SLR09 - Compression encryption & hashing
1/15
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
16 Terms
Purpose of compression
↓ size file
↓ download time
↓ storage requirements
make best use of bandwidth
Lossy compression
Some data lost
Slightly ↓ quality
Significantly ↓ file size
Suitable for: image, audio, video
Lossless compression
None orig data lost
Orig file can be recreated when it is uncompressed
Suitable for: executable files & documents
Methods of lossless compression
Dictionary coding: text based documents
Run-length coding: images
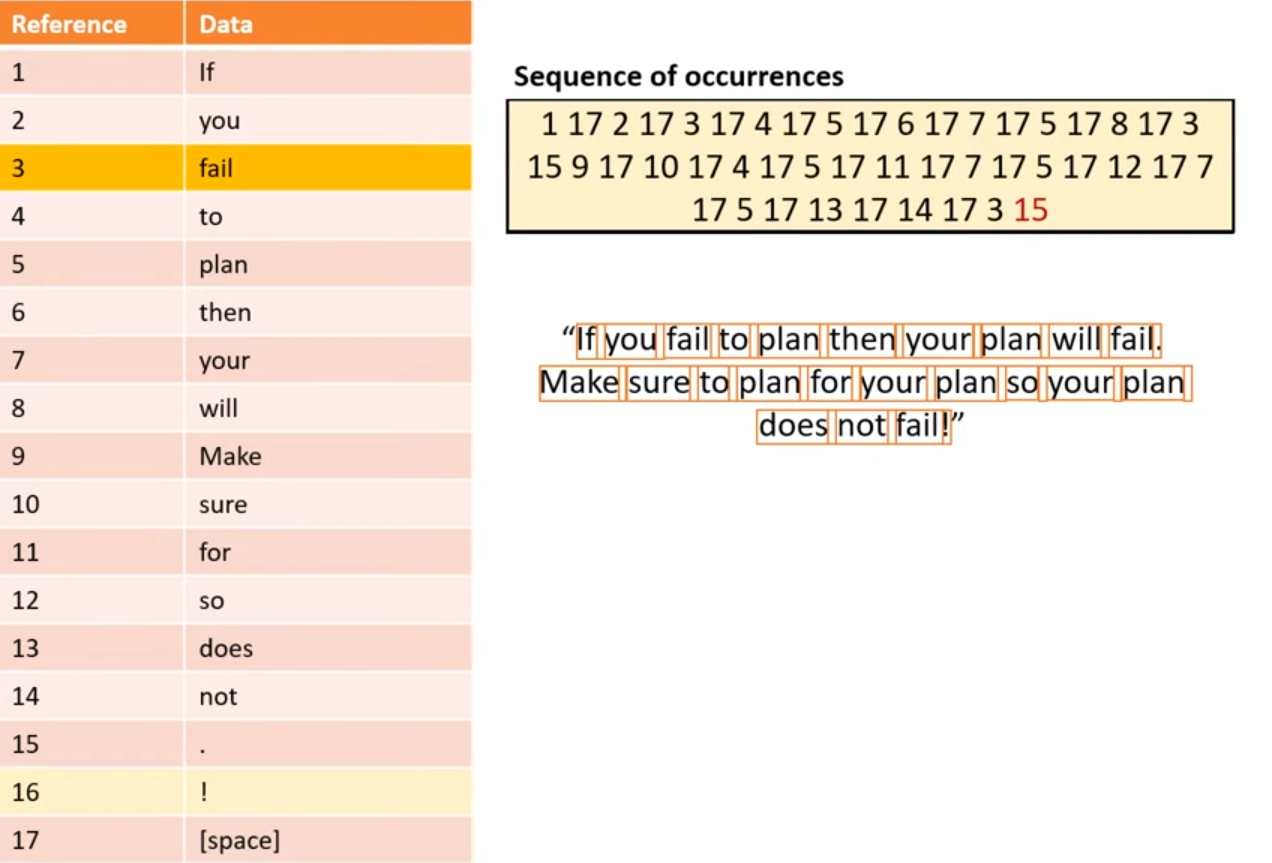
Dictionary coding
Builds index using every data item/entry in file
File is now made up of:
Dictionary index
Sequence of occurrences needed to recreate orig file
Run length coding
ideal for bitmap images
There may be continuous pixels of the same colour
So instead of storing each one individually, information stored in frequency/data pairs:
22 0: 22 continuous white pixels
6 1: 6 continuous black pixels
Explain why compression is important for the streaming of high resolution films
Symmetric encryption
Uses a single key during encryption & decryption
Both parties know the key
How can a symmetrically encrypted message be cracked?
Interception of key
Duplication of key production process to acquire a copy of the key
Asymmetric encryption
Each party has a pair of keys
Message encrypted by one key, decrypted by the other
One key is public - anyone can access, the other is private
How sending a file using asymmetric encryption works
Sender & recipient exchange public keys
Sender uses recipients public key to encrypt message
Recipient uses private key to decrypt
How to confirm that a message is authentic
Encrypt message with private key
Anyone can access public key & decrypt - confirmed authentic
Sending direct message
Send using:
Own private key
Recipients public key
Decrypted using:
Their private key
Own public key
Hashing function
Transforms string of characters into fixed length value or key
One way
How hashing function used to check password
Apply function on inputted password
Compare hashed vale to stored value
How can hashing be used for quick data storage & retrival
When storing, apply, function on string being stored
Store the string in the address corresponding to the value generated
When retrieving, run function again and retrieve value held in the given value - remove need to search