Encryption Technologies - CompTIA Security+ SY0-701 - 1.4
1/10
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
11 Terms
Trusted Platform Module (TPM)
• A specification for cryptographic functions
- Hardware to help with encryption functions
• Cryptographic processor
- Random number generator, key generators
• Persistent memory
- Comes with unique keys burned in during production
• Versatile memory
- Storage keys, hardware configuration information
- Password protected / No dictionary attacks
Hardware Security Model (HSM)
Used in large environments
- Clusters, redundant power
- Securely store thousands of cryptographic keys
High-end cryptographic hardware
- Plugin card or separate hardware device
Key backup
- Secure storage in hardware
Cryptographic accelerators
- Offload that CPU overhead from other devices
Key Management System (KMS)
Services are everywhere
- On premisis, cloud based
- Many different keys for many different services
Manage all keys from a centralized manager
- Often provided as third party software
- Separate the encryption keys from the data
All key management from one console
- Create keys for a specific service or cloud provider (SSL/TLS, SSH, etc.)
- Associate keys with specific users
- Rotate keys on regular intervals
- Log key use and important events
Keeping data private
• Our data is located in many different places
- Mobile phones, cloud, laptops, etc.
- The most private data is often physically closest to us
• Attackers are always finding new techniques
- It's a race to stay one step ahead
• Our data is changing constantly
- How do we keep this data protected?
Secure enclave
• A protected area for our secrets
- Often implemented as a hardware processor
- Isolated from the main processor
- Many different technologies and names
• Provides extensive security features
- Has its own boot ROM
- Monitors the system boot process
- True random number generator
- Real-time memory encryption
- Root cryptographic keys
- Performs AES encryption in hardware
- And more...
Obfuscation
• The process of making something unclear
- It's now much more difficult to understand
• But it's not impossible to understand
- If you know how to read it
• Hide information in plain sight
- Store payment information without storing a
credit card number
• Hide information inside of an image
- Steganography
Steganography
• Greek for "concealed writing"
- Security through obscurity
• Message is invisible
- But it's really there
• The covertext
- The container document or file
Common steganography techniques
Network Based:
- Embed messages in TCP Packets
Image:
- Embed message within an image
Invisible Watermarks:
- Yellow dots on printer
Other steganagraphy types
Audio steganography
- Modify the digital audio file
- Interlace a secret message within the audio
- Similar technique to image stegonagraphy
Video steganography
- A sequence of images
- Use image steganography on a larger scale
- Manage the signal to noise ratio
- Potentially transfer much more information
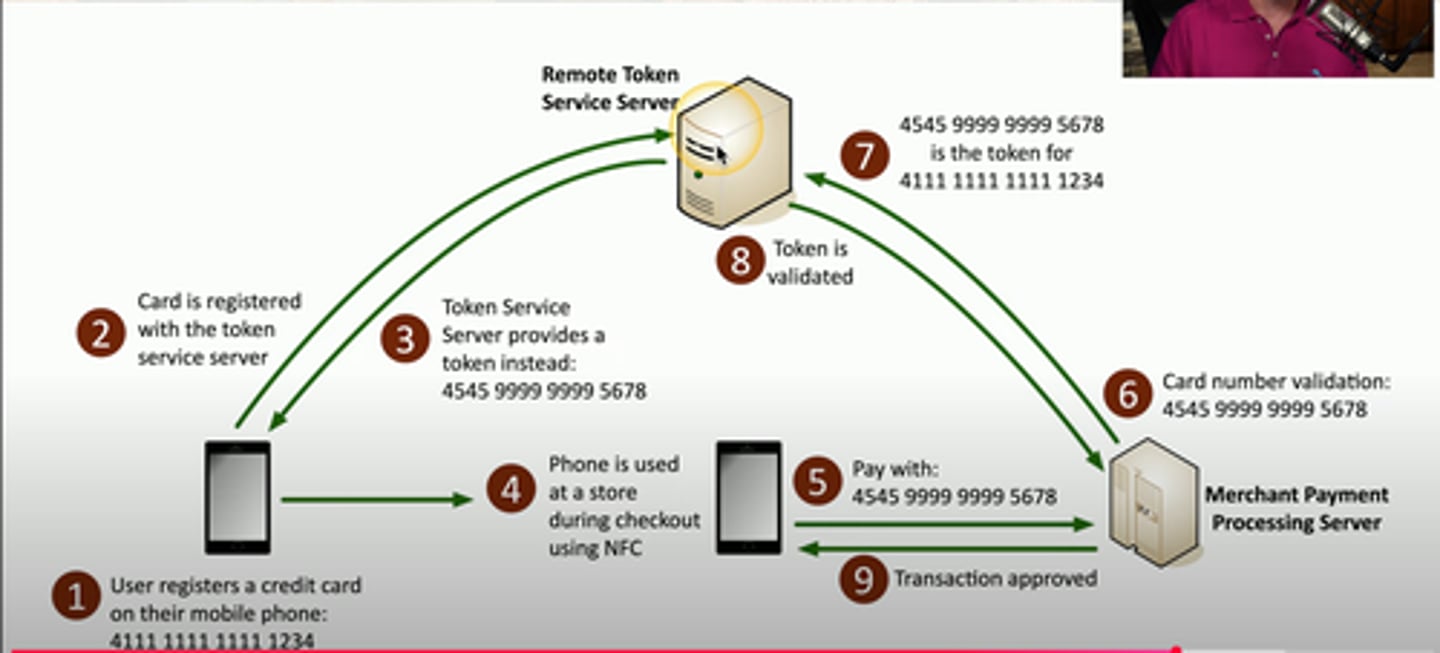
Tokenization
Replace sensitive data with non-sensitive tokens.
- SSN 266-12-1112 is not 691-61-8539
Common with credit card processing
- Use a temp token during payment
- An attacker capturing the card numbers can't use them later
This isn't encryption or hashing
- The original data and token aren't mathematically related
Data Masking
• Data obfuscation
- Hide some of the original data
• Protects PII
- And other sensitive data
• May only be hidden from view
- The data may still be intact in storage
- Control the view based on permissions
• Many different techniques
- Substituting, shuffling, encrypting, masking out, etc.