Content Area 4: Legislation
0.0(0)Studied by 8 people
Card Sorting
1/58
Earn XP
Description and Tags
Last updated 1:49 PM on 4/18/23
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
59 Terms
1
New cards
4\.1.1 What act provides guidance to employers and employees when working with computer systems
The Health and Safety at Work Act
2
New cards
4\.1.1 What is the main law covering the use of computer equipment
Health and Safety \[Display Screen Equipment\]
3
New cards
4\.1.1 What does DSR mean
Display screen regulations
4
New cards
4\.1.1 Give examples of a healthy general working environment
Good ventilation
Reasonable working temperature
Appropriate waste containers
Safe work environment
Reasonable working temperature
Appropriate waste containers
Safe work environment
5
New cards
4\.1.1 Who’s responsibility is it to report risks in the workplace
Employees role to report risks and it’s the employers responsibilities to identify risks and keep employees safe
6
New cards
4\.1.1 How is office places good for health and safety?
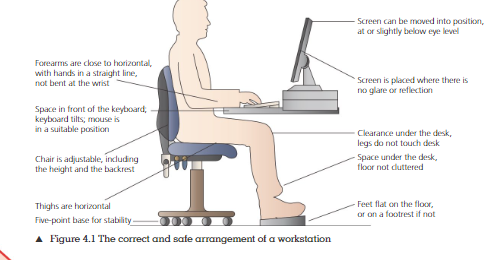
7
New cards
4\.1.2 What is the Data Protection Act 2018?
Attempts to control how personal data and information is used by organisations, businesses and the UK Gov.
8
New cards
4\.1.2 What is personal data?
Any information relating to an identified or identifiable living individual
9
New cards
4\.1.2 What information does the DPA provide protection to?
Race
Ethical background
Health
Genetics
Sex life / orientation
Political opinions
Ethical background
Health
Genetics
Sex life / orientation
Political opinions
10
New cards
4\.1.2 What is the GDPR?
provides a legal framework for keeping everyone's personal data safe by requiring companies to have robust processes in place for handling and storing personal information.
11
New cards
4\.1.2 Under what acts should consent be given before a marketing message is sent
The DPA and GPR
12
New cards
4\.1.2 How must the marketing consent be provided?
Knowingly, freely given, clear and specific
13
New cards
4\.1.2 What Act covers how the consent should be given?
The Privacy and Electronics Communications Regulations
14
New cards
4\.1.2 Examples of how the consent can be given
Tick box, positivbe action, clicking an icon and or sending an email.
15
New cards
4\.1.2 What is consenting called
Opt into reciving marketing
16
New cards
4\.1.2 What is the refusal of consent called
Opting out
17
New cards
4\.1.2 What are the two tiers of penalties that can be issued by the ICO \[enforcement\]
Maximum
Standard maximum
Standard maximum
18
New cards
4\.1.2 What does the higher maximum penalty apply
If failure to comply with the DPA principles there is a 17.5million or 4% of total anual turnover. \[Whatever is higer\]
19
New cards
4\.1.2 What does the higher maximum penalty apply to ?
Failure to comply with the core data protection principles or individual rights.
20
New cards
4\.1.2 What does the standard maximum penalty apply to ?
£8.7 million or 2% of worldwide turnover \[whatever is higheer\]
21
New cards
4\.1.2 7 principles of the DPA
* lawfulness. fairness and transparency
* purpose limitation
* data minimization
* accuracy
* storage limitation
* integrity and confidentiality
* accountability
* purpose limitation
* data minimization
* accuracy
* storage limitation
* integrity and confidentiality
* accountability
22
New cards
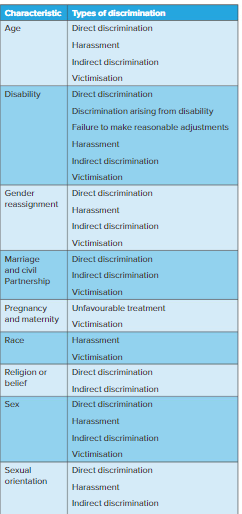
4\.1.2 Types of discrimination
Age
Disability
Gender reassignment
Marriage and civil partnership
pregnancy and maternirty
race
religion or belief
sex
sexual orientation
Disability
Gender reassignment
Marriage and civil partnership
pregnancy and maternirty
race
religion or belief
sex
sexual orientation
23
New cards
4\.1.2 What are my rights as the data sbject?
To be informed about how the data is being used
Access personal data
Have incorrect data updated
Have data erased
Stop or restrict thier processing of the data
Data portability
Object to how the data is processed in certain circumstances
\
Access personal data
Have incorrect data updated
Have data erased
Stop or restrict thier processing of the data
Data portability
Object to how the data is processed in certain circumstances
\
24
New cards
4\.1.3 What is Computer Misuse Act
The act of accessing or modifying data stored on a computer system without consent
25
New cards
4\.1.3 What are the consequences of breaking the CMA
Unauthorised access to computer material = a max fine of £5,000 and or 6 months max in prison
Unauthorised access with intent to commit a crime = Unlimited fine, max 5 years in prison
Unathroised modiciation of data = Unlimited fine and max 5 years in prison
Unauthorised access with intent to commit a crime = Unlimited fine, max 5 years in prison
Unathroised modiciation of data = Unlimited fine and max 5 years in prison
26
New cards
what does hacking mean?
finding out weaknesses in an established system and exploiting them
27
New cards
what are the 3 main types of hacking that can take place?
* white hat = where the hacker is given permission to hack into systems to identify any vulnerabilities
* grey hat = where the hacker hacks into computer systems for fun or to troll but does not have malicious intent towards the computer system.
* black hat = where the hacker hacks into a computer system with malicious intent
* grey hat = where the hacker hacks into computer systems for fun or to troll but does not have malicious intent towards the computer system.
* black hat = where the hacker hacks into a computer system with malicious intent
28
New cards
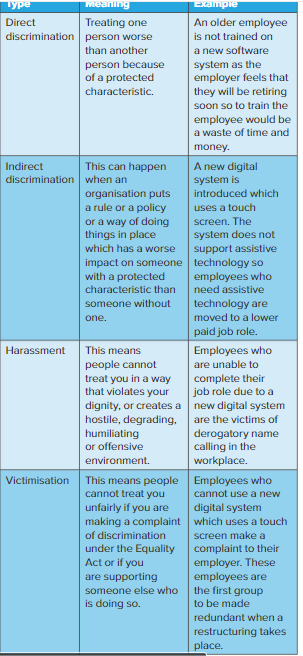
4\.1.3 How can individuals be discriminated against
Direct Discrimination
Indirect Discrimination
Harassments
Victimisation
Indirect Discrimination
Harassments
Victimisation
29
New cards
name 3 types of malware
* bug: connected to software and are flaws that produce an unwanted outcome
* ransomware: holds a computer system captive and demands a ransom
* spyware: collect data from an infected computer
* worm: a computer program that replicates itself so it can spread to other computers
* virus: attempts to make a computer system unreliable
* ransomware: holds a computer system captive and demands a ransom
* spyware: collect data from an infected computer
* worm: a computer program that replicates itself so it can spread to other computers
* virus: attempts to make a computer system unreliable
30
New cards
4\.1.4 How people can be discriminated against?
* Direct discrimination: treating one person worse than another person because of a protected characteristics
* indirect discrimination: this can happen when an organisation puts a rule or a policy or a way of doing things in place which has a worse impact on someone with a protected characteristic than someone without one
* Harassments: people cannot treat you in a way that violates your dignity.
* Victimisation: people cannot treat you unfairly if you are making a complaint of discrimination under the equality act
* indirect discrimination: this can happen when an organisation puts a rule or a policy or a way of doing things in place which has a worse impact on someone with a protected characteristic than someone without one
* Harassments: people cannot treat you in a way that violates your dignity.
* Victimisation: people cannot treat you unfairly if you are making a complaint of discrimination under the equality act
31
New cards
4\.1.4 Where are individuals protected?
In the wider society and the workplace
32
New cards
4\.1.5 What are the two types of design protections in the Intellectual Property Act 2014
Unregistered Design Right Protection
Registered Design Right Protection
Registered Design Right Protection
33
New cards
4\.1.5 What is the difference between the unregistered designs and registered
Registered - Gives full control over the design
Unregistered - Gives the ability to prevent others from copying the design
\
\[The level of protection for unregistered is lower than registered\]
Unregistered - Gives the ability to prevent others from copying the design
\
\[The level of protection for unregistered is lower than registered\]
34
New cards
4\.1.5 What is a patent?
The grant to an owner of a design the legal right to stop others from making, using or selling it for a specific number of years
35
New cards
4\.1.6 What are the types of monitoring electronic communication devices?
Email
Computer screens
Phones
Internet / Apps
Computer screens
Phones
Internet / Apps
36
New cards
4\.1.6 What can employee monitoring do?
Track attendance
Measure productivity
Ensure security
Collect proof of hours worked
Measure productivity
Ensure security
Collect proof of hours worked
37
New cards
4\.1.6 What act allows employers to monitor employees without consent.
The Telecommunications Regulations 2000
38
New cards
4\.1.6 What is work place monitoring?
The enabling of an employer to track employee activities and monitor the engagement with work-related tasks
39
New cards
4\.1.6 What details does the Telecommunications Regulations 2000 include
If/how users are being monitored
If personal emails and calls are not allowed
The acceptable number of personal emails and phone calls
If personal emails and calls are not allowed
The acceptable number of personal emails and phone calls
40
New cards
4\.1.6 Why would employers want to monitor electronic communications
Identify criminal activity
Investigate allegations
Check if employees are working to necessary standers
Ensure employees are not abusing work system
Investigate allegations
Check if employees are working to necessary standers
Ensure employees are not abusing work system
41
New cards
4\.1.6 Advantages of using monitoring software in the workplace
Productive employees can be identified and rewarded
Delivery drivers can be tracked to ensure their safety
Delivery drivers can be tracked to ensure their safety
42
New cards
4\.1.6 Disadvantages of using monitoring software in the workplace
Employees can feel that they are not trusted and that they monitoring is an invasion of privacy
Employee morale may reduce due to the invasion of privacy
Stress levels increased
Employee morale may reduce due to the invasion of privacy
Stress levels increased
43
New cards
4\.1.6 What is secret monitoring
The monitoring of employees without telling them
44
New cards
4\.1.6 Methods of secret monitoring
Hidden audio devices
Hidden cameras
Hidden cameras
45
New cards
4\.1.7 What are the international legislations relating to digital systems?
European Convection on Human Rights
Electronic Communications Privacy Act
Controlling the Assault of Non-Solicited Pornography and Marketing
Electronic Communications Privacy Act
Controlling the Assault of Non-Solicited Pornography and Marketing
46
New cards
4\.1.7 What is the ECPA?
The Electronic communications privacy.
47
New cards
4\.1.7 What is the CAN-SPAM?
another piece of US legislation and relates to the use of a digital system to send unsolicited commercial email
48
New cards
4\.2.1 What are the main code of conducts related to professional bodies for the use of digital
The British Computer Society
The institute of Analysts and programmers
\
The institute of Analysts and programmers
\
49
New cards
what are the british computer society (BCS) code of conduct
* public interest- you shall have due regard for public health, privacy, security and wellbeing of others and the environment
* professional competence and integrity - you shall NOT claim any level of competence that you do not possess
* duty to the relevant authority- you shall seek to avoid any situation that may give rise to a conflict of interest between you and your relevant authority
* duty to the profession - you shall encourage and support fellow members in their professional development
* professional competence and integrity - you shall NOT claim any level of competence that you do not possess
* duty to the relevant authority- you shall seek to avoid any situation that may give rise to a conflict of interest between you and your relevant authority
* duty to the profession - you shall encourage and support fellow members in their professional development
50
New cards
what are the institution of analysts and programmers code of conduct
* duties to the public - ensure that due regard is paid health and safety
* duties to the profession: conduct themselves as professionals at all times or they will tarnish their reputation
* duties to the institution of analysts and programmers - conduct themselves honorably in the practice of their profession
* duties to clients/employers: work with proper care and regard for the requirements of the client/employer
* duties to the profession: conduct themselves as professionals at all times or they will tarnish their reputation
* duties to the institution of analysts and programmers - conduct themselves honorably in the practice of their profession
* duties to clients/employers: work with proper care and regard for the requirements of the client/employer
51
New cards
what is the difference between a code of conduct and a code of practice
* a code of conduct is a set of guidelines that sets out actions that members may or are advised to follow
* a code of practice makes these guidelines mandatory
* a code of practice makes these guidelines mandatory
52
New cards
what are the other areas covered by a code of practice and explain them
* professional responsibilities= quality of work, meeting deadlines, communication and confidentiality
* contribution to society = how actions have an impact on society
* safety = the commitment t ensure that when carrying out work, all steps are taken to protect the health and safety of those involved
* security and privacy = where data and information will be stored, what processes should be used to maintaining the security
* innovation = e.g who has ownership of the outcomes of any tasks undertaken by employees
* contribution to society = how actions have an impact on society
* safety = the commitment t ensure that when carrying out work, all steps are taken to protect the health and safety of those involved
* security and privacy = where data and information will be stored, what processes should be used to maintaining the security
* innovation = e.g who has ownership of the outcomes of any tasks undertaken by employees
53
New cards
4\.2.3 what are the environmental impacts of implementing guidelines from professional codes of practice on organizations and their stakeholders
* improved environmental management systems
* increased energy efficiency and reduced resource consumption.
* help to ensure that organizations are adhering to environmental regulations, reducing waste and pollution, and taking steps to protect the environment.
* increased energy efficiency and reduced resource consumption.
* help to ensure that organizations are adhering to environmental regulations, reducing waste and pollution, and taking steps to protect the environment.
54
New cards
4\.2.3 what are the ethical impacts of implementing guidelines from professional codes of practice on organizations and their stakeholders
* ensure that everyone involved in the organization is acting responsibly and in the best interests of all stakeholders = lead to increased trust in the organization, improved customer service, better working conditions, and increased employee morale.
* help to reduce potential legal problems and minimize risks associated with malpractice.
* help organizations build a positive corporate culture and create an environment of fairness and respect.
* help to reduce potential legal problems and minimize risks associated with malpractice.
* help organizations build a positive corporate culture and create an environment of fairness and respect.
55
New cards
4\.2.3 what are the legal impacts of implementing guidelines from professional codes of practice on organizations and their stakeholders
* improved compliance with laws and regulations
* improved risk management, and reduced liability.
* help organizations ensure that they are adhering to applicable laws and regulations, as well as industry standards and best practices.
* improved risk management, and reduced liability.
* help organizations ensure that they are adhering to applicable laws and regulations, as well as industry standards and best practices.
56
New cards
4\.2.4 what is ISO
* International Standards Organization is an independent, international, non-governmental organization
* responsible for developing and publishing international standards
* responsible for developing and publishing international standards
57
New cards
4\.2.4 what is WCAG
* Web content Accessibility Guidelines
* to define a standard for web content accessibility that meets the needs of individuals
* to define a standard for web content accessibility that meets the needs of individuals
58
New cards
4\.2.4 what is IETF
* Internet Engineering Task Force is an Internet standards organization.
* responsible for developing and promoting internet standards.
* responsible for developing and promoting internet standards.
59
New cards
4\.2.5 what are the the role of implications of acceptable use policies within an organization
* An AUP is an agreement between employers and employees.
* sets down the rules that a user must agree to for access to a network, email facilities or the internet.
* sets down the rules that a user must agree to for access to a network, email facilities or the internet.