Authentication, Authorization, and Accounting - CompTIA Security+ SY0-701 - 1.2
1/6
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
7 Terms
AAA Framework
Identification
-This is who you claim to be
-Usually your username
Authentication
-Prove you are who you say you are.
-Password and other authentication factors
Authorization
-Based on your identification and authentication, what access do you have?
Accounting
-Resources used: login, time, data sent and received, logout time.
Authenticating people
The process of verifying the identities of users trying to gain access to a network or system.
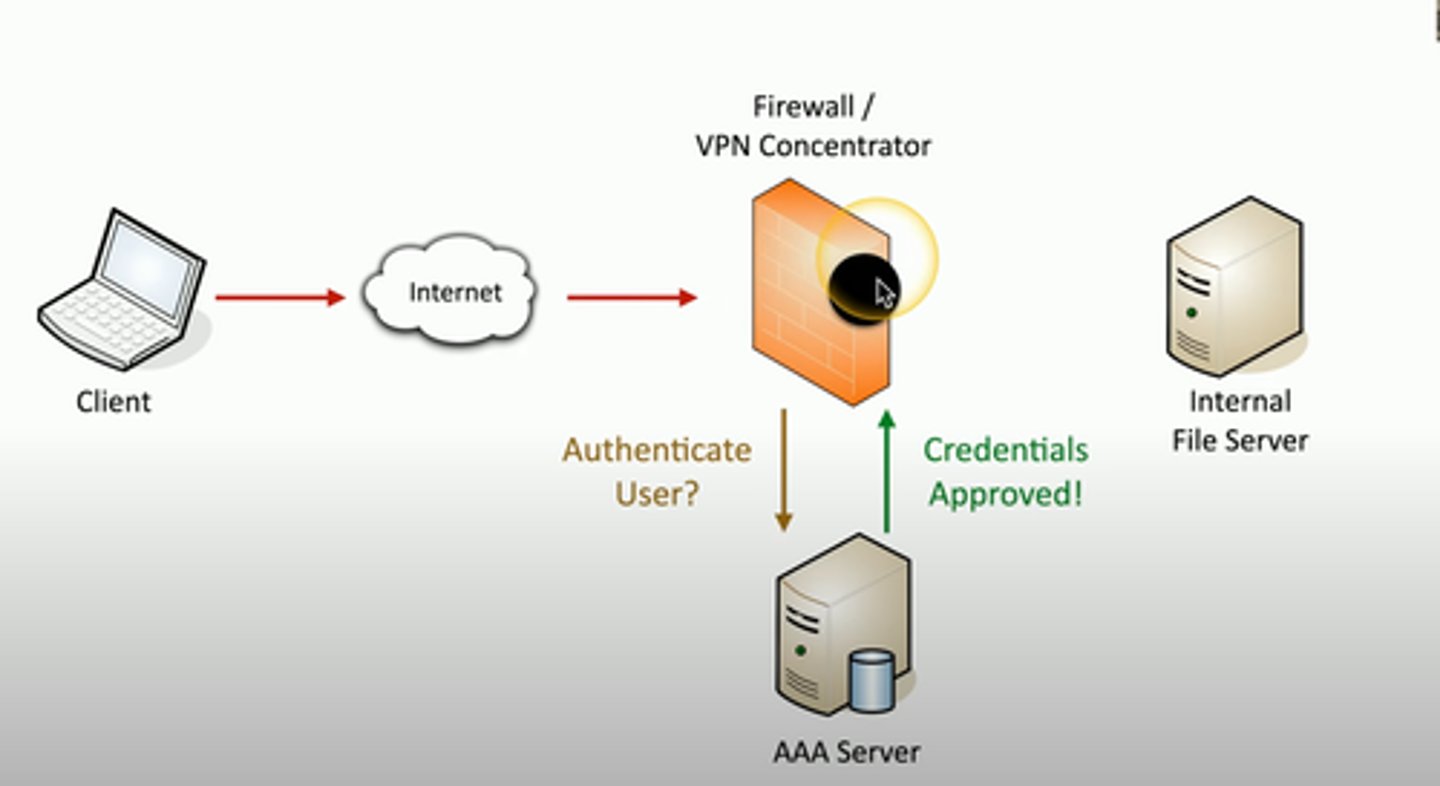
Authenticating systems
You have to manage many devices
-Often devices that you'll never physically see
A system can't type a password
-And you may not want to store one
How can you truly authenticate a device?
-Put a digitally signed certificate on the device
Other business processes rely on the certificate
-Access to the VPN from authorized devices
-Management software can validate the end device
Certificate Authentication
An organization has a trusted Certificate Authority (CA)
- Most organizations maintain their own CAs
The organization creates a certificate for a device
- And digitally signs the certificate with the organizations's CA
The certificate can now be included on a device as an authentication factor
- The CAs digital signature is used to validate the certificate

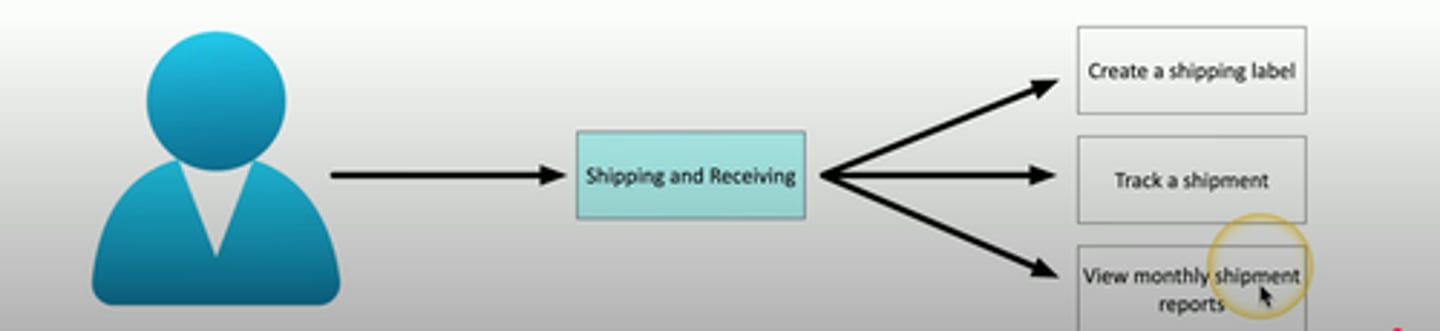
Authorization models
The user or device has now authenticated
- To what do they now have access
- Time to apply an authorization model
Users and services -> data and applications
- Associating individual users to access rights does not scale
Put an authorization model in the middle
- Define by roles, organizations, attributes, etc
No authorization model
• A simple relationship
- User -> Resource
• Some issues with this method
- Difficult to understand why an authorization may exist
- Does not scale
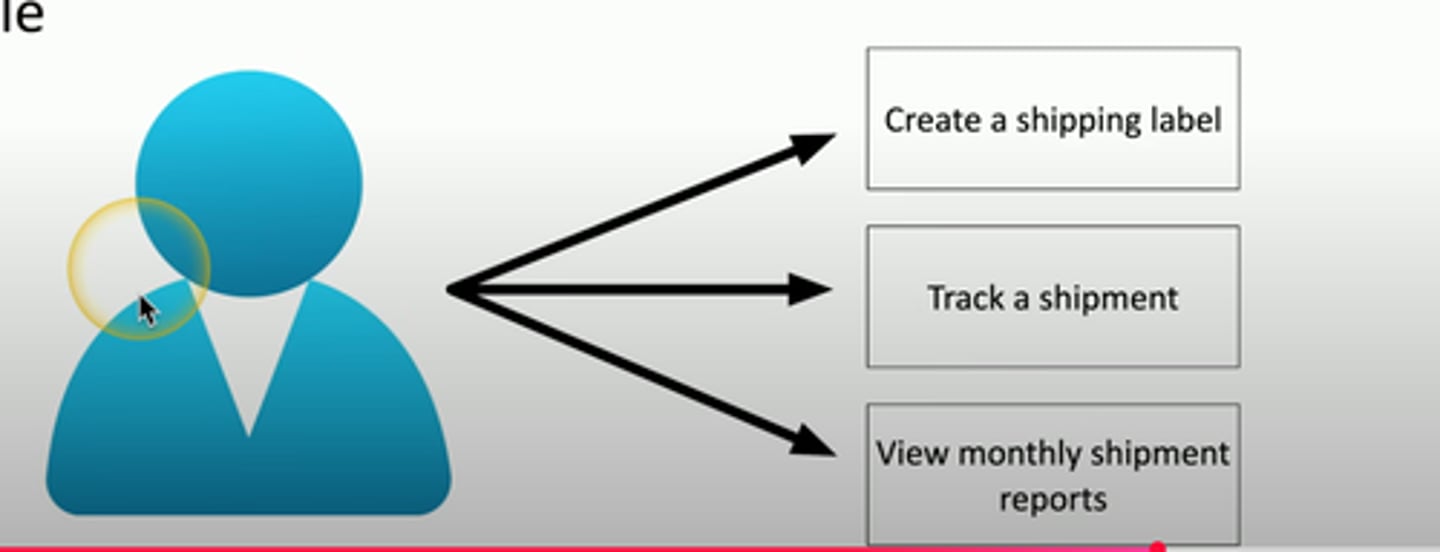
Using an authorization model
Add an abstraction
- Reduce complexity
- Create a clear relationship between the user
and the resource
Administration is streamlined
- Easy to understand the authorizations
- Support any number of users or resources