Security Rules - CompTIA Network+ N10-009 - 4.3
1/5
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
6 Terms
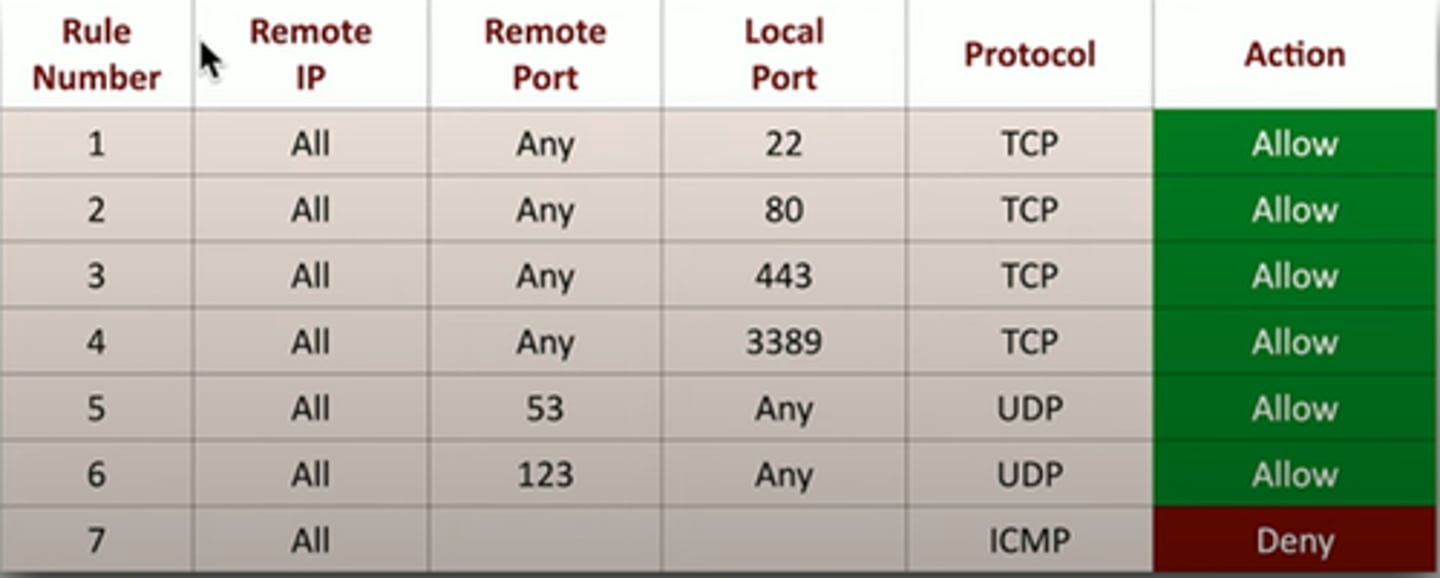
Access Control List
Allow or disallow traffic
- Groupings of categories
- Source IP, destination IP, port number, time of day, applciation, etc
Restrict access to network devices
- Limit by IP address or other identifier
- Prevent regular user / non-admin access
Can be implemented in many ways
- Router, firewall, operating system policies, etc
Firewalls security policies
A logical path
Can be specific or gebneral
Implicit deny
- Most firewalls include a deny at the bottom, even if you didn't put one
URL filtering
Allow or restrict based on URL
- Also called a Uniform Resource Identifier (URI)
- Allow list / block list
Managed by category
- Auction, hacking, malware, travel, recreation, etc
Often integrated in NGFW
Content FIltering
Control traffic based on data within the content
-Data in the packets
Corporate control of outbound and inbound data
-Sensitive materials
Control of inappropriate content
-Not safe for work
-Parental controls
Protection against evil
-Anti-virus, anti-malware
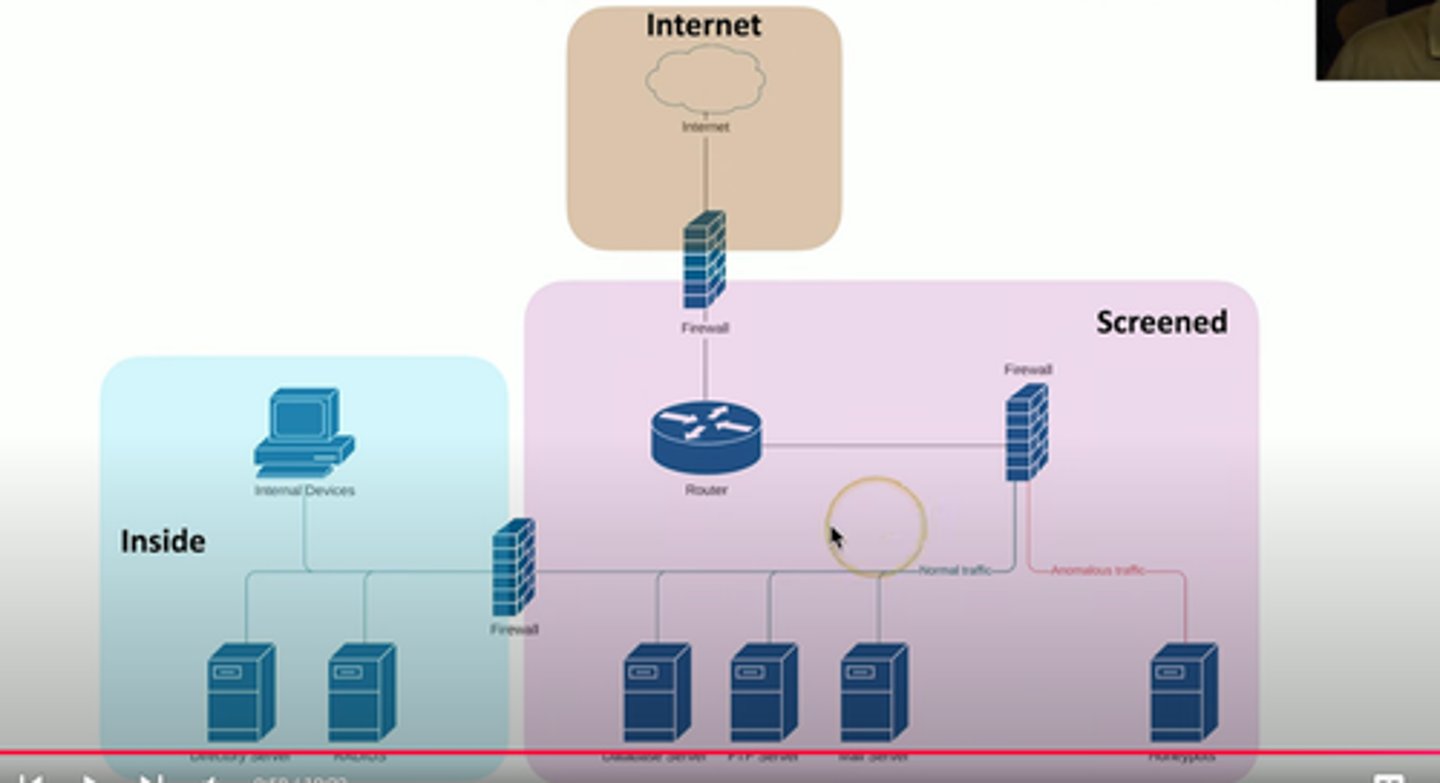
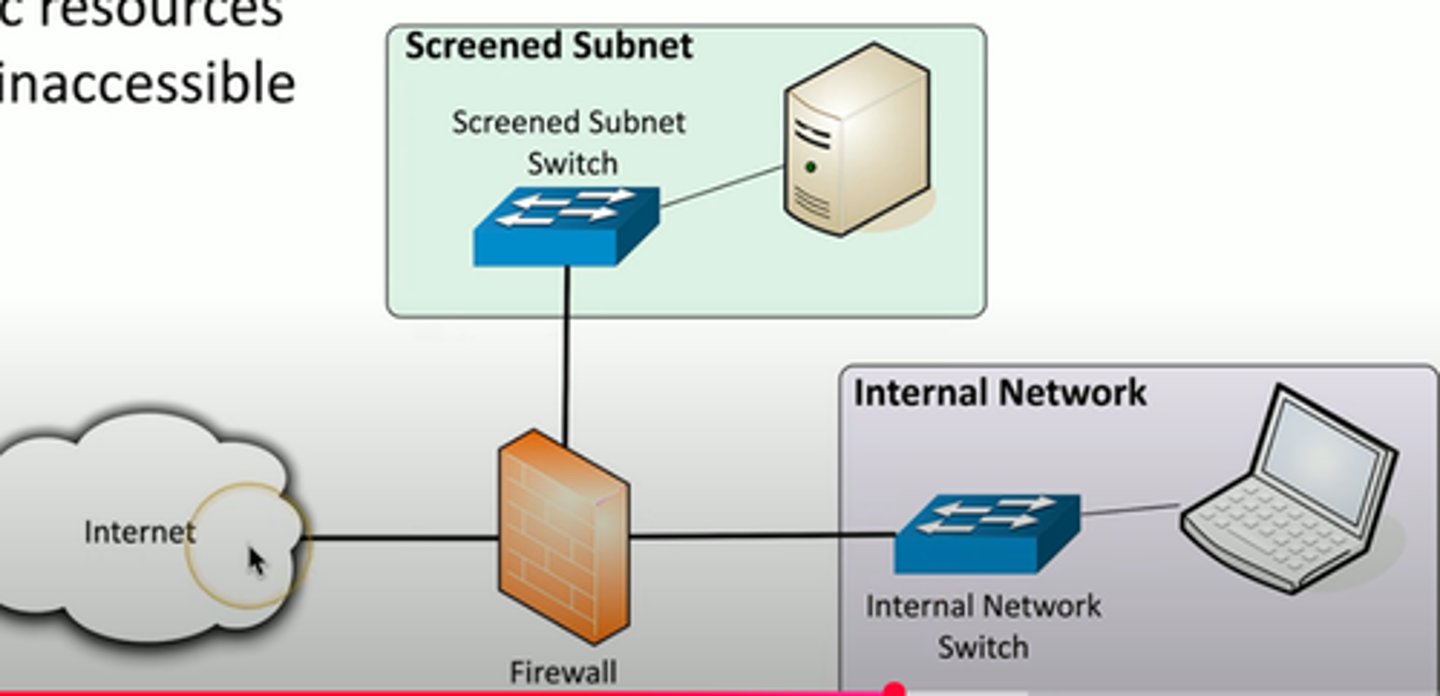
Screened subnet
• An additional layer of security between the you and
the Internet
- Public access to public resources
- Private data remains inaccessible
Security Zones
Zone-based security technologies
-More flexible (and secure) than IP address ranges
Each area of the network is associated with a zone
-Trusted, untrusted
-Internal, external
-Inside, Internet, Servers, Databases, Screened
This simplifies security policies
-Trusted to Untrusted
-Untrusted to Screened
-Untrusted to Trusted