Zero Trust - CompTIA Security+ SY0-701 - 1.2
1/6
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
7 Terms
Zero trust
Many networks are relatively open on the inside
- Once you're through the firewall, there are few
security controls
• Zero trust is a holistic approach to network security
- Covers every device, every process, every person
• Everything must be verified
- Nothing is trusted
- Multifactor authentication, encryption, system
permissions, additional firewalls, monitoring and
analytics, etc.
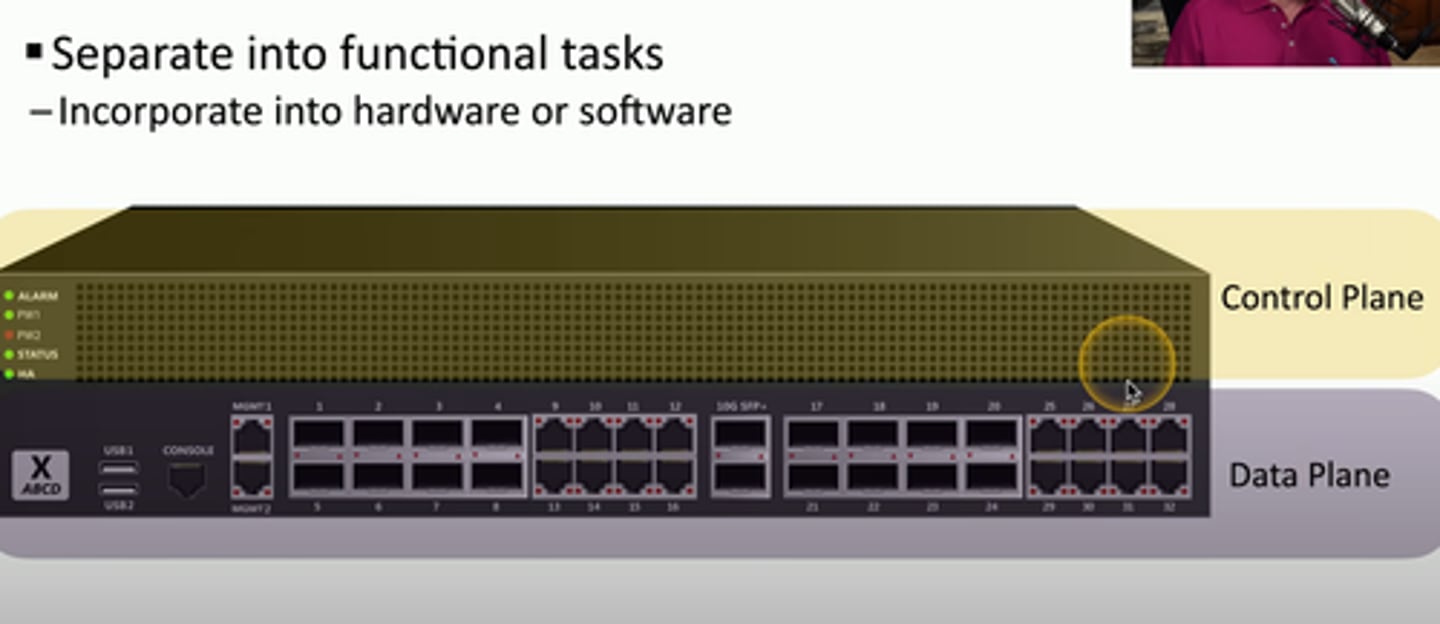
Planes of operation
-Split the network into functional planes
-Applies to physical, virtual, and cloud components
Data plane
- Process frames, packets and network data
- Processing forwarding trunking, encrypting, NAT
Control Plane
- Manages the actions on the data plane
- Define policies and rules
- Determines how packets should be forwarded
- Routing tables
Controlling trust
Adaptive identity
- Consider the source and the requested resources
- Multiple risk indicators - relationship to the
organization, physical location, type of connection, IP
Security zones
Security is more than a one-to-one relationship
- Broad categorizations provide a security-related
foundation
Where are you coming from and where
are you going
- Trusted, untrusted
- Internal network, external network
- VPN 1, VPN 5, VPN 11
- Marketing, IT, Accounting, Human Resources
Using the zones may be enough by itself to deny
access
- For example, Untrusted to Trusted zone traffic
Some zones are implicitly trusted
- For example, Trusted to Internal zone traffic
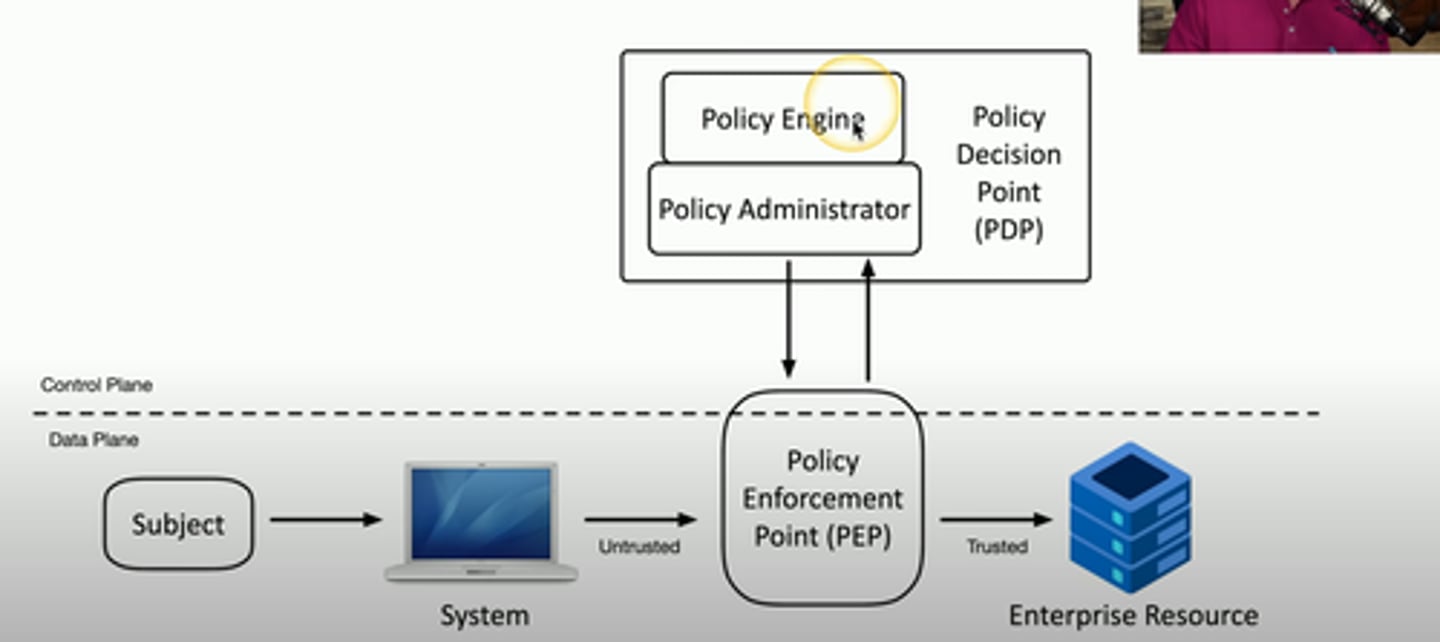
Policy enforcement point
Subjects and Systems- End users, applications, non-human entities.
Policy enforcement point (PEP)
- The gatekeeper
Allow, monitor, and terminate connections.
- Can consist of multiple components working together.
Applying trust in planes
Policy Decision Point
- There's a process for making an authentication decision
• Policy Engine
- Evaluates each access decision based on policy and other
information sources
- Grant, deny, or revoke
• Policy Administrator
- Communicates with the Policy Enforcement Point
- Generates access tokens or credentials
- Tells the PEP to allow or disallow access address, etc.
- Make the authentication stronger, if needed
• Threat scope reduction
- Decrease the number of possible entry points
• Policy-driven access control
- Combine the adaptive identity with a predefined set of rules
Zero Trust Across Planes