MBAN 504 LEC 3
1/14
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
15 Terms
Centralized Learning
Each dataset sends its information to the cloud in which is stored in a databased, passes through, and gives an output that goes back to each dataset
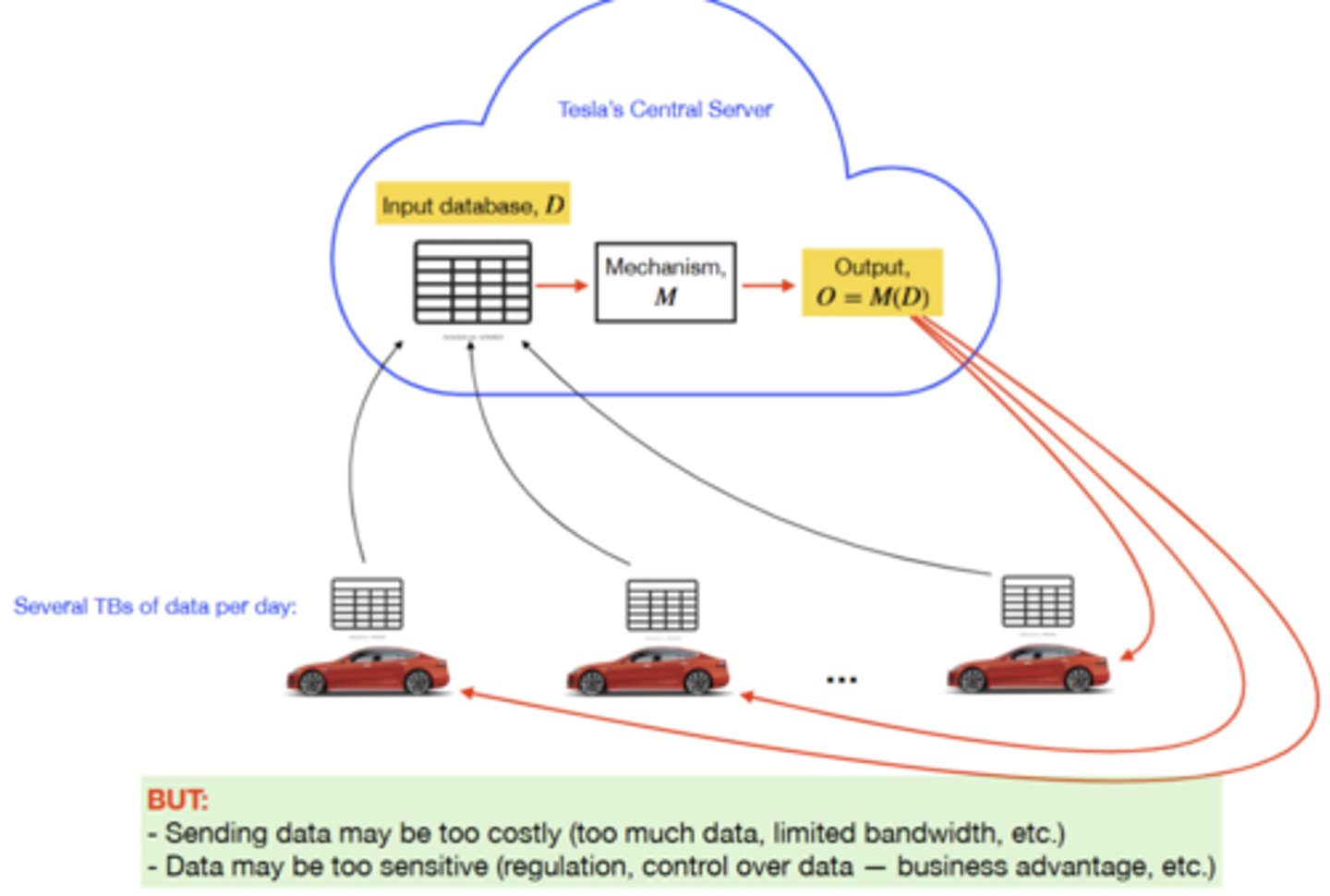
Centralized Learning Issues
Sending data may be to costly in this method. Data may be too sensitive
Fully Decentralized
Instead of going to the cloud any updates will happen internally withing that individual car itself.
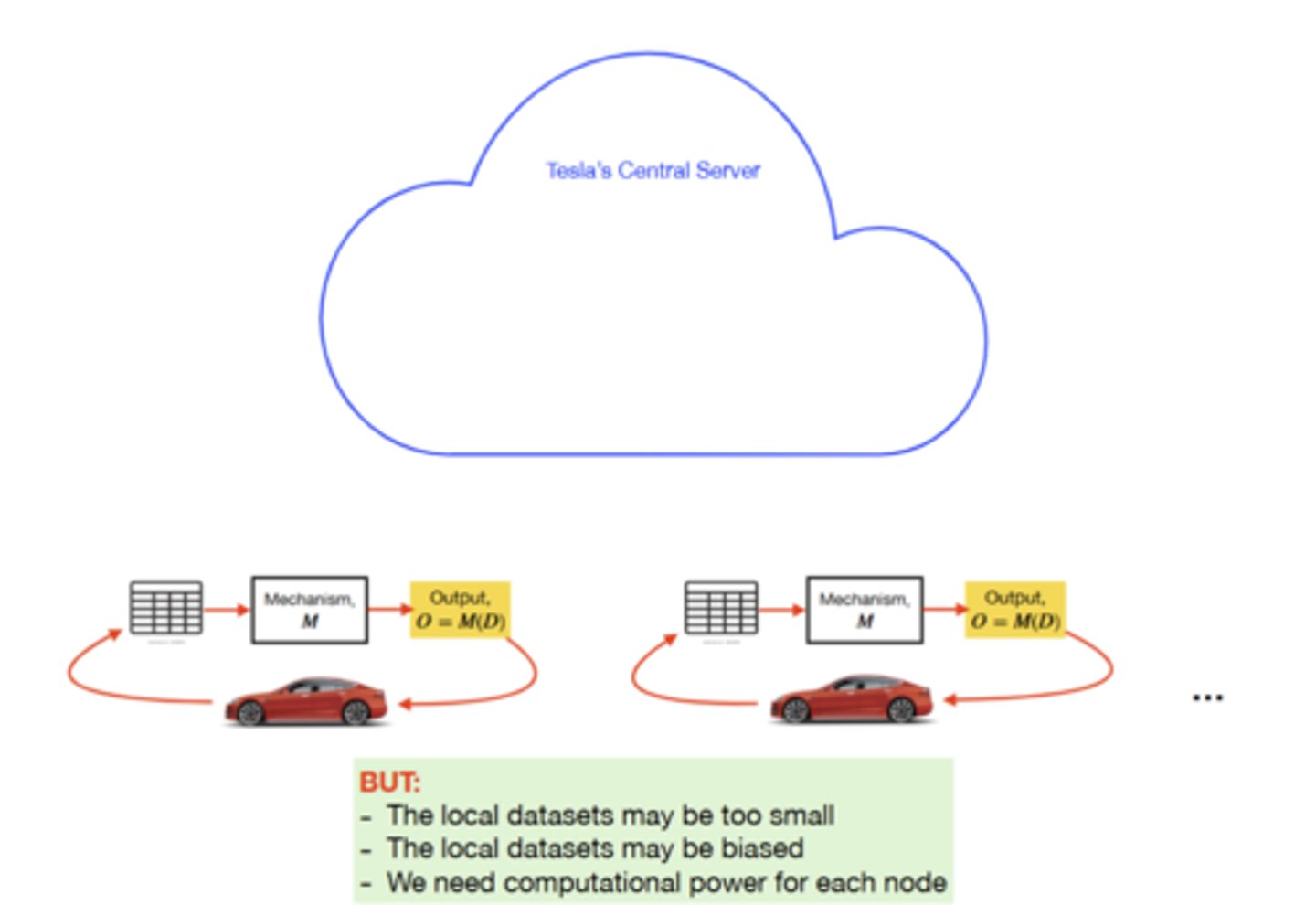
Fully Decentralized Issues
Local dataset may be too small & biased; need computational power for each node.
Federated Learning
A way to train AI models without anyone seeing or touching your data, offering ways to unlock information to feed new AI applications;
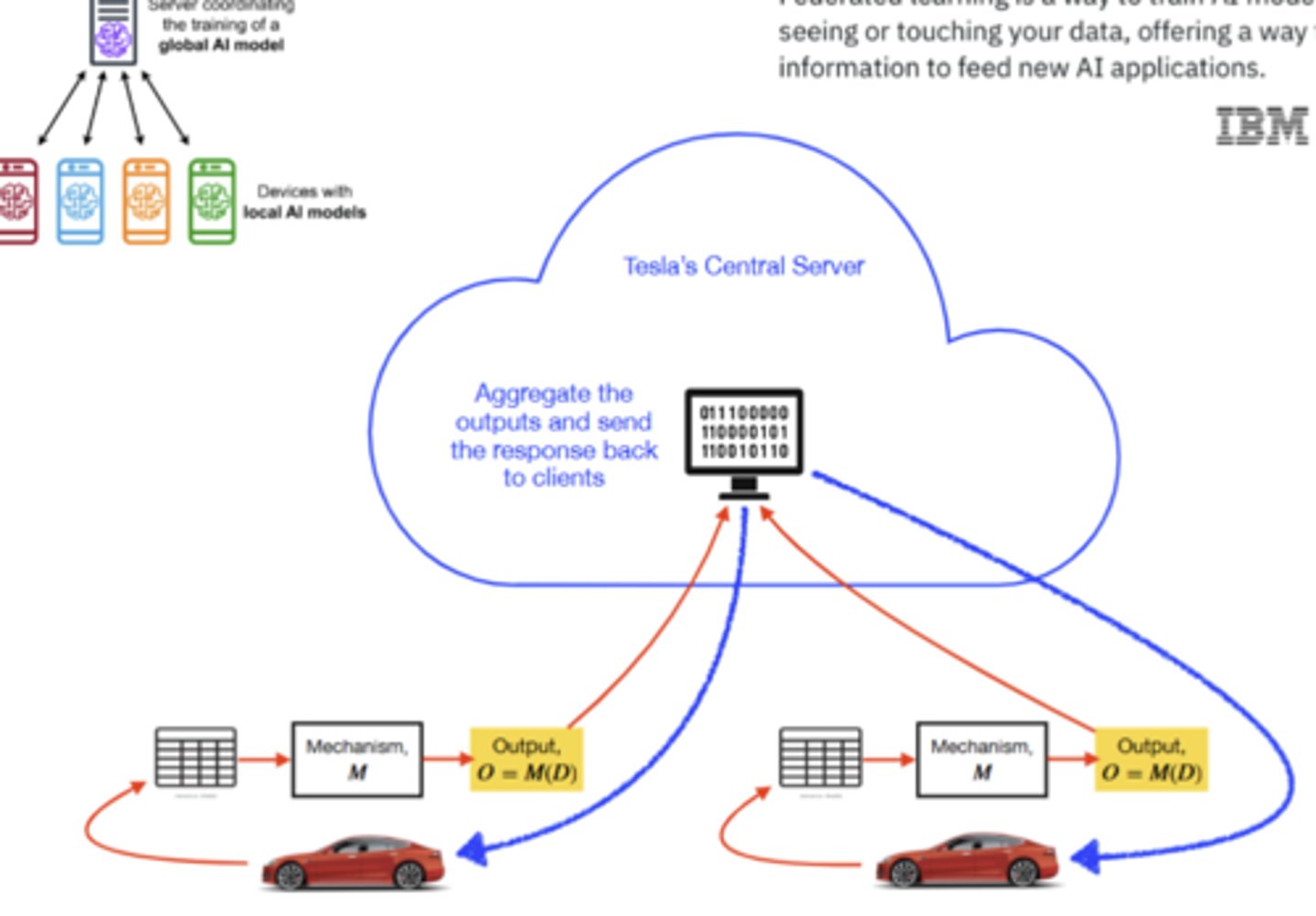
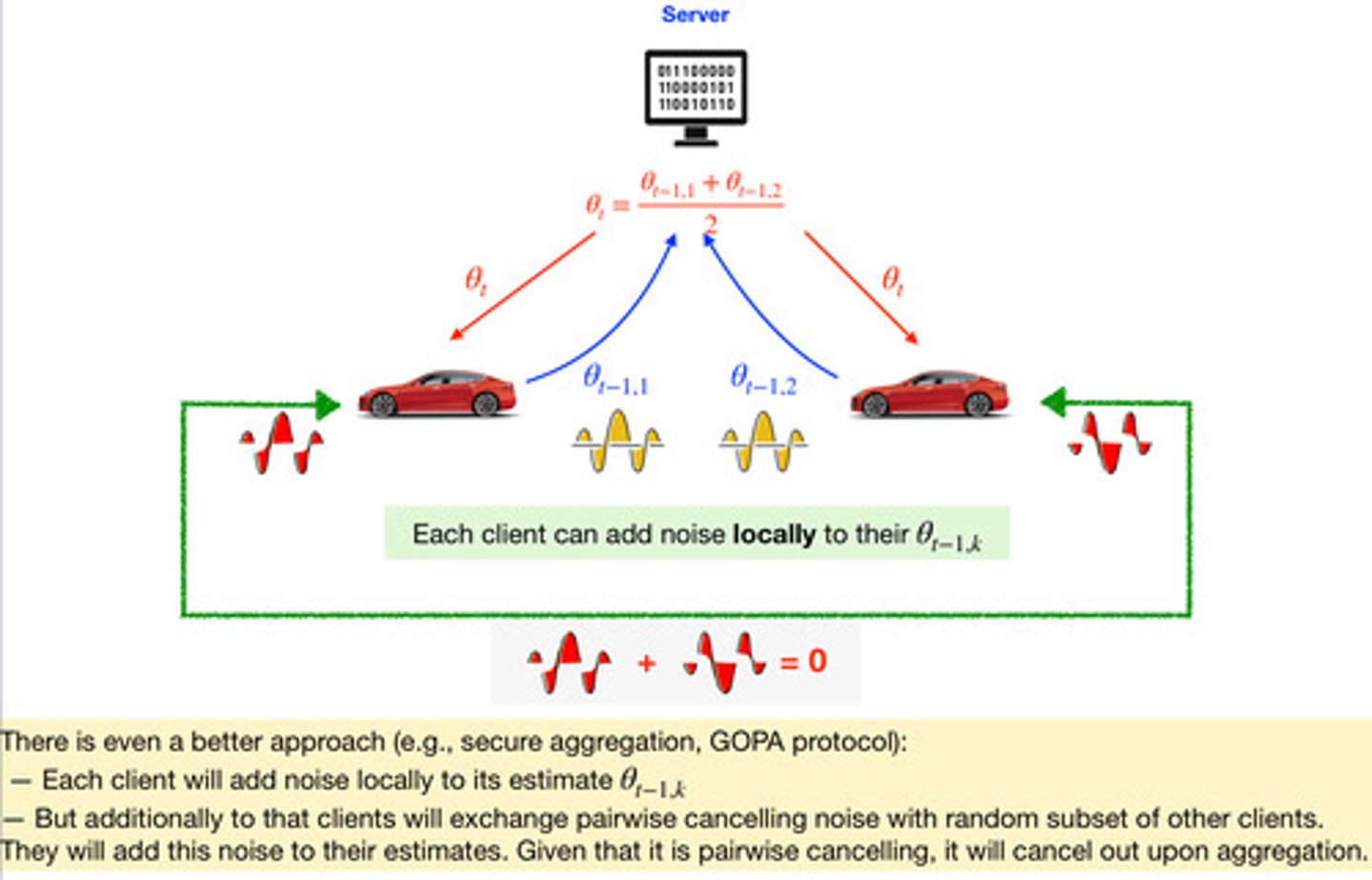
How to preserve privacy in Federated learning?
Add noise; only thing that get sent to the server is the output
Why do we need cyber security?
Protect companies from potential threats, investments in this industry are growing
How do most companies make cyber security decisions?
Usually companies when they start off, do not consider cyber security, but once they get hacked or have something leaked, they done want to think of adding an IT department or adding measures to protect themselves from future, cyber leaks or hacks
What is the cost of a data breach?
Loss of company time ransom loss of customers, overtime for work, lawyers it really depends on the industry
Is cyber security being 100% secure possible?
No, it is not
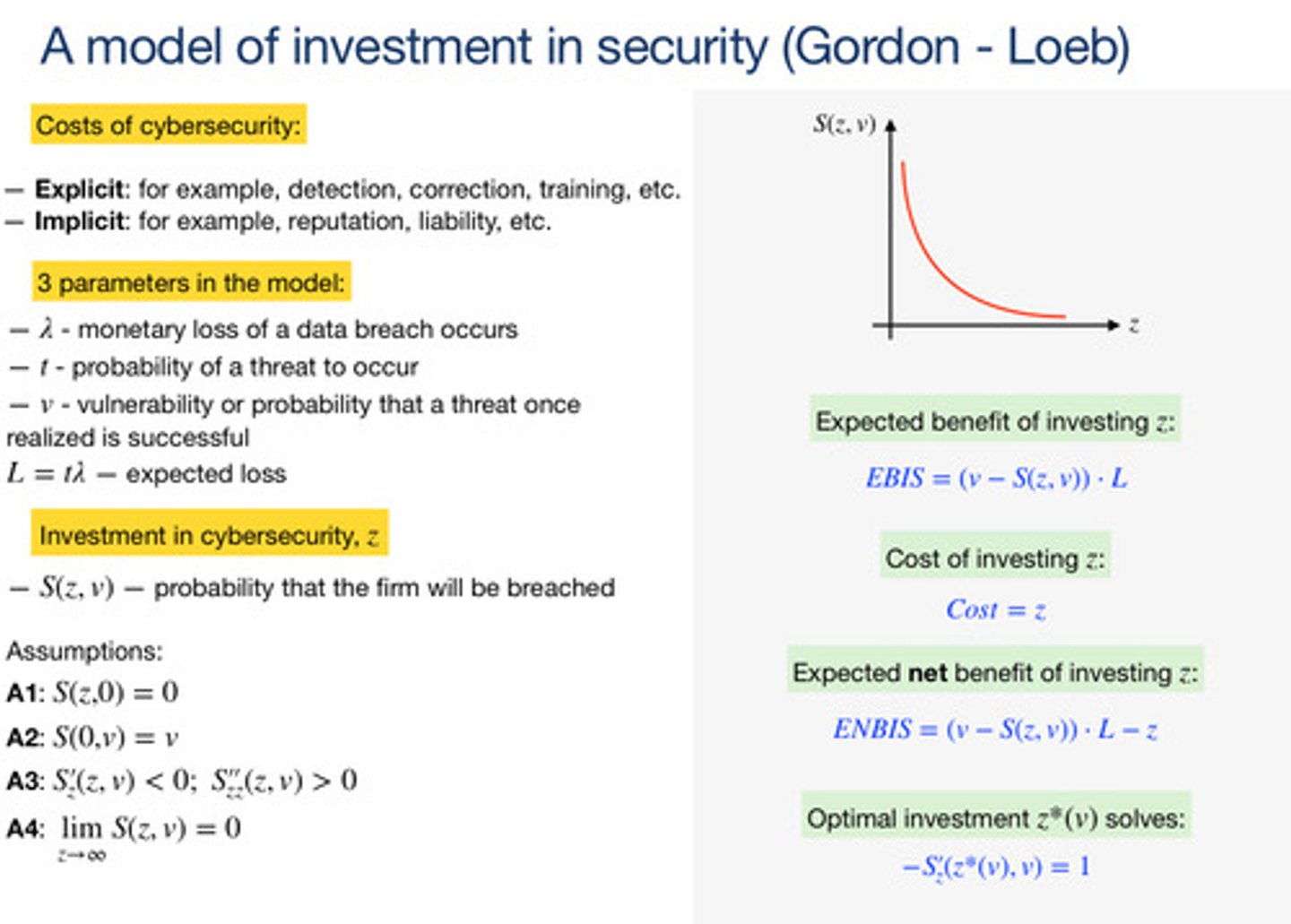
A model of investment in security (Gordon-Loeb)
Explicit costs: detection, correction, training | implicit: reputation liability, etc.
Model parameters
Lambda Monetary loss of a data breach occurs, T probability of a threat to occur, V vulnerability or probability that a threat once realized is successful (L = T(lambda)- expected loss)
When thinking about investments in cyber security
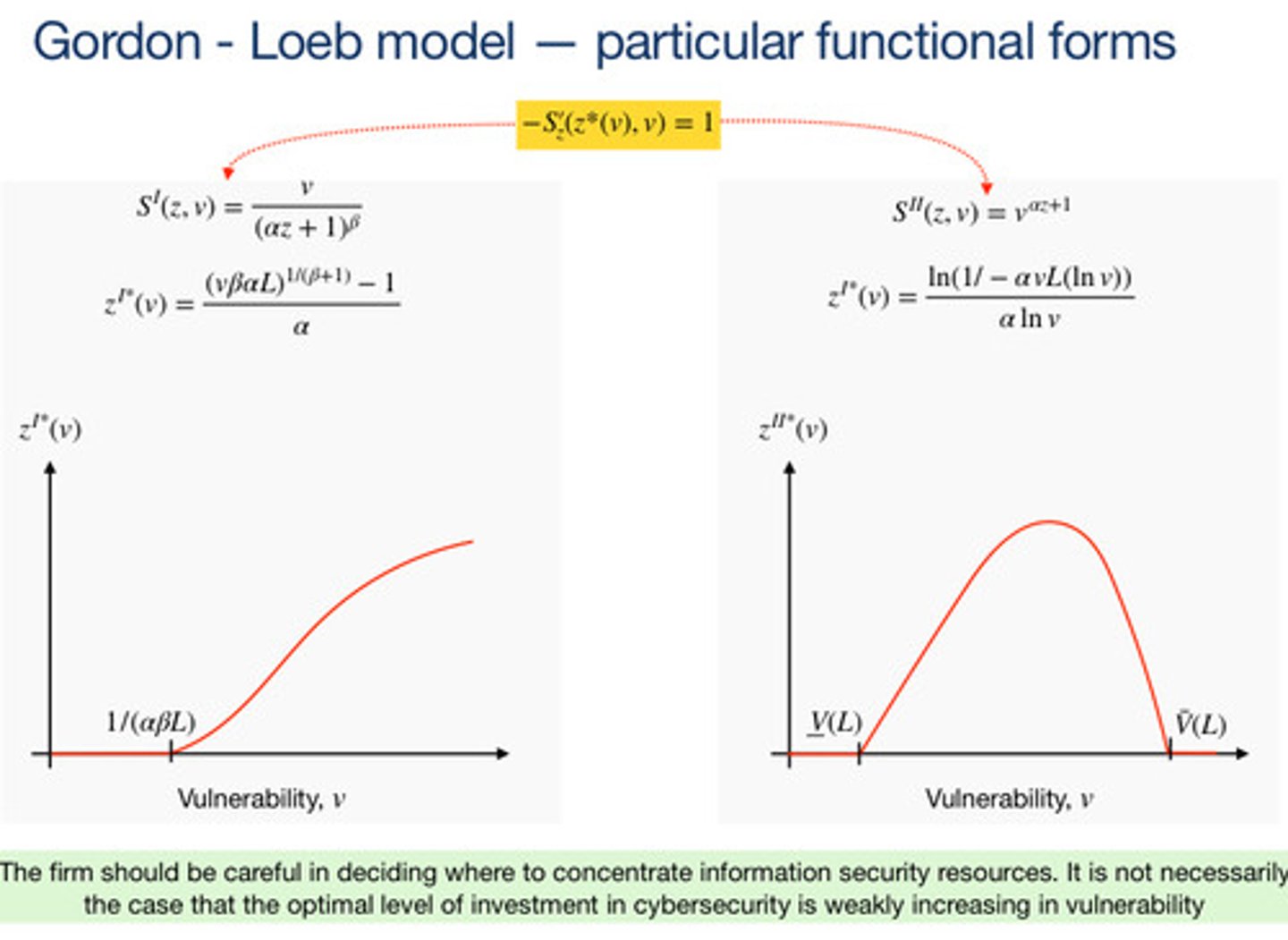
Protecting the least in most vulnerable resources may not be the best strategy. It may be better to focus on the moderately vulnerable resources.
Particular functional forms
A firm should be careful when deciding to where they should concentrate information security resources it's not optimal to invest in weekly, increasing in vulnerability
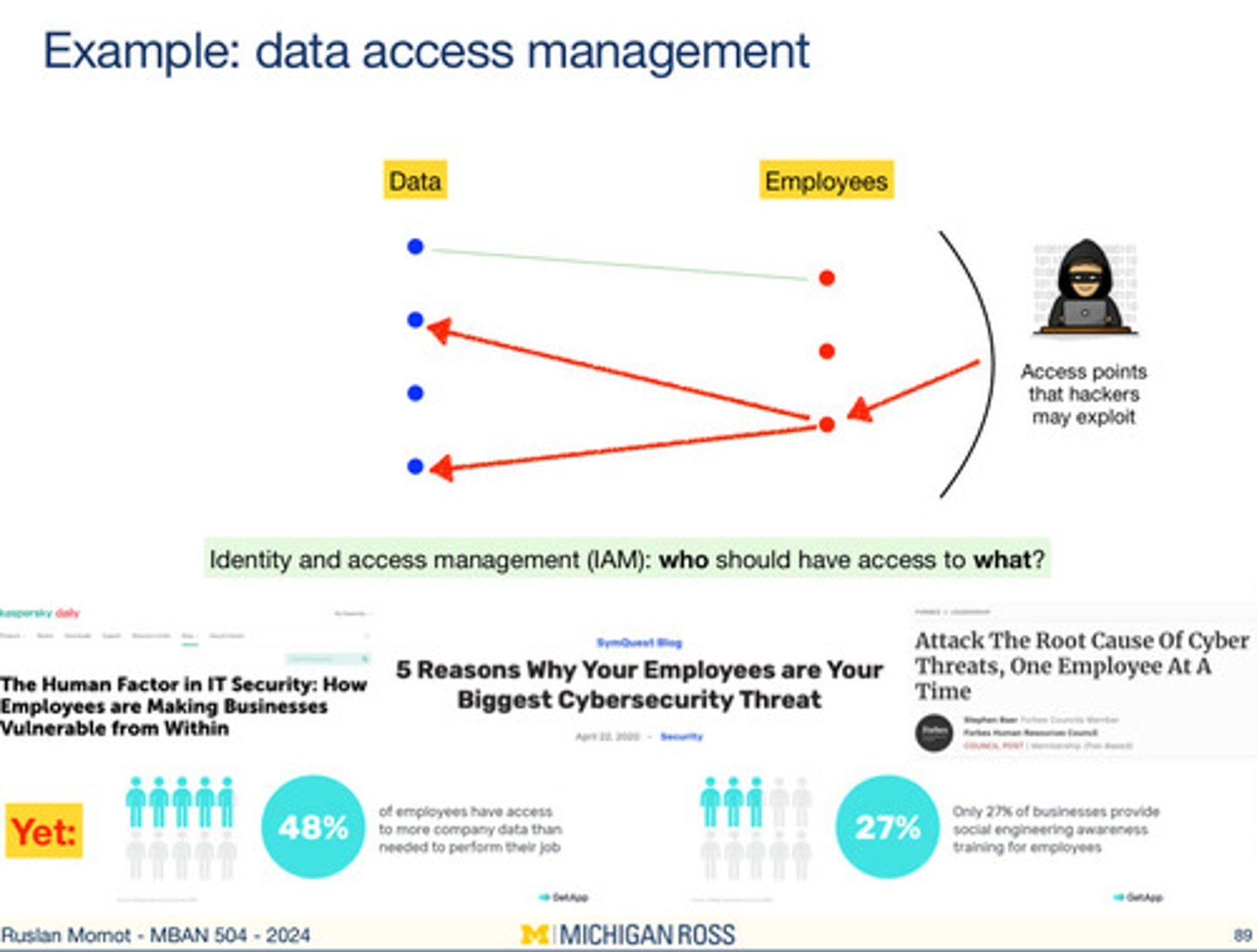
Data access management
Who should have access to what data and information identify the access points we're outside parties could exploit; think of work and how you have to have manager permission to use certain services at work