Password Security - CompTIA Security+ SY0-701 - 4.6
1/5
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
6 Terms
Password complexity and length
• Make your password strong
- Resist brute-force attack
• Increase password entropy
- No single words, no obvious passwords
• What's the name of your dog?
- Mix upper and lower case and use special characters
• Don't replace a o with a 0, t with a 7
• Stronger passwords are at least 8 characters
- Consider a phrase or set of words
• Prevent password reuse
- System remembers password history, requires
unique passwords
Password age and expiration
• Password age
- How long since a password was modified
• Password expiration
- Password works for a certain amount of time
- 30 days, 60 days, 90 days, etc.
- After the expiration date, the password does not work
- System remembers password history, requires
unique passwords
• Critical systems might change more frequently
- Every 15 days or every week
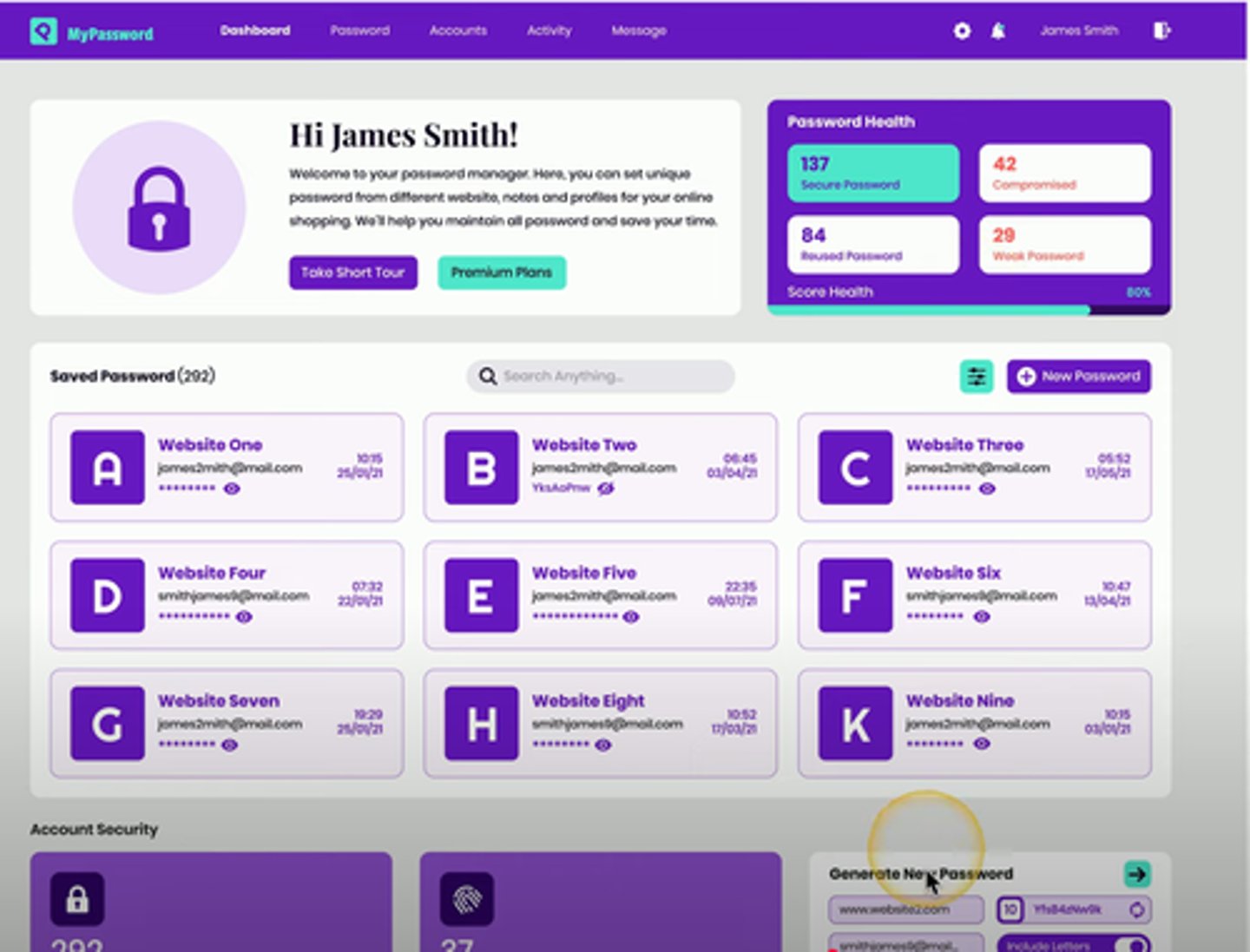
Password managers
Important to use different passwords for each account
- Remembering all of them would be impractical
Store all of your passwords in a single database
- Encrypted, protected
- Can include multifactor tokens
Enterprise password managers
- Centralized management and recovery options
Passwordless Authentication
Many breaches are due to poor password control
- Weak passwords, insecure implementation
Authenticate without a password
- This sovles many password management issues
You may already be passwordless
- Facial recognition, security key, etc
Passwordless may not be the primary authentication method
Just-in-time permissions
• In many organizations, the IT team is assigned
administrator/root elevated account rights
- This would be a great account to attack
• Grant admin access for a limited time
- No permanent administrator rights
- The principle of least privilege
• A breached user account never has elevated rights
- Narrow the scope of a breach
• Request access from a central clearinghouse
- Grants or denies based on predefined security policies
• Password vaulting
- Primary credentials are stored in a password vault
- The vault controls who gets access to credentials
• Accounts are temporary
- Just-in-time process creates a time-limited account
- Administrator receives ephemeral credentials
- Primary passwords are never released
- Credentials are used for one session then deleted
Just-in-Time (JIT) Permissions
Request access from a central clearinghouse
- Grants or denies based on predefined security policies
Password vaulting
- Primary credentials are stored in a password vault
- The vault controls who gets access to credentials
Accounts are temporary
- Just-in-time process creates a time-limited account
- Administrator receives ephemeral credentials
- Primary passwords are never released
- Credentials are used for one session then deleted