Denial of Service - CompTIA Network+ N10-009 - 4.2
1/4
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
5 Terms
Denial of Service
* Force a service to fail - Overload the service
* Take advantage of a design failure or vulnerability
- Keep your systems patched!
* Cause a system to be unavailable
- Competitive advantage
* Create a smokescreen for some other exploit
- Precursor to a DNS spoofing attack
* Doesn't have to be complicated - Turn off the power
A "friendly" DoS
• Unintentional DoSing - It's not always a ne'er-do-well
• Network DoS - Layer 2 loop without STP
• Bandwidth DoS
• Downloading multi-gigabyte Linux distributions
over a DSL line
• The water line breaks - Get a good shop vacuum
Distributed Denial of Service (DDpS)
Launch an army of computers to bring down a service
- Use all the bandwidth or resources - traffic spike
This is why the attackers have botnets
- Thousands or millions of computers at your command
- At its peak, Zeus botnet infected over 3.6 million PC's
- Coordinated attack
Asymmetric threat
- The attackers may have fewer resources than the victim
DDoS reflection and amplification
Turn your small attack into a big attack
- Often reflected off another device or service
An increasingly common network DDoS technique
- Turn Internet services against the victim
Uses protocols with little (if any) authentication or checks
- NTP, DNS, ICMP A common example of protocol abuse
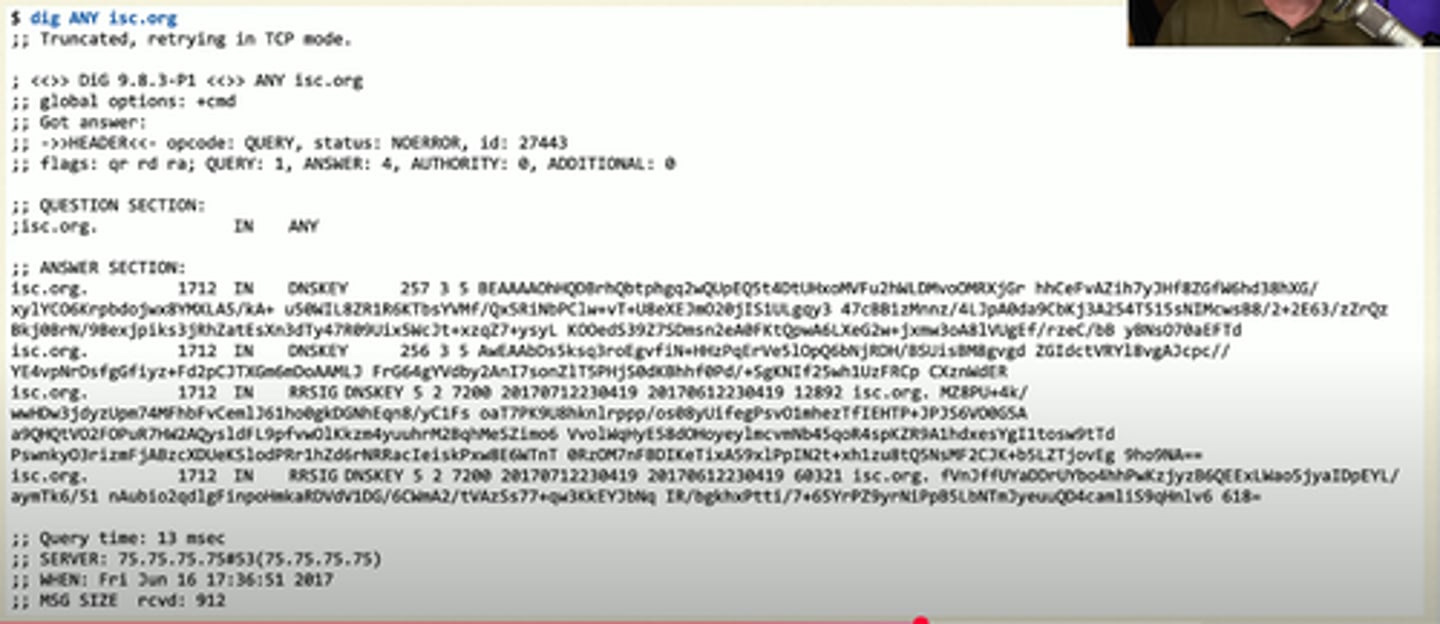
DNS Amplification DDoS
botnets receive commands to send requests to open DNS resolvers for large DNS keys or other large info.
they spoof the sender of the request as their target instead of themselves.
