csc438 section2
1/112
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
113 Terms
What does 'accuracy' refer to in cybersecurity?
The degree to which information is correct and reliable.
What is an 'advanced persistent threat' (APT)?
A prolonged and targeted cyberattack where an intruder gains access to a network and remains undetected.
Define 'adversary capability'.
The skills and resources that an adversary possesses to carry out an attack.
What is meant by 'attack vector'?
The method or pathway used by an attacker to gain access to a system.
What does 'Common Vulnerability Scoring System' (CVSS) provide?
A standardized framework for rating the severity of security vulnerabilities.
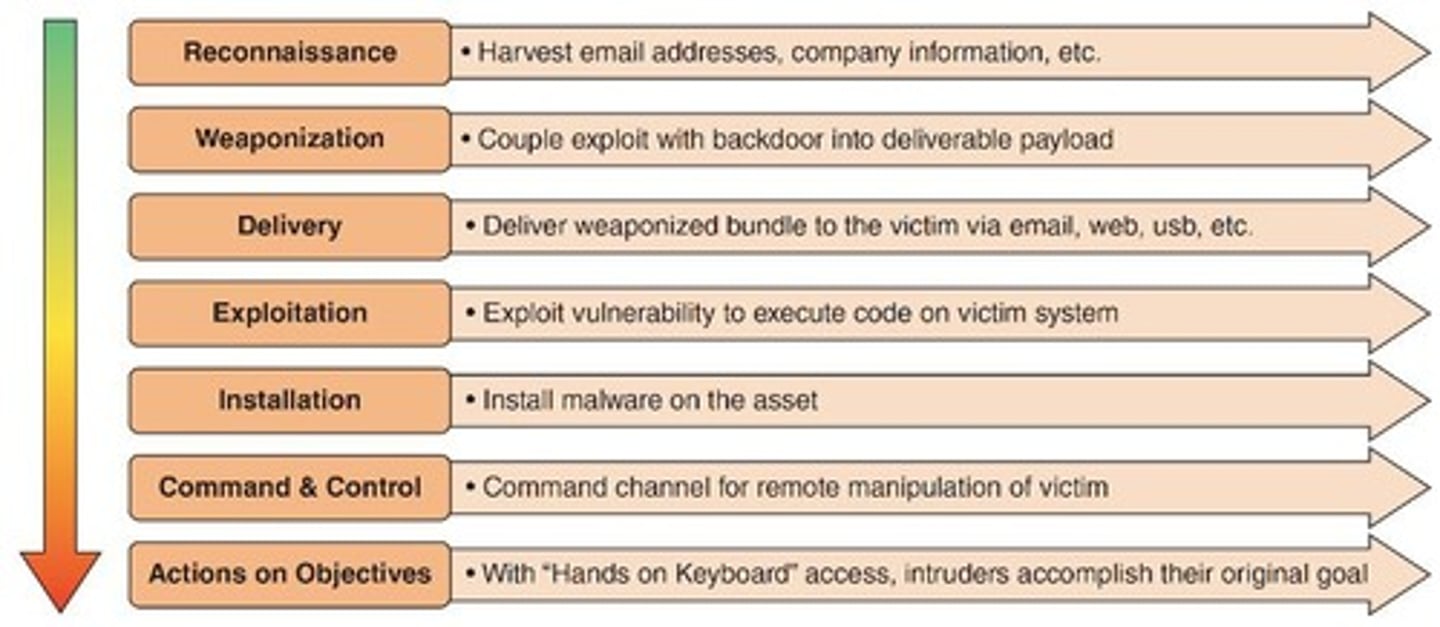
What is the 'Cyber Kill Chain™'?
A model that outlines the stages of a cyberattack, from reconnaissance to execution.
What is 'insider threat'?
A security risk that originates from within the organization, typically involving employees or contractors.
What does 'open source intelligence' (OSINT) entail?
The collection and analysis of publicly available information for intelligence purposes.
Define 'indicator of compromise' (IoC).
A piece of forensic data that indicates a potential intrusion or breach in a system.
What is 'vulnerability management'?
The process of identifying, classifying, remediating, and mitigating vulnerabilities in software or hardware.
What does 'risk management' involve?
The identification, assessment, and prioritization of risks followed by coordinated efforts to minimize, monitor, and control the probability or impact of unfortunate events.
What is a threat actor?
A term used to describe individuals or entities responsible for cyber incidents against enterprises, governments, and users.
What is commodity malware?
Malware sold by other threat actors that can be customized for specific attacks.
What distinguishes black hat hackers?
They violate computer security for personal gain or to inflict malicious damage.
What is the role of white hat hackers?
They probe systems with permission to find weaknesses and report them back to the organization.
Define gray hat hackers.
Attackers who break into systems without permission but disclose the attack to pressure organizations into fixing vulnerabilities.
What are hacktivists?
Groups motivated by ideology, often making political statements or retaliating against perceived injustices.
What are nation-state actors?
State-sponsored attackers who launch cyberattacks against foreign governments or their own citizens to cause harm.
What is an insider threat?
A threat that comes from employees, contractors, or business partners of an organization.
What are intentional insiders?
Individuals who intentionally steal or alter data for personal gain or revenge.
What are unintentional insiders?
Individuals who cause harm to the organization without malicious intent, often due to carelessness.
What is the role of competitors as threat actors?
They may launch attacks to steal classified information to gain a competitive advantage.
What do brokers do in the context of cybersecurity?
They sell knowledge of vulnerabilities to other attackers or governments instead of reporting them to vendors.
What is cyberterrorism?
Attacks aimed at causing disruption and panic among citizens by targeting critical infrastructure.
How has organized crime adapted in the digital age?
They have shifted from traditional crimes to online attacks that are more rewarding and less risky.
What is shadow IT?
When employees install their own equipment or software in violation of company policies due to frustration with slow technology acquisition.
What are known knowns in cybersecurity threats?
Threats that both threat actors and security personnel are aware of, such as established viruses.
What are known unknowns?
Vulnerabilities that organizations are aware of but have not been discovered by outside threat actors.
Define unknown knowns.
Threats known to threat actors but not to security professionals, often referred to as zero-day attacks.
What are unknown unknowns?
Security threats that are hidden from both threat actors and security professionals.
What is the goal of nation-state actors in cyberattacks?
To cause financial harm to businesses in foreign countries or damage the reputation of enterprises.
What motivates hacktivists today?
They may spread fake news and support conspiracy theories in addition to making political statements.
What is the primary motivation of organized crime in cyberattacks?
To engage in more rewarding and less risky online criminal activities.
What is the primary characteristic of gray hat hackers?
They operate without permission but do not seek personal gain from their actions.
What is a common consequence of insider threats?
Data theft or alteration that can harm the organization's resources and reputation.
What is the significance of the Johari Window in cybersecurity?
It helps categorize and understand the visibility of threats in relation to knowledge among threat actors and security professionals.
What type of hacker attempts to probe a system with permission?
White hat hackers.
What is the main difference between intentional and unintentional insiders?
Intentional insiders act with malicious intent, while unintentional insiders cause harm without malicious intent.
What are white hat hackers?
Ethical attackers who probe systems for weaknesses with permission and report findings to the organization.
What is a Key Risk Indicator (KRI)?
A metric indicating the upper and lower bounds of specific indicators of normal network activity.
What is an Indicator of Compromise (IoC)?
Evidence that malicious activity is occurring, often in the early stages of an attack.
How can sharing IoC information benefit organizations?
It aids predictive analysis and helps discover attacks before they escalate.
What are the areas that threat intelligence sharing can aid?
Incident response, vulnerability management, risk management, security engineering, and detection and monitoring.
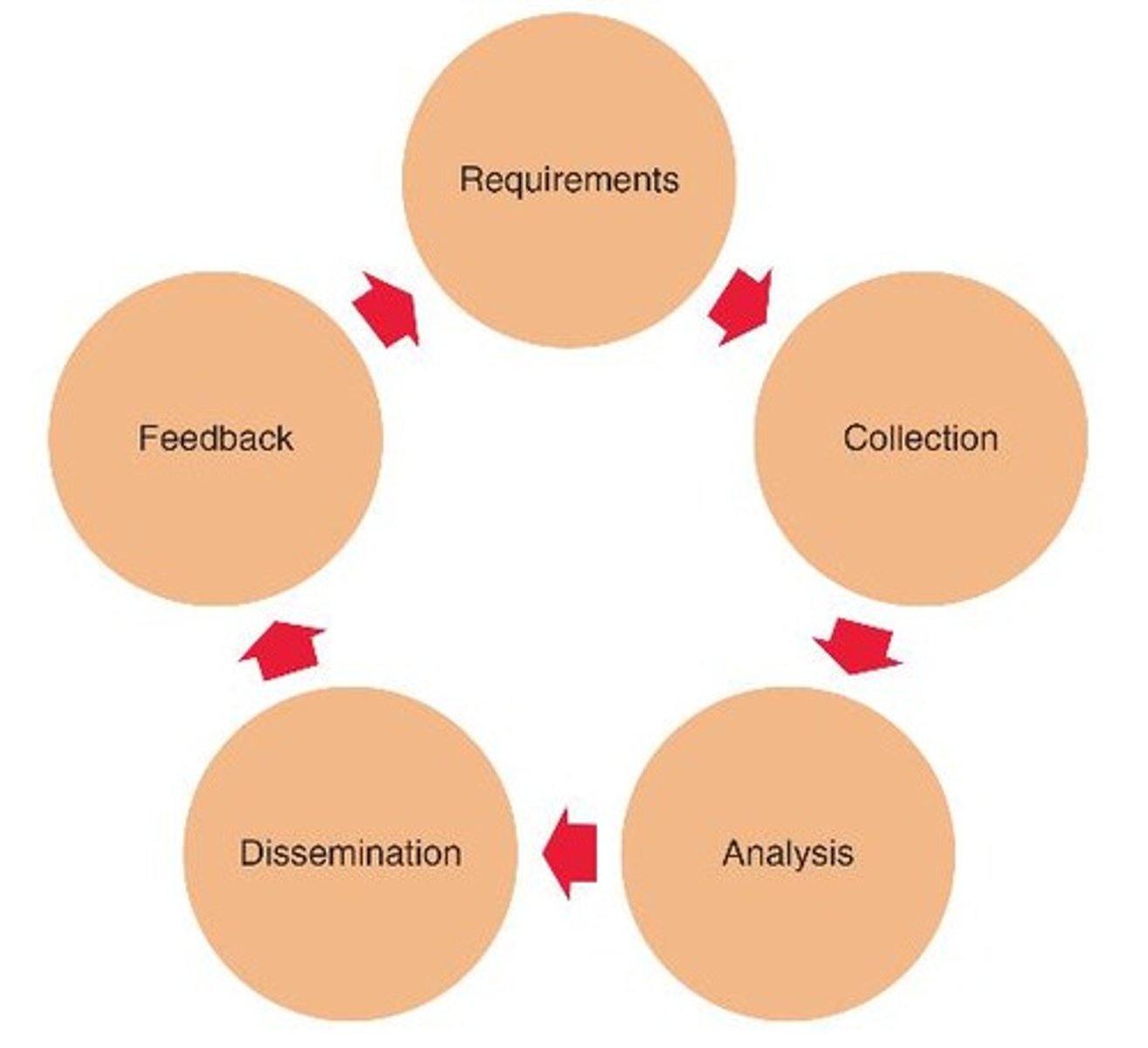
What is the intelligence cycle?
The process through which raw cybersecurity data is transformed into useful threat intelligence.
What is the first step of the intelligence cycle?
Requirements: Setting high-level goals for the threat intelligence program.
What does the collection step in the intelligence cycle involve?
Gathering information from internal networks, security devices, and external sources like security news and forums.
What happens during the analysis phase of the intelligence cycle?
Processing collected data into usable information.
What is the purpose of the dissemination phase in the intelligence cycle?
Making decisions on how the information should be acted upon and distributed.
What is the feedback phase in the intelligence cycle?
Evaluating the effectiveness of threat intelligence decisions and using that feedback to improve future requirements.
What are the two categories of threat intelligence sources?
Open Source Intelligence (OSINT) and Closed Source Intelligence.
What is Open Source Intelligence (OSINT)?
Threat intelligence that is freely available to the public.
What are the two types of OSINT?
Public lists of threat indicators and formalized sharing through trusted communities.
What services does the Cyber Information Sharing and Collaboration Program (CISCP) provide?
Analyst-to-analyst exchanges, analytical products, cross-industry orchestration, and digital malware analysis.
What are information sharing and analysis communities?
Organizations that share OSINT unique to their specific industry.
What is a challenge of Open Source Intelligence?
Data comes from various sources and formats, making consistency and relevance a concern.
What is the solution to address data variety in OSINT?
Formatting data in the eXtensible Markup Language (XML).
What are the three elements that differentiate data, information, and knowledge?
Data: discrete facts; Information: organized data with meaning; Knowledge: expertise applied to information.
What is an example of data?
Discrete facts like '141, 700, A, 701, B'.
What is an example of information?
Organized data such as 'Course 141-700 is offered in the A-Term'.
What is an example of knowledge?
Expert skills applied to information, like 'Enrollment in CIS 141/700 A-Term has increased over CIS 141/701 in the B-Term'.
What is the purpose of the feedback phase in the intelligence cycle?
To assess the effectiveness of decisions and improve future intelligence cycles.
What question does feedback in the intelligence cycle aim to answer?
'What did we do right, and what did we do wrong?'
What is the purpose of the Cybersecurity Information Sharing Act (CISA)?
CISA provides authority for cybersecurity information sharing between the private sector, state and local governments, and the federal government.
What does the Freedom of Information Act (FOIA) allow the public to do?
FOIA allows the public to request access to records from any federal agency, with certain exemptions.
What is the Traffic-Light Protocol (TLP)?
TLP is a set of designations used to ensure that sensitive information is shared only with the appropriate audience, indicated by four colors: red, amber, green, and white.
What does the Protected Critical Infrastructure Information (PCII) Act protect?
PCII protects private sector infrastructure information that is voluntarily shared with the government for homeland security.
What is Closed Source Intelligence?
Closed Source Intelligence is proprietary information owned by an entity with exclusive rights, requiring investigation based on specific criteria.
What are vulnerability databases?
Vulnerability databases are repositories of known vulnerabilities and information about how they have been exploited.
What is the correct order of the intelligence cycle?
Requirements, collection, analysis, dissemination, and feedback.
What is a cybersecurity framework?
A cybersecurity framework is a series of documented processes used to define policies and procedures for implementing and managing security controls.
What is the MITRE ATT&CK framework?
MITRE ATT&CK is a knowledge base of attacker techniques that have been classified in detail.
What does the Diamond Model of Intrusion Analysis examine?
The Diamond Model examines network intrusion events.
What is the Cyber Kill Chain™?
The Cyber Kill Chain™ is a set of steps used to break into a web server or computer network, based on a military targeting process.
What is reputational research in cybersecurity?
Reputational research involves looking into past actions and tracking the credibility of web domains.
What is behavioral research in cybersecurity?
Behavioral research acknowledges the importance of human behavior in designing and using cybersecurity technology.
What is the Common Vulnerability Scoring System (CVSS)?
CVSS assigns a numeric score to vulnerabilities based on factors like access vector, attack complexity, and system integrity.
Why might vulnerabilities with higher CVSS scores not be prioritized first?
Not all high CVSS vulnerabilities are equally damaging; circumstances must also be considered.
What is Automated Indicator Sharing (AIS)?
AIS is a method for computer-to-computer communication to distribute threat intelligence quickly.
What are threat maps?
Threat maps illustrate cyber threats overlaid on a geographical representation.

What role do file and code repositories play in cybersecurity?
They allow victims of attacks to upload malicious files and software code for examination.
What is the significance of the year 2015 in cybersecurity legislation?
In 2015, the Cybersecurity Information Sharing Act (CISA) was passed.
What is the main goal of the intelligence cycle?
The main goal is to set high-level objectives for the intelligence program and ensure effective information use.
What is the importance of feedback in the intelligence cycle?
Feedback assesses the effectiveness of the threat intelligence and informs future actions.
What does the term 'cyber threat intelligence' refer to?
Cyber threat intelligence refers to information that helps organizations understand and mitigate cyber threats.
What is the role of human behavior in cybersecurity?
Human behavior can significantly impact the effectiveness of cybersecurity measures, as users may inadvertently engage with threats.
What is the purpose of sharing limitations in the Traffic-Light Protocol?
To ensure that sensitive information is only shared with the appropriate audience.
What is the significance of the year 1967 in relation to FOIA?
The Freedom of Information Act (FOIA) was passed in 1967.
What factors are considered in behavioral research?
It acknowledges human behavior, such as users clicking on malicious links or attachments.
What does CVSS stand for?
Common Vulnerability Scoring System.
What does a higher CVSS score indicate?
It indicates a vulnerability that may be more serious, but not necessarily the one that should be addressed first.
What are some questions to assess vulnerabilities?
Questions include: Can it be fixed quickly? Can it be exploited externally? Is sensitive data involved?
What principle should defenders remember during a cyberattack?
Defenders cannot always assume the most likely course of action by the threat actor.
What is the definition of threat modeling?
A proactive strategy for evaluating risks by identifying potential threats and developing tests to detect and respond to them.
What is one advantage of threat modeling?
It helps quickly identify new threats and allows security teams to evaluate risks effectively.
What is the total attack surface?
The sum total of the number of different attack points in an organization.
What is an attack vector?
The method used to compromise a vulnerability, such as weak credentials or malware.
What does likelihood refer to in threat modeling?
The probability of an attack occurring and being successful, ranging from low to very high.
What is an attack tree?
A diagram that displays the goal of an attack, types of attacks, and techniques used.
What does the OCTAVE methodology focus on?
Assessing nontechnical organizational risks that may result from compromised data.
What is the drawback of the Trike threat modeling process?
It faces scalability issues if the system is too large.