Network Security Tuesday Final Exam
1/153
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced |
|---|
No study sessions yet.
154 Terms
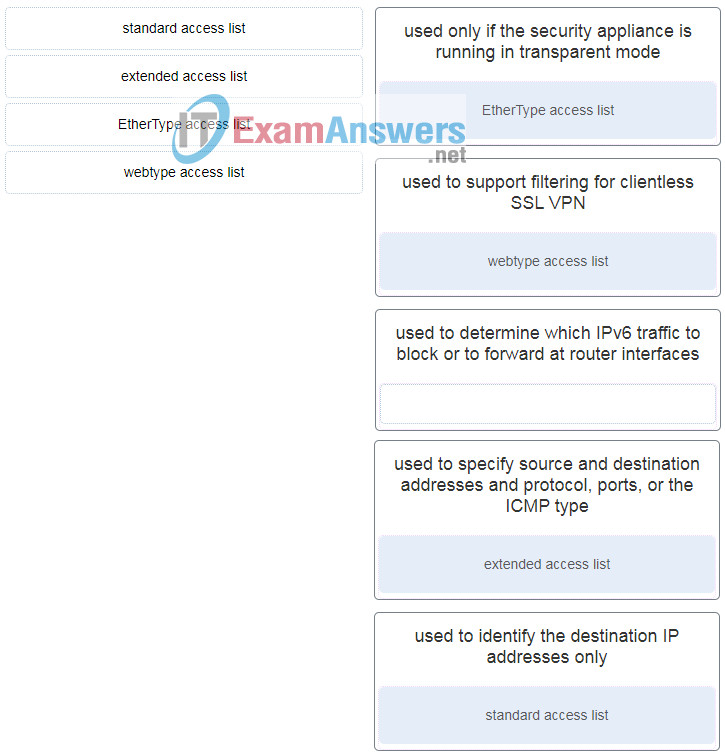
Match each ASA ACL type to its correct description:
extended access lists
webtype access lists
standard access lists
EtherType access lists
Descriptions:
A. used to specify source and destination addresses and protocol, ports, or the ICMP type
B. used to support filtering for clientless SSL VPN
C. used to identify the destination IP addresses only
D. used only if the security appliance is running in transparent mode
A → extended access lists
B → webtype access lists
C → standard access lists
D → EtherType access lists
2. Which statement describes a difference between the Cisco ASA IOS CLI feature and the router IOS CLI feature?
ASA uses the ? command whereas a router uses the help command to receive help on a brief description and the syntax of a command.
To use a show command in a general configuration mode, ASA can use the command directly whereas a router will need to enter the do command before issuing the show command.
To complete a partially typed command, ASA uses the Ctrl+Tab key combination whereas a router uses the Tab key.
To indicate the CLI EXEC mode, ASA uses the % symbol whereas a router uses the # symbol.
To use a show command in a general configuration mode, ASA can use the command directly whereas a router will need to enter the do command before issuing the show command.

3. Refer to the exhibit. A network administrator is configuring AAA implementation on an ASA device. What does the option link3 indicate?
the network name where the AAA server resides
the specific AAA server name
the sequence of servers in the AAA server group
the interface name
the interface name
4. What provides both secure segmentation and threat defense in a Secure Data Center solution?
Cisco Security Manager software
AAA server
Adaptive Security Appliance
intrusion prevention system
Adaptive Security Appliance
5. What are the three core components of the Cisco Secure Data Center solution? (Choose three.)
mesh network
secure segmentation
visibility
threat defense
servers
infrastructure
secure segmentation
visibility
threat defense
6. What are three characteristics of ASA transparent mode? (Choose three.)
This mode does not support VPNs, QoS, or DHCP Relay.
It is the traditional firewall deployment mode.
This mode is referred to as a “bump in the wire.”
NAT can be implemented between connected networks.
In this mode the ASA is invisible to an attacker.
The interfaces of the ASA separate Layer 3 networks and require IP addresses in different subnets.
This mode does not support VPNs, QoS, or DHCP Relay.
This mode is referred to as a “bump in the wire.”
In this mode the ASA is invisible to an attacker.
7. What is needed to allow specific traffic that is sourced on the outside network of an ASA firewall to reach an internal network?
ACL
NAT
dynamic routing protocols
outside security zone level 0
ACL
8. What will be the result of failed login attempts if the following command is entered into a router?
login block-for 150 attempts 4 within 90
All login attempts will be blocked for 150 seconds if there are 4 failed attempts within 90 seconds.
All login attempts will be blocked for 90 seconds if there are 4 failed attempts within 150 seconds.
All login attempts will be blocked for 1.5 hours if there are 4 failed attempts within 150 seconds.
All login attempts will be blocked for 4 hours if there are 90 failed attempts within 150 seconds.
All login attempts will be blocked for 150 seconds if there are 4 failed attempts within 90 seconds.
9. Which two tasks are associated with router hardening? (Choose two.)
placing the router in a secure room
disabling unused ports and interfaces
installing the maximum amount of memory possible
securing administrative access
using uninterruptible power supplies
disabling unused ports and interfaces
securing administrative access
10. Which threat protection capability is provided by Cisco ESA?
web filtering
cloud access security
spam protection
Layer 4 traffic monitoring
spam protection
11. What are two security measures used to protect endpoints in the borderless network? (Choose two.)
denylisting
Snort IPS
DLP
DMZ
rootkit
denylisting
DLP
12. Which three types of traffic are allowed when the authentication port-control auto command has been issued and the client has not yet been authenticated? (Choose three.)
CDP
802.1Q
IPsec
TACACS+
STP
EAPOL
CDP
STP
EAPOL
13. Which statement describes a characteristic of the IKE protocol?
It uses UDP port 500 to exchange IKE information between the security gateways.
IKE Phase 1 can be implemented in three different modes: main, aggressive, or quick.
It allows for the transmission of keys directly across a network.
The purpose of IKE Phase 2 is to negotiate a security association between two IKE peers.
It uses UDP port 500 to exchange IKE information between the security gateways.
14. Which action do IPsec peers take during the IKE Phase 2 exchange?
exchange of DH keys
negotiation of IPsec policy
negotiation of IKE policy sets
verification of peer identity
negotiation of IPsec policy
15. What are two hashing algorithms used with IPsec AH to guarantee authenticity? (Choose two.)
SHA
RSA
DH
MD5
AES
SHA
MD5
16. Which command raises the privilege level of the ping command to 7?
user exec ping level 7
authorization exec ping level 7
accounting exec level 7 ping
privilege exec level 7 ping
privilege exec level 7 ping
17. What is a characteristic of a role-based CLI view of router configuration?
A CLI view has a command hierarchy, with higher and lower views.
When a superview is deleted, the associated CLI views are deleted.
A single CLI view can be shared within multiple superviews.
Only a superview user can configure a new view and add or remove commands from the existing views.
A single CLI view can be shared within multiple superviews.
18. What is a limitation to using OOB management on a large enterprise network?
Production traffic shares the network with management traffic.
Terminal servers can have direct console connections to user devices needing management.
OOB management requires the creation of VPNs.
All devices appear to be attached to a single management network.
All devices appear to be attached to a single management network.
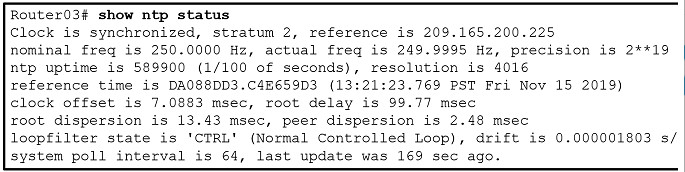
19. Refer to the exhibit. A corporate network is using NTP to synchronize the time across devices. What can be determined from the displayed output?
Router03 is a stratum 2 device that can provide NTP service to other devices in the network.
The time on Router03 may not be reliable because it is offset by more than 7 seconds to the time server.
The interface on Router03 that connects to the time sever has the IPv4 address 209.165.200.225.
Router03 time is synchronized to a stratum 2 time server.
Router03 is a stratum 2 device that can provide NTP service to other devices in the network.
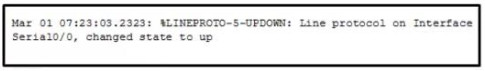
20. Refer to the exhibit. Which two conclusions can be drawn from the syslog message that was generated by the router? (Choose two.)
This message resulted from an unusual error requiring reconfiguration of the interface.
This message indicates that service timestamps have been configured.
This message indicates that the interface changed state five times.
This message is a level 5 notification message.
This message indicates that the interface should be replaced.
This message indicates that service timestamps have been configured.
This message is a level 5 notification message.
21. Which two types of hackers are typically classified as grey hat hackers? (Choose two.)
hacktivists
cyber criminals
vulnerability brokers
script kiddies
state-sponsored hackers
vulnerability brokers
hacktivists
23. Which type of packet is unable to be filtered by an outbound ACL?
multicast packet
ICMP packet
broadcast packet
router-generated packet
router-generated packet
22. When describing malware, what is a difference between a virus and a worm?
A virus focuses on gaining privileged access to a device, whereas a worm does not.
A virus replicates itself by attaching to another file, whereas a worm can replicate itself independently.
A virus can be used to launch a DoS attack (but not a DDoS), but a worm can be used to launch both DoS and DDoS attacks.
A virus can be used to deliver advertisements without user consent, whereas a worm cannot.
A virus replicates itself by attaching to another file, whereas a worm can replicate itself independently.
24. Consider the access list command applied outbound on a router serial interface.
access-list 100 deny icmp 192.168.10.0 0.0.0.255 any echo reply
What is the effect of applying this access list command?
The only traffic denied is echo-replies sourced from the 192.168.10.0/24 network. All other traffic is allowed.
The only traffic denied is ICMP-based traffic. All other traffic is allowed.
No traffic will be allowed outbound on the serial interface.
Users on the 192.168.10.0/24 network are not allowed to transmit traffic to any other destination.
No traffic will be allowed outbound on the serial interface.
25. Which command is used to activate an IPv6 ACL named ENG_ACL on an interface so that the router filters traffic prior to accessing the routing table?
ipv6 access-class ENG_ACL in
ipv6 traffic-filter ENG_ACL out
ipv6 traffic-filter ENG_ACL in
ipv6 access-class ENG_ACL out
ipv6 traffic-filter ENG_ACL in
26. What technology has a function of using trusted third-party protocols to issue credentials that are accepted as an authoritative identity?
digital signatures
hashing algorithms
PKI certificates
symmetric keys
PKI certificates
27. What are two methods to maintain certificate revocation status? (Choose two.)
subordinate CA
OCSP
DNS
LDAP
CRL
OCSP
CRL
28. Which protocol is an IETF standard that defines the PKI digital certificate format?
SSL/TLS
X.500
LDAP
X.509
X.509
29. A network administrator is configuring DAI on a switch. Which command should be used on the uplink interface that connects to a router?
ip arp inspection trust
ip dhcp snooping
ip arp inspection vlan
spanning-tree portfast
ip arp inspection trust
30. What is the best way to prevent a VLAN hopping attack?
Disable trunk negotiation for trunk ports and statically set nontrunk ports as access ports.
Disable STP on all nontrunk ports.
Use VLAN 1 as the native VLAN on trunk ports.
Use ISL encapsulation on all trunk links.
Disable trunk negotiation for trunk ports and statically set nontrunk ports as access ports.
31. What would be the primary reason an attacker would launch a MAC address overflow attack?
so that the switch stops forwarding traffic
so that legitimate hosts cannot obtain a MAC address
so that the attacker can see frames that are destined for other hosts
so that the attacker can execute arbitrary code on the switch
so that the attacker can see frames that are destined for other hosts
32. What is the main difference between the implementation of IDS and IPS devices?
An IDS can negatively impact the packet flow, whereas an IPS can not.
An IDS needs to be deployed together with a firewall device, whereas an IPS can replace a firewall.
An IDS would allow malicious traffic to pass before it is addressed, whereas an IPS stops it immediately.
An IDS uses signature-based technology to detect malicious packets, whereas an IPS uses profile-based technology.
An IDS would allow malicious traffic to pass before it is addressed, whereas an IPS stops it immediately.
33. Which attack is defined as an attempt to exploit software vulnerabilities that are unknown or undisclosed by the vendor?
zero-day
Trojan horse
brute-force
man-in-the-middle
zero-day
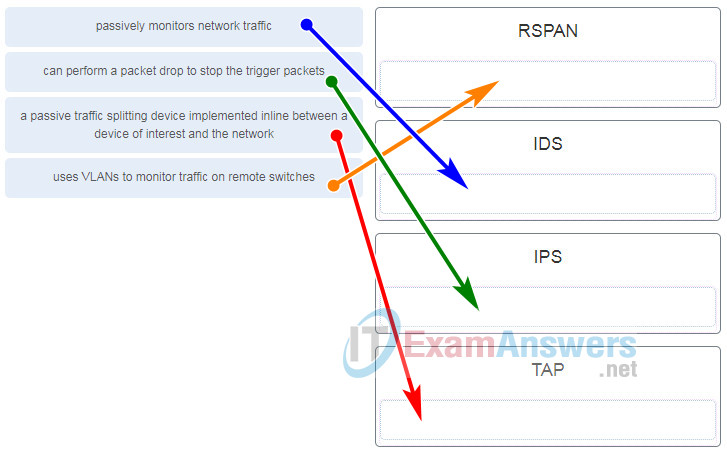
34. Match the network monitoring technology with the description.
Passively monitors network traffic RSPAN
Can perform a packet drop to stop the trigger packets IDS
A passive traffic splitting device implemented inline between a device of interest and the network IPS
Users VLANs to monitor traffic on remote switches TAP
passively monitors network traffic | IDS |
uses VLANs to monitor traffic on remote switches | RSPAN |
a passive traffic splitting device implemented inline between a device of interest and the network | TAP |
can perform a packet drop to stop the trigger packets | IPS |
35. What are the three signature levels provided by Snort IPS on the 4000 Series ISR? (Choose three.)
security
drop
reject
connectivity
inspect
balanced
security
connectivity
balanced
36. What are three attributes of IPS signatures? (Choose three.)
action
length
trigger
type
depth
function
action
trigger
type
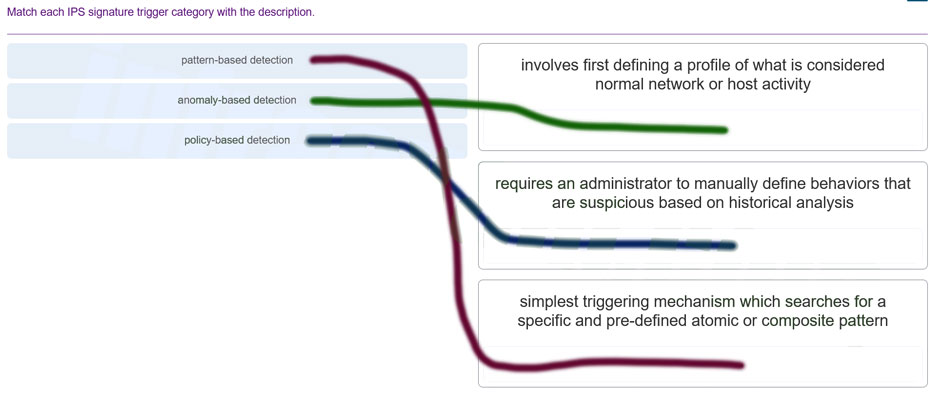
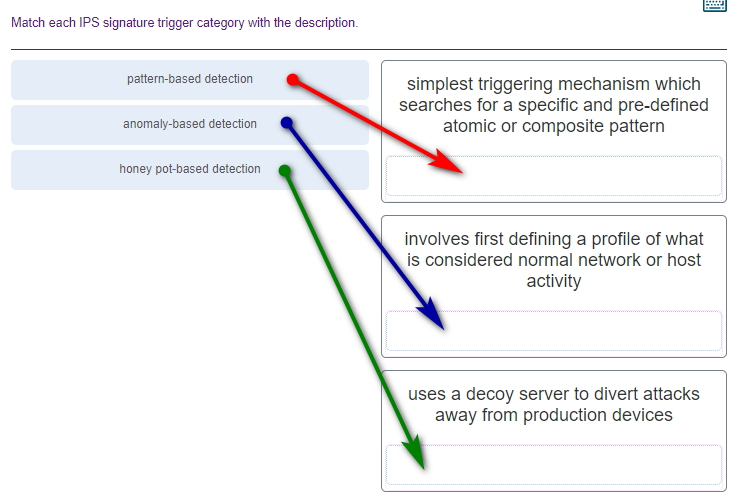
pattern-based detection: simplest triggering mechanism which searches for a specific and pre-defined atomic or composite pattern
anomaly-based detection: involves first defining a profile of what is considered normal network or host activity
honey pot-based detection: uses a decoy server to divert attacks away from production devices
38. Which two features are included by both TACACS+ and RADIUS protocols? (Choose two.)
SIP support
password encryption
802.1X support
separate authentication and authorization processes
utilization of transport layer protocols
password encryption
utilization of transport layer protocols
39. What function is provided by the RADIUS protocol?
RADIUS provides encryption of the complete packet during transfer.
RADIUS provides separate AAA services.
RADIUS provides separate ports for authorization and accounting.
RADIUS provides secure communication using TCP port 49.
RADIUS provides separate ports for authorization and accounting.
40. What are three characteristics of the RADIUS protocol? (Choose three.)
utilizes TCP port 49
uses UDP ports for authentication and accounting
supports 802.1X and SIP
separates the authentication and authorization processes
encrypts the entire body of the packet
is an open RFC standard AAA protocol
uses UDP ports for authentication and accounting
supports 802.1X and SIP
is an open RFC standard AAA protocol
41. Which zone-based policy firewall zone is system-defined and applies to traffic destined for the router or originating from the router?
local zone
inside zone
self zone
system zone
outside zone
self zone
42. What are two benefits of using a ZPF rather than a Classic Firewall? (Choose two.)
ZPF allows interfaces to be placed into zones for IP inspection.
The ZPF is not dependent on ACLs.
Multiple inspection actions are used with ZPF.
ZPF policies are easy to read and troubleshoot.
With ZPF, the router will allow packets unless they are explicitly blocked.
The ZPF is not dependent on ACLs.
ZPF policies are easy to read and troubleshoot.
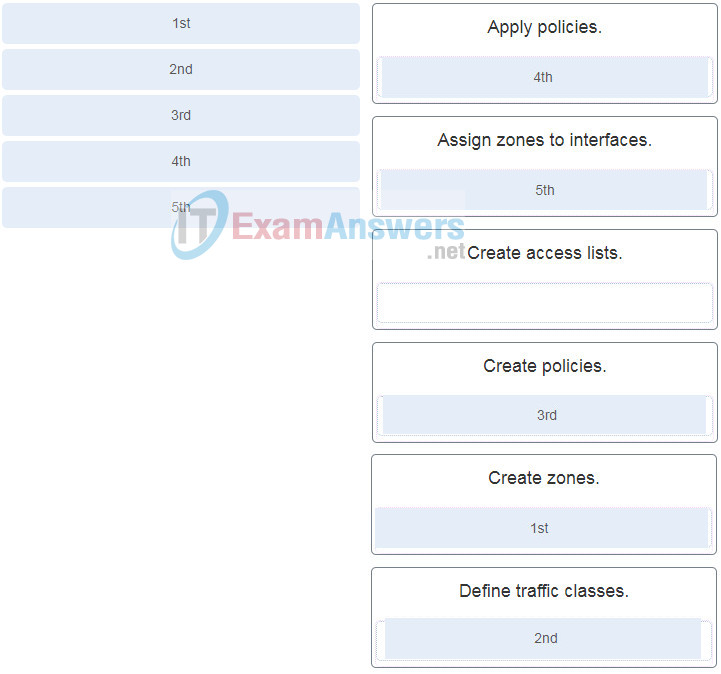
43. Place the steps for configuring zone-based policy (ZPF) firewalls in order from first to last. (Not all options are used.)
2nd | Define traffic classes. |
1st | Create zones. |
4th | Apply policies. |
5th | Assign zones to interfaces. |
3rd | Create policies. |
44. How does a firewall handle traffic when it is originating from the private network and traveling to the DMZ network?
The traffic is selectively denied based on service requirements.
The traffic is usually permitted with little or no restrictions.
The traffic is selectively permitted and inspected.
The traffic is usually blocked.
The traffic is usually permitted with little or no restrictions.
45. Which two protocols generate connection information within a state table and are supported for stateful filtering? (Choose two.)
ICMP
UDP
DHCP
TCP
HTTP
TCP
HTTP
46. Which type of firewall is supported by most routers and is the easiest to implement?
next generation firewall
stateless firewall
stateful firewall
proxy firewall
stateless firewall
47. What network testing tool would an administrator use to assess and validate system configurations against security policies and compliance standards?
Tripwire
L0phtcrack
Nessus
Metasploit
Tripwire
48. What type of network security test can detect and report changes made to network systems?
vulnerability scanning
network scanning
integrity checking
penetration testing
integrity checking
49. What network security testing tool has the ability to provide details on the source of suspicious network activity?
SIEM
SuperScan
Zenmap
Tripwire
SIEM
50 How do modern cryptographers defend against brute-force attacks?
Use statistical analysis to eliminate the most common encryption keys.
Use a keyspace large enough that it takes too much money and too much time to conduct a successful attack.
Use an algorithm that requires the attacker to have both ciphertext and plaintext to conduct a successful attack.
Use frequency analysis to ensure that the most popular letters used in the language are not used in the cipher message.
Use a keyspace large enough that it takes too much money and too much time to conduct a successful attack.
51. How does a Caesar cipher work on a message?
Letters of the message are replaced by another letter that is a set number of places away in the alphabet.
Letters of the message are rearranged randomly.
Letters of the message are rearranged based on a predetermined pattern.
Words of the message are substituted based on a predetermined pattern.
Letters of the message are replaced by another letter that is a set number of places away in the alphabet.
52. What is the main factor that ensures the security of encryption of modern algorithms?
complexity of the hashing algorithm
the use of 3DES over AES
secrecy of the keys
secrecy of the algorithm
secrecy of the keys
53 What is the next step in the establishment of an IPsec VPN after IKE Phase 1 is complete?
negotiation of the ISAKMP policy
negotiation of the IPsec SA policy
detection of interesting traffic
authentication of peers
negotiation of the IPsec SA policy
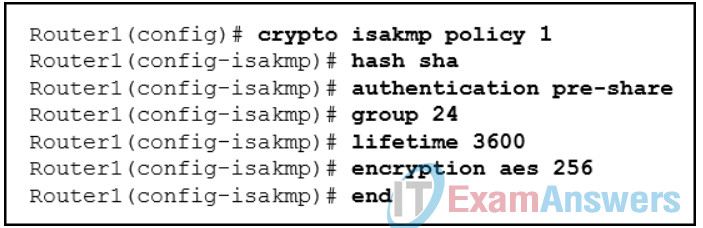
54. Refer to the exhibit. What algorithm will be used for providing confidentiality?
RSA
Diffie-Hellman
DES
AES
AES
55. After issuing a show run command, an analyst notices the following command:
crypto ipsec transform-set MYSET esp-aes 256 esp-md5-hmac
What is the purpose of this command?
It establishes the set of encryption and hashing algorithms used to secure the data sent through an IPsec tunnel.
It defines the default ISAKMP policy list used to establish the IKE Phase 1 tunnel.
It establishes the criteria to force the IKE Phase 1 negotiations to begin.
It indicates that IKE will be used to establish the IPsec tunnel for protecting the traffic.
It establishes the set of encryption and hashing algorithms used to secure the data sent through an IPsec tunnel.
56. Which algorithm can ensure data integrity?
RSA
AES
MD5
PKI
MD5
57. A company implements a security policy that ensures that a file sent from the headquarters office to the branch office can only be opened with a predetermined code. This code is changed every day. Which two algorithms can be used to achieve this task? (Choose two.)
HMAC
MD5
3DES
SHA-1
AES
3DES
AES
58. A network technician has been asked to design a virtual private network between two branch routers. Which type of cryptographic key should be used in this scenario?
hash key
symmetric key
asymmetric key
digital signature
symmetric key
59. Which two options can limit the information discovered from port scanning? (Choose two.)
intrusion prevention system
firewall
authentication
passwords
encryption
intrusion prevention system
firewall
60. An administrator discovers that a user is accessing a newly established website that may be detrimental to company security. What action should the administrator take first in terms of the security policy?
Ask the user to stop immediately and inform the user that this constitutes grounds for dismissal.
Create a firewall rule blocking the respective website.
Revise the AUP immediately and get all users to sign the updated AUP.
Immediately suspend the network privileges of the user.
Revise the AUP immediately and get all users to sign the updated AUP.
61. If AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.)
Create a superview using the parser view view-name command.
Associate the view with the root view.
Assign users who can use the view.
Create a view using the parser viewcommand.
Assign a secret password to the view.
Assign commands to the view.
Create a view using the parser viewcommand.
Assign a secret password to the view.
Assign commands to the view.
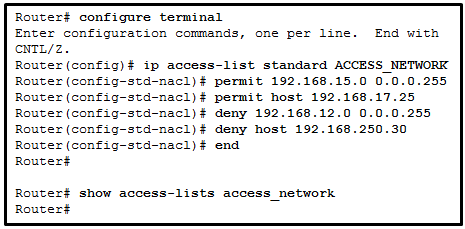
62. Refer to the exhibit. A network administrator configures a named ACL on the router. Why is there no output displayed when the show command is issued?
The ACL is not activated.
The ACL name is case sensitive.
The ACL has not been applied to an interface.
No packets have matched the ACL statements yet.
The ACL name is case sensitive.
63. ACLs are used primarily to filter traffic. What are two additional uses of ACLs? (Choose two.):
specifying internal hosts for NAT
identifying traffic for QoS
specifying source addresses for authentication
reorganizing traffic into VLANs
filtering VTP packets
specifying internal hosts for NAT
identifying traffic for QoS
64. What two features are added in SNMPv3 to address the weaknesses of previous versions of SNMP? (Choose two.)
authentication
authorization with community string priority
bulk MIB objects retrieval
ACL management filtering
encryption
authentication
encryption
65. What network testing tool is used for password auditing and recovery?
Nessus
Metasploit
L0phtcrack
SuperScan
L0phtcrack
66. Which type of firewall makes use of a server to connect to destination devices on behalf of clients?
packet filtering firewall
proxy firewall
stateless firewall
stateful firewall
proxy firewall
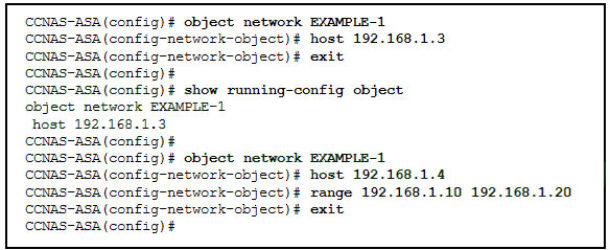
67. Refer to the exhibit. What will be displayed in the output of the show running-config object command after the exhibited configuration commands are entered on an ASA 5506-X?
host 192.168.1.4
range 192.168.1.10 192.168.1.20
host 192.168.1.3, host 192.168.1.4, and range 192.168.1.10 192.168.1.20
host 192.168.1.3
host 192.168.1.3 and host 192.168.1.4
host 192.168.1.4 and range 192.168.1.10 192.168.1.20
range 192.168.1.10 192.168.1.20
![<p>68. Refer to the exhibit. According to the command output, which three statements are true about the DHCP options entered on the ASA? (Choose three.)</p><p>The dhcpd address [ start-of-pool ]-[ end-of-pool ] inside command was issued to enable the DHCP server.</p><p>The dhcpd address [ start-of-pool ]-[ end-of-pool ] inside command was issued to enable the DHCP client.</p><p>The dhcpd enable inside command was issued to enable the DHCP server.</p><p>The dhcpd auto-config outside command was issued to enable the DHCP client.</p><p>The dhcpd auto-config outside command was issued to enable the DHCP server.</p><p>The dhcpd enable inside command was issued to enable the DHCP client.</p>](https://knowt-user-attachments.s3.amazonaws.com/41cfba6b-159b-42fb-acf6-1af52c39263b.png)
68. Refer to the exhibit. According to the command output, which three statements are true about the DHCP options entered on the ASA? (Choose three.)
The dhcpd address [ start-of-pool ]-[ end-of-pool ] inside command was issued to enable the DHCP server.
The dhcpd address [ start-of-pool ]-[ end-of-pool ] inside command was issued to enable the DHCP client.
The dhcpd enable inside command was issued to enable the DHCP server.
The dhcpd auto-config outside command was issued to enable the DHCP client.
The dhcpd auto-config outside command was issued to enable the DHCP server.
The dhcpd enable inside command was issued to enable the DHCP client.
The dhcpd address [ start-of-pool ]-[ end-of-pool ] inside command was issued to enable the DHCP server.
The dhcpd enable inside command was issued to enable the DHCP server.
The dhcpd auto-config outside command was issued to enable the DHCP client.
69. Which two statements describe the characteristics of symmetric algorithms? (Choose two.)
They are commonly used with VPN traffic.
They use a pair of a public key and a private key.
They are commonly implemented in the SSL and SSH protocols.
They provide confidentiality, integrity, and availability.
They are referred to as a pre-shared key or secret key.
They are commonly used with VPN traffic.
They are referred to as a pre-shared key or secret key.
70. A web server administrator is configuring access settings to require users to authenticate first before accessing certain web pages. Which requirement of information security is addressed through the configuration?
availability
integrity
scalability
confidentiality
confidentiality
71. The use of 3DES within the IPsec framework is an example of which of the five IPsec building blocks?
authentication
nonrepudiation
integrity
Diffie-Hellman
confidentiality
confidentiality
72. What function is provided by Snort as part of the Security Onion?
to generate network intrusion alerts by the use of rules and signatures
to normalize logs from various NSM data logs so they can be represented, stored, and accessed through a common schema
to display full-packet captures for analysis
to view pcap transcripts generated by intrusion detection tools
to generate network intrusion alerts by the use of rules and signatures
73. What are two drawbacks to using HIPS? (Choose two.)
With HIPS, the success or failure of an attack cannot be readily determined.
With HIPS, the network administrator must verify support for all the different operating systems used in the network.
HIPS has difficulty constructing an accurate network picture or coordinating events that occur across the entire network.
If the network traffic stream is encrypted, HIPS is unable to access unencrypted forms of the traffic.
HIPS installations are vulnerable to fragmentation attacks or variable TTL attacks.
With HIPS, the network administrator must verify support for all the different operating systems used in the network.
HIPS has difficulty constructing an accurate network picture or coordinating events that occur across the entire network.
74. In an AAA-enabled network, a user issues the configure terminal command from the privileged executive mode of operation. What AAA function is at work if this command is rejected?
authorization
authentication
auditing
accounting
authorization
75. A company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?
automation
accounting
authentication
authorization
authorization
76. What is a characteristic of a DMZ zone?
Traffic originating from the inside network going to the DMZ network is not permitted.
Traffic originating from the outside network going to the DMZ network is selectively permitted.
Traffic originating from the DMZ network going to the inside network is permitted.
Traffic originating from the inside network going to the DMZ network is selectively permitted.
Traffic originating from the outside network going to the DMZ network is selectively permitted.
77. Which measure can a security analyst take to perform effective security monitoring against network traffic encrypted by SSL technology?
Use a Syslog server to capture network traffic.
Deploy a Cisco SSL Appliance.
Require remote access connections through IPsec VPN.
Deploy a Cisco ASA.
Deploy a Cisco SSL Appliance.
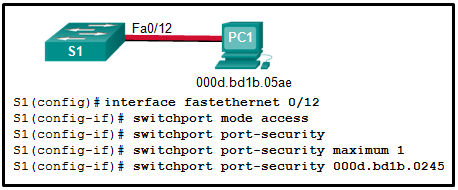
78. Refer to the exhibit. Port security has been configured on the Fa 0/12 interface of switch S1. What action will occur when PC1 is attached to switch S1 with the applied configuration?
Frames from PC1 will be forwarded since the switchport port-security violation command is missing.
Frames from PC1 will be forwarded to its destination, and a log entry will be created.
Frames from PC1 will be forwarded to its destination, but a log entry will not be created.
Frames from PC1 will cause the interface to shut down immediately, and a log entry will be made.
Frames from PC1 will be dropped, and there will be no log of the violation.
Frames from PC1 will be dropped, and a log message will be created.
Frames from PC1 will cause the interface to shut down immediately, and a log entry will be made.
79. What security countermeasure is effective for preventing CAM table overflow attacks?
DHCP snooping
Dynamic ARP Inspection
IP source guard
port security
port security
80. What are two examples of DoS attacks? (Choose two.)
port scanning
SQL injection
ping of death
phishing
buffer overflow
ping of death
buffer overflow
81. Which method is used to identify interesting traffic needed to create an IKE phase 1 tunnel?
transform sets
a permit access list entry
hashing algorithms
a security association
a permit access list entry
82. When the CLI is used to configure an ISR for a site-to-site VPN connection, which two items must be specified to enable a crypto map policy? (Choose two.)
the hash
the peer
encryption
the ISAKMP policy
a valid access list
IP addresses on all active interfaces
the IKE Phase 1 policy
a valid access list
the peer
83. How does a firewall handle traffic when it is originating from the public network and traveling to the DMZ network?
Traffic that is originating from the public network is inspected and selectively permitted when traveling to the DMZ network.
Traffic that is originating from the public network is usually permitted with little or no restriction when traveling to the DMZ network.
Traffic that is originating from the public network is usually forwarded without inspection when traveling to the DMZ network.
Traffic that is originating from the public network is usually blocked when traveling to the DMZ network.
Traffic that is originating from the public network is inspected and selectively permitted when traveling to the DMZ network.
84. A client connects to a Web server. Which component of this HTTP connection is not examined by a stateful firewall?
the source IP address of the client traffic
the destination port number of the client traffic
the actual contents of the HTTP connection
the source port number of the client traffic
the actual contents of the HTTP connection
85. Which network monitoring technology uses VLANs to monitor traffic on remote switches?
IPS
IDS
TAP
RSPAN
RSPAN
86. Which rule action will cause Snort IPS to block and log a packet?
log
drop
alert
Sdrop
drop
87. What is typically used to create a security trap in the data center facility?
IDs, biometrics, and two access doors
high resolution monitors
redundant authentication servers
a server without all security patches applied
IDs, biometrics, and two access doors
88. A company is concerned with leaked and stolen corporate data on hard copies. Which data loss mitigation technique could help with this situation?
strong PC security settings
strong passwords
shredding
encryption
shredding
89. Upon completion of a network security course, a student decides to pursue a career in cryptanalysis. What job would the student be doing as a cryptanalyst?
cracking code without access to the shared secret key
creating hashing codes to authenticate data
making and breaking secret codes
creating transposition and substitution ciphers
cracking code without access to the shared secret key
90. What command is used on a switch to set the port access entity type so the interface acts only as an authenticator and will not respond to any messages meant for a supplicant?
dot1x pae authenticator
authentication port-control auto
aaa authentication dot1x default group radius
dot1x system-auth-control
dot1x pae authenticator
91. What are two disadvantages of using an IDS? (Choose two.)
The IDS does not stop malicious traffic.
The IDS works offline using copies of network traffic.
The IDS has no impact on traffic.
The IDS analyzes actual forwarded packets.
The IDS requires other devices to respond to attacks.
The IDS does not stop malicious traffic.
The IDS requires other devices to respond to attacks.
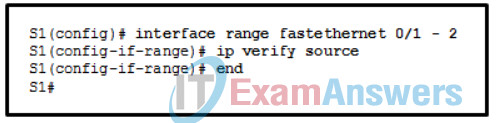
92. Refer to the exhibit. The ip verify source command is applied on untrusted interfaces. Which type of attack is mitigated by using this configuration?
DHCP spoofing
DHCP starvation
STP manipulation
MAC and IP address spoofing
MAC and IP address spoofing
93. What ports can receive forwarded traffic from an isolated port that is part of a PVLAN?
other isolated ports and community ports
only promiscuous ports
all other ports within the same community
only isolated ports
only promiscuous ports
94. A user complains about being locked out of a device after too many unsuccessful AAA login attempts. What could be used by the network administrator to provide a secure authentication access method without locking a user out of a device?
Use the login delay command for authentication attempts.
Use the login local command for authenticating user access.
Use the aaa local authentication attempts max-fail global configuration mode command with a higher number of acceptable failures.
Use the none keyword when configuring the authentication method list.
Use the login delay command for authentication attempts.
95. What are two drawbacks in assigning user privilege levels on a Cisco router? (Choose two.)
Only a root user can add or remove commands.
Privilege levels must be set to permit access control to specific device interfaces, ports, or slots.
Assigning a command with multiple keywords allows access to all commands using those keywords.
Commands from a lower level are always executable at a higher level.
AAA must be enabled.
Assigning a command with multiple keywords allows access to all commands using those keywords.
Commands from a lower level are always executable at a higher level.
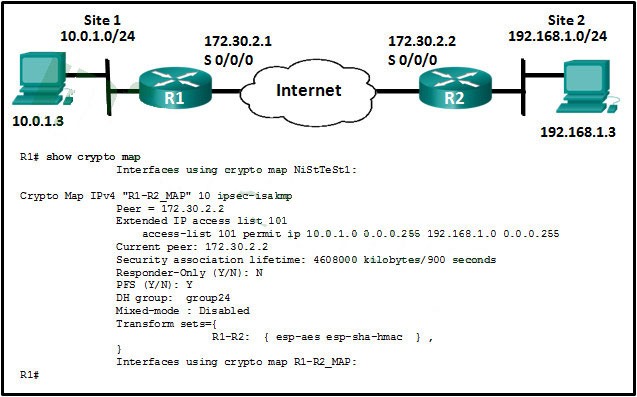
96. Refer to the exhibit. Which conclusion can be made from the show crypto map command output that is shown on R1?
Which conclusion can be made from the show crypto map command output that is shown on R1
The crypto map has not yet been applied to an interface.
The current peer IP address should be 172.30.2.1.
There is a mismatch between the transform sets.
The tunnel configuration was established and can be tested with extended pings.
The crypto map has not yet been applied to an interface.
97. What are two reasons to enable OSPF routing protocol authentication on a network? (Choose two.)
to prevent data traffic from being redirected and then discarded
to ensure faster network convergence
to provide data security through encryption
to prevent redirection of data traffic to an insecure link
to ensure more efficient routing
to prevent data traffic from being redirected and then discarded
to prevent redirection of data traffic to an insecure link
98. Which three functions are provided by the syslog logging service? (Choose three.)
gathering logging information
authenticating and encrypting data sent over the network
retaining captured messages on the router when a router is rebooted
specifying where captured information is stored
distinguishing between information to be captured and information to be ignored
setting the size of the logging buffer
gathering logging information
specifying where captured information is stored
distinguishing between information to be captured and information to be ignored
99. What two ICMPv6 message types must be permitted through IPv6 access control lists to allow resolution of Layer 3 addresses to Layer 2 MAC addresses? (Choose two.)
neighbor solicitations
echo requests
neighbor advertisements
echo replies
router solicitations
router advertisements
neighbor solicitations
neighbor advertisements
100. Which three services are provided through digital signatures? (Choose three.)
accounting
authenticity
compression
nonrepudiation
integrity
encryption
nonrepudiation
integrity
authenticity