CSE 4471INCIDENT RESPONSE AND CONTINGENCY PLANNING 2 OF 2 *3/20
1/33
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced |
|---|
No study sessions yet.
34 Terms
Industry recommendations for data backups
“3-2-1 backup rule,”
3: three copies of important data
2: on at least two different media,
1: with at least one copy stored off-site
Daily on-site backups
Weekly off-site backups
Types of Backup
Full- Entire data set, regardless of any previous backups or circumstances
Differential- Additions and alternations since the most recent full backup
Incremental- additions and alterations since the most recent incremental backup
Incident Response
Detecting, reacting to, and recovering from attacks, employee errors, service outages, and small-scale natural disasters
Incident Response Planning (IRP)
The preparation for such an effort and is performed by the IRP team (IRPT).
Incident:
Adverse event that manifests itself as a real threat to information
Computer Security Incident Response Team (CSIRT):
An IR team composed of technical IT, managerial IT, and InfoSec professionals who are prepared to react to, and recover from an incident
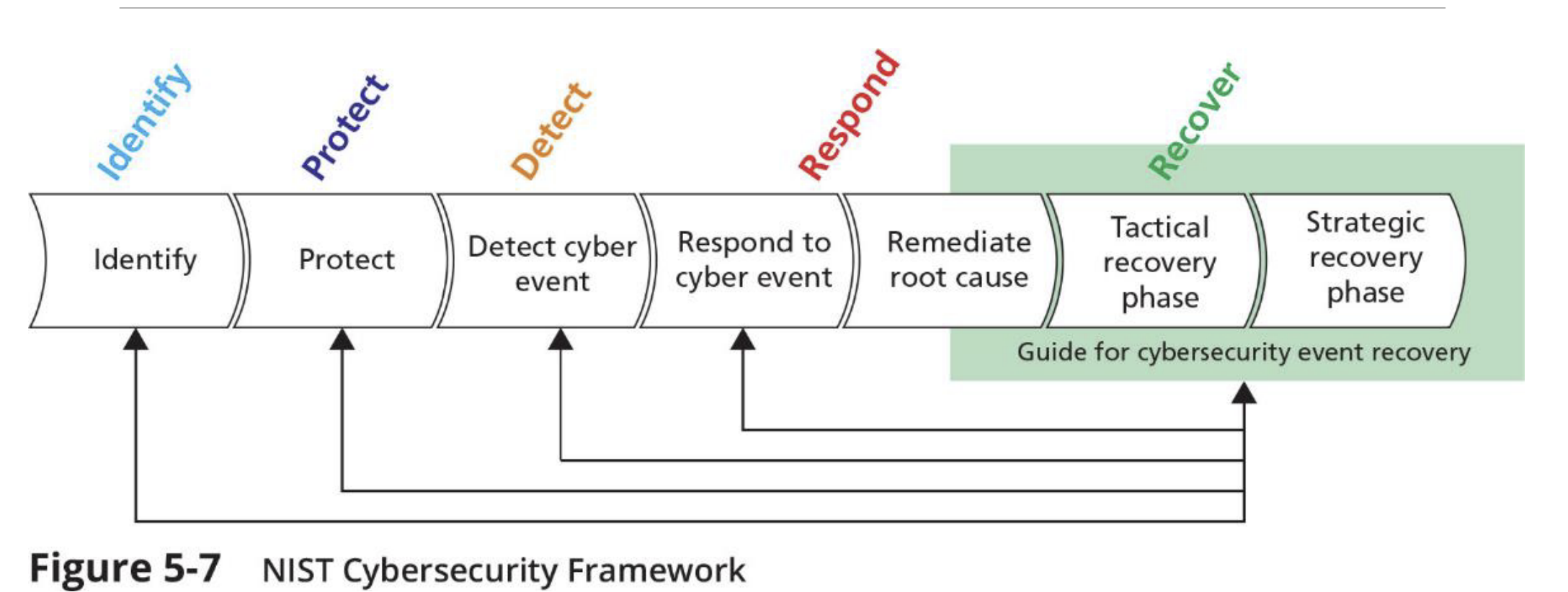
NIST Cybersecurity Framework
Incident Response Policy-NIST SP 800-61, Rev. 2: The Computer Security Incident Handling Guide identifies:
◦ Statement of management commitment
◦ Purpose and objectives of the policy
◦ Scope of the policy (to whom and what it applies and under what circumstances)
◦ Definition of InfoSec incidents and related terms
◦ Organizational structure and definition of roles, responsibilities, and levels of authority
◦ Prioritization or severity ratings of incidents
◦ Performance measures
◦ Reporting and contact forms
When a threat becomes a valid adverse event, it is classified as an InfoSec incident if:
◦ It is directed against information assets.
◦ It has a realistic chance of success.
◦ It threatens the confidentiality, integrity, or availability of information resources and assets.
Creation of an organization’s IR plan usually falls to the CISO, or an IT manager with security responsibilities. According to NIST SP 800-61, the IR plan includes:
◦ Mission ◦ Strategies and goals ◦ Senior management approval ◦ Organizational approach to incident response ◦ How the incident response team will communicate ◦ Metrics for measuring incident response capability and effectiveness ◦ Roadmap for maturing incident response capability ◦ How the program fits into the overall organization
For every incident scenario, the CP team creates three sets of incident handling procedures:
◦ During the incident
◦ After the incident
◦ Before the incident
The execution of the IR plan typically falls to the:
computer security incident response team (CSIRT). CSIRT is composed of technical and managerial IT and InfoSec professionals prepared to diagnose and respond to an incident.In some organizations, it may be a loose or informal association of IT and InfoSec staffers who would be called up if an attack were detected. In other, more formal implementations, the CSIRT is a set of policies, procedures, technologies, people, and data put in place to prevent, detect, react to, and recover from an incident.
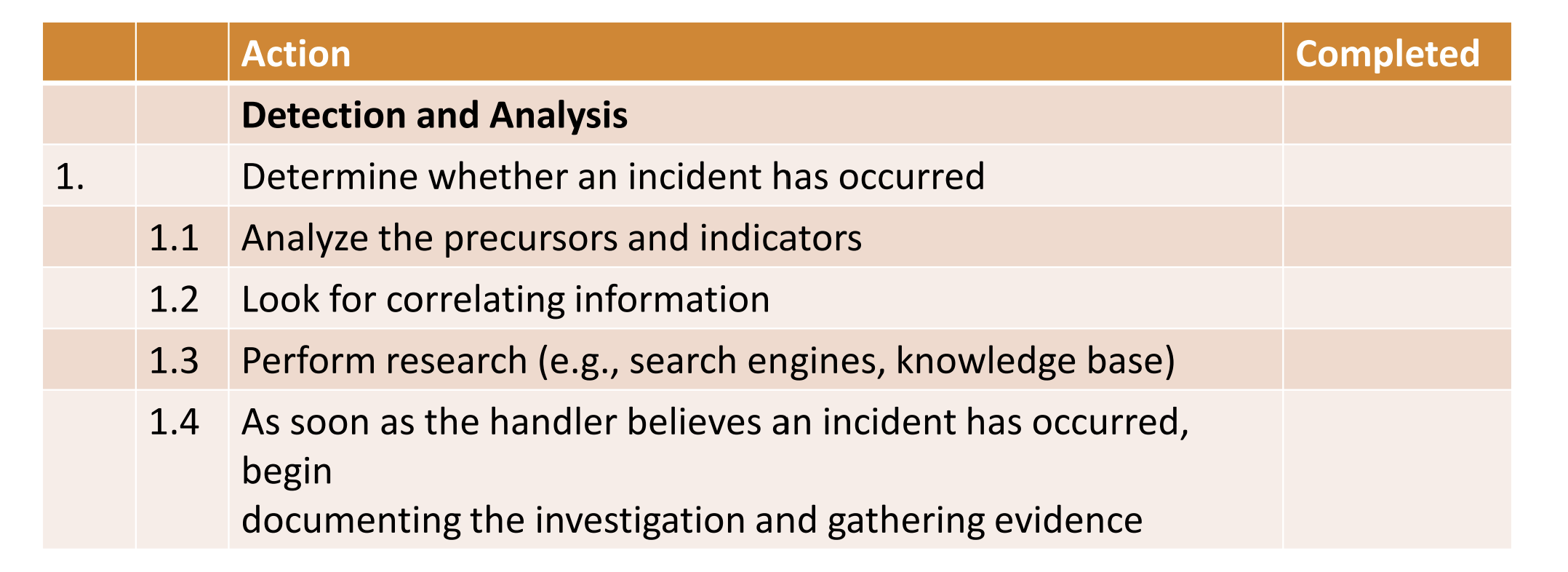
NIST SP 800-61 Incident Handling Checklist
Incident Indicators
Possible indicators
◦ Presence of unfamiliar files ◦ Presence or execution of unknown programs or processes ◦ Unusual consumption of computing resources ◦ Unusual system crashes
Probable indicators
◦ Activities at unexpected times ◦ Presence of new accounts ◦ Reported attacks ◦ Notification from IDS
Definite indicators
◦ Use of dormant accounts ◦ Changes to logs ◦ Presence of hacker tools ◦ Notifications by partner or peer ◦ Notification by hacker
Potential incident results
◦ Loss of availability ◦ Loss of integrity ◦ Loss of confidentiality ◦ Violation of policy ◦ Violation of law
Incident containment strategies focus on two tasks:
◦ Stopping the incident
◦ Recovering control of the affected systems
Typical containment strategies include:
◦ Disabling compromised user accounts
◦ Reconfiguring a firewall to block the problem traffic
◦ Temporarily disabling the compromised process or service
◦ Disconnecting the conduit application or server
◦ Disconnecting the affected network or network segment
◦ Stopping computers and network devices
Digital Forensics
Used for two key purposes: ◦ To investigate allegations of digital malfeasance ◦ To perform root cause analysis Organization chooses one of two approaches: ◦ Protect and forget (patch and proceed) ◦ Apprehend and prosecute (pursue and prosecute)