IDSC 3001 Topics 7 and 8
1/100
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
101 Terms
Computing Hardware
physical components of information technology, which includes the computer and peripherals (storage devices, input devices, output devices)
Software
computer program or collection of programs. Precise set of instructions that tells hardware what to do
Hardware/Software Layer Cake (Stack)
- User
- Application
- Operating System
- Hardware
Operating System (OS)
controls the computer hardware. Provides a common set of controls for managing computer hardware.
- Makes it easier for users to interact with computers and for programmers to write application software.
- Graphical user interface items are displayed on the hardware of the computer display.
- Files are saved to the hardware of a hard drive or other storage device.
- Most include control panels, desktop file management, and other support programs to work directly with hardware elements.
- Designed to give programmers a common set of commands with which to consistently interact with the hardware.
Graphical User Interface (GUI)
visual items that appear on the hardware of a computer display.
- Ex: scroll bars, menus
Firmware
software stored on nonvolatile memory chips
Volatile Memory
loses data when power is off
Nonvolatile Memory
retains data even when power is turned off
Embedded Systems
special-purpose software designed and included inside physical products.
- As computing gets cheaper, special-purpose technology is increasingly becoming _____________ into all sorts of devices (i.e. cars, picture frames, aircraft engines, photocopiers, and heating and A/C systems)
Distributed Computing
a form of computing where systems in different locations communicate and collaborate to complete a task.
Server
program that fulfills the requests of a client.
- Hardware context: computer that has been configured to support requests from other computers.
- Software context: program that fulfills requests.
Client
software program that makes requests of a server program.
- a user's laptop, phone, desktop, typically using Windows or iOS
Architecture
process of development of methodical technology specifications, models, and guidelines.
Platform
a common technology term that is used for a variety of computing environments, standards, and marketplaces. Products and services that allow for the development and integration of software products and other complementary goods.
- Not all created equal.
- Very different in how they create network effects, interactions they enable, do you build the demand side first or the supply side, openness levels, growth dynamics, competitive strategies and monetization method.
- Building a successful ________ is more about making the right trade-offs than it is about best technology.
- Ex: Windows, the iPhone, the Wii, and the standards that allow users to create Facebook apps
Operability
systems run as designed and are relatively simple to operate
Usability
systems are intuitive and user-friendly
Availability
system down time is minimized
Flexibility and Maintainability
systems can be improved in a cost-effective manner
Scalability and Performance
systems can grow and expand
Interoperability and Portability
systems can run in multiple environments
Security
systems are protected and safe
Enterprise Architecture (EA) Framework
numerous technology decisions need to be made to make an organization's systems work together. Business functions and technology require a plan, guidance
- The plan looks like a pyramid with the Business function / requirements at the top, providing direction for key tech decisions.
- Built upon a variety of different technologies (hardware, networks, devices)

Enterprise Architecture Methodology
Current State (as-is) --> Target State (should be) --> Roadmap (how to, what to)
Technical Standard
a set of requirements for repeatable designs or task, using rules, conditions, or guidelines.
- A key component of strong Quality Management
Types of Standards
- Hardware
- Communication
- Data
- Security
- Software
- Design
Tangible Value of Standards
- Increases Interoperability
- Improves reliability
- Aids in regulatory compliance
- Reduces risk
- Lowers complexity and cost
Application Server
software that houses business logic for use (and reuse) by multiple applications.
Database Server
software that manages database management software and provides for access and storage of data
Web Services
small pieces of code that are accessed via the application server that permit interoperable machine-to-machine interaction over a network.
- Run on web servers
Application Programming Interface (API)
programming hooks, or guidelines, published by firms that tell other programs how to get a service to perform a task such as send or receive data.
Service-Oriented Architecture (SOA)
set of Web services built around an organization's processes and procedures.
LAMP Stack
Linux based web servers consist of four software components, arranged in layers supporting one another. Websites and Web Applications run on top of this underlying stack (Client).
- Linux
- Apache
- MySQL
- PHP
Internet Service Provider (ISP)
organization or firm that provides access to the internet. ___________ connect to one another, exchanging traffic and ensuring that messages can get to any other computer that's online and willing to communicate
- Ex: Verizon, Comcast, AT&T
Redundant and Fault-Tolerant
if one network, connecting wire, or server stops working, everything else should keep running.
- The Internet was designed this way
Internet
is a network of networks, and these networks are connected.
URL (Uniform Resource Locator)
identifies resources on the Internet along with the application protocol needed to retrieve it.
- Often used interchangeably with "Web address."
- Consists of:
- Application Transfer Protocol
- Host Name
- Domain Name
- Top-Level Domain
- Path
- File
HTTP (Hypertext Transfer Protocol)
application transfer protocol that allows Web browsers and Web servers to communicate with each other.
HTML (Hypertext Markup Language)
language used to compose Web pages.
Protocol
enables communication by defining the format of data and rules for exchange.
SMTP (Simple Mail Transfer Protocol)
a server to hold e-mail.
FTP (File Transfer Protocol)
application transfer protocol that is used to copy files from one computer to another.
Case-Sensitive Parts of a Web Address
- Path
- File
Non-Case-Sensitive Parts of a Web Address
- Application Transport Protocol
- Host Name
- Domain Name
- Top-Level Domain
Application Transport Protocol
- NOT case sensitive
- Ex: HTTPS, FTP, SMTP
Host Name
the computer you're looking for on a network.
- NOT case sensitive
- Assigning several computers to a ____ ____ helps ensure that all visits to a popular site like https://www.google.com won't overload a single computer.
- It is also possible for a single computer to have several ____ _____.
Domain Name
the name of the network you're trying to connect to (usually represents an organization).
- NOT case sensitive
- Some __________ are further broken down into sub__________, many times to represent smaller networks or subgroups within a larger organization.
Top-Level Domain
- NOT case sensitive
Path
maps to a folder location where the file is stored on the server
- Case sensitive
File
the name of the ____ you're looking for
- Case sensitive
SSL (Secure Sockets Layer)
a security standard that creates an encrypted link between a Web server and a browser.
- websites that use ___ will begin with https (note the 's' at the end).
Load Balancing
distributing a computing or networking workload across multiple systems in order to avoid congestion and slow performance.
Fault Tolerance
systems that are capable of continuing operation even if a component fails.
Domain Name Registrar
firms that individuals pay for the rights to use a certain domain name. The right is renewable over time
- Some simply register domain names while others are able to run a website on their Internet-connected servers for a fee (web hosting service).
Web Hosting Services
a firm that provides hardware and servers to run the websites of others.
ICANN (Internet Corporation for Assigning Names and Numbers)
a nonprofit governance and standards-setting body that accredits registrars throughout the world. Responsible for managing the Internet's domain and numbering systems.
Generic Top-Level Domain (gTLD)
top-level domains such as .com, .net, or .org.
Sponsored Top-Level Domain (sTLD)
sponsored top-level domains run by private agencies or organizations with established rules restricting the eligibility of registrants
- Ex: only those in the aerospace industry can use .aero
- Ex: only education institutions have access to .edu.
Country Code Top-Level Domain (ccTLD)
two-character top-level domains that represent countries.
Geographic Top-Level Domain (GeoTLDs)
top-level domains that are not two-level country codes, but that are associated with a geographical, geopolitical, ethnic, linguistic, or cultural community.
- Ex: .cat (for Catalan), .paris, and .asia.
Cybersquatting
acquiring a domain name that refers to a firm, individual, product, or trademark, with the goal of exploiting it for financial gain. The practice is illegal in many nations, and ICANN has a dispute resolution mechanism that in some circumstances can strip people of registered domains.
404 Error
an error that occurs when you mistype the path and file of a URL (i.e. by using incorrect case)
IP Address
value used to identify a device that is connected to the Internet. Can be used to:
- Identify a user's physical location.
- Tailor search results.
- Customize advertising.
IPv4
the widely-used IP address format. Expressed as four numbers (from 0-255), separated by periods
- Ex: 216.3.128.12
NAT (Network Address Translation)
conserves IP addresses by mapping devices on a private network to single Internet-connected devices that acts on their behalf.
- Helps delay the impact of the IP address drought but slows down Internet access and is complex, cumbersome, and expensive to administer
IPv6
increases the possible address space from the addresses used in the current system.
- Not backward compatible with IPv4 and transition has been very slow.
•When ____ is deployed, some of the benefits may include potentially improving speed, reliability, and security of the internet.
Domain Name Service (DNS)
Internet directory service that allows devices and services to be named and discoverable. Distributed database that looks up host and domain names and returns the actual IP address for them.
- Likened to a big, hierarchical set of phone books capable of finding Web and email servers and more.
- Nameservers that work together can get you anywhere you need to go online.
- The system also remembers what's it's done so next time your computer can pull this out of cache
Nameservers
similar to phonebooks that can find Web and email servers, and more.
- When they work together to create the DNS, they can get you anywhere you need to go online
Cache
temporary storage space used to speed computing tasks.
Governance, Regulation, and Compliance (GRC)
governments, partnerships, imposed standards, and industry standards oversee and control the data that an organization collects, stores, and uses.
- Main goal of ensuring transparency
- Increasingly complex and rigorous burden
- Tech plays a vital role: ___ systems can assess risk against a particular objective, and can increase visibility of compliance efforts.
- There must be a central function that can aggregate _______________ information
- Management of policies must happen locally
- Execution needs to be owned by the business
- People are as important as the process
Reasons for Implementing GRC Programs
- Regulatory requirements
- Monetary risks and / or reputation risks
Regulations
- data retention,
- protecting confidential information
- financial accountability
- disasters recovery
Horizontal (Cross-Industry) Obligations
financial reporting, labor laws, data privacy that spans industries
Vertical Obligations
regulatory requirements for food, medical devices, higher education, etc.
- Industry-specific
Contractual Obligations
obligations to business partners, supply chain, outsourcers, service providers, and contractors.
Strategic Objectives
maintaining visibility and control so that the organization can meet business objectives.
Pros of GRC
- Provides Transparency for Shareholders
- Create a high barrier entry for new competitors
- Discourages current competitors from 'cheating'
Cons of GRC
- Expensive and Time Consuming
- Can Limit Innovation & Risk Taking
- Risk of Fines and Penalties
Corporate Governance
the set of processes, policies, laws, customs, and rules affecting the way a corporation is directed, managed and controlled.
- Board of Directors and Delegation of Authority
- ____________ has a "top-down" component.
Board of Directors
play a key role in overseeing, administering, and monitoring a company.
- Part of corporate governance
Delegation of Authority
the accountability of individuals in an organization through information systems.
- Part of corporate governance
IT Governance
provides structure around how organizations align IT strategy with business strategy.
- Enterprise-wide visibility for compliance
- Monitoring all existing processes is a daunting task
- Requires access to numerous information systems and timely reporting
- Involves IT systems
- ____________ has a "bottom-up" component.
IT Systems
when implemented properly, helps companies increase visibility into the effectiveness of compliance efforts.
- poorly designed __ _______ leaves companies vulnerable to a variety of potential issues.
Environmental, Social, and Governance Software (ESG)
- Environmental (Sustainability & Carbon Management, Hazardous substances, Waste Recycling, Water Use)
- Social (DEI, labor practices, health and safety)
- Governance (Enterprise Risk Management, Compliance Management, Vendor Risk Management)
Principles
outcome-focused direction for decision making (e.g., Hiring ____________)
- Very strategic and high risk
Policies
formal guidelines (e.g., Travel Expense ______)
- Strategic and risky
Standards
methods and resources provided to support policy (e.g., ISO 9001 ___________)
- In between strategic and tactical
- Moderate risk
Procedures
detailed directions on how policies should be followed (e.g., _________ to file for Travel Reimbursement)
- Tactical and not very risky
Guidelines
informal suggested practices (e.g., Social Media _________)
- Very tactical and low risk
Examples of Audits
- Internal Financial Audit
- External Financial Audit
- Tax Audit
- Operational Audit
- Compliance Audit
- Information System Audit
- Payroll Audit
Examples of Controls
- Log-in Credentials
- Approvals
- Legal review of Contracts
- Spending Authority & Spending Limits
- Segregation of Duties
- Account Reconciliation
Sarbanes-Oxley Act (SOX)
mandates a strong internal control environment, including the electronic data needed to prove it. Aims to enforce corporate governance and strengthen corporate accountability by:
- internal checks and balances
- levels of approval and sign-off
- full transparency
- adequate controls
- supported by enterprise applications (ERP, CRM, SCM)
- All data (emails, communications, files, directives and requests) that may be relevant to lawsuits must be produced and thus it must be archived.
Health Insurance Portability and Accountability Act (HIPAA)
imposed tough data privacy and protection for any businesses related to health care.
Basel IV
introduces changes that limit the reduction in capital, a standardized floor for capital requirement, requiring banks to meet higher maximum leverage ratios.
PCI Standards
council that offers comprehensive standards to enhance payment card data security.
Biggest IT Compliance Challenges
- Employees
- Mobile Devices
- Third Parties
- Cloud Service Providers
GDPR (General Data Protection Regulation)
the EU's new privacy law as of 2018. 87 pages long and contains 99 articles, is still the "most complex piece of regulation the EU has ever produced". Privacy is considered a fundamental human right, this is an attempt to put individuals back in charge.
- Concern is that it would make collecting and handling personal information prohibitively complicated.
- Personal data can be even harder to pin down than money and financial products.
- Many questions had to be addressed: How should data be collected? Who should have access? What can be done with them? Who should ultimately be in control of them?
- Consent to collect and use personal data now has to be "unambiguous" and for "specific" purposes.
- People can demand a copy of the data held on them, ask for information to be deleted (the "right to be forgotten").
- Data transferred to another service ("data portability").
- Fines up to $24 M or 4% of global annual sales, whichever is greater.
- Controversy over extraterritorial reach. It will apply not just in the EU, but wherever personal data about European citizens are processed.
EDI (Electronic Data Interchange)
a set of standards for exchanging messages containing formatted data between computer applications.
XML (Extensible Markup Language)
a tagging language that can be used to identify data fields made available for use by other applications. Most APIs and Web services send messages where the data exchanged is wrapped in identifying ___ tags.
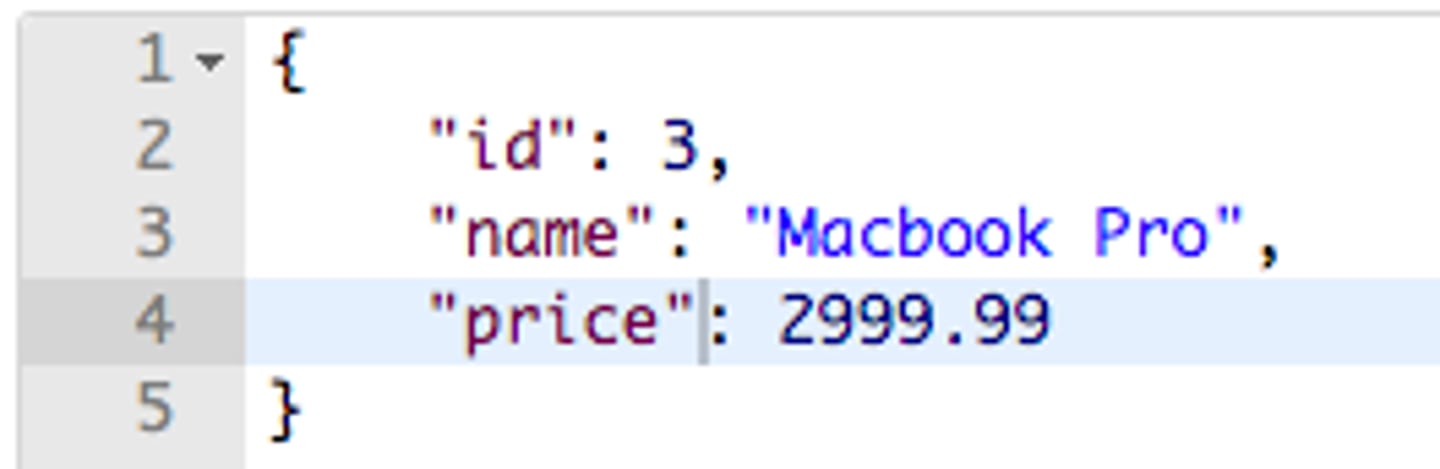
JSON (JavaScript Object Notation)
a popular data interchange format. A technology standard often used to format data when being sent or received via APIs.
Governance
the process to monitor and control an organization's information technology and systems. Involves use, security, responsibility, enforcement, penalties, ethics, and audit, among other areas.