Chapter 4 Quiz Guide - ITEC 2201
1/48
Earn XP
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
49 Terms
Information Security
protection of information/information systems from unauthorized use, disclosure, disruption, modification, or destruction in order to provide confidentiality, integrity, and availability.
NIST
National Institute of Standards and Technology
Information Systems Security (INFOSEC)
protection of information systems against unauthorized access to or modification of information, whether in storage, processing or transit, and against the denial of service to authorized users, including those measures necessary to detect, document, and counter such threats
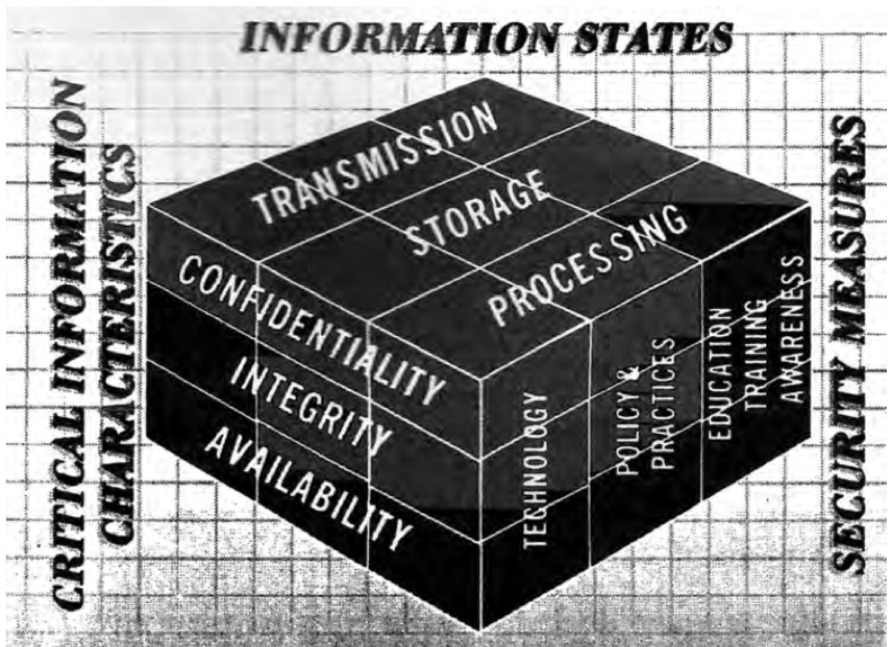
CIA
Confidentiality, Integrity, and Availability - defines the classic security concerns in an automated environment
ISO
International Organization for Standardization
Access Control
the practice of Identity Management, authentication, authorization, and accountability (grants access ONLY to authorized users)
Availability
objective that generates the requirement for protection against intentional or accidental attempts to
(1) perform unauthorized deletion of data or
(2) otherwise cause a denial of service or data
Confidentiality
objective that generates the requirement for protection from intentional or accidental attempts to perform unauthorized data reads.
covers data in storage, during processing, and while in transit
Integrity as an Objective
objective that generates the requirement for protection against either intentional or accidental attempts to violate data integrity or system integrity
Data Integrity
the property that data has not been altered in an unauthorized manner
System Integrity
the quality that a system has when it performs its intended function in an unimpaired manner, free from unauthorized manipulation
Access Control List (ACL)
mechanism that implements access control for a system resource by enumerating the identities of the system entities that are permitted to access the resources
Authentication
process that establishes the origin of information, or determines an entity’s identity.
In a general information security context: Verifying the identity of a user, process, or device, often as a prerequisite to allowing access to resources in an information system
Authentication Factor
something you know, something you have, and something you are
Identity
The set of physical and behavioral characteristics by which an individual is uniquely recognizable
Identification
A unique, auditable representation of identity within the system usually in the form of a simple character string for each individual user, machine, software component or any other entity
Identity Management Systems
comprised of one or more systems or applications that manages the identity verification, validation and issuance process
Multi-factor Authentication (MFA)
using two or more different factors to achieve authentication. Factors include: something you know (e.g., password/PIN) something you have (e.g., cryptographic identification device, token) or something you are (e.g., biometric)"
Password
A secret that a Claimant memorizes and uses to authenticate his or her identity. Typically character strings
Role Based Access Control (RBAC)
model for controlling access to resources where permitted actions on resources are identified with roles rather than with individual subject identities
Access Control: DENY
deny everybody and everything you can
Access Control: AUTHORIZE
allow limited capability only AFTER proper authorization and authentication
Access Control: RECORD
record EVERYTHING
Access Control for Databases
used to create UNIQUE, SECURE usernames and passwords, change those passwords regularly, and create separate MySQL users for different types of activity
MySQL: PUBLIC
SELECT
MySQL: CUSTOMER
SELECT, INSERT, UPDATE
MySQL: ADMIN
SELECT, INSERT, UPDATE, DELETE
What should you avoid when managing Access Control for Databases?
avoid giving SHUTDOWN, GRANT, RELOAD, DROP, and CREATE privileges to any MySQL user that will be connecting from a website
What are some SECURITY CONCERNS for customers?
Professional in appearance, honest and transparent, and use of SSL and HTTPS
Secure Sockets Layer (SSL)
creates encrypted link between web server and web browser
Hypertext Transfer Protocol Secure (HTTPS)
encrypts communication over a computer network (widely used on internet)
Cryptography
transforms data into CIPHER TEXT readable only by sender and receiver
Cipher Text
Data in its encrypted form
Cipher
Series of transformations that converts plaintext to ciphertext using the Cipher Key
Cipher Key
parameter used in conjunction with a cryptographic algorithm that determines its operation in such a way that an entity with knowledge of the key can reproduce the operation, while an entity without knowledge of the key cannot
Plaintext
Data input to the Cipher or output from the Inverse Cipher
Symmetric Key Cryptography
sender and receiver use the SAME digital key to encrypt and decrypt messages - requires a different set of keys for every transaction
Public Key Cryptography
uses TWO mathematically related digital keys (public and private). Both keys are used to encrypt and decrypt message and once they’re used, the same key cannot be used again.
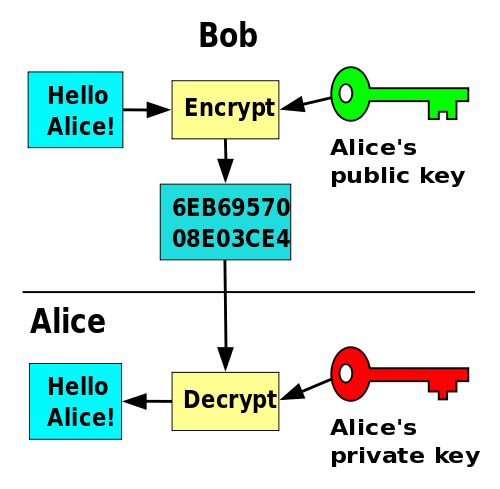
Public Key
widely disseminated
Private Key
kept secret by owner
What does Integrity mean?
Data is not altered by unauthorized users
What does Confidentiality mean?
Data is kept secret
What ensures that an entity can be traced uniquely to that entity
Accountability
___________ refers to weakness in an information system, system security procedures, internal control
Vulnerability
a message is changed into a format that cannot be read by an unauthorized user
Encryption
In Cryptography, the original message that is scrambled is referred to as the _________.
Plain Text
The regulation that oversees the secure storage and transaction of customer credit data is called __________
PCI - Payment Card Industry
__________ encryption uses DIFFERENT keys for encryption and decryption
Public Key/Asymmetric key
_______ encryption uses the SAME key for encryption and decryption
Symmetric