware
Natural disasters (fires etc)
Overwriting data
What are some motives for hackiong into a system?
Criminal motives (Finacial gain, sabotage, revenge)
Personal motive (Vendetta against a company)
Political (Espionage (to gain sensitive intelligence))
Dangers that can arise from the use of computers to manage personal data files.
Data Breaches: Unauthorized access to personal data files can lead to significant data breaches, where sensitive information is exposed to malicious actors. This can result in identity theft, financial loss, and other forms of exploitation.
Malware and Ransomware: Computers managing personal data are susceptible to malware and ransomware attacks, which can corrupt, steal, or lock access to data until a ransom is paid.
Insider Threats: Employees or individuals with access to data files may misuse their privileges to steal or manipulate personal data for personal gain or malicious intent.
Breaches of personal data can lead to a loss of trust between individuals and organizations, damaging reputations and customer relationships.
Accidental deletion, hardware failures, or other technical issues can result in the permanent loss of personal data, affecting individuals' records and histories.
Errors in data entry, processing, or storage can lead to significant issues for individuals and organizations.
Personal data can be shared without the consent of the individuals involved, leading to violations of privacy and potentially damaging consequences.
What are some protections we can use to protect data agains mailcious or accidental damage?
Access rights
Recovery procedures
Required strong passwords
Antivirus
Clear instructions
Staff training on scams and malware
Confirmation for deleting files
Backups
Data entry validation
Contemporary processes that protect the security and integrity of data for Levels of Permitted Access
Role-Based Access Control (RBAC): Assigning permissions based on the user's role within the organization. Users are granted access only to the data necessary for their job functions.
Principle of Least Privilege (PoLP): Ensuring users have the minimum level of access needed to perform their duties, reduces the risk of accidental or intentional data misuse.
Access Control Lists (ACLs): Defining which users or system processes are granted access to objects, as well as what operations are allowed on given objects.
What are some standard clerical procedures to protect data
Things that an organisations employees should do to protect data such as:
Clean desk policy
Secure storage
Visitor control (control their access)
Staff training
Data minimisation (only collect necessary data)
Backups of data
Encryption of data
Contemporary processes that protect the security and integrity of data for passwords for access
Strong Password Policies: Requiring complex passwords that include a combination of letters, numbers, and special characters to increase security.
Two-Factor Authentication (2FA): Adding an additional layer of security by requiring users to provide two forms of identification before gaining access (e.g., password and a code sent to their phone).
Password Managers: Encouraging the use of password managers to generate and store strong, unique passwords for different systems.
Regular Password Changes: Implementing policies that require users to change their passwords regularly to mitigate the risk of compromised credentials.
Passwords stored as encrypted data in databases or locally on a machine to keep them safe
Passwords can ensure that no unathorised access can happen meaning access rights are much more effective
Contemporary processes that protect the security and integrity of data for write-protect mechanisms.
Read-Only Access: Setting certain files or databases to read-only mode ensures that data cannot be altered or deleted. (Doesnt stop reading though)
File Permissions: Configuring file systems to set permissions that restrict write access to authorized users only.
Immutable Storage: Using storage solutions that prevent data from being altered or deleted after it has been written, useful for log files or legal records.
Software will prevent data from being written to, modified, or erased protecting the data security
Cryptography
Cryptography, practically known as encryption, is simply the act of scrambling a piece of plain text into cipher text so that it can't be immediately understood.
It is used to safeguard information and communications through code so data is no interpreted by unauthroised parties
Why is cryptography important?
Transmission over public networks (data cannot be intercepted and read)
Data breaches (So it harder for confidential data to be exposed)
Compliance with legislation (Like GDPR)
Secure communication
Which is important in industries like banking and for messaging where you want data to be private
Caesar Cypher
Caesar Cypher (Shift Cyper) is the simplest and most well-known form of encryption, where each letter of the alphabet is shifted a certain number of places according to the key. (e.g. a key of 1 would shift a → b)
This can generally be cracked by analysing common letter frequencies (like A and E and use those to start as a basis for the shift)
What is a brute force attack
A method that involves systematically trying all possible comindations of encryption keys or passwords untill the correct one is found (software can greatly speed this up). It works by attempting to find the code and if the system returns a valid or invalid response then you know if it is correct or rong
What are ways that make brute foce attacks harder to perform
Strong passwords
2FA
Account lockout if too many incorrect passwords
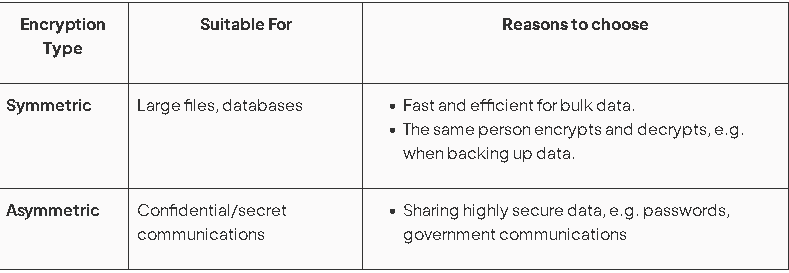
What are the types of encryptions?
Symmetric (single key) Encryption
Asymmetric (Double key) Encryption
Symmetric (single key) Encryption
Symmetric encryption uses only one key that is used for both encrypting and decrypting the data.
The sender must send the message and the key to the receiver, although they will not be sent together.
The key must be sent securely as if it is incercepted during transmission then data can be decrypted
For example and XOR gate with a mask would be symmetric because you use the same on each time
Advantages and Disadvantages of Symmetric (single key) Encryption
- Symmetric algorithms have one key that has to be at both ends of a transmission.
- Symmetric is best used for data on your own disks, as it's fast
- Single key encryption can be faster to use.
- Single key encryption may not be secure if the key value has to be transferred over the internet and is intercepted by an unauthorised person.
- symmetric techniques are very easy for modern computers to crack.
- Single key encryption is suitable for personal use when encrypting files on a single computer. No transfer of the key value to another user is needed.
- Single key encryption is suitable for use within an office or work group, where the key value can be transferred during personal meetings or over a secure local area network.
Asymmetric (Double key) Encryption
Asymmetric encryption is also known as public key encryption. It uses two keys (public and private key), one to encrypt the data and one to decrypt the data. The keys are separate but mathematically connected. A public key can be shared and used to encrypt data and only the private key can decrypt it
This solves the key distribtuion issue for symmetric
What is the public and private key?
Public - Can be shared openly so that anyone can encrypt a message for the recipient
Private - The recipient of the message hold the private key and it is kept secret as it is the only thing that decrypts the messages
Advantages and Disadvantages of Asymmetric (Double key) Encryption
• Asymmetric algorithms have two keys - a private and a public key.
• With asymmetric algorithms, a shared secret key does not have to be exchanged over an insecure medium such as the Internet, as it does with symmetric algorithms
• If someone knows the encryption key, they can encrypt information but not decrypt it.
• Asymmetric is best used for keys, digital signatures, data sent over the web, e.g. bank details, etc.
• Double key encryption avoids the security risk by only revealing the public encryption key to the sender. The private decryption key is held securely by the receiver and is not revealed.
• Double key encryption is more suitable for the transfer of confidential data over the internet (such as credit card details), e.g., online hotel/airline bookings or shop purchases.
• In many cases, the public and private key pairs in an asymmetric system can remain intact for many years without compromising the security of the system. E.g., SSL certificates
• Asymmetric keys are far slower to use and not feasible for use in transmitting large amounts of data because of the increase in transmission times
• Asymmetric keys are harder to generate.
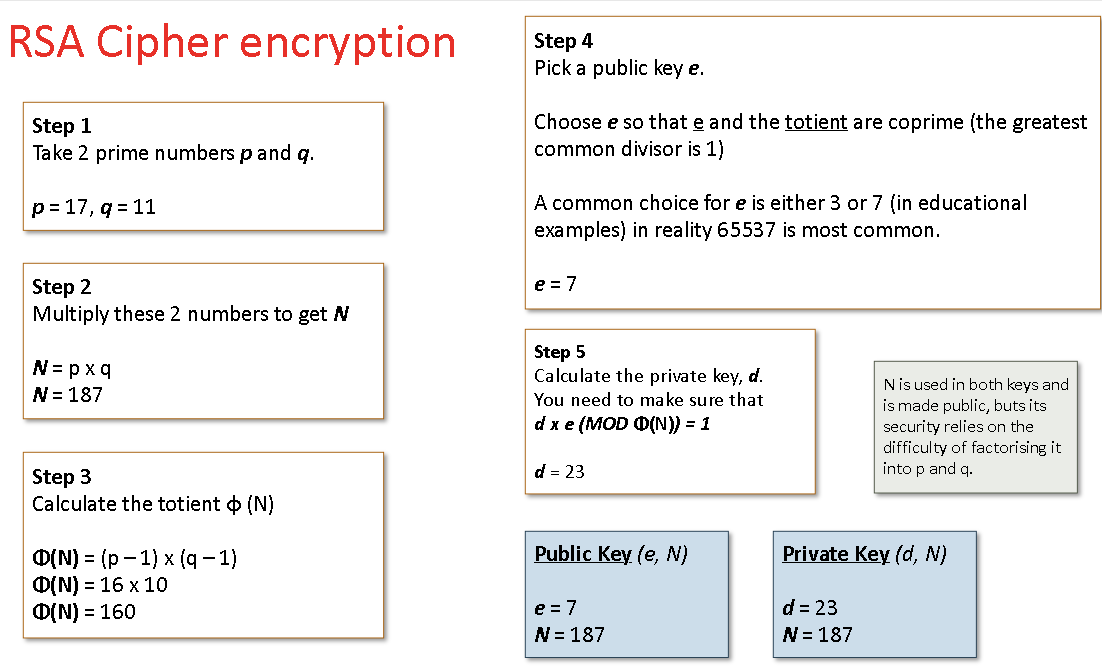
Whats and RSA cipher?
Asymmetric encrtion that uses prime numbers to encrypt data. It would use two prime numbers and follow the steps. for a public and private key. Then it will use powers and MOD to encrypt the message which can only be decrypted with the private key.
This data is gjven for exams
Symmetric vs Asymmetric encrytion?
Biometric Security
Biometric devices are used to add security to a computer system.
A biometric device is something that works with unique features of the human body (behavioural and biological characterisitics) to recognise individuals
Types of Biometric Security
• Fingerprint recognition
• Iris Scanning
• Retina Scanning
• Facial recognition
• Voiceprint recognition
• DNA
Fingerprint Recognition
Fingerprint recognition is the process of capturing the person's fingerprints (for all or some of their fingers), then digitising and storing this data on a computer system. It isolates the fingerprint on the image and extracts certain features then uses this to create a template for comparison
When entry/access is attempted, the fingerprint is captured again.
The images are compared, with entry/access being allowed if there is a match.
However you may be able to replicate a fingerprint using a 3D model and use this to access a system (very specific and hard to do though)
Iris & Retina Scanning
Iris and retina scanning involve capturing the unique patterns of a person's iris or retina (such as blood vessels and patterns), digitising this data and creating a template, and storing it on a computer system, so that when entry/access is attempted, the iris or retina is scanned again, the new scan is digitised and compared to the stored data, and entry/access is allowed if there is a match.
It can be costly due to high resolution cameras required for this scanning
Facial Recognition and its uses
Face recognition involves capturing a person's facial features, digitising this data, and storing it on a computer system, so that when entry/access is attempted or surveillance is conducted, the facial image is captured again, the new image is digitised and compared to the stored data, and entry/access or identification is confirmed if there is a match.
It measured key facial features such as proportions and sizes of features like nose, eyes, and mouth
Face recognition could be used for instance, by the police at football grounds to check for known troublemakers by comparing current images with stored images.
There could be concern over the lack of privacy if innocent people's facial images are stored by the police.
This technology could also be used in airport security, city centre drunkenness patrols, shopping centre CCTV, etc.
Voiceprint Recognition
Voiceprint recognition involves capturing a person's unique voice characteristics, digitising this data, and storing it on a computer system, so that when entry/access is attempted or verification is needed, the voice is captured again, the new voiceprint is digitised and compared to the stored data, and entry/access or identification is confirmed if there is a match.
This technology could be used to access a room or building by speaking a name or keyword at the door. The person's voice needs to have been recorded previously and it needs to be compared / matched with the original before access is granted.
Factors that could affect Voiceprint Recognition
• High background noise
• Cold / sore throat
• Recording and playing back of the original voice (to gain unauthorised access)
Benefits of biometrics
• Biometric data is unique to a person and cannot be transferred, which reduces the risk of impersonation
• Biometric data is very difficult to copy, steal or imitate (unlike PINs, signatures, etc)
• It is not possible to "forget," as it would be with access cards, PINs, etc
• Convenient
Concerns of biometrics
• Some people might see this use of biometrics as an infringement of privacy / modesty, etc, (personal liberty)
• People might also be concerned about the uses the data might be put to
• People might be concerned about physical damage (e.g. eye damage from repeated flash photography)
• Will not work if the original data capture was flawed (e.g. if criminals manage to have their data recorded and fraudulently become authorised)
• The facial recognition database could allow officials to carry out unauthorised surveillance by monitoring CCTV pictures.
• Possible errors in the system, (e.g. through misidentifying persons in poorly lit streets following a crime).
• If your biometric data is stolen you cannot change it like a password
What is authenticaiton?
Verifying a users identity by comparing data stored related to that person to data entered
What is identification?
Determining a persons identity by comparing data entered to all data stored in the database (like CCTV criminal recognition)
What is FRR and FAR
FAR - False acceptance rate of biometric data giving access to a system
FRR - probability data incorrectly rejects a user
Disaster Planning
• Backups should be made
• Files should be archived off-site
• There should be an alternative system / hardware that can be replaced quickly
• There should be a back-up power supply
• Staff should be trained in recovery procedures
• It must be possible to rebuild the data
Types of malicious software
- viruses
- worms
- trojan horses
- spyware
- scare-ware/ransome ware
- Botnets
Virus
A virus is software that will attempt to spread over the network by infecting emails, removable storage devices, or known software vulnerabilities.
Once a virus is in play, it will deliver to one or more other pieces of software known as the payload.
The attack vector for a virus tends to be through emails or infected websites.
Will replicate itself onto other files or computers
Trojans
Trojans work in a similar way to viruses, only they are hidden in files or programs. When these files are opened, the Trojan is activated, delivering its payload.
Tricking users into downloading files or using illegal peer-to-peer networks is the most common attack vector for Trojans.
Spyware
Spyware is malicious software that runs secretly on a computer, unknown to the user. Rather than disrupting a computer or causing data loss, spyware tracks key presses and software use, which is then sent back to the hackers.
This is commonly used to commit identification fraud. The spyware attack vector tends to be from other malicious software, such as a virus.
Scare-ware/ransom-ware
Scareware software will try to scare the user into buying fake or further malicious software. It will pop up messages suggesting that your system is compromised and only their software can fix the problem, at a price.
Ransomware uses similar tactics but will delete, collect, or encrypt files, which they will then ransom back.
Ransomware can also take control of webcams.
Scareware tends to be used on compromised websites while ransom-ware tends to have an attack vector as the payload of a virus.
Botnets
Botnets will create a back door to your computer, allowing a hacker to use it without your permission.
The hacker will then use your computer as part of a larger group of compromised computers to launch further attacks, normally denial of service.
Again, this tends to be the payload of a virus.
These may remain dormant for a while but will work after activiation and will generally spread it self by sending to other computers
Worm
A worm is malicious software that replicates itself and will spread to any machine in a network.
Unlike viruses, worms do not need to be attached to a file to run.
A worm infects a computer by being downloaded or over a network connection.
It will also disrupt a machine or network and cause data loss.
How does malware generally infect a device?
Exploiting technical vulnerabilities in a firewall or other software (Worms or botnets)
Are downloaded online by mistake (Trogans or adware or ransomeware)
Are downloaded as part of a social engineering scam (malicious email attachments or phishing links) (Toragans or spyware)
Infected removable media (Viruses or spyware)
Spread on a network
Protection against malware
• Install virus protection software, also called anti-virus software - each virus has its own unique'signature’ that is known to virus protection software and stored in a database. Data stored on a computer system is scanned to see if any of the virus signatures within the database exist on the system. There are many thousands of known viruses, and new viruses are created daily. Virus protection software therefore needs to be updated regularly to combat these.
• Use a firewall - A firewall can be a software or hardware security system that controls the incoming and outgoing network traffic. Packets of data are analysed to determine whether they should be allowed through or not.
• Keep your operating system up to date - New ways to bypass the operating system’s built-in security are often discovered and can be covered by installing the security patches issued by the operating system manufacturer.
Staff training - make sure staff know how to stop malware and scams
What are the three types of hackers?
- Black hat hacker
- Grey hat hacker
- White hat hacker
Black hat hacking
Black hat hackers will break into systems for their own purposes without permission.
This could be for financial gain, political motivation, to test their skills or just for fun.
Generally will install malware, or modify or steal data when agained access.
White hat hacking
White hat hackers will use their skills to break into a system to expose flaws and then advise on how they will be fixed with permission.
They will work directly for the company, or are hired by that company, to perform penetration testing, which identifies vulnerabilites with the system
After access is gained will generally report on flaws of the system
Grey hat hacking
Grey hat hackers are like white hat hackers, who are not directly hired by a company but perform penetration testing anyway to expose flaws. Without prior authorisiation
The hope is that they will be hired by the company, but more often than not, they are prosecuted under the Computer Misuse Act.
Once access is gained will generally disclose these vulnerabilities
Penetration testing
Penetration testing is done by all three types of hackers and involves trying to break into a system by exploring vulnerabilities in the OS, application flaws, poorly configured systems and user behaviour.
The goal of this testing is to find flaws in the security in order to exploit them or fix them, depending on who is doing the testing.
For a white hat hacker this is authorised assessment or security to indentify vulnerabilities in software. It involves simulating an attack on a system by exploring weaknesses in (applications, the OS, user behaviour, network configuration)
What are the 5 phases of Penetration Testing?
1. Reconnaissance (Information gathering)
2. Scanning (Indetifying vulnerabilities)
3. Gaining access
4. Maintaining access (To test damage)
5. Clearing tracks/Reporting findings
Reconnaissance
Reconnaissance is all about collecting as much publicly available data as possible.
This could include software in use, names of employees, IP addresses, and other such data.
The key here is not to set off any alarm bells by trying to access protected information too early.
Once this is done, phase two will start, which will probe the system defences in more detail.
Scanning?
This tage involves probing system defences in more detail. Scans are done on available ports, software bersions are found, and addresses of public computers are found to create a blueprint of the system
Ganing access?
Once a blueprint is created vulnerabilities are identified and may be expolited (such as out of date software with unpatched security flaws)
Maintaining access/report findings?
A malicious attacker may try to change passwords or create a back door to the system or future access. And they then would clear logs to hide their tracks and avoid fines or jail time.
An authorised peneration tester would document and report findings to the company
What are the types of penetration testin? And definitions
Black box - No internal knowledge or permissions for the system
White box - Given insider permissions and knowledge of the system to simulate an employee
How are files and data protected from security risks?
Administrative controls (staff training, company policy on things like passwords)
Authentication cotnrols (2FA, Strong password policies)
Access controls (permisson levels)
Physcial controls (Secure disposal of documents, Locking of sensitive data)
What is contigency planning?
A contignecy plant outlines procedures an organisation follows to maintain or restoer operations after a disruption.
Its aimed to procted Availability and integrity of data through recovery procedures.
What are some examples of distaters that you would need to recover from?
Natural disasters (floods, fire)
Hardware failure
Cyber attacks
Power outages
What are key elements of a contignecy plan?
Backups regularly taken and tested for recovery
Off-site or cloud storage
Redundant systems (fail safe)
Clear recovery procedures for employees
Defined roles and responsibilities
Business continuity planning
What is a Recovery Time and Recovery Point objective?
RTO - How much downtime is acceptable for a system
RPO - How much data loss is acceptable