Finals
0.0(0)
Studied by 9 peopleCard Sorting
1/54
Earn XP
Description and Tags
Last updated 12:50 AM on 6/12/23
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
55 Terms
1
New cards
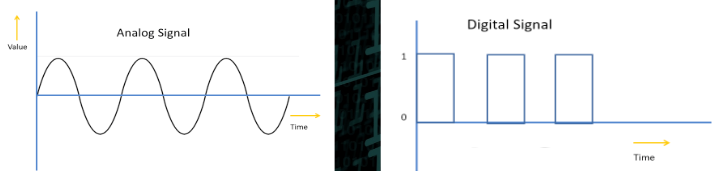
analog vs digital
analog:
* infinite values (sine waves)
* continuous signal, one time-varying quantity represents another time-based variable
* measures natural/physical values, suitable for audio/visual transmission
\
digital:
* discrete/separate values (square waves)
* represents data as a sequence of discrete (separate) values at any point in time versatile
* easy to process & transmit
\
analog to digital
* infinite values (sine waves)
* continuous signal, one time-varying quantity represents another time-based variable
* measures natural/physical values, suitable for audio/visual transmission
\
digital:
* discrete/separate values (square waves)
* represents data as a sequence of discrete (separate) values at any point in time versatile
* easy to process & transmit
\
analog to digital
2
New cards
lossless vs lossy compression
* lossless loses none and compresses at a lesser extent, moves slower than lossy because data file is larger bc it cannot be compressed as big
* lossy compresses at a greater extent but loses the og so not good for text compression cuz u literally cannot read it how its supposed to be read
* lossy compresses at a greater extent but loses the og so not good for text compression cuz u literally cannot read it how its supposed to be read
3
New cards
B, KB, MB, GB, TB
data storage metrics, in order increasing by 1000x bits

4
New cards
match
1. analog
2. compression
3. digital
4. heuristic
5. lossless
6. lossy
7. RGB
a. color model that adds different shades of light to reproduce a variety of colors
b. compressed data can be reconstructed back to the original; perfectly reversible
c. laser thermometer
d. mercury thermometer
e. reducing file size by reducing the number of bits used to store the information
f. uses inexact approximations and partial data discarding to represent the content; irreversible
g. technique for finding an approximate solution quickly when an exact solution is too slow
1. analog
2. compression
3. digital
4. heuristic
5. lossless
6. lossy
7. RGB
a. color model that adds different shades of light to reproduce a variety of colors
b. compressed data can be reconstructed back to the original; perfectly reversible
c. laser thermometer
d. mercury thermometer
e. reducing file size by reducing the number of bits used to store the information
f. uses inexact approximations and partial data discarding to represent the content; irreversible
g. technique for finding an approximate solution quickly when an exact solution is too slow
1. d
2. e
3. c
4. g
5. b
6. f
7. a
5
New cards
Digital Divide
The gap between people with and without access to the internet, creates a disparity in knowledge and societal participation.
6
New cards
valid IP address
\
A valid IP address must be in the form of A.B.C.D, where A,B,C and D are numbers from 0-255.
A valid IP address must be in the form of A.B.C.D, where A,B,C and D are numbers from 0-255.
7
New cards
redundancy
backup/extra components incase a line is down or broken to ensure packets are sent to their destination; providing fault tolerance.
8
New cards
packet routing / TCP
creates packets at sending to be sent simultaneously but in different routes and reassembles them at the receiving. Ensures packets are sent to their destination, if a packet is lost or not sent than TCP requests that specific packet back to be sent.
9
New cards
DNS
turns domain names into computer readable IP addresses
ex: google turns into 33.44.51.126
ex: google turns into 33.44.51.126
10
New cards
\
algorithm
algorithm
finite set of instructions that accomplish a task; is the answer to a problem
11
New cards
linear vs binary search
* binary (logarithmic):
* needs to be a sorted list
* number of inputs and number of steps are equal
* in a list from 1-10 trynna get the target number, binary search goes for the middle number each time then halves the list and continues until getting the target number. If the number is 6 then binary picks 5 and removes numbers 1-5 then the list is now 6-10 chooses 8 and removes 8-10, now the number is 6-7 and binary chooses 7, remove s7 and chooses 6 aka the target number.
* more efficient than linear
\
* linear:
* doesn’t need to be a sorted list
* number of steps is the binary equivalent to the number of inputs (5 inputs has 3 steps because 101 is the binary of 5)
* in a list from 1-10 trynna get the target number, linear checks each one in a linear/orderly process until getting to the target. if the number is 6 then linear search checks starting from 1 to 6 and stops at 6 because 6 is the target number and linear has reached it.
* needs to be a sorted list
* number of inputs and number of steps are equal
* in a list from 1-10 trynna get the target number, binary search goes for the middle number each time then halves the list and continues until getting the target number. If the number is 6 then binary picks 5 and removes numbers 1-5 then the list is now 6-10 chooses 8 and removes 8-10, now the number is 6-7 and binary chooses 7, remove s7 and chooses 6 aka the target number.
* more efficient than linear
\
* linear:
* doesn’t need to be a sorted list
* number of steps is the binary equivalent to the number of inputs (5 inputs has 3 steps because 101 is the binary of 5)
* in a list from 1-10 trynna get the target number, linear checks each one in a linear/orderly process until getting to the target. if the number is 6 then linear search checks starting from 1 to 6 and stops at 6 because 6 is the target number and linear has reached it.
12
New cards
Efficiency
a measure of how many steps are needed to complete an algorithm
13
New cards
\
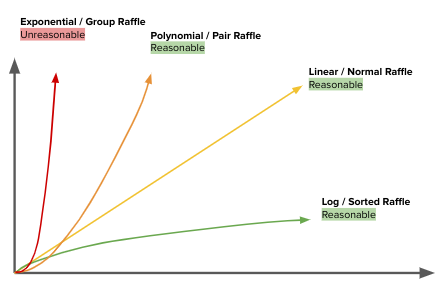
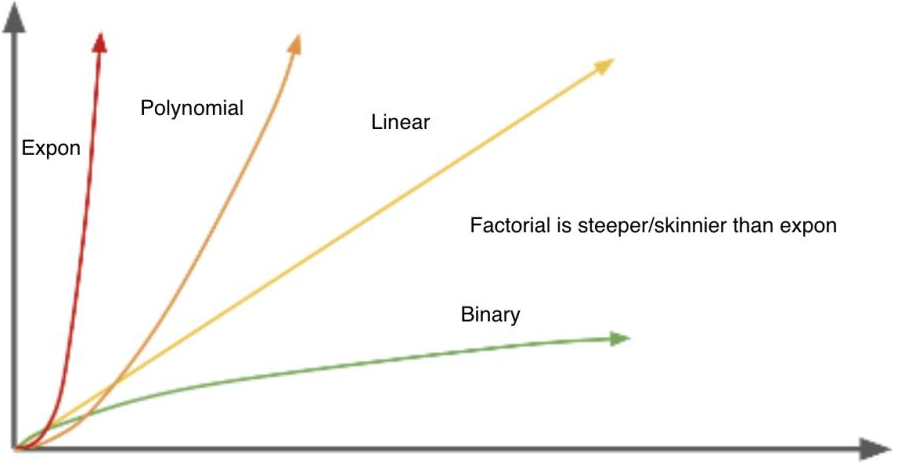
reasonable time versus unreasonable time
reasonable time versus unreasonable time
reasonable time: linear, polynomial, binary/log efficiency
unreasonable time: exponential & factorial efficiency
unreasonable time: exponential & factorial efficiency
14
New cards
unreasonable vs undecidable
the difference between undecidable problems and unreasonable time algorithms is that an undecidable problem is a problem that no algorithm can be made because it loops forever, this is always capable of providing a yes or no answer, while an unreasonable time algorithm is an algorithm with exponential efficiencies and cannot create an answer in a reasonable amount of time.
* unreasonable:
* an algorithm with exponential efficiencies and cannot create an answer in a reasonable amount of time
* undecidable:
* a problem for which no algorithm can be constructed that is always capable of providing a correct yes-or-no answer
* loops forever
* unreasonable:
* an algorithm with exponential efficiencies and cannot create an answer in a reasonable amount of time
* undecidable:
* a problem for which no algorithm can be constructed that is always capable of providing a correct yes-or-no answer
* loops forever
15
New cards
heuristic
Provide an approximate solution that’s good enough to solve a problem when an actual solution is impractical or impossible
16
New cards
traveling salesperson problem
* The Traveling Salesperson Problem is an **optimization** problem. We are trying to find the shortest path to visit all homes/cities.
* Is unreasonable because there is not an algorithm that can solve the problem in a reasonable amount of time.
* Needs to use a **heuristic** to come up with a solution that is "good enough" for most instances of the problem.
* Is unreasonable because there is not an algorithm that can solve the problem in a reasonable amount of time.
* Needs to use a **heuristic** to come up with a solution that is "good enough" for most instances of the problem.
17
New cards
parallel processing & speedup
Parallel processing is where programs are broken into small pieces, some of which are run simultaneously. Speedup is the time used to complete a task sequentially divided by the time to complete the task in parallel. Speedup is never equal to the number of processors. \n Eventually the speedup reaches a limit.
18
New cards
distributed computing
data is distributed among multiple computers and each computer runs the program on its own section of the data
\-provides heightened processing speed and memory to handle big datasets
\-provides heightened processing speed and memory to handle big datasets
19
New cards
one column charts
* bar chart
* few values
\
* histogram
* many values
* all numbers in a range or "bucket" are grouped together. For example, a chart with the a bucket size of 20 so the numbers 41, 48, and 53 would all be placed in the same bucket between 40 and 60.
* can only be created with numeric data but can be useful when a normal bar chart may be difficult to read.
* Information we can get out of histograms:
* What range of value(s) are most common in this column?
* What range value(s) are least common in this column?
* What ranges of values do or do not appear in this column?
* few values
\
* histogram
* many values
* all numbers in a range or "bucket" are grouped together. For example, a chart with the a bucket size of 20 so the numbers 41, 48, and 53 would all be placed in the same bucket between 40 and 60.
* can only be created with numeric data but can be useful when a normal bar chart may be difficult to read.
* Information we can get out of histograms:
* What range of value(s) are most common in this column?
* What range value(s) are least common in this column?
* What ranges of values do or do not appear in this column?
20
New cards
two column charts (x, y)
* crosstab
* few values, usually finite data put in
\
* scatterplot
* many values, continual data being put in
* few values, usually finite data put in
\
* scatterplot
* many values, continual data being put in
21
New cards
big/open/crowdsourced data
\
Big data: Collect huge amounts of data so we can learn even more from it, big huge lots of data
Open data: sharing data with others so they can can analyze it, data is OPEN to be shared w/ others
Crowdsourcing: collecting data from others so you can analyze it, sourcing data from the crowd/people to analyze
Big data: Collect huge amounts of data so we can learn even more from it, big huge lots of data
Open data: sharing data with others so they can can analyze it, data is OPEN to be shared w/ others
Crowdsourcing: collecting data from others so you can analyze it, sourcing data from the crowd/people to analyze
22
New cards
cleaning data
making data consistent, removing useless and corrupt data
23
New cards
algorithmic bias: face detection
AI better recognizes white faces and least black faces
24
New cards
algorithmic bias: cropping photos
AI more likely to crop out black faces than white faces
25
New cards
if values on a chart are too unique
then theres little point in doing a chart cuz charts are for finding correlations and connections
26
New cards
data analysis process
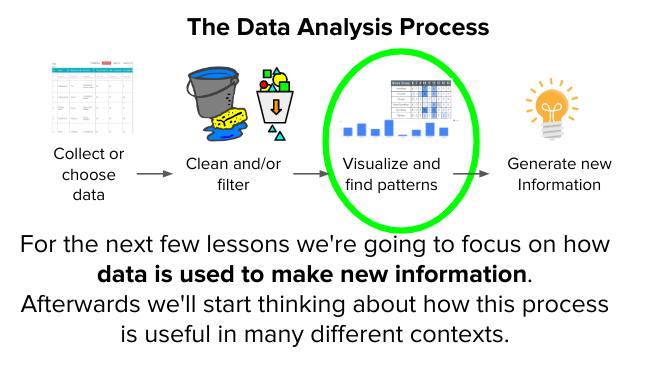
27
New cards
algorithm search types
most efficient: binary
least efficient: exponential (or factorial if a choice in q) both being unreasonable
least efficient: exponential (or factorial if a choice in q) both being unreasonable
28
New cards
sum()
finds the sum of numbers in an array(s)
29
New cards
countif()
finding how many times a # appears:
countif(range of data beginning:range of data ending, #)
ex: countif(A2:A13, 5) indicates array A value beginning with cell 2 and ending with cell 13, trynna find how many times the number 5 is a part of this array
\
countif(range of data beginning:range of data ending, ‘ ‘)
ex: countif(A2:A13, ‘Green’) indicates array A value beginning with cell 2 and ending with cell 13, trynna find how many times the color Green is a part of this array
countif(range of data beginning:range of data ending, #)
ex: countif(A2:A13, 5) indicates array A value beginning with cell 2 and ending with cell 13, trynna find how many times the number 5 is a part of this array
\
countif(range of data beginning:range of data ending, ‘ ‘)
ex: countif(A2:A13, ‘Green’) indicates array A value beginning with cell 2 and ending with cell 13, trynna find how many times the color Green is a part of this array
30
New cards
Bunk or Valid?
1. Regular bitrate upgrades protect you against cyber attacks.
2. Antivirus programs aim to protect computers against malware.
3. The FBI developed ransomware to defend against hackers encrypting other people’s data.
4. A brute force attack tries all possible letters, numbers, and special characters in an attempt to reverse an encrypted password.
5. The health industry uses antivirus software to track the spread of communicable diseases.
6. Data backups are often encrypted in a distant, secure location, often in an underground climate-controlled “tomb.”
7. Hackers phish for unsecure computers using automated tools.
8. In a spear phishing attack, a thief contacts a user pretending to be their manager or close acquaintance.
1. Regular bitrate upgrades protect you against cyber attacks.
2. Antivirus programs aim to protect computers against malware.
3. The FBI developed ransomware to defend against hackers encrypting other people’s data.
4. A brute force attack tries all possible letters, numbers, and special characters in an attempt to reverse an encrypted password.
5. The health industry uses antivirus software to track the spread of communicable diseases.
6. Data backups are often encrypted in a distant, secure location, often in an underground climate-controlled “tomb.”
7. Hackers phish for unsecure computers using automated tools.
8. In a spear phishing attack, a thief contacts a user pretending to be their manager or close acquaintance.
1. bunk
2. valid
3. bunk
4. valid
5. bunk
6. bunk
7. bunk
8. valid
31
New cards
Define
1. computing innovation
2. personally identifiable information (PII)
3. phishing
4. keylogging
5. malware
6. encryption
7. decryption
8. symmetric key encryption
9. public key encryption
10. password security math
1. computing innovation
2. personally identifiable information (PII)
3. phishing
4. keylogging
5. malware
6. encryption
7. decryption
8. symmetric key encryption
9. public key encryption
10. password security math
1. innovation in CS
2. passwords, IP address, sensitive & personal info
3. feigning legitimacy by attaching to a valid file to get a person to reveal their PII
4. tool to record a victims every keystroke and sends to the attacker
5. malicious software intended to compromise a computer system
6. converting info and data into code
7. converting code back to its original
8. private key encryption, uses the same key to encrypt and decrypt information
9. assymetric encryption, uses a public key to encrypt and a private key to decrypt information, the most secure & reliable form of encryption.
10. 26^number of letters in a word
32
New cards
phishing indicators
* Spelling errors.
* Unusual requests.
* Strange email content.
* Personal information solicitation.
* Unfamiliar email addresses.
* Unusual requests.
* Strange email content.
* Personal information solicitation.
* Unfamiliar email addresses.
33
New cards
average()
finds the average number for a list(s)
=average(letter#:letter#)
=average(B2:E2)
=average(letter#:letter#)
=average(B2:E2)
34
New cards
stdev()
how widely varied your range of numbers are from the average (central point aka the mean)
=stdev(letter#:letter#)
=stdev(A2:A10)
=stdev(letter#:letter#)
=stdev(A2:A10)
35
New cards
unique()
returns a list of unique values in an array/list
36
New cards
T or F?
correlation calculation needs numeric responses
correlation calculation needs numeric responses
True, must be numbers. Letter numbers don’t count and numbers with ‘‘ or something similar won’t work. Must be a clean # like 5 not ‘5’ or five.
37
New cards
T or F?
correlation calculation needs clean data
correlation calculation needs clean data
True, data must be consistent and free from corruption and mistakes. EX: In a list of numbers they should all be #’s so some boxes shouldn’t have letter numbers like four or ‘‘ in them like ‘4’, all should be like 4 5 6 7
38
New cards
– 2 types are…
button and text
39
New cards
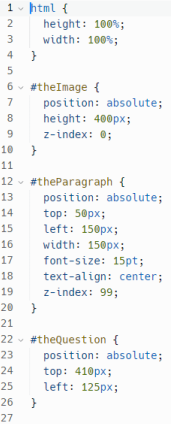
z-index
where an element is in relation to other elements, basically the depth.
ex: u have image1 and image2
image1 has a z index of 0
and image2 has a z index of 1
image2 will be in front of image1
because the z index is higher
ex: u have image1 and image2
image1 has a z index of 0
and image2 has a z index of 1
image2 will be in front of image1
because the z index is higher
40
New cards
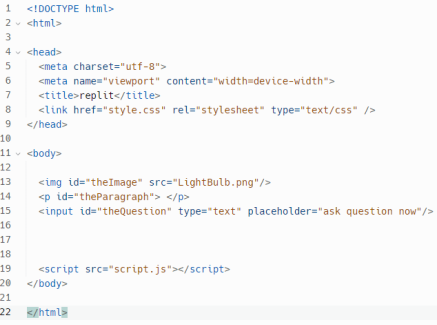
css element to put an image in
attributes are:
src- adds the source/link of the image, and
alt- if the image cannot be shown then shows text as an ALTERNATIVE
width- width of the image
height- height of the image
\
attributes are:
src- adds the source/link of the image, and
alt- if the image cannot be shown then shows text as an ALTERNATIVE
width- width of the image
height- height of the image
\
41
New cards
CSS ID elements must have what 3 components?
be written in camelCase and have a # before and { after
\#theImage {
\#theImage {
42
New cards
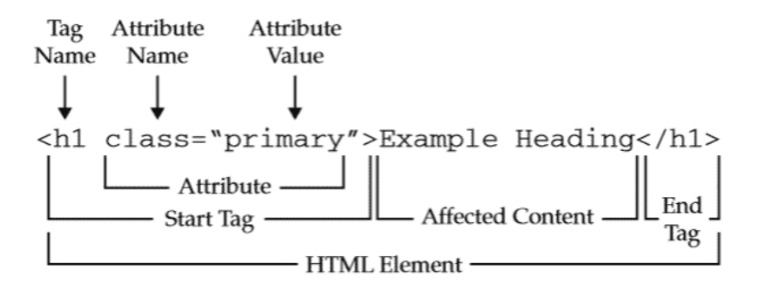
how to open and close HTML code
open & close:
\
self-closing:
\
self-closing:
43
New cards
-
biggest heading level
smallest heading level
44
New cards
vs
includes the meta elements i.e info abt the content
closes the head
has the contents of the code
closes the body
45
New cards
T or F
both tags and ID’s must have a # before them in CSS
both tags and ID’s must have a # before them in CSS
false, ID’s must because ID’s are particular, but tags don’t
46
New cards
CSS
47
New cards
JavaScript

48
New cards
HTML
49
New cards
position: absolute;
makes the position of an element absolute aka set in the top and left locations
position: absolute;
top: 410px;
left: 120px;
position: absolute;
top: 410px;
left: 120px;
50
New cards
CSS rules: property + value
property + value is the declaration of a CSS property name and its value
ex:
\#theParagraph {
position: absolute;
top: 400px;
color: red;
z-index: 0;
height: 100%;
}
ex:
\#theParagraph {
position: absolute;
top: 400px;
color: red;
z-index: 0;
height: 100%;
}
52
New cards
Math.random() output
outputs a random number larger from the given specified range, is bigger than 0.0 but smaller than 1.0, is effectively a percentage
53
New cards
addEventListener()
attaches an event handler to an element
54
New cards
creative commons license
international ngo designed to determine what rights you want to preserve for your intellectual property when putting it on the internet, point of creative commons is to get creators to grant public permission of their stuff to expand the amount of creative works on the internet
55
New cards
putting styles on element IDs vs every element created by an HTML tag such as
etc
putting styles on element IDs means the attributes which personalize elements like color and size. elements created by an HTML tag are opened and closed by said tags with contents inside involving the attributes, making the whole line an element.