OCR Computing A Level - Unit 04 - Exchanging data
0.0(0)
Card Sorting
1/46
Earn XP
Description and Tags
Last updated 8:44 AM on 4/18/23
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
47 Terms
1
New cards
Lossy compression
Non-essential data is permanently removed
JPEG and MP3 use lossy compression
JPG removes data permanently to reduce file size then tries to reconstruct without the missing data
MP3 removes the sound in frequency ranges that are outside of human hearing or least affect the perceived playback quality, and quieter notes played at the same time as louder sounds are also removed
JPEG and MP3 use lossy compression
JPG removes data permanently to reduce file size then tries to reconstruct without the missing data
MP3 removes the sound in frequency ranges that are outside of human hearing or least affect the perceived playback quality, and quieter notes played at the same time as louder sounds are also removed
2
New cards
Lossless compression
Patterns in the data are spotted and summarised in a shorter format without permanently removing any information
Works by recording patterns in the data rather than the data itself, meaning a new file can be replicated without any loss of data
PNG and GIF use lossless compression
Works by recording patterns in the data rather than the data itself, meaning a new file can be replicated without any loss of data
PNG and GIF use lossless compression
3
New cards
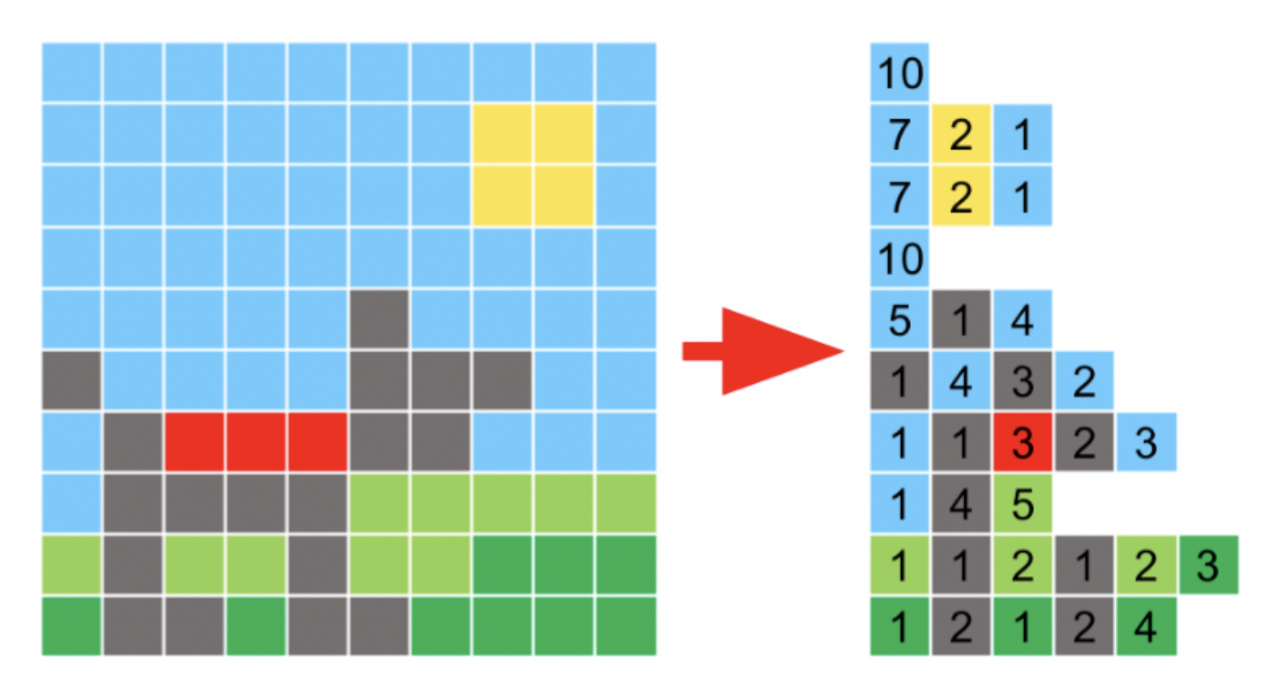
Run Length Encoding (RLE)
A basic method of lossless compression that summarises consecutive patterns of the same data
Works well with image and sound where data could be repeated many times
A sound recording could have thousands of samples taken a second, so the same sound or note played for a fraction of a second could result in hundreds of identical samples, so RLE records one example of the sample and how many times it consecutively repeats
Works well with image and sound where data could be repeated many times
A sound recording could have thousands of samples taken a second, so the same sound or note played for a fraction of a second could result in hundreds of identical samples, so RLE records one example of the sample and how many times it consecutively repeats
4
New cards
Dictionary compression
Spots regularly occurring data and stores it separately in a dictionary
The reference to the entry in the dictionary is stored in the main file, reducing the original data stored
Even though the dictionary produces additional overheads, the space saving negates this problem
The reference to the entry in the dictionary is stored in the main file, reducing the original data stored
Even though the dictionary produces additional overheads, the space saving negates this problem
5
New cards
Encryption
A way of making sure data cannot be understood if you don’t possess the means to decrypt it
Encrypts and decrypts by performing an XOR operation with a shared key, bit by bit
Encrypts and decrypts by performing an XOR operation with a shared key, bit by bit
6
New cards
Plaintext
The message to be sent before encryption
7
New cards
Ciphertext
The plaintext is encrypted using a cipher algorithm and key into equivalent ciphertext, which can then be decrypted back into plaintext using the same or different key
8
New cards
Caesar cipher
Most basic type of encryption and most insecure
Letters of the alphabet are shifted by a consistent amount
Letters of the alphabet are shifted by a consistent amount
9
New cards
Brute force attack
An attack which attempts to apply every possible key to decrypt ciphertext until one works
10
New cards
Frequency analysis
Letters are not used equally often; in english, E is the most common letter (followed by T,A,O,I,N,S,R,H)
This attack analyses patterns in language to check possibilities and make substitutions of letters in ciphertext to break substitution ciphers
This attack analyses patterns in language to check possibilities and make substitutions of letters in ciphertext to break substitution ciphers
11
New cards
Vernam cipher
The encryption key, also known as a one-time pad, is unbreakable
The key must be a truly random sequence greater than or equal in length than the plaintext and only ever used once
Shared with the recipient by hand, independently of the message and destroyed immediately after use
The key must be a truly random sequence greater than or equal in length than the plaintext and only ever used once
Shared with the recipient by hand, independently of the message and destroyed immediately after use
12
New cards
One-time pad
Must be truly random, generated from a physical or unpredictable phenomenon (e.g. atmospheric noise, radioactive decay, snapshots of a lava lamp)
A truly random key will render any frequency analysis useless as it would half a uniform distribution
Computer generated ‘random’ sequences are not actually random
A truly random key will render any frequency analysis useless as it would half a uniform distribution
Computer generated ‘random’ sequences are not actually random
13
New cards
Database
A structured way to store data so that it can be retrieved using queries
Can hold data about several entities
Can hold data about several entities
14
New cards
Uses of a database
School use -- management information such as SIMS or iSAMS, learning platforms such as Google Classroom
Organisation or business use -- customer relationship management software, online calendars, backend of most websites to dynamically generate pages
Personal use -- social media data, multiplayer games
Organisation or business use -- customer relationship management software, online calendars, backend of most websites to dynamically generate pages
Personal use -- social media data, multiplayer games
15
New cards
Flat file
Simplest kind of database
Consists of information about a single entity
Consists of information about a single entity
16
New cards
Entity
An object, person, event or thing of interest about which data needs to be recorded
Entity descriptions can be written in format: e.g: Customer(__custID__, title, firstname, surname, email)
Each entity needs an identifier which uniquely identifies a particular record, known as the primary key
Entity descriptions can be written in format: e.g: Customer(__custID__, title, firstname, surname, email)
Each entity needs an identifier which uniquely identifies a particular record, known as the primary key
17
New cards
Natural primary key
A naturally occurring unique identifier
E.g. mobile number, national insurance number
E.g. mobile number, national insurance number
18
New cards
Composite primary key
When 2+ attributes are needed to uniquely identify a record
19
New cards
Secondary key
In some databases, searches may often need to be made on other fields than just the primary key
If searches often need to be made on title or subject, either or both of these fields could be defined as a secondary key, and then would be indexed for faster lookups
If searches often need to be made on title or subject, either or both of these fields could be defined as a secondary key, and then would be indexed for faster lookups
20
New cards
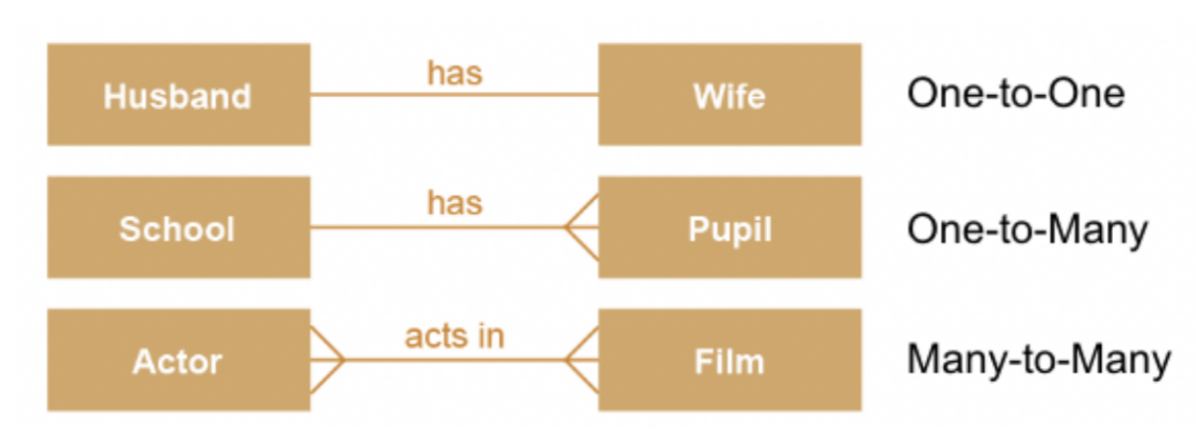
Entity relationships
One-to-one (e.g: husband and wife)
One-to-many (e.g: mother and child, school and pupil)
Many-to-many (e.g: actor and film, recipe and ingredient)
One-to-many (e.g: mother and child, school and pupil)
Many-to-many (e.g: actor and film, recipe and ingredient)
21
New cards
Entity-relationship diagram
A graphical way of representing relationships between entities
22
New cards
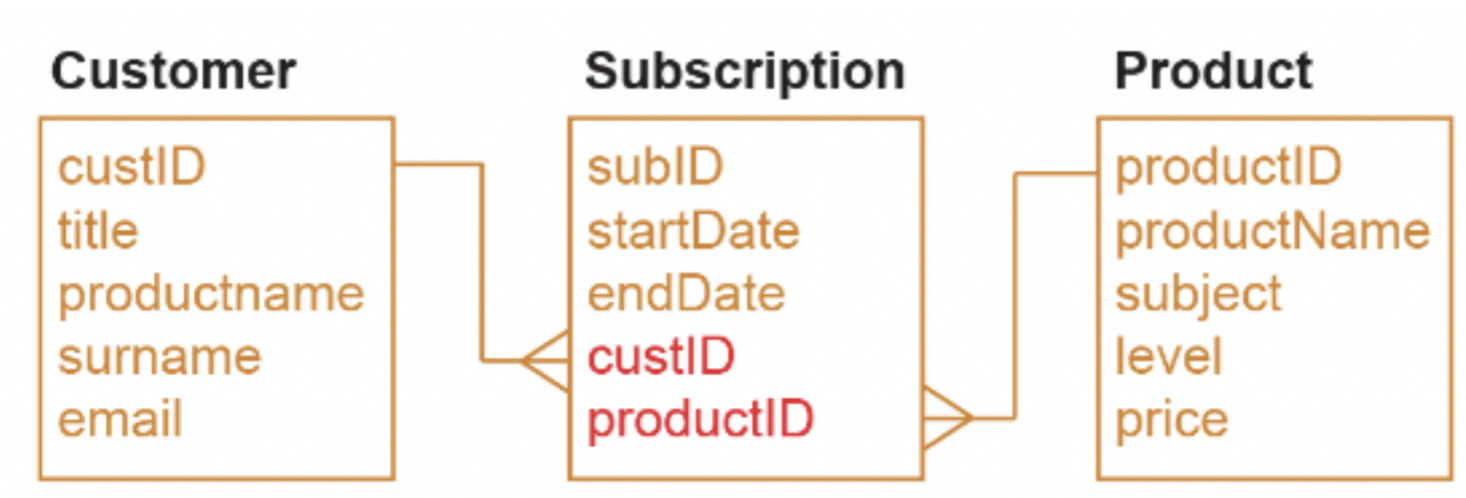
Foreign key
An attribute that creates a join between 2 tables (relations)
It is the primary key in the first relation
It always goes on the ‘many’ side of a relationship
It is the primary key in the first relation
It always goes on the ‘many’ side of a relationship
23
New cards
Referential integrity
No foreign key in one table can reference a non-existent record in a related table -- all data is consistent over entire database
Values in fields should be atomic (a single attribute cannot consist of 2 data items, e.g: first name and surname)
No 2 records can be identical
Each table needs a primary key
Values in fields should be atomic (a single attribute cannot consist of 2 data items, e.g: first name and surname)
No 2 records can be identical
Each table needs a primary key
24
New cards
Normalisation
A process used to come up with the best possible design for a database
No duplication, consistent data, flexibility, complex querying
No duplication, consistent data, flexibility, complex querying
25
New cards
Partial dependency
When the fields are only dependent on part of the primary key (only occurs if primary key is a composite key)
26
New cards
Non-key dependency
Where the value of a field is determined by the value of another field that isn’t part of the primary key
27
New cards
First Normal Form (1NF)
A table contains no repeating attributes or groups of attributes
All field names must be unique
Values in fields should be the same domain
Values in fields should be atomic (lowest level of detail; a single attribute cannot consist of 2 data items)
No two records can be identical
Each table needs a primary key
All field names must be unique
Values in fields should be the same domain
Values in fields should be atomic (lowest level of detail; a single attribute cannot consist of 2 data items)
No two records can be identical
Each table needs a primary key
28
New cards
Second Normal Form (2NF)
Ensure data is already in 1NF, all partial dependencies have been removed
(partial dependencies fixed by splitting table so that the part of the composite key becomes the primary key of a new table, with all fields solely dependent on the key put into the table)
If a field or group of fields can be inferred from a field that isn’t a primary key, then they can be split into a separate table
(partial dependencies fixed by splitting table so that the part of the composite key becomes the primary key of a new table, with all fields solely dependent on the key put into the table)
If a field or group of fields can be inferred from a field that isn’t a primary key, then they can be split into a separate table
29
New cards
Third Normal Form (3NF)
Ensure data is already in 2NF, any transitive dependencies have been removed
(remove any non-key dependencies)
‘The fields are dependent on the key, the whole key and nothing but the key’
(remove any non-key dependencies)
‘The fields are dependent on the key, the whole key and nothing but the key’
30
New cards
SQL
Structured Query Language
A declarative language used for creating, querying and updating tables in a relationship
A declarative language used for creating, querying and updating tables in a relationship
31
New cards
Common data types in SQL
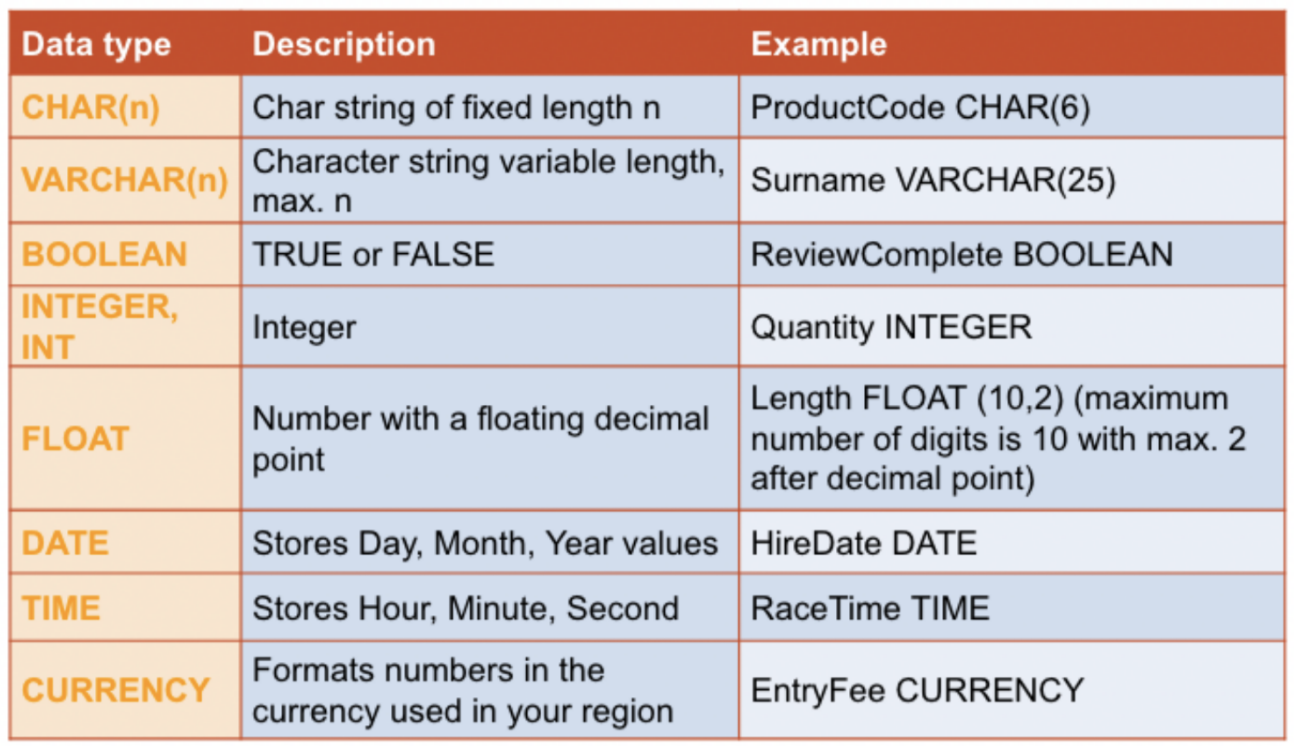
32
New cards
Everyday methods of data capture
Barcode scanners
Cookies
Contactless
Form/census
Cookies
Contactless
Form/census
33
New cards
Automated methods of data capture
Smart card readers
Scanners
Optical character recognition (OCR)
Optical mark recognition (OMR)
Magnetic ink character recognition
Sensors
Scanners
Optical character recognition (OCR)
Optical mark recognition (OMR)
Magnetic ink character recognition
Sensors
34
New cards
Methods of inputting data into database
Automatically, using a DBMS software
Typing manually into customised form
Importing from spreadsheet or file
Using EDI (Electronic Data Interchange) -- used to transfer data between one computer system and another
Typing manually into customised form
Importing from spreadsheet or file
Using EDI (Electronic Data Interchange) -- used to transfer data between one computer system and another
35
New cards
EDI (Electronic Data Interchange)
The computer-to-computer exchange of documents such as purchase orders, invoices, shipping documents between 2 companies or business partners, etc.
It replaces post, email or fax
All documents must be in a standard format so that the computer can understand them, to reduce errors and confusion in systems
It replaces post, email or fax
All documents must be in a standard format so that the computer can understand them, to reduce errors and confusion in systems
36
New cards
Transaction processing
A single logical operation in databases is defined as a transaction
It may consist of several operations, all of which must be processed and checked appropriately
It may consist of several operations, all of which must be processed and checked appropriately
37
New cards
ACID
Atomicity, Consistency, Isolation, Durability
A set of properties to ensure that the integrity of the database is remained under all circumstances
A set of properties to ensure that the integrity of the database is remained under all circumstances
38
New cards
Atomicity
This property requires that a transaction is processed in its entirety or not at all
In any situation, including power cuts or hard disk crashes, it is not possible to process only part of a transaction
In any situation, including power cuts or hard disk crashes, it is not possible to process only part of a transaction
39
New cards
Consistency
This property ensures that no transaction can violate any of the defined validation rules/referential integrity is upheld
Any changes to a database have to be reflected across the entire database (e.g: if a part of a table has been removed, all other instances of that part in other tables have to be fully removed as well
Any changes to a database have to be reflected across the entire database (e.g: if a part of a table has been removed, all other instances of that part in other tables have to be fully removed as well
40
New cards
Isolation
This property ensures that concurrent execution of transactions leads to the same result as if transactions were processed one after the other
Crucial to a multi-user database
Any transactions that are happening at the same time cannot affect the quality and consistency of the data
Crucial to a multi-user database
Any transactions that are happening at the same time cannot affect the quality and consistency of the data
41
New cards
Durability
This property ensures that once a transaction has been committed, it will remain so, even in the event of an issue such as a power cut or system crash
All information is stored, non-volatile and can be retrieved later
As each part of a transaction is completed, it is held in a buffer on disk until all elements of the transaction have been completed, only then will changes be made to database tables
All information is stored, non-volatile and can be retrieved later
As each part of a transaction is completed, it is held in a buffer on disk until all elements of the transaction have been completed, only then will changes be made to database tables
42
New cards
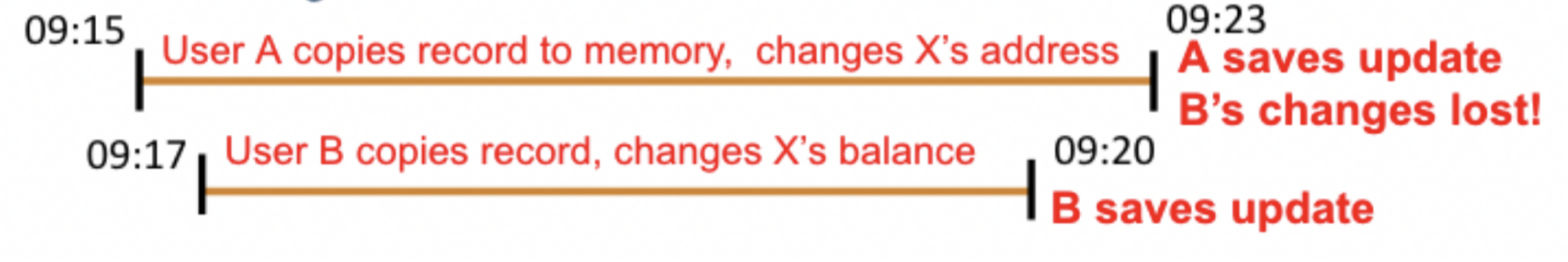
Potential problems with multi-user databases
Multiple users simultaneously accessing a database could potentially cause one of the updates to be lost
43
New cards
Record locking
Prevents simultaneous access to objects in a database in order to prevent updates being lost or inconsistencies in the data arising
A record is locked when a user retrieves it for editing or updating; anyone else attempting to retrieve it is denied access until the transaction is completed
Issue: could result in a deadlock if 2 users are attempting to update 2 records, and neither can proceed as each has locked the other record
A record is locked when a user retrieves it for editing or updating; anyone else attempting to retrieve it is denied access until the transaction is completed
Issue: could result in a deadlock if 2 users are attempting to update 2 records, and neither can proceed as each has locked the other record
44
New cards
Serialisation
Ensures that transactions do not overlap in time and therefore cannot interfere with each other or lead to updates being lost
Techniques: Timestamp ordering, commitment ordering
Techniques: Timestamp ordering, commitment ordering
45
New cards
Timestamp ordering
Each object in the database has a read timestamp and write timestamp, updated whenever an object is read or written
When a user tries to save an update, if the read timestamp is not the same as it was when they started the transaction, the DBMS knows another user has accessed the same object, so the transaction will be cancelled with an ‘Update unsuccessful’ message sent to the user
When a user tries to save an update, if the read timestamp is not the same as it was when they started the transaction, the DBMS knows another user has accessed the same object, so the transaction will be cancelled with an ‘Update unsuccessful’ message sent to the user
46
New cards
Commitment ordering
Ensures that no transactions are lost of 2 clients are simultaneously trying to update a record
Transactions are ordered in terms of their dependencies on one another as well as the time they were initiated
Can be used to prevent a deadlock by blocking one request until another is completed
Transactions are ordered in terms of their dependencies on one another as well as the time they were initiated
Can be used to prevent a deadlock by blocking one request until another is completed
47
New cards
Redundancy
Duplicate hardware, located in different geographical locations, mirrors every transaction that takes place on the main system, so that if it fails the backup system automatically takes over
Many organisations cannot afford to have their computer systems go down for even a short time (e.g. air traffic control) and so have a built-in redundancy in their computer systems
Many organisations cannot afford to have their computer systems go down for even a short time (e.g. air traffic control) and so have a built-in redundancy in their computer systems