Web Filtering - CompTIA Security+ SY0-701 - 4.5
1/7
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
8 Terms
Content Filtering
• Control traffic based on data within the content
- URL filtering, website category filtering
• Corporate control of outbound and inbound data
- Sensitive materials
• Control of inappropriate content
- Not safe for work
- Parental controls
• Protection against evil
- Anti-virus, anti-malware
URL Scanning
• Allow or restrict based on Uniform Resource Locator
- Also called a Uniform Resource Identifier (URI)
- Allow list / Block list
• Managed by category
- Auction, Hacking, Malware,
- Travel, Recreation, etc.
• Can have limited control
- URLs aren't the only way to surf
• Often integrated into an NGFW
- Filters traffic based on category or specific URL
Agent based
Install client software on the user's device
- Usually managed from a central console
Users can be located anywhere
- the local agent makes the filtering decisions
- Always on, always filtering
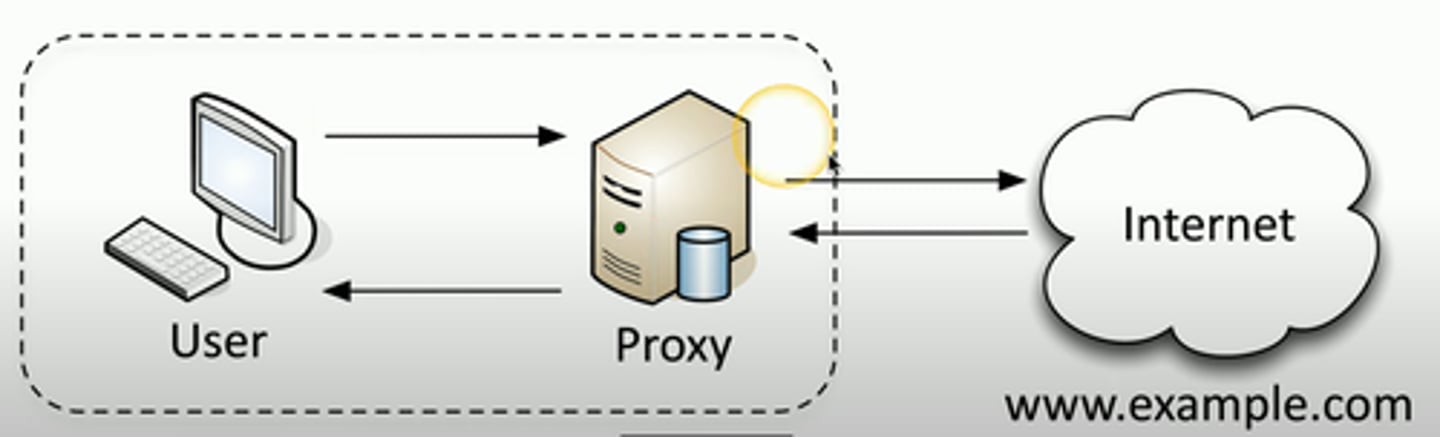
Proxies
• Sits between the users and the external network
• Receives the user requests and sends the request
on their behalf (the proxy)
• Useful for caching information, access control,
URL filtering, content scanning
• Applications may need to know
how to use the proxy (explicit)
• Some proxies are invisible (transparent)
Forward Proxy
• A centralized "internal proxy"
- Commonly used to protect and control user
access to the Internet
Block rules
• Based on specific URL
- *.professormesser.com: Allow
• Category of site content
- Usually divided into over 50 different topics
- Adult, Educational, Gambling, Government,
Home and Garden, Legal, Malware, News, etc.
• Different dispositions
- Educational: Allow
- Home and Garden: Allow and Alert
- Gambling: Block
Reputation
Filters URLs based on perceived risk
- A good reputation is allowed
- A bad reputation is blocked
- Risk: Trustworthy, low risk, medium risk, suspicious, High risk
Automated reputation
- Sites are scanned and assigned a reputation
Manual reputation
- Managers can administratively assign a rep
DNS Filtering
Before connecting to a website, get the IP Address
- Perform a DNS lookup
DNS is updated with real time threat intelligence
- Both commercial and public lists
Harmful sites are not resolved
- No IP address, no connection
This works for any DNS lookup