CCNA 3 (Version 7.00) ENSA Practice Final Exam Answers
1/55
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced |
|---|
No study sessions yet.
56 Terms
Which QoS mechanism allows delay-sensitive data, such as voice, to be sent first before packets in other queues are sent?
LLQ
Which QoS technique retains excess packets in a separate queue for later transmission?
shaping
What term describes adding a value to the packet header, as close to the source as possible, so that the packet matches a defined policy?
traffic marking
What is a characteristic of the distribution layer in the three layer hierarchical model?
provides access to the rest of the network through switching, routing, and network access policies
Which two methods help to prevent the disruption of network services? (Choose two.)
- installing duplicate equipment to provide failover services
- using redundant connections to provide alternate physical paths
Which technology provides laptops the ability to function on a cellular network?
mobile hotspot
Which two types of devices are specific to WAN environments and are not found on a LAN? (Choose two.)
- broadband modem
- CSU/DSU
Which three traffic-related factors would influence selecting a particular WAN link type? (Choose three.)
- amount of traffic
- security needs
= type of traffic
Which type of NAT maps a single inside local address to a single inside global address?
static
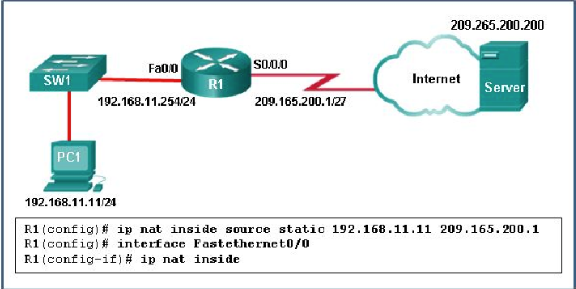
Refer to the exhibit. What has to be done in order to complete the static NAT configuration on R1?
Interface S0/0/0 should be configured with the command ip nat outside.
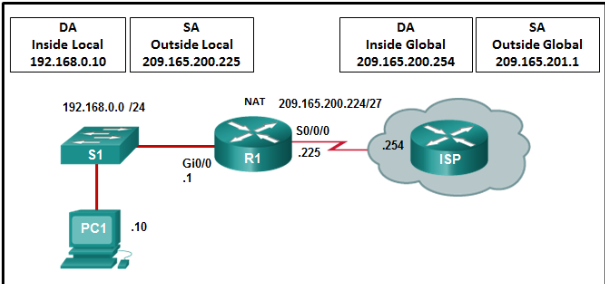
Refer to the exhibit. R1 is configured for static NAT. What IP address will Internet hosts use to reach PC1?
209.165.200.225
A network administrator is troubleshooting the dynamic NAT that is configured on router R2. Which command can the administrator use to see the total number of active NAT translations and the number of addresses that are allocated from the NAT pool?
R2# show ip nat statistics
What is correct in relation to NAT for IPv6?
It is a temporary mechanism to assist in the migration from IPv4 to IPv6.
Which three statements are generally considered to be best practices in the placement of ACLs? (Choose three.)
- Filter unwanted traffic before it travels onto a low-bandwidth link.
- Place standard ACLs close to the destination IP address of the traffic..
- Place extended ACLs close to the source IP address of the traffic.
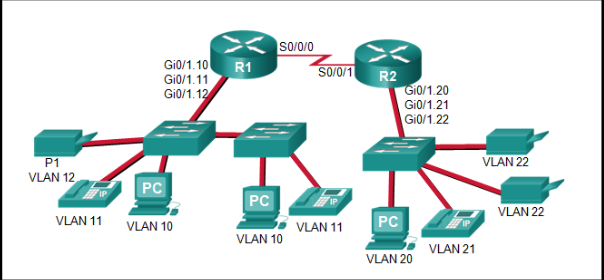
Refer to the exhibit. The Gigabit interfaces on both routers have been configured with subinterface numbers that match the VLAN numbers connected to them. PCs on VLAN 10 should be able to print to the P1 printer on VLAN 12. PCs on VLAN 20 should print to the printers on VLAN 22. What interface and in what direction should you place a standard ACL that allows printing to P1 from data VLAN 10, but stops the PCs on VLAN 20 from using the P1 printer? (Choose two.)
- R1 Gi0/1.12
- outbound
If a router has two interfaces and is routing both IPv4 and IPv6 traffic, how many ACLs could be created and applied to it?
8
Which type of Hypervisor is implemented when a user with a laptop running the Mac OS installs a Windows virtual OS instance?
type 2
Which two layers of the OSI model are associated with SDN network control plane functions that make forwarding decisions? (Choose two.)
- Layer 2
- Layer 3
What defines a two-tier spine-leaf topology?
The Cisco APICs and all other devices in the network physically attach to leaf switches.
Which SNMP message type informs the network management system (NMS) immediately of certain specified events?
Trap
Which number represents the most severe level of syslog logging?
0
Which command will backup the configuration that is stored in NVRAM to a TFTP server?
copy startup-config tftp
Which statement describes a feature of site-to-site VPNs?
Internal hosts send normal, unencapsulated packets.
Which VPN solution allows the use of a web browser to establish a secure, remote-access VPN tunnel to the ASA?
clientless SSL
Which two types of VPNs are examples of enterprise-managed remote access VPNs? (Choose two.)
- clientless SSL VPN
- client-based IPsec VPN
When JSON data format is being used, what characters are used to hold objects?
double braces { }
Which two statements describe remote access VPNs? (Choose two.)
- Client software is usually required to be able to access the network.
- Remote access VPNs support the needs of telecommuters and mobile users.
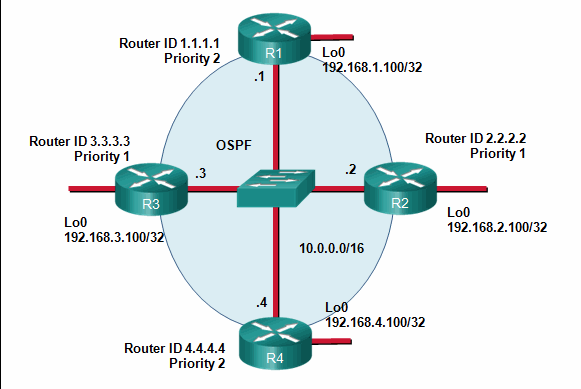
Refer to the exhibit. If the switch reboots and all routers have to re-establish OSPF adjacencies, which routers will become the new DR and BDR?
Router R4 will become the DR and router R1 will become the BDR.
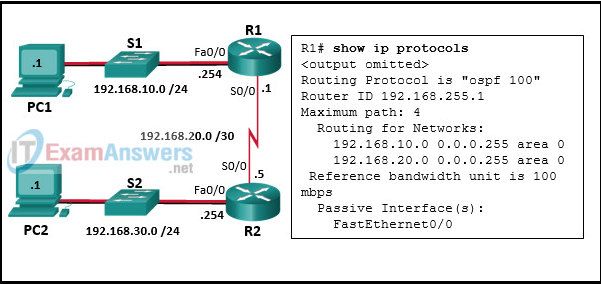
Refer to the exhibit. A network administrator has configured OSPFv2 on the two Cisco routers as shown. The routers are unable to form a neighbor adjacency. What should be done to fix the problem?
Change the IP address on S0/0 of router R2 to 192.168.20.2.
What are the two purposes of an OSPF router ID? (Choose two.)
- to uniquely identify the router within the OSPF domain
- to facilitate router participation in the election of the designated router
Which command will a network engineer issue to verify the configured hello and dead timer intervals on a point-to-point WAN link between two routers that are running OSPFv2?
show ip ospf interface serial 0/0/0
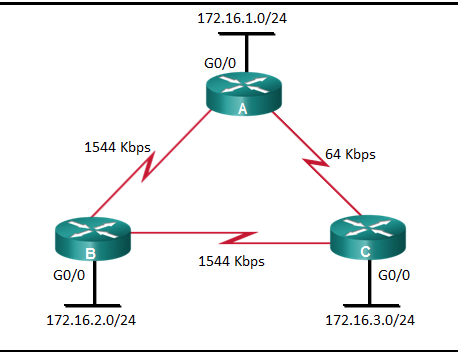
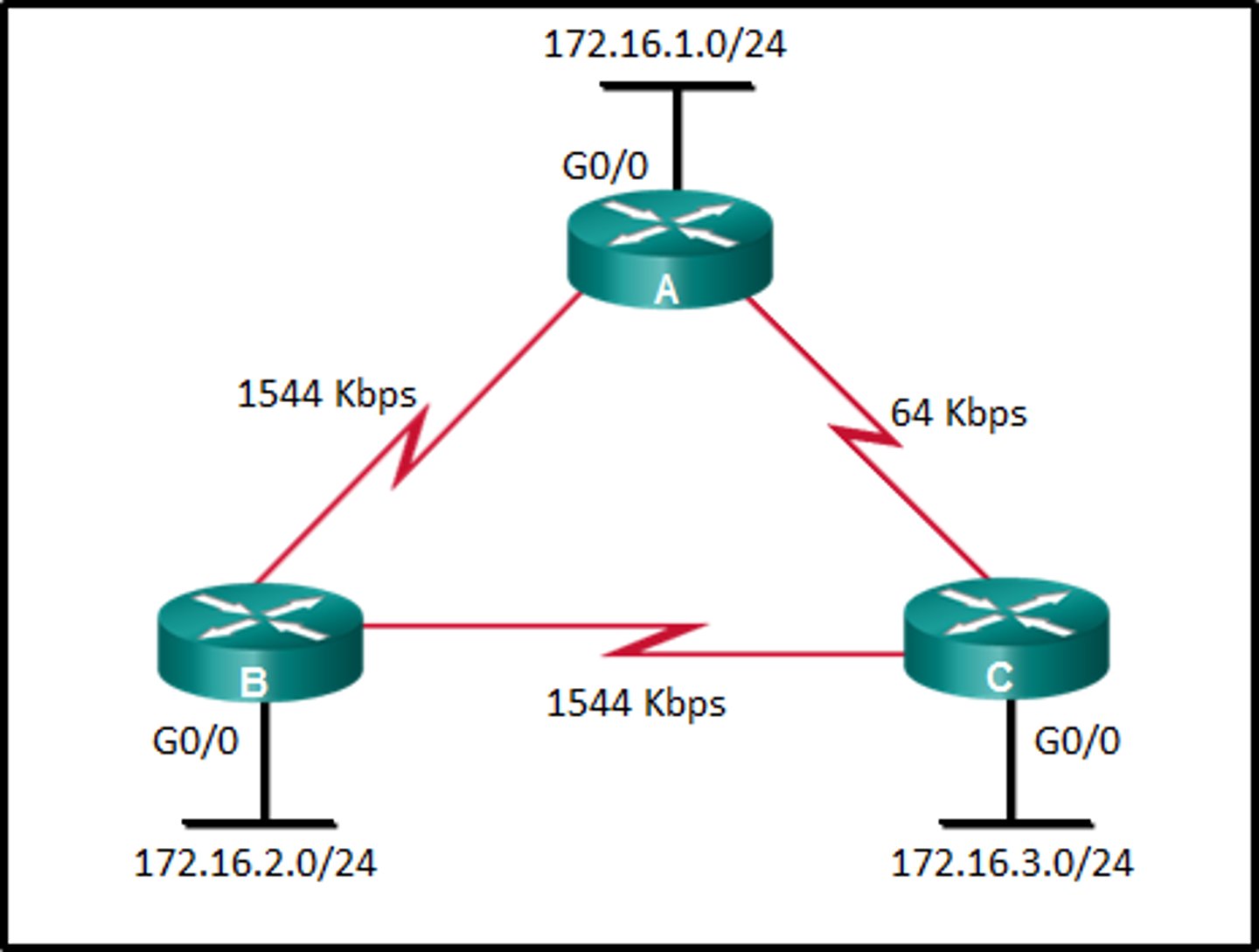
Refer to the exhibit. What is the OSPF cost to reach the router A LAN 172.16.1.0/24 from B?
65
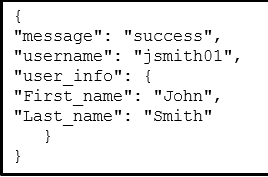
Refer to the exhibit. Which data format is used to represent the data for network automation applications?
YAML
A user is reading a book from the website https://www.books-info.com/author1a/book2.html#page100 . Which part of the web link is called a fragment?
#page100
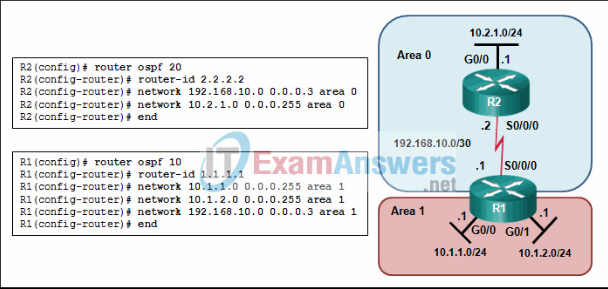
Refer to the exhibit. Why are routers R1 and R2 not able to establish an OSPF adjacency?
The serial interfaces are not in the same area.
A network technician has used the access-list 1 permit 172.16.0.0 0.0.0.255 command to configure NAT on an edge router to translate only four networks, 172.16.0.0 /24, 172.16.1.0 /24, 172.16.2.0 /24, and 172.16.3.0 /24. After receiving complaints about limited access to the Internet, issuing the show ip nat translations command reveals that some networks are missing from the output. Which change will resolve the problem?
The access list should be replaced with access-list 1 permit 172.16.0.0 0.0.3.255
Which type of tool would an administrator use to capture packets that are going to and from a particular device?
protocol analyzer
A user reports that the workstation cannot connect to a networked printer in the office in order to print a report created with word processing software. Which troubleshooting action by the helpdesk technician would follow the divide-and-conquer approach?
Ask the user to issue the ipconfig command
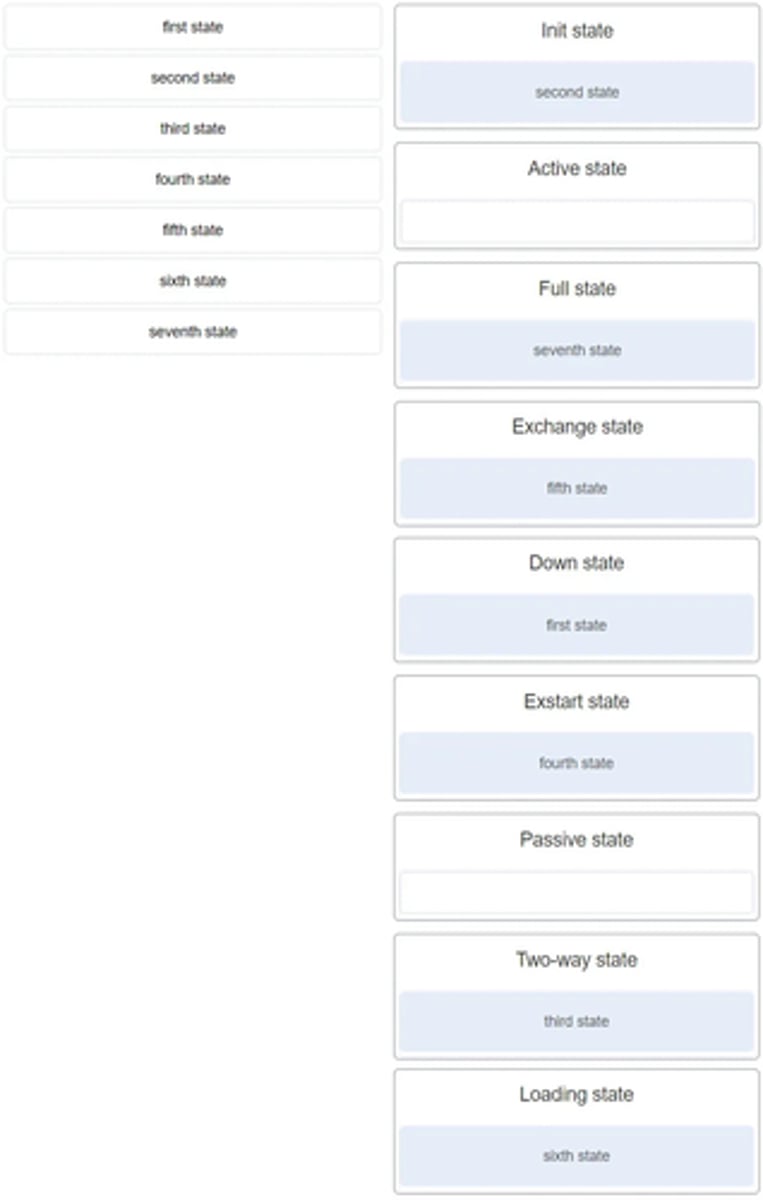
Match the OSPF state with the order in which it occurs. (Not all options are used.)
When an OSPF network is converged and no network topology change has been detected by a router, how often will LSU packets be sent to neighboring routers?
every 30 minutes
Which type of OSPFv2 packet contains an abbreviated list of the LSDB of a sending router and is used by receiving routers to check against the local LSDB?
database description
Which step in the link-state routing process is described by a router building a link-state database based on received LSAs?
building the topology table
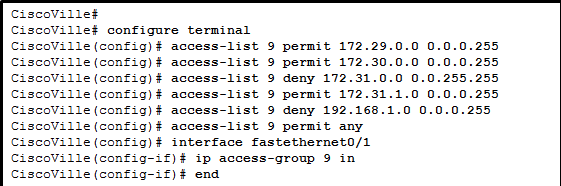
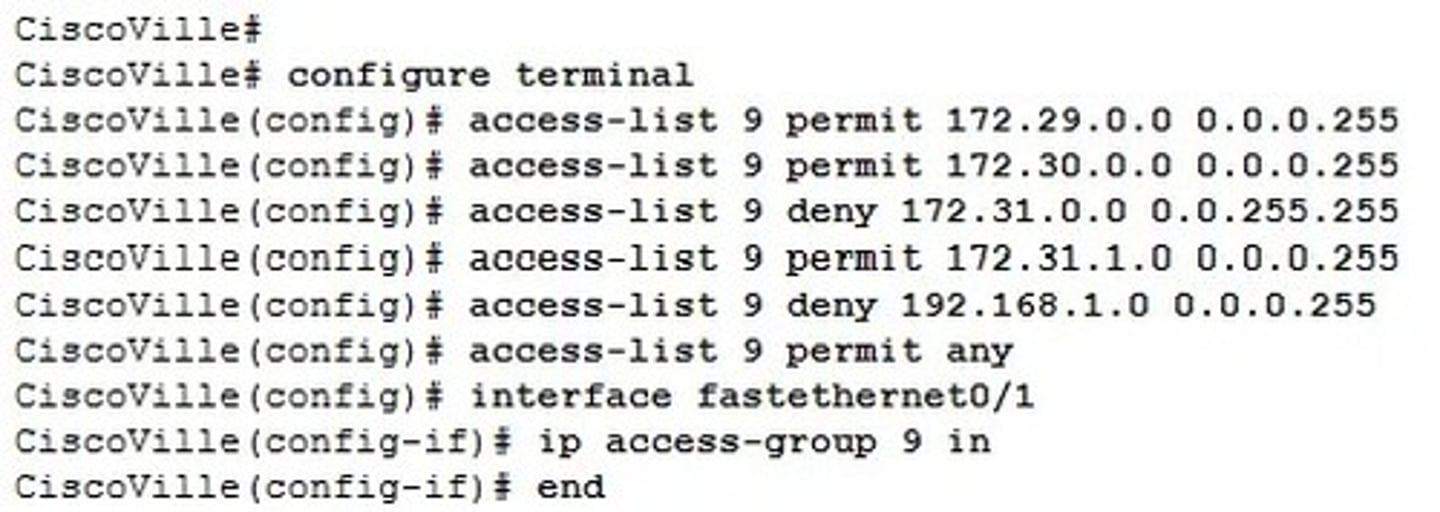
Refer to the exhibit. A network administrator has configured ACL 9 as shown. Users on the 172.31.1.0 /24 network cannot forward traffic through router CiscoVille. What is the most likely cause of the traffic failure?
The sequence of the ACEs is incorrect.
A technician is tasked with using ACLs to secure a router. When would the technician use the access-class 20 in configuration option or command?
to secure administrative access to the router
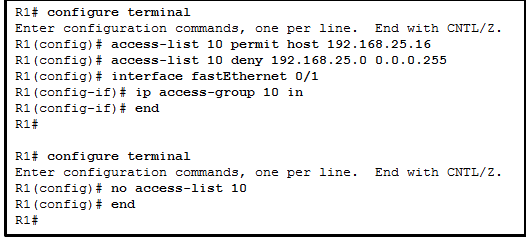
Refer to the exhibit. A network administrator is configuring a standard IPv4 ACL. What is the effect after the command no access-list 10 is entered?
ACL 10 is removed from the running configuration.
An administrator has configured an access list on R1 to allow SSH administrative access from host 172.16.1.100. Which command correctly applies the ACL?
R1(config-line)# access-class 1 in
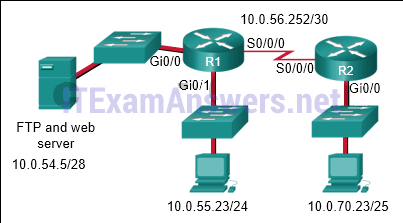
Refer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server.
Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)
- access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq wwwaccess-list 105 deny ip any host 10.0.54.5access-list 105 permit ip any any
- R1(config)# interface gi0/0R1(config-if)# ip access-group 105 out
What is a feature of an IPS?
It can stop malicious packets.
Which type of security threat can be described as software that attaches itself to another program to execute a specific unwanted function?
virus
What is the significant characteristic of worm malware?
A worm can execute independently of the host system.
What is the best description of Trojan horse malware?
It appears as useful software but hides malicious code.
What is the function of ASICs in a multilayer switch?
They streamline forwarding of IP packets in a multilayer switch by bypassing the CPU.
What is the port density of a switch?
the number of available ports on a switch
What is a difference between the functions of Cloud computing and virtualization?
Cloud computing separates the application from the hardware whereas virtualization separates the OS from the underlying hardware.
Why would a network administrator use the config-register 0x2102 command on a Cisco network device?
to ensure that the device loads the startup configuration file during startup
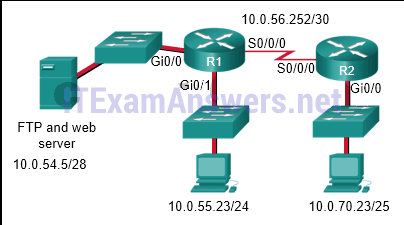
Refer to the exhibit. The network administrator that has the IP address of 10.0.70.23/25 needs to have access to the corporate FTP server (10.0.54.5/28). The FTP server is also a web server that is accessible to all internal employees on networks within the 10.x.x.x address. No other traffic should be allowed to this server. Which extended ACL would be used to filter this traffic, and how would this ACL be applied? (Choose two.)
- access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 20access-list 105 permit tcp host 10.0.70.23 host 10.0.54.5 eq 21access-list 105 permit tcp 10.0.0.0 0.255.255.255 host 10.0.54.5 eq wwwaccess-list 105 deny ip any host 10.0.54.5access-list 105 permit ip any any
- R1(config)# interface gi0/0R1(config-if)# ip access-group 105 out