ISDS 4123 exam 1 terms
1/101
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
102 Terms
Access control matrix
A two-dimensional table that allows for individual subjects and objects to be related to each other.
Advanced Encyption Standard (AES)
symmetric encryption algorithm that uses the Rijndael block cipher to protect data. It is a worldwide standard used for secure communication and is characterized by the following technical specifications:
Block Size: AES processes data in fixed 128-bit blocks.
Key Sizes and Processing Rounds: The algorithm supports three different key lengths, each requiring a specific number of transformation rounds to complete the encryption process:
128-bit keys use 10 rounds.
192-bit keys use 12 rounds.
256-bit keys use 14 rounds.
ARP
Resolves IP addresses to MAC addresses. ARP poisoning attacks can redirect traffic through an attacker's system by sending false MAC address updates. VLAN segregation helps prevent the scope of ARP poisoning attacks within a network.
Asymmetric Encryption (Public/Private key)
Two different but mathematically related keys are used where one key is used to encrypt and another is used to decrypt. Has both a public key to be shared and a private key that is held onto by the owner that should remain private. If the public key encrypts, only the private key can decrypt and vice versa.The receiver has a public key the sender can accessThe receiver also has a private key needed to open and decrypt the message they are receiving.
binary
Bi(2) each character represents 1 of 2 values: 0 or 1.
boolean logic (AND OR XOR BUT)
A logic operation that is widely used in cryptography as well as in generating parity bits for error checking and fault tolerance.
brute- force attack/bruter
A program which will allow you to perform a dictionary or brute force attack against a remote system.Attempts every possible valid combination for a key or password.
cable limits and repeaters (100 meters)
You need a repeater when the total length of a single span of network cable exceeds 100 meters (328 feet).
The 100-meter length limit applies to the cable that connects a computer to the switch or the cable that connects switches to each other when switches are daisy chained together.
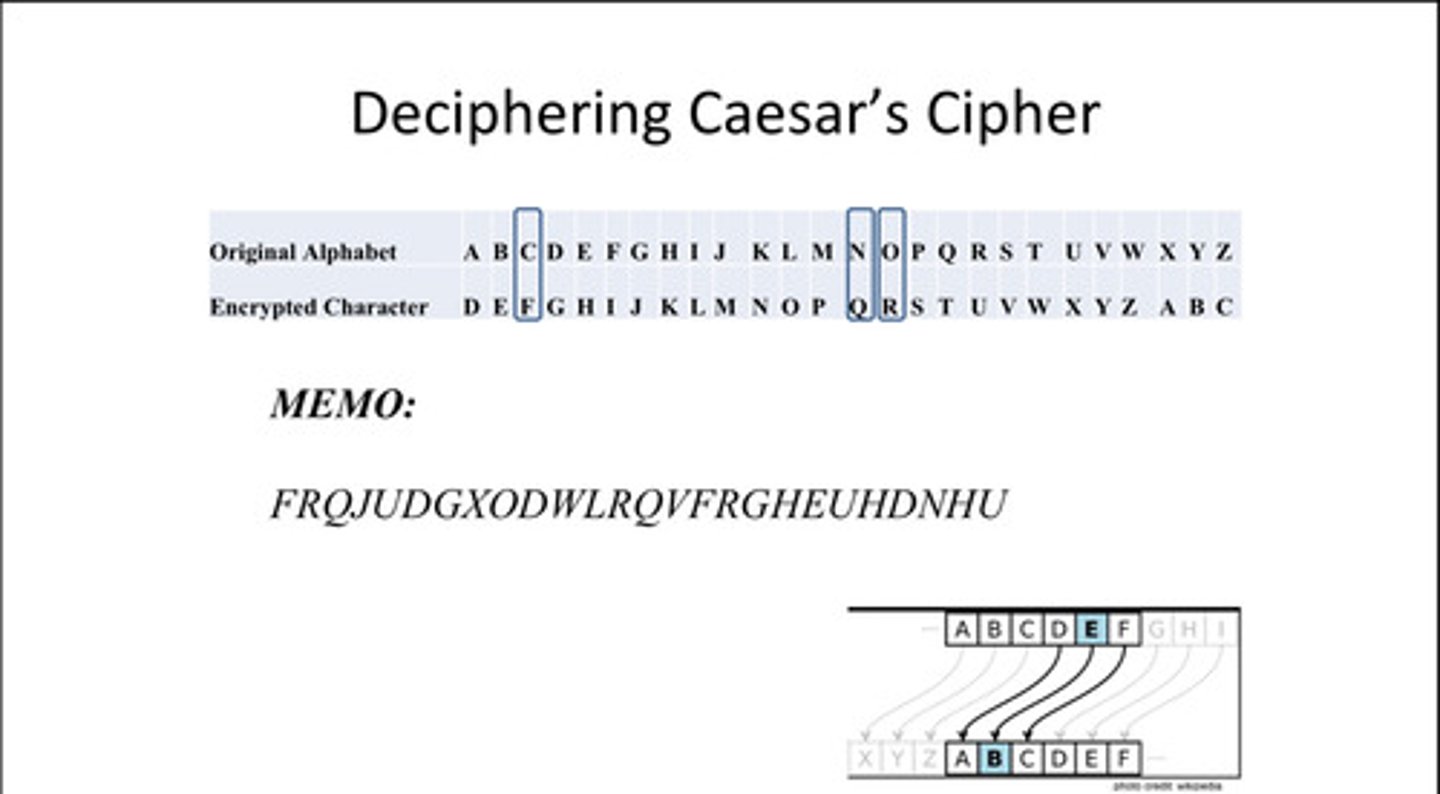
Ceasar Cipher
a technique for encryption that shifts the alphabet by some number of characters
Substitution Cipher
Letters of the alphabet replaced by other letters. weakness of the frequency distributions of symbols in the plaintext and in the ciphertext are identical, only the symbols having been relabeled
certificates and PKI (public key infrastructure)
certificate: digital document used to verify the ownership of a public key
PKI: technical framework and security standard that enables the use of asymmetric encryption for authentication, confidentiality, and integrity
chosen cipher attack
a scenario in which the attacker has the ability to choose ciphertexts C i and to view their corresponding decryptions - plaintexts P i . It is essentially the same scenario as a chosen plaintext attack but applied to a decryption function, instead of the encryption function.
chosen plaintext attack
a method hackers use to break a secret code or encryption system in order to gain unauthorized access to information. In this attack, hackers can choose specific messages (plaintexts) to be encrypted using the target's encryption algorithm.
Ciphertext-only and known-plaintext attack
Ciphertext-only: type of cryptanalysis where the attacker has access only to the encrypted ciphertext and seeks to recover the original plaintext or the key without any additional knowledge, such as the secret key or the corresponding plaintext.
known- plaintext attack: ryptographic attack where the attacker has access to both a copy of the encrypted message (the ciphertext) and the original plaintext message used to create it
containerization and virtualization
virtualization: used to host one or more operating systems (OSs) within the memory of a single host computer or to run applications that are incompatible with the host OS
containerization: lightweight form of virtualization that involves bundling an application together with all its related configuration files, libraries, and dependencies so that it can run efficiently across different computing environments.
cryptanalytic attacks
advanced techniques and methodologies designed to circumvent or break cryptographic systems
Cryptographic Key Lifecycle / Key Management Practices
involves a set of practices designed to protect information by overseeing the entire "life cycle" of a key, from selection to retirement.
Default Settings (Security Hardening)
Default configurations help make hardware, software, and systems more user-friendly, but can leave organizations vulnerable to cyber threats.
Device Lockout / Screen Locks
Enforce ______________ following a predetermined threshold of local failed authentication attempts on portable end-user devices.
Digital Signatures and Non-repudiation
digital signature: A cryptographic mechanism that uses asymmetric cryptography to bind an entity’s identity to a specific message or piece of information
Non-repudiation: A security goal that provides assurance that a party cannot later deny a previous statement or action
Dotted Decimal Notation (IP Address Format)
a human-readable representation of IP addresses in the IPv4 (Internet Protocol version 4) format. It is expressed as a series of four decimal numbers, each ranging from 0 to 255, separated by periods (dots).ex: 205.57. 32.9
Edge Computing
- Intelligene and processing are contained within each device.
- Ex: web filtering, anti-malware, intrusion prevention systems, and next-generation firewalls
Encryption in Phases (AES in Transit, DES at Rest)
A security strategy where different cryptographic protections are applied to information based on its current state: Data in Motion (in transit) or Data at Rest (stored)
The application of the Advanced Encryption Standard (AES)—a symmetric block cipher—to protect data while it is being transmitted across a network; this is often achieved through protocols like Transport Layer Security (TLS), which wraps a "temporary envelope of security" around data such as email to prevent eavesdropping
The use of the Data Encryption Standard (DES)—a legacy symmetric algorithm with a 56-bit key—to secure information that resides in a permanent location, such as a hard drive, cloud storage, or backup tape, awaiting future access
Encryption vs. Hashing
hashing: a data security technique used to convert data values into alternate, unique identifiers called hashes for quick and secure access.No one can forge a message in a way that will result in the same hash as the legitimate message.
Error Handling and Input Validation
a meaningful error message to the user, diagnostic information to the site maintainers, and no useful information to an attacker" and recommends writing specific policies for error handling that can achieve these things.
fgdump.exe (Windows Hash Dump Tool)
Extracting NTLM and LanMan password hashes from Windows. It is also capable of displaying password histories if they are available.
File Integrity Verification (e.g., md5sum)
A security process that uses cryptographic hash functions (such as SHA-256 or MD5) to ensure that a file has not been unauthorizedly altered or tampered with. It involves generating a unique checksum or digital "fingerprint" of the file and comparing it against a known-good original hash; even a minor change to the file will result in a completely different hash value, indicating a lack of integrity
Full-Device / Disk Encryption (FDE)
A way to assure data at-rest is secure even in the event of loss or theft is to use.
Hash Functions and Integrity (Length, e.g., 128 bits)
There are three SHA's, described as: SHA-1: A 160-bit hash value is generated by the widely used SHA-1 hashing algorithm. SHA-256: SHA-256 is a member of the SHA-2 family and generates hash values that are 256 bits long. SHA-3: The newest member of the SHA family, SHA-3 offers enhanced performance and security.
HTTPS / TLS / SSL (Security and Limitations)
Encrypts HTTP traffic with SSL or TLS using port 443.
Infrastructure as Code (IaC)
used for infrastructure automation to create environments.
The most common use of is in software development to build, test, and deploy applications. Traditionally, system administrators used a combination of scripts and manual processes to set up infrastructure environments.
Input Sanitization and Filtering
the process of checking and filtering input data to ensure it's free of characters or strings that could inject malicious code into an application or system.
Integrity and Hashing Concepts
fundamental security goal that ensures data is not altered or destroyed without authorization, providing assurance that a received message is identical to the one sent
Internet Protocols (SMTP, HTTP, SNMP, SSH & OSI Layers)
A suite of rules developed by the DoD that governs all activity across the Internet and most networks by operating at the Network and Transport layers to provide reliable or fault-tolerant communication
Simple Mail Transfer Protocol (SMTP): The primary protocol used by internet email servers to accept and transport messages from clients to other server-based inboxes, typically using TCP port 25
HTTP vs. HTTPS: HTTP is an unencrypted protocol vulnerable to eavesdropping, while HTTPS verifies website identity and encrypts nearly all information sent between the user and the service
IoT Security and Edge Devices
- smart devices, appliances, garage doors, door locks, lights etc.Security is probably not the primary focus- in some cases, it's not a consideration at allIoT devices should be segmented from the private network- keep your personal devices and storage systems away from IoT devices- If an IoT device is breached, your personal data is not accessibleUse a separate VLAN- many home access points provide a "guest" network- this is different than the DMZ or screened-subnet
IP Address / IPv4 vs IPv6
An internet protocol address: Numerical label assigned to each device connected to a computer network that uses the internet Protocol for communication.Two main functions: Host or network interface identification and local addressing."Temporary" logical address assigned over or on the MAC addressEx: 10.0.07 or 10.0.0.13
Key Generation / Keyspace
This is the number of possibilities that a specific key length can generate.
Lab Tools: Disk Encryption, SSH/SCP, Hardening, Network Sniffing
Disk Encryption (Full-Disk Encryption): A security method that protects data at rest by encrypting the entire storage medium, typically requiring successful authentication to access the operating system and often utilizing a Trusted Platform Module (TPM) on the motherboard for secure key management.
SSH and SCP: (Note: Definitions are from outside the sources; please verify independently). SSH (Secure Shell) is a protocol used for secure remote login and command execution, while SCP (Secure Copy Protocol) is used for secure file transfers; the sources note that the Blowfish symmetric algorithm is frequently used in SSH implementations.
Hardening: (Note: The term is not explicitly defined in the sources; definition is from outside sources). The process of securing a system by minimizing its attack surface; the sources support this through practices such as disabling unused features and apps and strictly auditing and configuring secure defaults rather than relying on vendor presets.
Network Sniffing (Protocol Analyzer): A tool—also known as a sniffer or traffic monitor—used to capture and examine network frames and packets as they travel across a wire; to capture all data passing through a segment, the tool typically places the network interface card (NIC) into promiscuous mode
Loopback Address (127.0.0.1)
The IP address 127.0. 0.1.
Packets sent to this address never reach the network but are looped through the network interface card only. This can be used for diagnostic purposes to verify that the internal path through the TCP/IP protocols is working.
MAC Address (Physical Address)
a hardware address that uniquely identifies each node on a network.Six groups of two hexadecimal digits: D0:03:4B:....
MAC Prefix and Vendor Identification
The first six digits of a MAC address. A unique identifier for a network device that uses a connection based on one of the IEEE 802 standards, such as Ethernet, Wi-Fi, or Bluetooth. It is factory-installed and is meant to unambiguously identify each host, as well as provide precision routing of packets in broadcast networks.
MAC Spoofing / Address Conflict
a commonly employed tactic by threat actors to illicitly obtain access to confidential information in diverse situations.After a successful attempt, the perpetrator can illicitly infiltrate the network and potentially execute further malicious activities, such as compromising other devices or exfiltrating sensitive data.
Man-in-the-Middle (MITM) Attack
attack is a cyber attack in which a threat actor puts themselves in the middle of two parties, typically a user and an application, to intercept their communications and data exchanges and use them for malicious purposes like making unauthorized purchases or hacking.
MD5 Hashing and Verification
128-bit message digest that is computationally infeasible to match
Micro-Segmentation / SDN / SD-WAN
Micro-segmentation: A security technique used in Zero Trust Architecture that involves dividing a network into small, granular zones to isolate workloads and protect individual resources. It moves defenses away from a static, network-based perimeter to focus on users, assets, and resources, ensuring that no internal traffic is automatically trusted.
SDN (Software-Defined Networking): (Information not found in the sources). An approach to network virtualization that allows for centralized, programmable network management by decoupling the control plane (which makes decisions about where traffic is sent) from the data plane (the underlying hardware that forwards the traffic).
SD-WAN (Software-Defined Wide Area Network): (Information not found in the sources). A virtualized service that connects and extends enterprise networks over large geographical distances, using software to dynamically manage and optimize traffic across various connection types like broadband, LTE, and MPLS for better performance and security.
Mobile Device Management (MDM)
is the process of managing mobile devices, largely in terms of usage and securityBring your own device: Allows employees to bring personal mobile device. Can be used through the company network.Company owned, personally enabled: Organization purchases devices and provides them to employees. Each user can customize the device and use it for both work and personal activities.Choose your own device: Provides users with a list of approved devices.Corporate-owned mobile strategy: Corporate-owned and used for business only.
Mobile Device Security (Remote Wipe, Screen Lock, FDE)
Device authentication: Passwords, pins, biometrics, etcs., used to verify the user's identity. When device is locked data is secured
Communication protection: Encrypted voice calls, text messages, and data transmission to ensure that the content is indecipherable to unauthorized parties.
Remote wiping: Allows users to remotely erase data and configuration settings from a lost or stolen device.
Device lockout: After a number of failed authentication attempts device locks for a specific duration or require additional authentication methods to regain access.
Screen locks: Protect the device from causal access. Triggers after a specific period of inactivity.
Application control: Limits the installation of apps from unknown sources and enforces security settings to mitigate risks associated with unauthorized software.
Asset Tracking and Inventory Control: Helps verify device ownership, locate missing or stolen devices, and maintain oversight of mobile device assets.Disabling unused features
Rooting or Jailbreaking: Bypassing restrictions to gain full system privileges on a mobile devices. Exposed device to potential risks and vulnerabilities.
Text messaging: Transmits messages via SMS MMS or other apps. SMS-based 2FA provides an additional layer of authentication, but may not be the most secure option.
Modulo Operation and Examples
often used in various cryptographic algorithms and protocols to ensure data integrity, generate keys, and perform other operations. The modulo operation calculates the remainder when one number is divided by another. It is denoted by the symbol "%".
Network Access Control / Open vs. Closed Systems
Closed systems are more secure as they limit user access to only what is necessary and authenticates users before giving them access to the system.
Network Scanning (nmap, zenmap)
network scanning tool—an open source Linux command-line tool—used for network exploration, host discovery, and security auditing.
Open Ciphers and Open Systems
open ciphers: cryptographic algorithms whose source code is openly available for inspection, modification, and use by anyone. This openness allows for transparency and peer review, which can help identify and fix security vulnerabilities more effectively than closed, proprietary algorithms.
open systems: Open systems provide a higher level of flexibility as users can more easily customize the system according to their needs but this comes at the cost of lower security.
What is the OSI Model?
Open System Interconnection model used for program development.
What is the function of the Application Layer in the OSI Model?
Responsible for interacting with end users and includes programs that interact with the network.
What is an example of software included in the Application Layer?
Email software, as it transmits and receives messages over the network.
What is the function of the Presentation Layer in the OSI Model?
Responsible for the coding of data, including file formats and character representations.
Where does encryption generally take place in the OSI Model?
At the Presentation Layer.
What is the function of the Session Layer in the OSI Model?
Responsible for maintaining communication between computers.
What does the Transport Layer do in the OSI Model?
Responsible for breaking data into datagrams or segments and ensuring proper transmission.
What protocols are associated with the Transport Layer?
TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
What is the function of the Network Layer in the OSI Model?
Responsible for logical addressing and routing data.
What form does logical addressing take in the Network Layer?
IP addresses.
What is the function of the Data Link Layer in the OSI Model?
Responsible for translating information on computers connected to the same local area network (LAN).
What addresses are used in the Data Link Layer?
Media Access Control (MAC) addresses.
What is the function of the Physical Layer in the OSI Model?
Translates binary 1s and 0s into the language of the transport medium.
What is an example of how the Physical Layer translates data?
In copper network cables, it translates data into electrical pulses.
What is a PKI Certificate?
A digital document that binds a public key to a specific identity to prevent impersonation.
What information does a PKI Certificate contain?
It contains the public key, user ID, and a validity period, all digitally signed by a trusted Certificate Authority (CA).
What is the purpose of a Certificate Authority (CA) in PKI?
To verify ownership of the public key by digitally signing the PKI Certificate.
What is Hostname Verification?
A security process where a client checks that the domain name in the server's certificate matches the hostname the user is visiting.
Why is Hostname Verification important?
It ensures the user is connecting to the legitimate service and not an imposter.
Privacy by Design (PbD)
a method of planning and implementing a system and architecture that fully supports individual rights and protects people's data.
Process Confinement and Isolation
is a key requirement for workloads in the cloud and in other contexts
Proxy Servers and TLS Inspection
a system or router that provides a gateway between users and the internet. Therefore, it helps prevent cyber attackers from entering a private network. It is a server, referred to as an "intermediary" because it goes between end-users and the web pages they visit online.
What is Public Key Encryption?
A cryptographic system that uses a mathematically related pair of keys: a public key for encryption or signature verification, and a private key for decryption or signature creation.
What is RSA in the context of Public Key Encryption?
RSA (Rivest, Shamir, and Adleman) is a worldwide standard for public-key encryption proposed in 1977 that relies on the difficulty of factoring the product of two large prime numbers.
What is ECC in the context of Public Key Encryption?
ECC (Elliptic Curve Cryptography) is a public-key encryption technique based on elliptic curves over finite fields, providing the same security as RSA with smaller key sizes.
Replay Attack vs MITM
A replay attack is a network attack when an attacker intercepts a network communication between two parties to delay, redirect, or repeat it.
Remote Wiping
The ability to remotely erase sensitive data stored on a mobile device.
Rooting / Jailbreaking Risks
A replay attack is a network attack when an attacker intercepts a network communication between two parties to delay, redirect, or repeat it.
Rootkit Detection and Prevention
collection of software designed to give malicious actors control of a computer network or application. Once activated, the malicious program sets up a backdoor exploit and may deliver additional malware, such as ransomware, bots, and more.
Rule of Least Power (in Programming)
the less powerful the [computer] language, the more you can do with the data stored in that language
Salted and Hashed Passwords / Salts in Password Storage
technique to protect passwords stored in databases by adding a string of 32 or more characters and then hashing them. Salting prevents hackers who breach an enterprise environment from reverse-engineering passwords and stealing them from the database.a random piece of data is added to the password before it runs through the hashing algorithm, making it unique and harder to crack.
SCP (Secure Copy Protocol)
a means of securely transferring computer files between a local host and a remote host or between two remote hosts.
What is the principle of Secure Defaults?
The principle that software and hardware should be configured with the most restrictive security settings upon initial installation.
Why must practitioners verify Secure Defaults?
Because vendor defaults are often chosen to minimize technical support needs rather than to provide reasonable security.
What does Fail Securely mean in design principles?
A design principle focused on managing system failures to minimize risk, ensuring the system defaults to a state that maintains a high level of security.
What is the goal of the KISS Principle in security?
To keep systems as uncomplicated as possible to reduce complexity, potential points of failure, and the attack surface.
Secure Design Principles (Least Privilege, Defense in Depth)
Least Privilege: A security principle where subjects (users) are granted only the minimum access levels and permissions strictly necessary to perform their assigned tasks; it is a core requirement of Zero Trust Architecture and is often implemented via an Access Control Matrix,.
Defense in Depth (Multilayered Security): A strategy that employs multiple layers of security controls throughout a network—such as using multilayered firewalls to protect subnets with different security levels—to ensure that if one defense is breached, additional layers remain to protect sensitive assets
What is a Side-Channel Attack?
A cryptographic attack that seeks to retrieve information being actively encrypted by monitoring a system's physical 'footprints' of activity, such as changes in power consumption, electromagnetic radiation, or processor utilization.
What is a Timing Attack?
A specific type of side-channel attack where a malicious actor measures exactly how long cryptographic operations take to complete to gain insights into the process that can be used to undermine its security.
SMS (text) Weaknesses
Lack of Encryption: SMS messages are not encrypted, and as a result, they can be intercepted and read by attackers.
Split Tunneling
lets you route some of your application or device traffic through an encrypted VPN, while other applications or devices have direct access to the internet.
SSH (Secure Shell)
a method for securely sending commands to a computer over an unsecured network. it uses cryptography to authenticate and encrypt connections between devices.
SSID Broadcast and Discovery
displaying your network as available for nearby users trying to connect their devices to a wireless network.
Symmetric Encryption (Shared Key)
the same key is used to encode and decodeEx: Company issue separate keys to each employeeBoth employees have to use the same key each employee-employee pair would have to have its own unique keys.Each time an employee joined or left keys would have to be added or deleted. (Too many keys, undesirable)
tcpdump (Packet Capture and Analysis)
a command line based network analyzer that lets you inspect network traffic. It can capture and display packets on the network interface of your Linux/UNIX computer in real-time.
# -i eth0
Virtual Networks and VM Sprawl
a phenomenon that occurs when the number of virtual machines (VMs) on a network reaches a point where administrators can no longer manage them effectively.
Wireshark Traffic Analysis
The process of using a protocol analyzer to capture, examine, and interpret data frames and packets as they travel across a network to monitor activity or troubleshoot security issues
"You Aren't Gonna Need It" (YAGNI Principle)
A simplicity principle that advises against adding capabilities or functions to an application until they are actually necessary, thereby keeping the system's complexity and attack surface to a minimum
What is the Zero Trust Architecture?
A modern security paradigm based on the principle of 'never trust, always verify,' which assumes breaches are possible and requires strict identity verification and internal microsegmentation regardless of a user's location.