CSC438 section1
1/117
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
118 Terms
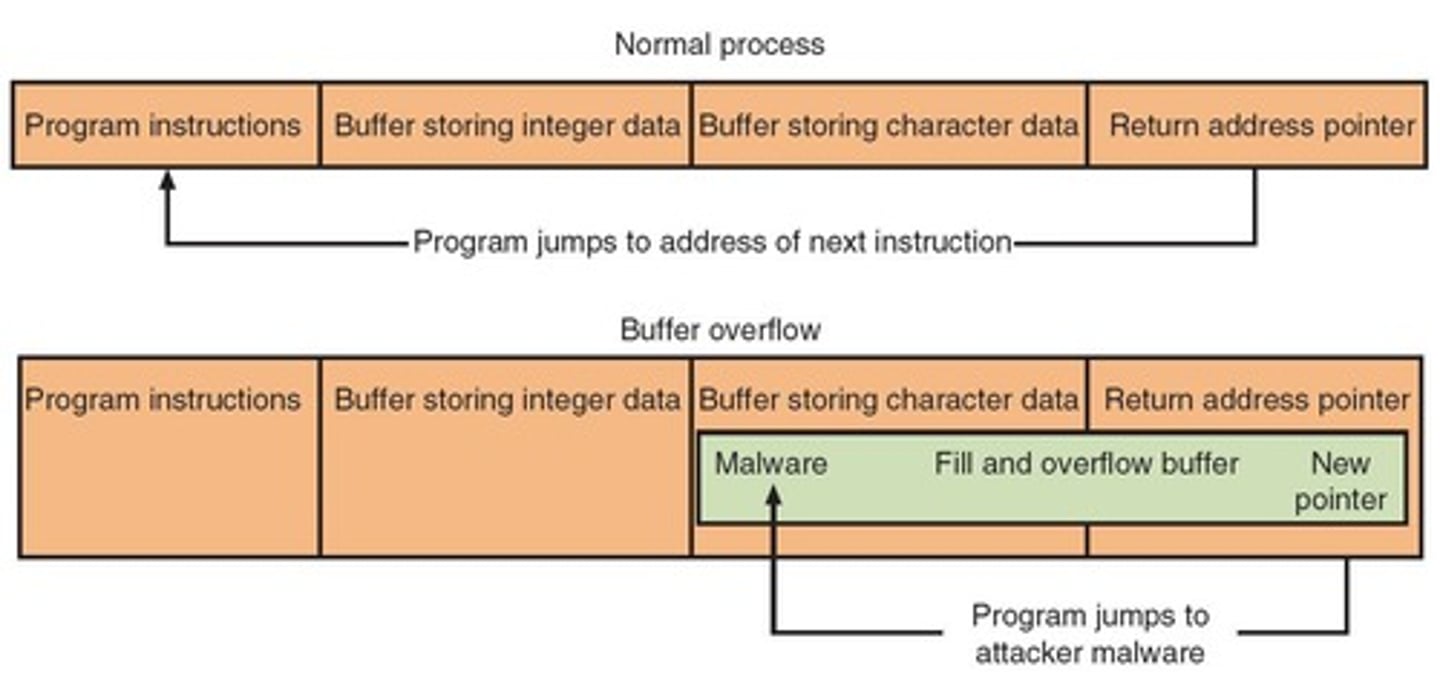
What is a buffer overflow attack?
A type of attack where excess data overflows into adjacent memory, potentially allowing attackers to execute arbitrary code.
What does building automation system refer to?
A system that controls and monitors building systems such as HVAC, lighting, and security.
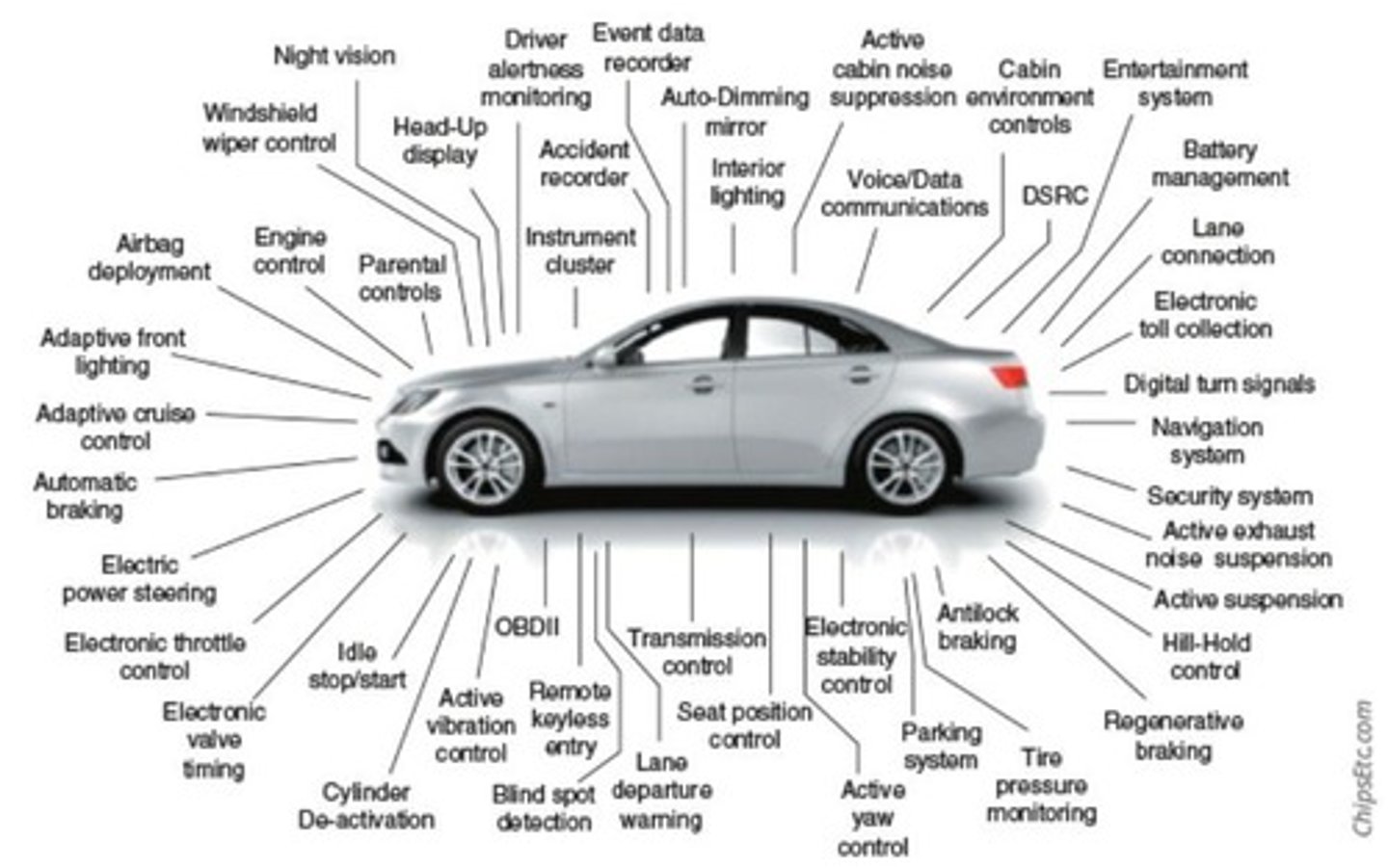
What is a controller area network (CAN) bus?
A robust vehicle bus standard designed to facilitate communication among various microcontrollers without a host computer.
What is credential stuffing?
An attack method where stolen account credentials are used to gain unauthorized access to user accounts through automated login requests.
What does cross-site scripting (XSS) entail?
A security vulnerability that allows attackers to inject malicious scripts into content from otherwise trusted websites.

What is directory traversal?
An attack that allows unauthorized access to files and directories stored outside the web document root.
What is a drone in the context of cybersecurity?
An unmanned aerial vehicle that can be exploited for various purposes, including surveillance and data collection.

What is an embedded system?
A computer system with a dedicated function within a larger mechanical or electrical system.
What is an eXtensible Markup Language (XML) attack?
An attack that exploits vulnerabilities in XML processing to manipulate or corrupt data.
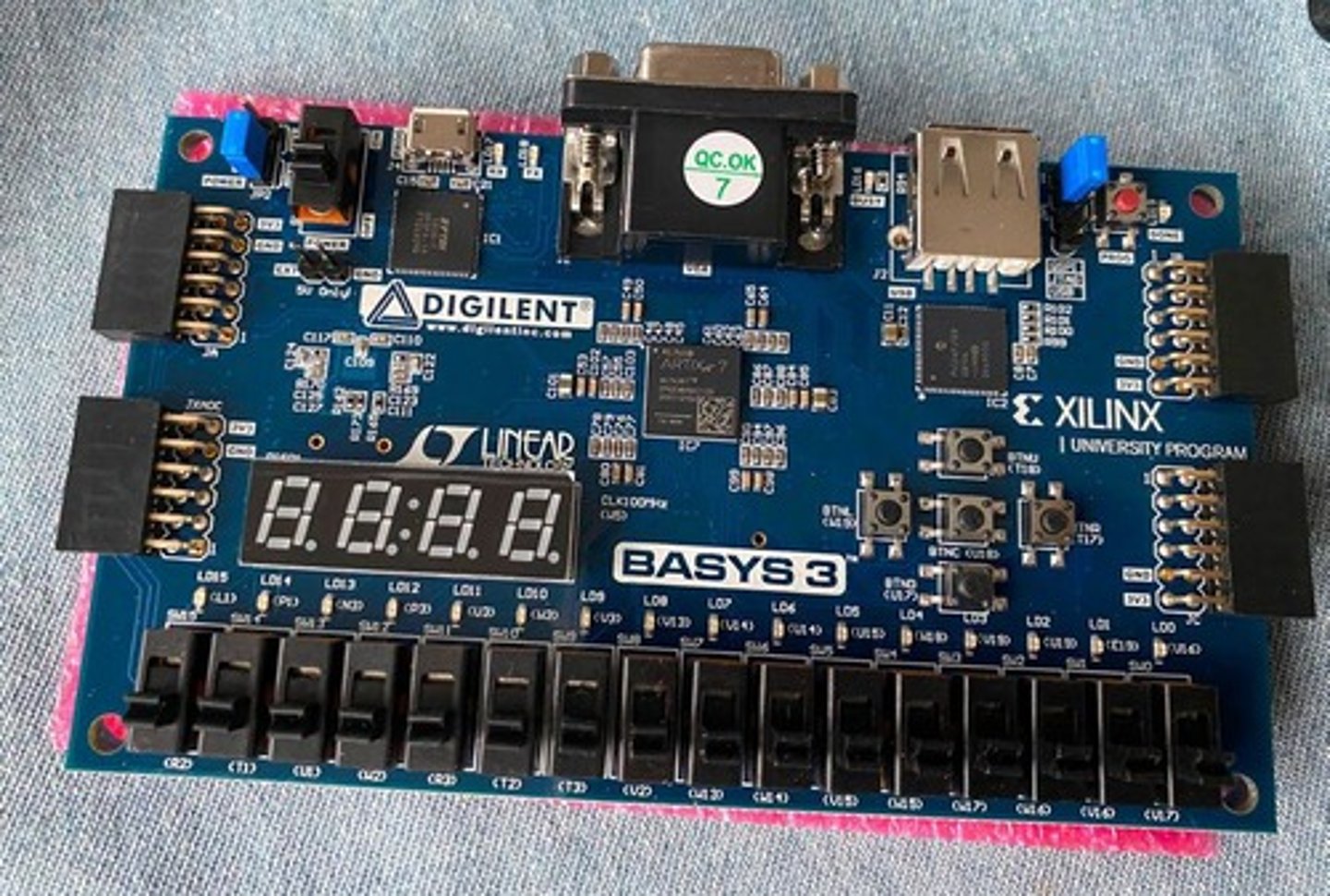
What is a field-programmable gate array (FPGA)?
An integrated circuit that can be configured by the customer or designer after manufacturing.
What is a heap overflow?
A type of buffer overflow that occurs in the heap memory area, potentially allowing code execution.
What does impersonation refer to in cybersecurity?
The act of pretending to be another user or device to gain unauthorized access or information.
What is an industrial control system (ICS)?
A system used to control industrial processes such as manufacturing, production, and power generation.
What is an integer overflow attack?
An attack that occurs when an arithmetic operation attempts to create a numeric value that is too high to be represented within the allocated space.
What does Internet of Things (IoT) refer to?
The network of physical devices connected to the internet, enabling them to collect and exchange data.
What is a man-in-the-middle (MITM) attack?
An attack where the attacker secretly intercepts and relays messages between two parties who believe they are directly communicating with each other.
What is Modbus?
A communication protocol used for transmitting information over serial lines between electronic devices.
What is a password spraying attack?
An attack method where a small number of commonly used passwords are tried against many accounts.
What is Persistent XSS?
A type of cross-site scripting attack where the injected script is permanently stored on the target server.
What does physical access control entail?
Measures taken to restrict physical access to facilities, equipment, and resources.
What is privilege escalation?
An exploit that allows an attacker to gain elevated access to resources that are normally protected from an application or user.
What is a real-time operating system (RTOS)?
An operating system that guarantees a certain capability within a specified time constraint.
What is Reflected XSS?
A type of cross-site scripting attack where the injected script is reflected off a web server.
What is remote code execution (RCE)?
A vulnerability that allows an attacker to execute arbitrary code on a remote machine.
What is a rootkit?
A collection of software tools that enable unauthorized access to a computer or network while hiding its presence.
What is session hijacking?
An attack where an attacker takes control of a user's session after they have authenticated.
What is Structured Query Language (SQL) injection?
An attack that allows an attacker to execute arbitrary SQL code on a database by injecting malicious SQL statements.
What does supervisory control and data acquisition (SCADA) refer to?
A system used for controlling industrial processes and infrastructure.
What is a system on a chip (SoC)?
An integrated circuit that consolidates all components of a computer or other electronic system onto a single chip.
What are workflow and process automation systems?
Systems designed to automate complex business processes and functions beyond conventional automation.
What is the focus of Module 1 in the CompTIA CySA+ Guide?
Enterprise Threats and Vulnerabilities
What are the objectives of the module?
Identify different types of common attacks, describe risks associated with mobile devices, and explain security issues of embedded and specialized devices.
What are some types of cyberattacks mentioned?
Attacks using malware, memory vulnerability attacks, web server application attacks, session hijacking, attacks on credentials, exploitation and penetration attacks, and social engineering attacks.
Define malware.
Malicious software designed to harm or exploit a device, service, or network, entering a system without user consent.
In which areas of memory can a buffer overflow attack occur?
In both the heap and stack areas.
What is cross-site scripting (XSS)?
An attack using scripting that originates on one site to impact another site, essentially a client-side code injection attack.
What is Document Object Model (DOM) XSS?
An XSS attack where a web application writes data to the DOM without proper sanitization, allowing attackers to manipulate the data.
What is the total number of malware instances currently in existence?
Exceeds 1.2 billion instances.
What are the components of a process in memory?
Text, data, stack (local variables), and heap (dynamic memory).
What can modify the stack pointer or heap pointer in a buffer overflow attack?
Malicious software memory location.
What is the role of a process control block (PCB) in memory vulnerability attacks?
It can be modified to point to malicious software memory locations.
What is the purpose of the icebreaker activity in the class?
To discuss various types of cyberattacks and personal safety measures against them.
What is a session hijacking attack?
An attack where an attacker takes control of a user's session after they have logged in.
What are social engineering attacks?
Attacks that manipulate individuals into divulging confidential information.
What is the significance of identifying common attacks in cybersecurity?
It helps in understanding risks and implementing effective security measures.
What is the consequence of a successful malware attack?
It can lead to unauthorized access, data theft, and system damage.
What is the main risk associated with mobile devices?
They can be easily lost or stolen, leading to potential data breaches.
What is the importance of sanitization in web applications?
It prevents XSS and other injection attacks by ensuring user input is properly handled.
What is the goal of penetration attacks?
To exploit vulnerabilities in a system to gain unauthorized access.
How can organizations protect against social engineering attacks?
By training employees to recognize and respond to such threats.
What is the impact of memory vulnerabilities on software security?
They can lead to exploitation and unauthorized access to sensitive data.
What is the role of user input in web server application attacks?
Threat actors exploit user input to execute attacks like XSS.
What is a threat actor's capability when controlling a script executed in a victim's browser through XSS?
They could fully compromise that user.
What can an attacker do when they have control over a victim's session through XSS?
Initiate interactions with other application users, modify information, perform any action the user can, and view any information the user can.
What is SQL injection?
An attack that targets SQL servers by introducing commands into the server to retrieve confidential information.
What is the intent of SQL injection attacks?
To retrieve confidential information from the database, not to inject malicious code.
How can an attacker verify if an email address exists using SQL injection?
By entering an email in a field and observing the server's response; a specific message indicates whether the email is verified.
What is an XML injection attack?
An attack on NoSQL databases that use XML for data manipulation, which can occur if input is not sanitized.
What is a session ID?
A unique value assigned by a web server to a specific user for the duration of their visit.
What is one method used for hijacking a session?
Intercepting the session ID through XSS or a man-in-the-middle (MITM) attack.
Why is password spraying less likely to raise alarms?
Because it uses common passwords, which may not trigger account lockouts.
Why does credential stuffing have a higher probability of success than password spraying?
Because it leverages a large number of stolen passwords and users often reuse passwords across multiple accounts.
What is the first step threat actors take in exploitation and penetration tactics?
Conduct reconnaissance against systems to look for vulnerabilities.
What do threat actors do after gaining advanced privileges?
They tunnel through the network to access additional systems and may use directory traversal attacks.
What is a backdoor in cybersecurity?
A method installed by attackers to maintain long-term access to a compromised system.
What is social engineering?
A method of gathering data by exploiting the weaknesses of individuals.
What is social engineering impersonation?
Masquerading as a real or fictitious character to fool victims, also known as identity fraud.
What is the goal of pretexting in social engineering?
To obtain private information by impersonating someone else.
Which attack takes advantage of user input?
Cross-site scripting attack.
What is a cross-site scripting (XSS) attack?
An attack using scripting that originates on one site to impact another site.
Give an example of an embedded system.
Central heating system, GPS system, fitness tracker, medical devices.
What are the categories of embedded and specialized devices?
Hardware and software, industrial systems, campus systems, IoT devices, specialized systems.
What is a Raspberry Pi?
A low-cost, credit card-sized computer motherboard.
What is an Arduino?
A controller designed for other devices, with less power compared to Raspberry Pi.
What do industrial control systems (ICSs) manage?
Devices locally or remotely by collecting, monitoring, and processing real-time data.
What is a supervisory control and data acquisition (SCADA) system?
A system that manages multiple ICSs to maintain efficiency and reduce downtime.
What common protocol do many SCADA systems use?
Modbus for transmitting information between devices.
What is a building automation system?
A system that manages building elements, including physical access control systems.
What is an example of an IoT device?
Smartwatch, fitness devices, coffee makers, or keyless entry systems.
What are the security constraints for embedded systems?
Power limitations, low processing capabilities, lack of advanced network security features, and inability to patch vulnerabilities.
Why do embedded systems have low power requirements?
To prolong battery life, which limits their ability to perform strong security measures.
What is the impact of low compute capabilities on embedded systems?
It restricts the implementation of complex and comprehensive security measures.
What is a common use of IoT devices?
Home automation items like thermostats, coffee makers, and washing machines.
What is the role of workflow and process automation systems in a campus?
To interconnect various elements for centralized and automatic monitoring and control.
What is a common example of a specialized system in automobiles?
Controller area network (CAN) bus.
What is the purpose of a building automation system?
To manage building elements, including access control and environmental systems.
What is the significance of real-time operating systems (RTOS) in SoC?
They are specifically designed for embedded or specialized systems.
What is an example of a specialized system?
Drones or specific industrial control systems.
What is the primary function of industrial control systems?
To control devices such as valves, pumps, and motors without human intervention.
What is a common feature of modern campuses?
The use of workflow and process automation systems.
What is the main challenge regarding cryptography in embedded systems?
Encryption and decryption require significant processing and storage capacities that these devices lack.
What is the role of IoT devices in everyday life?
To enhance convenience and automation in tasks such as home management.
What is a common security constraint for embedded systems?
Lack of authentication features.
Why do many devices operate on an 'implied trust' basis?
They are designed without security features, assuming all other devices or users can be trusted.
What are weak defaults in device security?
Common usernames and passwords like 'admin', '123456', or 'password' that are easy to guess.
What does the Internet of Things (IoT) Cybersecurity Improvement Act of 2019 require?
Connected devices must have reasonable security features appropriate for their function and the information they handle.
What are the four categories of mobile devices?
Tablets, smartphones, portable computers, and wearables.
What is a significant risk associated with mobile devices?
Device vulnerabilities, connection vulnerabilities, and accessing untrusted content.
What is a major physical security concern for mobile devices?
They are frequently lost or stolen, risking data retrieval by thieves.
How long does Apple provide Over The Air (OTA) updates for iOS devices?
At least four years.