Information Security I Exam
1/63
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
64 Terms
information security
protection of information and information systems from unauthorized access, use, disclosure, and disruption, modification, or destruction in order to provide confidentiality, integrity, and access
confidentiality
assures that confidential information is not disclosed to unauthorized individuals
integrity
assures that information and programs are changed only in a specified and authorized manner. involves maintaining consistency, accuracy, and trustworthiness of data
accessibility
assures systems work promptly and service is not denied to users
data confidentiality
private or confidential information is not made available or disclosed to unauthorized individuals
privacy
an individual’s control or influence over what information is related to them may be collected and stored, and by whom and to whom that information may be disclosed
risk
expectation of loss as the probability that a threat will exploit a vulnerability with a harmful result
threat
a potential for violation of security, capability, action, or event that could breach security and cause harm
passive attack
attempts to learn or make use of information from system but does not affect system
active attacker
attempts to alter system resources or affect their operation
cryptographic tools
symmetric encryption
secure hash functions in message authentication
public key (asymmetric encryption)
data encryption standard (DES)
most widely used encryption scheme
64-bit plaintext block
56-bit key
64-bit ciphertext block
triple DES
repeats DES 3 times
uses 2 or 3 unique keys for a key size of 112 or 158 bits
advanced encryption standard
better replacement for triple DES
128-bit data
128/192/256-bit keys
electronic codebook (ECB)
tells you how to implement encryption method
block ciphers
encrypt full 128-bit blocks
stream ciphers
encrypts data bit-by-bit as a continuous stream
cipher block chaining (CBC)
each ciphertext block depends on all plaintext blocks processed up to that point
initialization vector must be used in 1st block to make each message unique
replay attack
an adversary can capture a valid message and resend the same message to the receiver later whenever it benefits them or damages the system
substitution attack
adversary can remove a message in a sequence without the receiver knowing since receiver does not know what or how many it’s expecting
message authentication code (MAC)
does not rely on encryption
uses MAC algorithm to “encrypt” message and compare for later
cryptographic hash function
accepts a variable-size message M as input and produces a fixed-size message digest h = H(M) as output
uses symmetric key for MAC one-way hash function and symmetric encryption
hash function properties
applied to any size data
H produces a fixed-length output
H(x) is relatively easy to compute for any given X, making hardware and software implementations practical
one-way resistant
weak collision resistance (should be hard to find a different input with same hash)
strong collision resistance (should be hard to find two different inputs of any length that result in same hash)
digital signature
asymmetric encryption and hash function together
RSA (rivest, shamir, adleman) steps
select p, q
calculate n = p x q
calculate Φ(n) = (p-1)(q-1)
select integer e gcd(Φ(n), e) = 1; 1 < e < Φ(n)
calculate d de mod Φ(n) = 1
public key KU = {e, n}
private key KR = {d, n}
user authentication: two steps
identification, verification
access control
constraints on what a user can do directly, as well as what programs executing on behalf of the users are allowed to do
object
access controlled resource
subject
entity that can access objects
access right
way in which subject accessed an object
discretionary based access control (DBAC)
user-oriented security policy (based on identity of requester)
entity has rights to grant another entity access to a resource
mandatory access control (MAC)
access permissions defined by system itself
cleared entity cannot pass on access rights to another entity
role based access control (RBAC)
based on roles that users have within system and on rules stating what accesses are allowed to users in given roles
attribute-based access control (ABAC)
controls access based on attributes of user, resource, and current environmental conditions
intrusion
a security event, or multiple security events, in which an intruder gains, or attempts to gain access to a system without having authorization to do so
intrusion detection system (IDS)
security service that monitors/ analyzes system events for the purpose of finding, and providing real-time warning of attempts to access system resources in an unauthorized manner
sensors
collect real-time data about various systems and network functions
anamoly detection
involves collection of data relating to behavior of legitimate users
current behavior is observed and analyzed to determine if behavior is intruder or legitimate user
signature/ heuristics deteciton
uses a set of known malicious data patterns or attack rules that are compared with current behavior
can only identify known attacks that has patterns or rules
model of normality
describe normal system behavior
profile
a set of observed measures of behavior
host-based IDS
applies specialized layer of security software to vulnerable and sensitive systems
can use an anomaly or signature approaches
monitors activity to detect suspicious behavior
covers limited IP space (e.g. my laptop and it’s system call traces, audit records, file checksums)
netowork-based IDS
deploying sensors at strategic locations (before switches/ routers and after host devices, also before external firewall)
inspecting network traffic
monitoring user activities
can be defeated by encryption
honeypot
decoy system design to lure attack away from critical systems, collect information about attacker, encourage attacker to stay long enough that admins can respond
snort
open-source IDS that’s now developed by CISCO
performs real-time packet capture, protocol analysis, and content searching and matching
measure of IDS
proper detection attacks and absence of false alarms
TPR
indicates intrusions
FPR
indicates non-intrusions
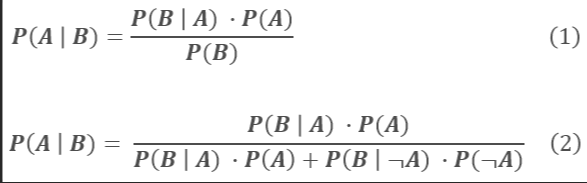
bayesian decision rate
firewall
combination of hardware and software that isolates an organization’s internal network from the internet at large, allowing some packets to pass and blocking others
firewall filter characteristics
IP address (limits access to specific services)
application protocol (monitors information exchange)
user identity (inside users using authentication technology)
network activity (controls access based on time, req, rate of req, activity patterns)
application proxy (application-level gateway)
acts as a relay of application-level traffic
economy of mechanism
design of security measures should be as simple and small as possible
fail-safe default
access decisions should be based on permissions rather than exclusions (e.g. blacklist)
complete mediation
every access must be compared with access control mechanicsm
open design
design of security mechanism should be open to the public rather than secret
least privilege
every process and every user of system should operate using the least set of privileges neccessary to perform the task
least common mechanism
design should minimize the functions shared amongst different users, providing mutual security
psychology acceptability
security mechanisms should not interfere with the work of the users but shall simultaneously meet the needs of those who authorize access
isolation
public access systems shall be isolated from critical resources to prevent disclosure or tampering
process and files of indvidual users shall be isolated from one another
security mechanisms should be isolated in the sense of preventing access to mechanism by unauthorized user
encapsulation
specific form of isolation based on object-oriented functionality
collection of proceudres and data objects
modularity
security functions shall be developed separately and separated modules
layering
use of multiple, overlapping protection approaches addressing people, technology, and operational aspects of information systems
least astonishment
programs or user interface shall always respond in a way that is least likely to astonish (surpise) the user. should be intuitive and users can have a good understanding