MBA 506 Corporate Information Systems WWU
1/49
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
50 Terms
Resources like may provide competitive advantage
Brand, scale economies, switching costs, differentiation, network effects, distribution channels, and patents
4 characteristics of sustainable competitive advantage
Valuable, rare, tough to imitate, and non-substitutable
Brand
Is top of mind, represents quality, inspires trust, and likely to be recommended
Scale economies
Large fixed costs, high volumes of production, may provide bargaining power with suppliers/customers, and creates a barrier to entry for new firms
Switching costs
Customer learning curve, integration with other aspects of your life, loss of personalized data, bundled pricing discounts, shopping and acquisition costs, and cancellation costs
Network effects
Metcalfe’s law, value of a product/service increases with the number of users
Distribution channels
Required to access potential customers, retail stores, and smartphone platform
Patents
securing ownership to technology innovations, time-limited, open to theft, duplication, reverse engineering, costly and timely to prosecute, and virtually no ability to prosecute across international borders
Porter’s five forces (key framework)
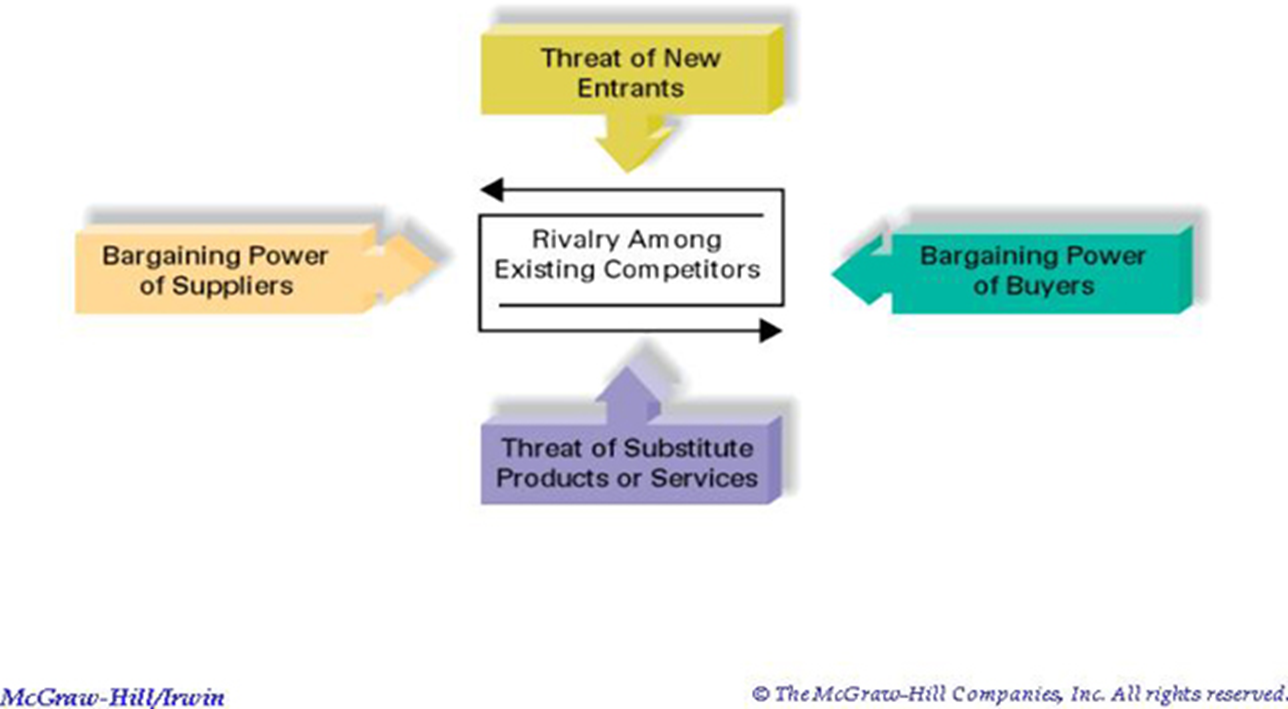
1) threat of new entrants
2) bargaining power of suppliers
3) rivalry among existing competitors
4) bargaining power of buyers
5) threat of substitutes
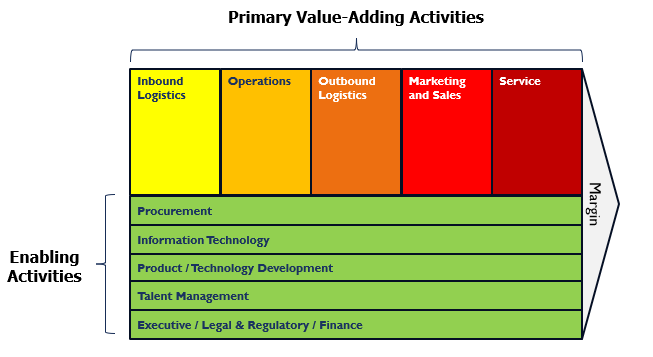
Primary value-adding activities
Inbound logistics, operations, outbound logistics, marketing and sales, and service
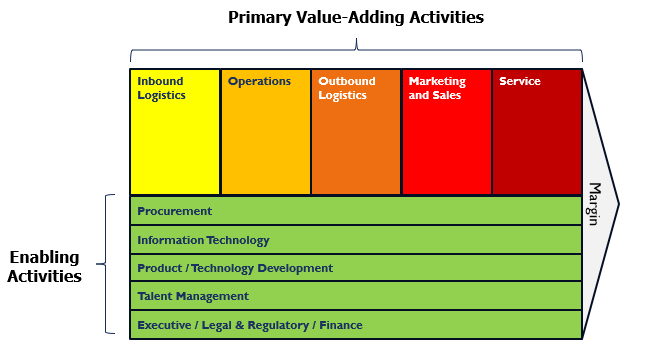
Enabling activities
Procurement, information technology, product/technology development, talent management, and executive/ legal and regulatory/ finance
Corporate strategy
A series of choices that determine the opportunities you’ll pursue, products, markets, and how to differentiate, and revenue drivers, business network. Drives positioning on market, product, business network, and boundary
Business model
Defines how an organization interacts with its environment to define a unique strategy, attract resources, build capabilities, execute strategy, and create value for all stakeholders
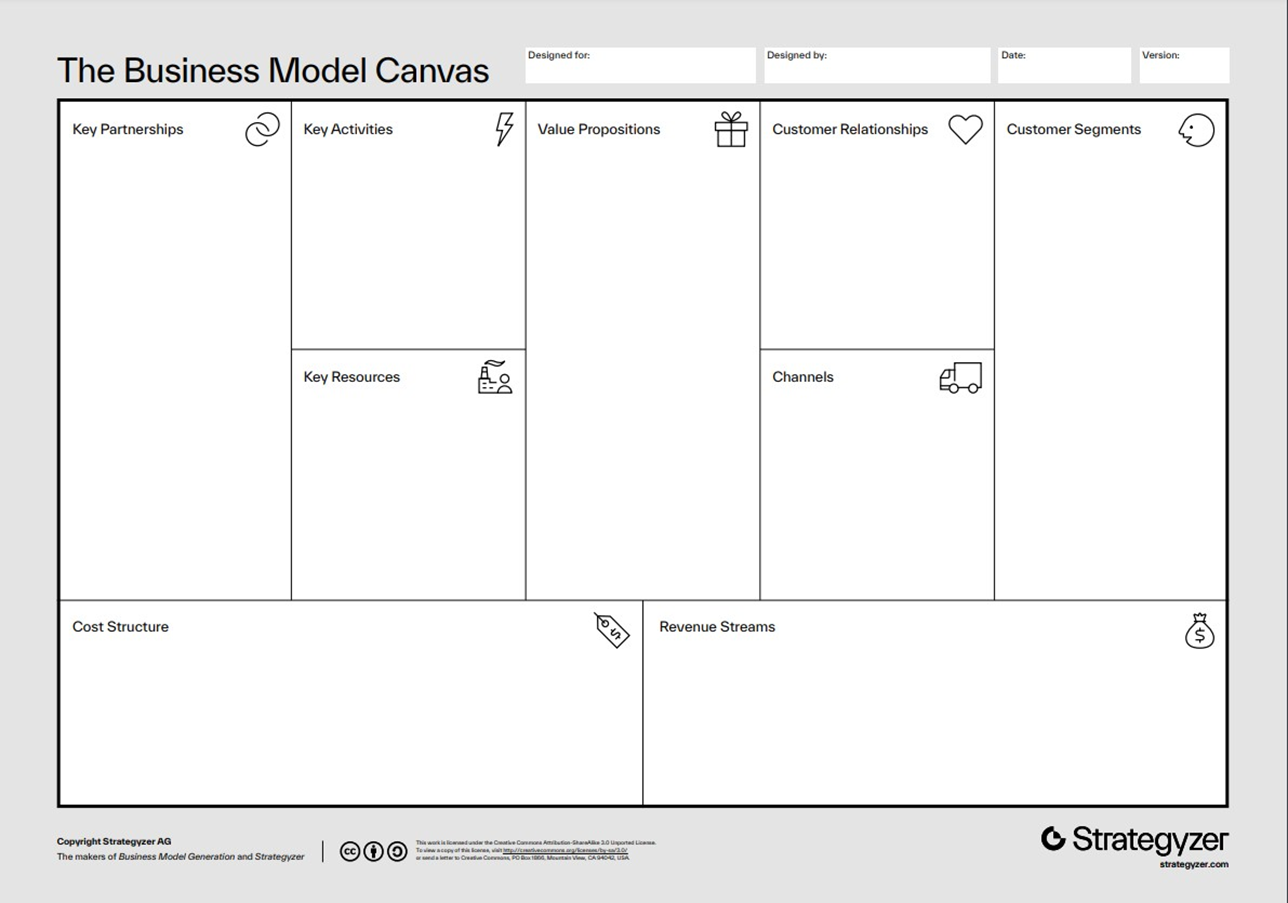
Business model canvas (key framework)
Structured template for documenting and analyzing a company’s business model including key partnerships, key activities, key resources, value propositions, customer relationships, channels, customer segments, cost structure, and revenue streams
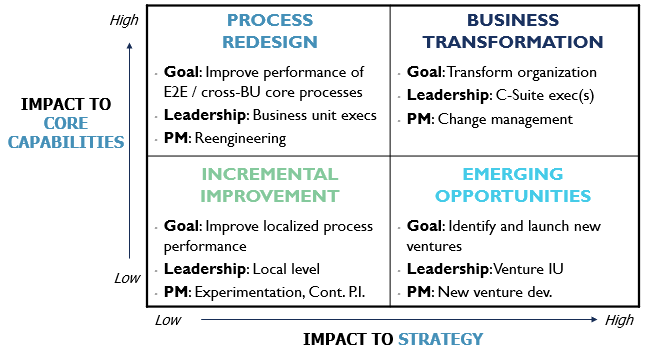
IT initiative impact assessment (key framework)
Graphed based on impact to core capabilities vs impact to strategy.
Incremental improvement (low impact to core capabilities, low impact to strategy)
Process redesign (high impact to core capabilities, low impact to strategy)
Emerging opportunities (low impact to core capabilities, high impact to strategy)
Business transformation (high impact to core capabilities, high impact to strategy)
Business transformations
Designed to boost overall performance through increased revenue, lower operating costs, and better customer satisfaction and workforce productivity
Digital transformations
A specific type of business transformation that integrates digital technologies as crucial enablers in achieving the desired outcomes
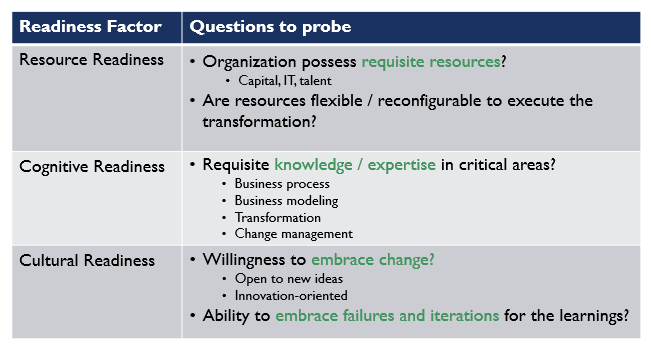
Digital transformation readiness audit (key framework)
Assessing a company’s readiness to undertake a digital transformation on their resource readiness, cognitive readiness, and cultural readiness
Kroger case key takeaways
1) digital transformations must be visibly led from the top with a believable strategy and clear vision
2) partnerships and acquisitions are practical ways to accelerate a transformation given the time requires and the risk of going DIY
3) digital transformations place bets on key capabilities and capacities needed to satisfy evolving trends
Moore’s Law
Predicts transistor count on chips doubles every two years, boosting computing power exponentially
Platforms
Products and services that allow for the development and integration of software products and other complementary goods, effectively creating an ecosystem of value-added offerings
One-sided market
Single class of users generate all value (same-side exchange benefits between users)
Two-sided market
Two distinct types of users generate value (cross-side exchange benefits between user and merchant)
Social media four M’s of engagement
Megaphone, magnet, monitoring and mediation
URL (uniform resource locator)
Identifies resources on the internet along with the application protocol needed to retrieve it
http (hypertext transfer protocol)
Application transfer protocol that allows web browsers and web servers to communicate with each other
Protocol
Enables communication by defining the format of data and rules for exchange
IP address
Value used to identify a device that is connected to the internet used to identify a users physical location, tailor search results, and customize advertising
Domain name service (DNS)
Internet directory that lets devices and services be names and discovered, distributed database around the world to look up host/domain name and return the IP address, analogous to a big, hierarchical set of phone books capable of finding web and email servers and more
TCP (transmission control protocol)
Works at both ends of internet communication to ensure a perfect copy of a message is sent
IP (internet protocol)
Routing protocol in charge of forwarding packets on the internet
Components of the internet
networks, compute/storage, applications, and devices
Networking systems
Transport traffic between two physical locations, route traffic between specific nodes, and control systems manage, monitor, control, and maintain security
Data centers
Servers do the thinking, computing, analysis and AI, storage of applications and databases, lakes, warehouses, etc., and control systems manage, monitor, control, and secure the environment
Infrastructure as a service (IaaS)
Simplifies operations for enterprises by providing hardware (servers, storage, networking, and security)
Software as a service (SaaS)
Simplifies operations for enterprises by providing software (office productivity, ERP, CRM, financial, etc.)
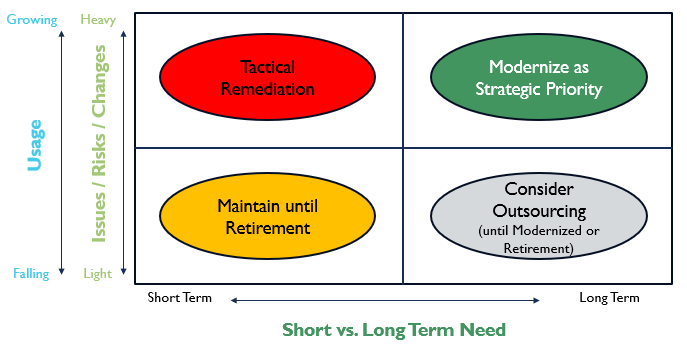
Legacy system strategies
Graphed on scale of falling to growing usage vs short to long term need
Maintain until retirement (falling usage, short term need)
Tactical remediation (growing usage, short term need)
Modernize as strategic priority (growing usage, long term need)
Consider outsourcing (falling usage, long term need)
Series system design
Linear component design that is subject to failure of any component
Parallel system design
Non-linear component design that can provide redundancy to a failed component
Costs of cyber attacks
Lost revenues, brand damage/loss of customers, release of sensitive information, consultancy fees, ransom fees, recovery and restoration, and enhanced protection
Cyber security best practices
Access controls, awareness, detection, preparedness, protection, and reduce vulnerabilities
The project trade-off triangle
Scope, time, and cost are inextricably linked for a given quality
Enterprise IT projects types and risks
Infrastructure, applications, and system integration (with increasing project complexity and risk)
Waterfall software development methodology
1) requirements
2) design
3) development
4) testing
5) deployment
6) maintenance
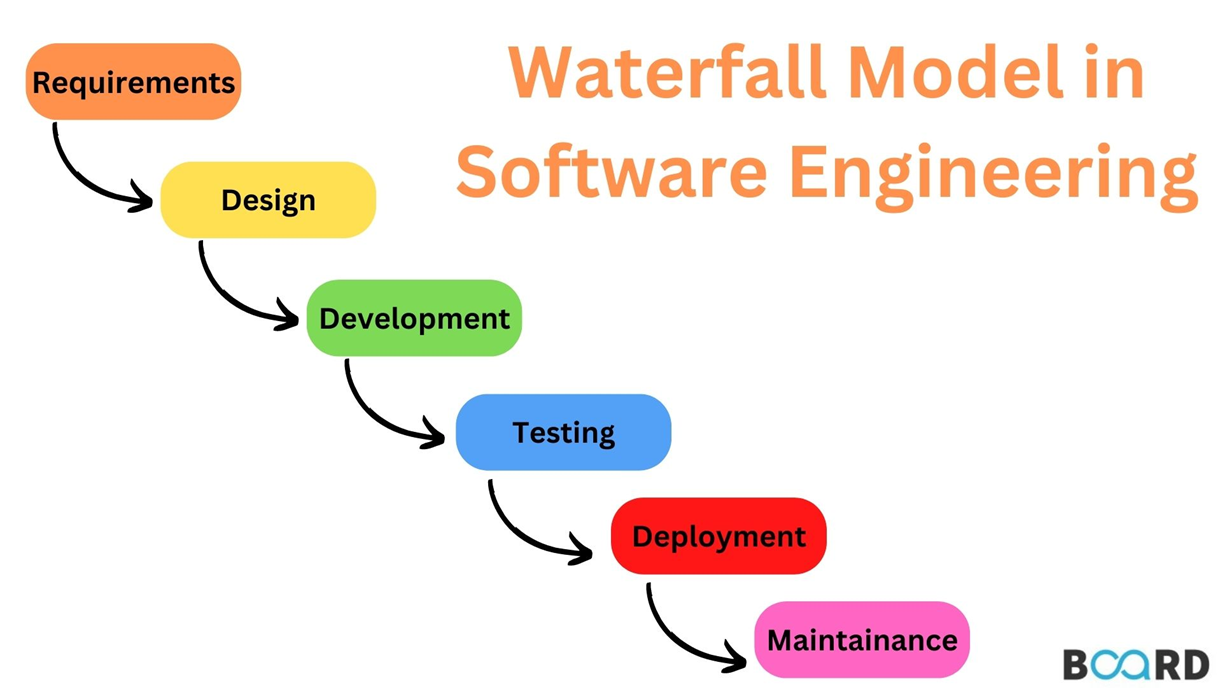
Waterfall methodology projects are best suited for
Fixed budget, fixed and well documented requirements, require specific and detailed documentation, and use well understood technology with few surprises
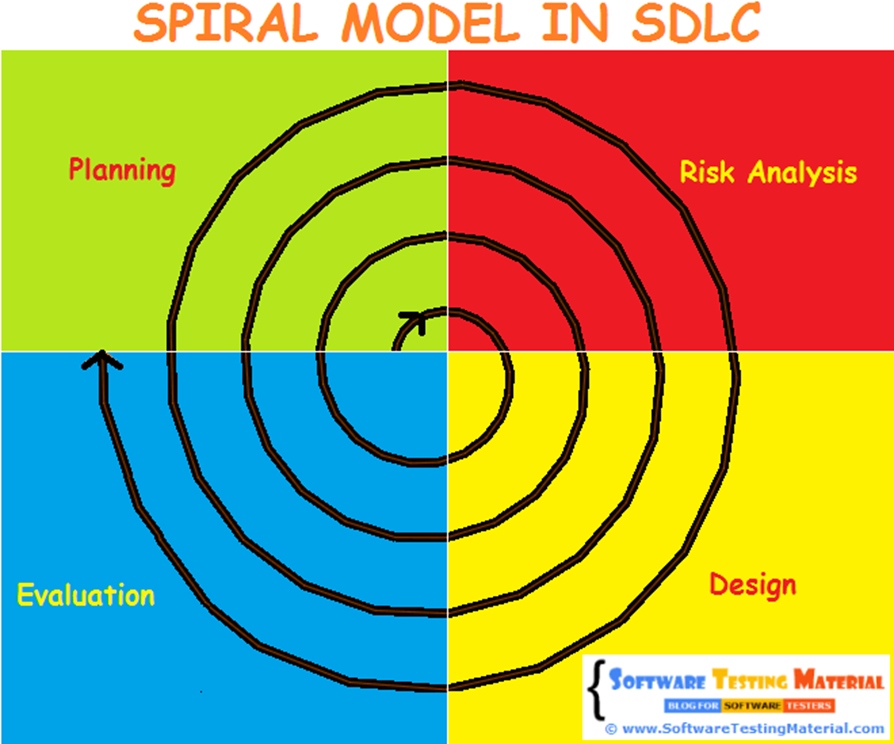
Spiral model of software development
Spiraling through planning, risk analysis, design, and evaluation
Spiral methodology is best suited for projects that
Have cost-plus contracts or private/public partnership, is a new application of recent technology innovation, and highly complex system-of-systems
Agile methodology of software development
Series of <4 week sprints until project finishes
Agile methodologies are best suited for projects that
Clients wants on-going enhancements with flexible budget, frequent change in requirements, benefit from iterative development, require close collaboration between customer and development, and does not require detailed documentation
Top reasons IT projects fail
Lack of executive support, low user adoption, poor communication with stakeholder, scope creep, unclear or changing requirements, and inexperienced people