(FINAL)ITEC3010
1/53
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
54 Terms
Use Case Realization
Process of elaborating the detailed design with interaction diagrams for a particular use case
Interaction Diagram
Shows how objects work together to carry out a use case.
Includes Sequence Diagrams and Communication Diagrams.
Sequence Diagram
An interaction diagram that focuses on the order of messages over time between objects.
Communication Diagram
Structure-focused diagram showing which objects communicate and what messages are sent
Use Case Controller
A designer-created class that links UI to business logic, coordinates tasks, and handles user actions.
Message Flow
The typical path of interaction: Actor → Boundary (UI) → Controller → Entities (data).
Purpose of Controller
To reduce coupling, increase cohesion, and make the system more reusable and easier to modify.
Actor
Represents an external role of the person or thing that initiates the use case by sending the initial message
Object
instantiated class objects that perform actions to help carry out the use case
Link
connectors that illustrate the flow of messages
Messages
primary element of a communication diagram
True/false condition (optional)
if true the message is sent, if false the message is not sent
Sequence number - identifies the order of messages
Sequence number
identifies the order of messages
Return-value
the type of value that the message returns after the completion of the service requested in a forward message. Basically the method return value.
Message-name
usually camelCase. Should be named informatively.
Parameter list
items of data that are passed to the destination object via the message. Basically the arguments of the method.
Activation lifelines
show the period during which a method of an object is alive and executing
Lifelines
Show the passage of time
Synchronous Message (Synchronous Call)
- Filled arrow head
- Message is sent from source lifeline to target lifeline
Asynchronous Message (Asynchronous Call)
Open or Flat Arrowhead
External Systems (Analysis)
Identify all systems your system must connect to or exchange data with.
Technology Architecture (Design)
Specifies message formats, web/network addresses, communication protocols, security, and error handling.
User Interface (UI)
Part of the system users interact with, involving mockups, tools, models, storyboards, and prototypes.
User Experience (UX)
The broader scope of UI design, focusing on how users feel and interact with the system overall.
Centralized vs Distributed
Centralized systems run from one location, while distributed systems operate across multiple locations or servers.
Normalization
Organizing a relational database using normal forms to minimize redundancy and ensure data integrity.
Controls
mechanisms and procedures built into a system to safeguard the system and the information within
Integrity controls
controls that reject invalid data inputs, prevent unauthorized data outputs, protect data and programs against tampering
Input Controls
controls that prevent invalid or erroneous data from entering the system
Value limit controls
controls that check numeric data input to ensure that that value is reasonable, e.g. must be greater than zero
Completeness controls
controls that ensure that all required data values describing an object are present
Data validation controls
controls that ensure that numeric fields that contain codes or identifiers are correct
Field combination controls
controls that review combinations of data inputs to ensure that the correct data are entered
Output controls
controls that ensure that output arrives at the proper destination, which are “Accurate, current and complete”.
Security controls
controls that protect the assets of an organization from all threats
Access controls
control that limits a users ability to access resourses.
Authentication
process of identifying users who request access to access controlled resources
Authorization
process of allowing or restricting a specific authenticated users access to a specific resource based on access controls
CRUD
Create, Read (or Report), Update, and Delete — the 4 basic operations on data. Step 1: Identify all domain classes in the system. Step 2: For each class, ensure there are use cases to Create, Read/Report, Update, and Delete or archive instances. Step 3: Add any missing use cases and identify the stakeholders responsible for them. Step 4: Assign each action to the application or system responsible for carrying it out (e.g., which app handles "create").
Encryption
cryptographically altering data to be undecipherable to those without the key (Requires an algorithm; Requires a key (or multiple keys))
Decryption
convert encrypted data back to its original state
Symmetric key encryption
uses the same key to encrypt and decrypt
Asymmetric key encryption
uses different keys to encrypt and decrypt
Public key encryption
uses public key to encrypt and private key to decrypt
Digital Certificates
has an institutions name and public key
Technology Architecture
The set of computing hardware, network hardware, and system software employed by an organization
Application Architecture
The set of information systems (including software applications) that an organization needs to support its strategic plan or fulfill its business goals
Distributed Architecture
Distribution of system components (hardware and software) across multiple geographic locations
Client/Server Architecture
server manages system resources and provides access to the resources, client communicates with the server to request resources
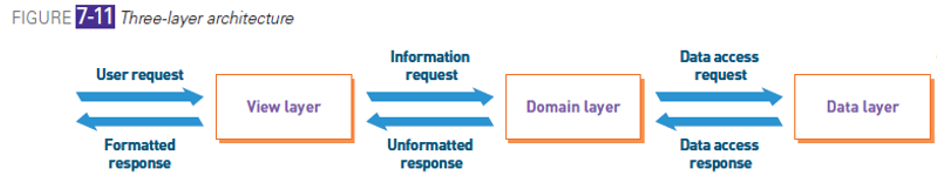
Three-layer Architecture
• View layer: accepts user input and displays outputs
• Business logic layer: (aka domain layer) implements the rules and procedures of business processing
• Data layer: manages stored data, usually in databases
Location Diagram
model that shows the geographic placement of systems components
Network Diagram
Model that shows how locations and hardware components are interconnected
Deployment Diagram
Model that shows how software components are distributed across hardware components
Structure Chart
A hierarchical model (not UML) that shows how software modules relate and break down functions.