Vulnerability Scanning - CompTIA Security+ SY0-701 - 4.3
1/4
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
5 Terms
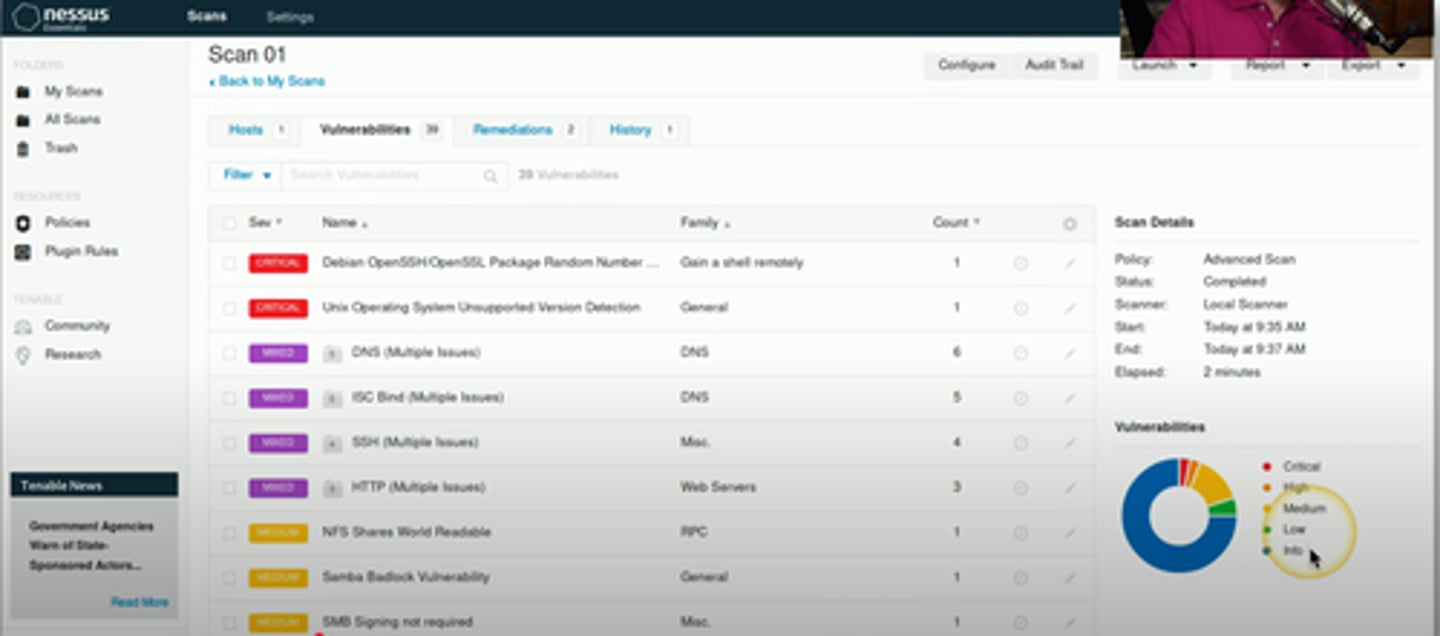
Vulnerability scanning
• Usually minimally invasive
- Unlike a penetration test
• Port scan
- Poke around and see what's open
• Identify systems
- And security devices
• Test from the outside and inside
- Don't dismiss insider threats
• Gather as much information as possible
- We'll separate wheat from chaff later
Static code analyzers
• Static Application Security Testing (SAST)
- Help to identify security flaws
• Many security vulnerabilities found easily
- Buffer overflows, database injections, etc.
• Not everything can be identified through analysis
- Authentication security, insecure cryptography, etc.
- Don't rely on automation for everything
• Still have to verify each finding
- False positives are an issue
Dynamic Analysis (Fuzzing)
Send random input to an application
• Fault-injecting, robustness testing, syntax testing, negative testing
Fuzzing engines and frameworks
• Many different fuzzing options
• Platform specific, language specific, etc.
• Very time and processor resource heavy
• Many, many different iterations to try
• Many fuzzing engines use high-probability tests
• Carnegie Mellon Computer
• Emergency Response Team (CERT)
• CERT Basic Fuzzing Framework (BFF)
Package Monitoring
Some applications are distributed in a package
- Especially open source
- Supply chain integrity
Confirm the package is legit
- Trusted source
- No added malware
- No embedded vulnerabilities
Confirm a safe package before deployment
- Verify the contents