220-1102 CompTIA Exam
1/29
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced |
|---|
No study sessions yet.
30 Terms
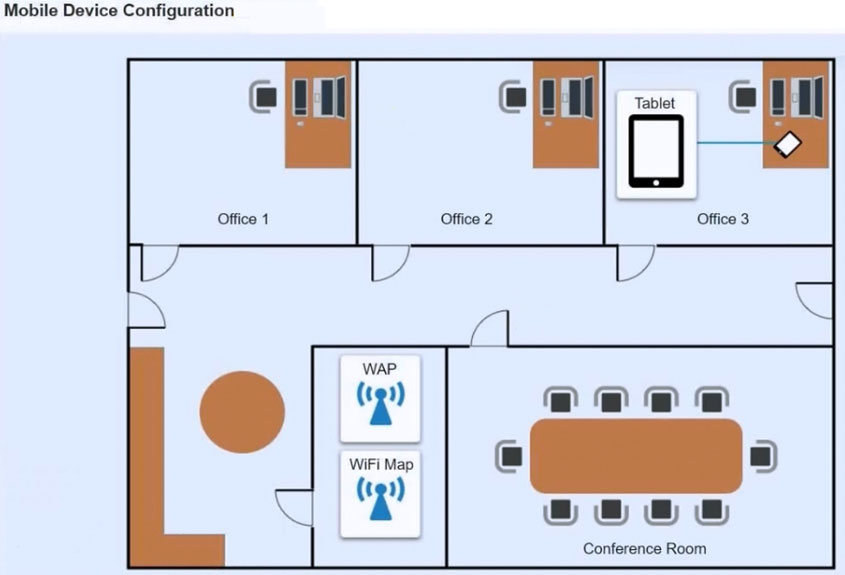
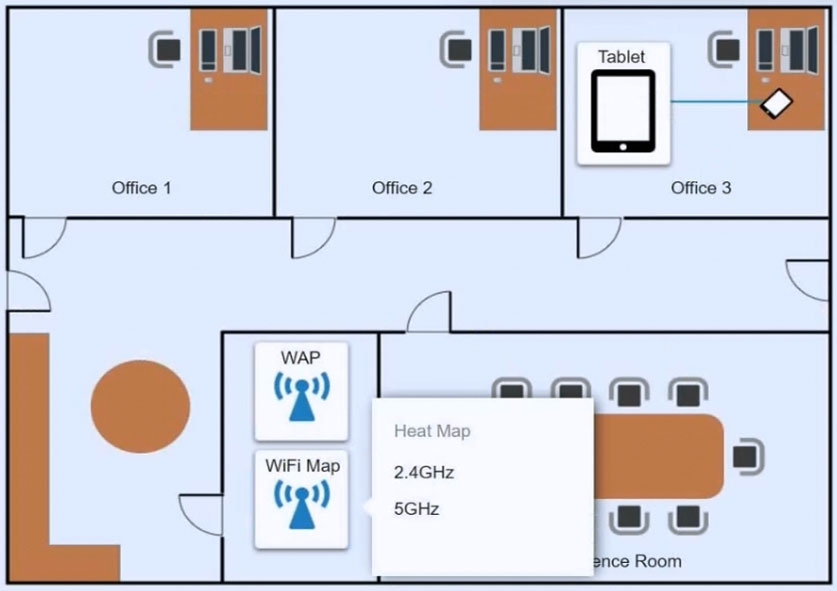
SIMULATION -
Ann, a CEO, has purchased a new consumer-class tablet for personal use, but she is unable to connect to the wireless network. Other users have reported that their personal devices are connecting without issues. She has asked you to assist with getting the device online without adjusting her home WiFi configuration.
INSTRUCTIONS -
Review the network diagrams and device configurations to determine the cause of the problem and resolve any discovered issues.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
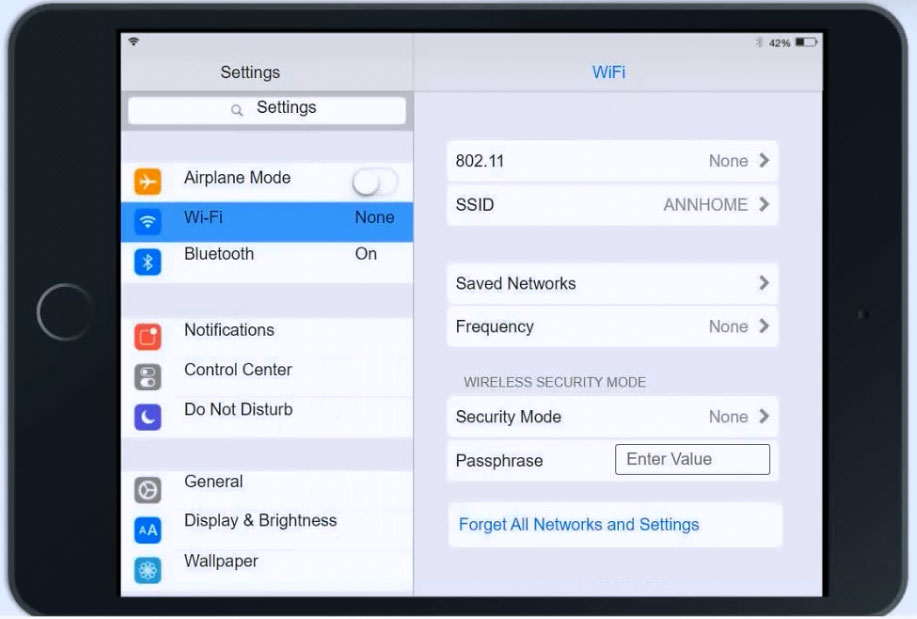
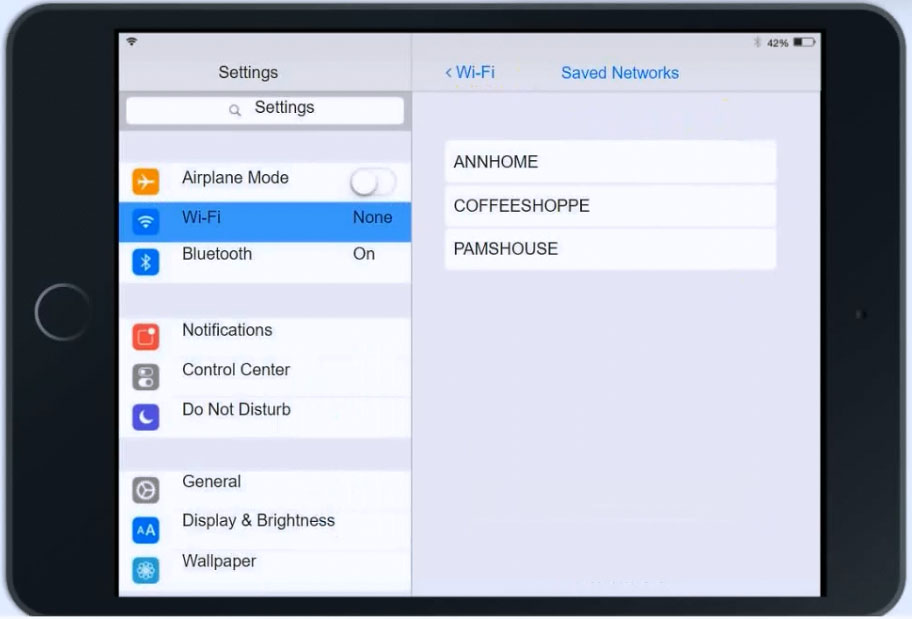
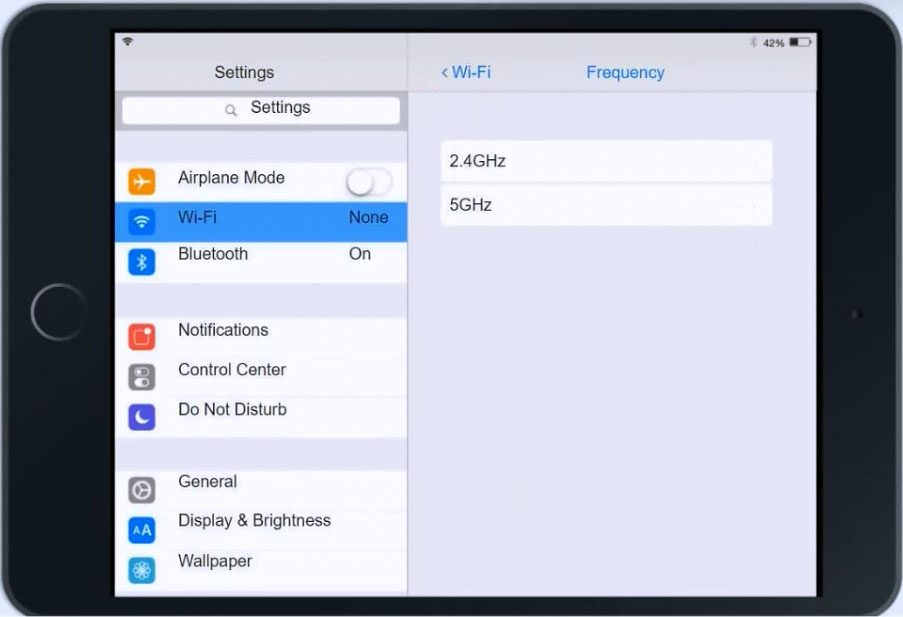
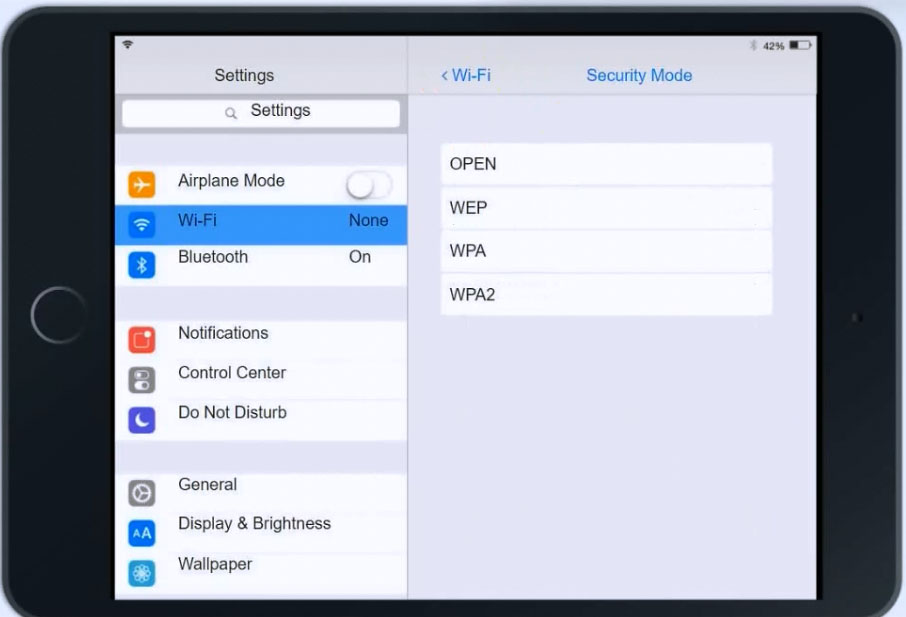
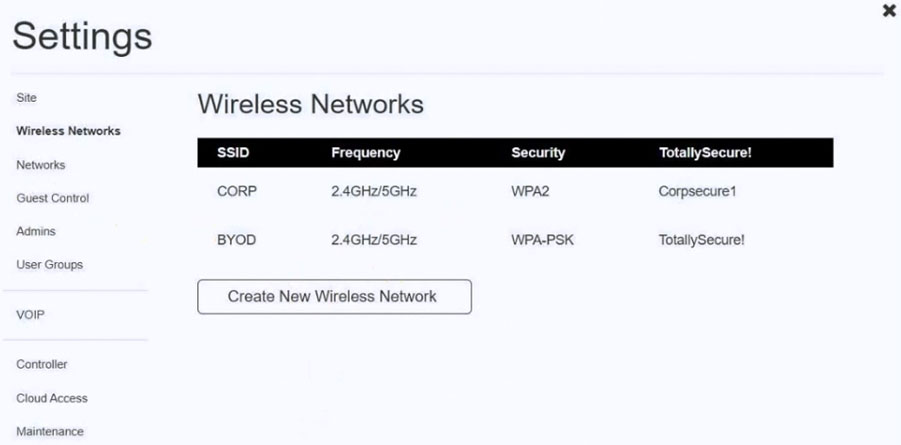
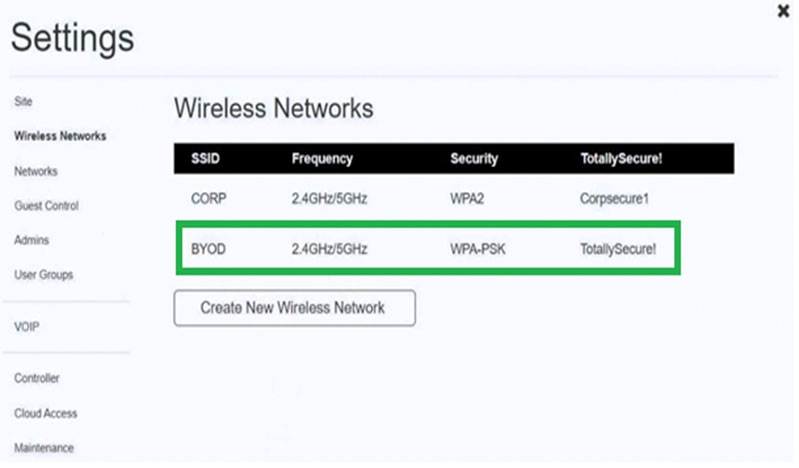
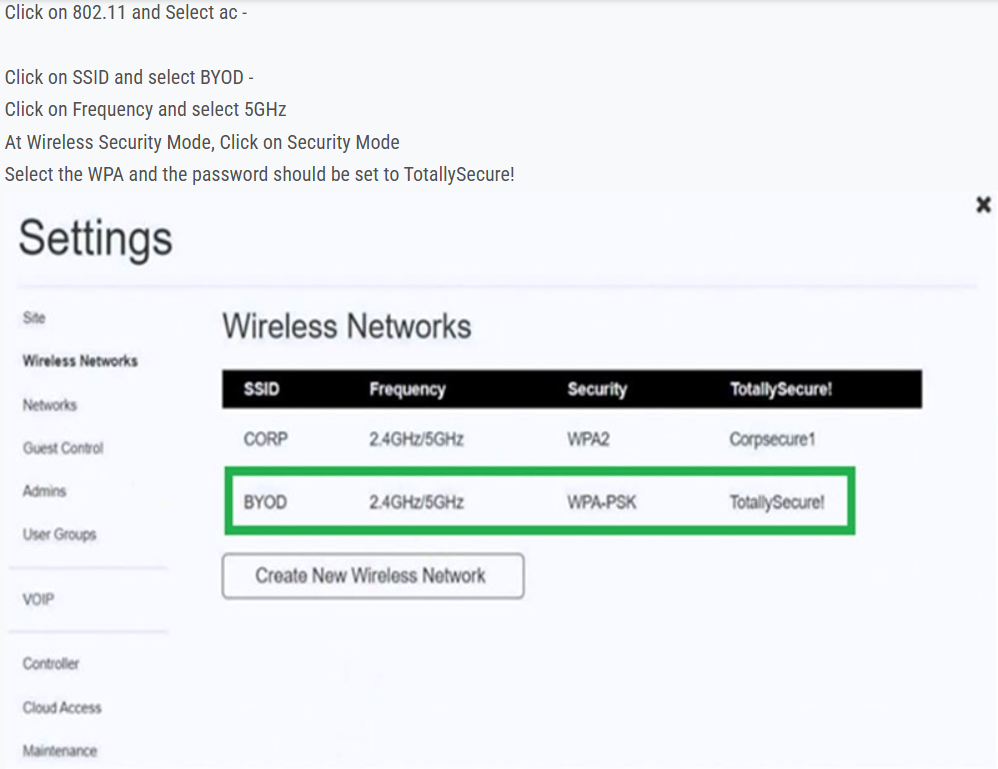
Correct Answer:

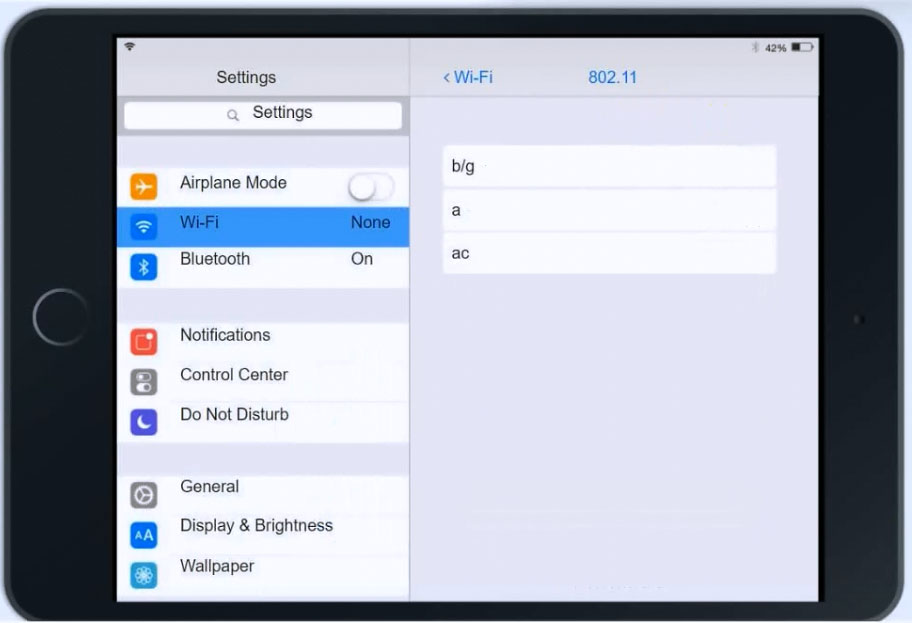
Click on 802.11 and Select ac -
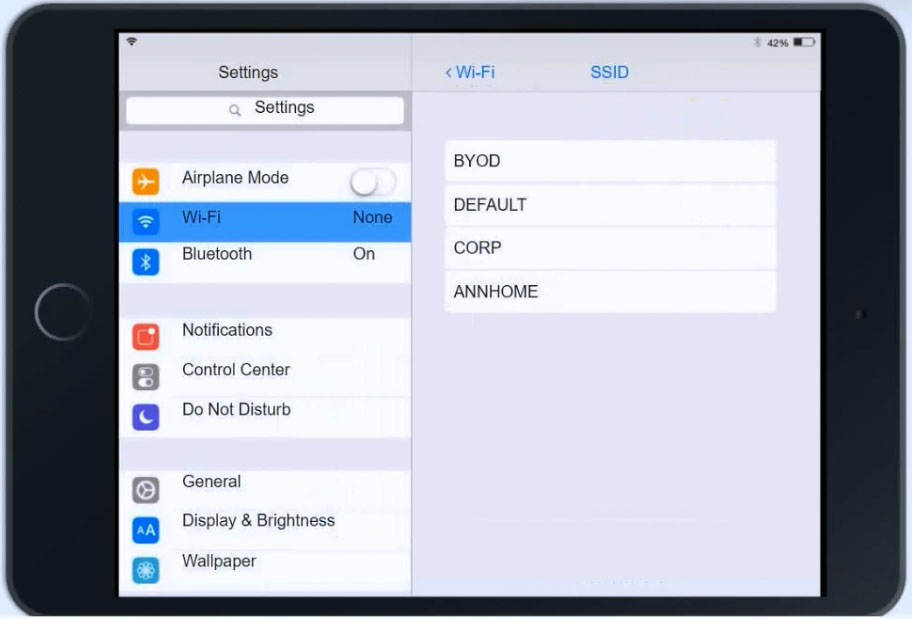
Click on SSID and select BYOD -
Click on Frequency and select 5GHz
At Wireless Security Mode, Click on Security Mode
Select the WPA and the password should be set to TotallySecure!
A help desk team lead contacts a systems administrator because the technicians are unable to log in to a Linux server that is used to access tools. When the administrator tries to use remote desktop to log in to the server, the administrator sees the GUI is crashing. Which of the following methods can the administrator use to troubleshoot the server effectively?
A. SFTP
B. SSH
C. VNC
D. MSRA
B. SSH
A company wants to remove information from past users' hard drives in order to reuse the hard drives. Which of the following is the MOST secure method?
A. Reinstalling Windows
B. Performing a quick format
C. Using disk-wiping software
D. Deleting all files from command-line interface
C. Using disk-wiping software
A user is having phone issues after installing a new application that claims to optimize performance. The user downloaded the application directly from the vendor's website and is now experiencing high network utilization and is receiving repeated security warnings. Which of the following should the technician perform FIRST to mitigate the issue?
A. Reset the phone to factory settings.
B. Uninstall the fraudulent application.
C. Increase the data plan limits.
D. Disable the mobile hotspot.
B. Uninstall the fraudulent application.
A change advisory board just approved a change request. Which of the following is the MOST likely next step in the change process?
A. End user acceptance
B. Perform risk analysis
C. Communicate to stakeholders
D. Sandbox testing
A. End user acceptance
A user calls the help desk to report that none of the files on a PC will open. The user also indicates a program on the desktop is requesting payment in exchange for file access. A technician verifies the user's PC is infected with ransomware. Which of the following should the technician do FIRST?
A. Scan and remove the malware.
B. Schedule automated malware scans.
C. Quarantine the system.
D. Disable System Restore.
C. Quarantine the system.
A company is issuing smartphone to employees and needs to ensure data is secure if the devices are lost or stolen. Which of the following provides the BEST solution?
A. Anti-malware
B. Remote wipe
C. Locator applications
D. Screen lock
B. Remote wipe
A user reports seeing random, seemingly non-malicious advertisement notifications in the Windows 10 Action Center. The notifications indicate the advertisements are coming from a web browser. Which of the following is the BEST solution for a technician to implement?
A. Disable the browser from sending notifications to the Action Center.
B. Run a full antivirus scan on the computer.
C. Disable all Action Center notifications.
D. Move specific site notifications from Allowed to Block.
D. Move specific site notifications from Allowed to Block.
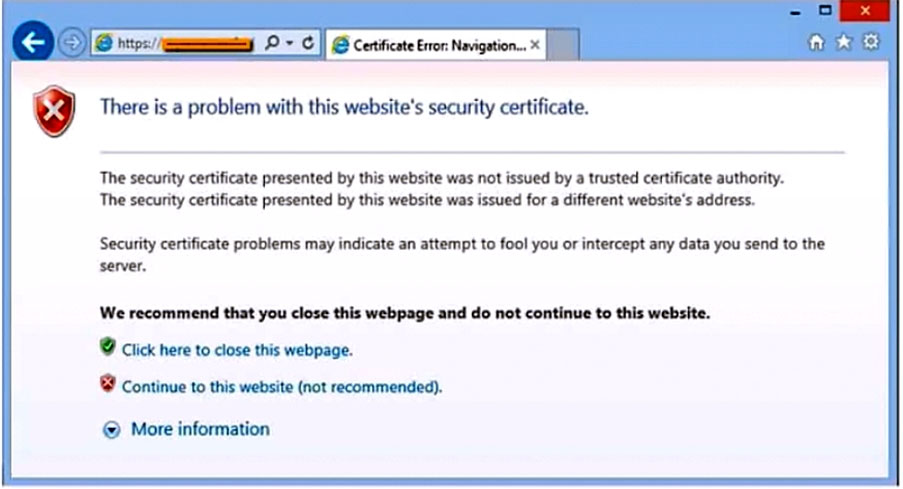
After clicking on a link in an email, a Chief Financial Officer (CFO) received the following error:
The CFO then reported the incident to a technician. The link is purportedly to the organization's bank. Which of the following should the technician perform FIRST?
A. Update the browser's CRLs.
B. File a trouble ticket with the bank.
C. Contact the ISP to report the CFO's concern.
D. Instruct the CFO to exit the browser.
D. Instruct the CFO to exit the browser.
A help desk technician is troubleshooting a workstation in a SOHO environment that is running above normal system baselines. The technician discovers an unknown executable with a random string name running on the system. The technician terminates the process, and the system returns to normal operation. The technician thinks the issue was an infected file, but the antivirus is not detecting a threat. The technician is concerned other machines may be infected with this unknown virus. Which of the following is the MOST effective way to check other machines on the network for this unknown threat?
A. Run a startup script that removes files by name.
B. Provide a sample to the antivirus vendor.
C. Manually check each machine.
D. Monitor outbound network traffic.
C. Manually check each machine.
A laptop user is visually impaired and requires a different cursor color. Which of the following OS utilities is used to change the color of the cursor?
A. Keyboard
B. Touch pad
C. Ease of Access Center
D. Display settings
C. Ease of Access Center
A manager reports that staff members often forget the passwords to their mobile devices and applications. Which of the following should the systems administrator do to reduce the number of help desk tickets submitted?
A. Enable multifactor authentication.
B. Increase the failed log-in threshold.
C. Remove complex password requirements.
D. Implement a single sign-on with biometrics.
D. Implement a single sign-on with biometrics.
A technician suspects a rootkit has been installed and needs to be removed. Which of the following would BEST resolve the issue?
A. Application updates
B. Anti-malware software
C. OS reinstallation
D. File restore
C. OS reinstallation
A technician is setting up a SOHO wireless router. The router is about ten years old. The customer would like the most secure wireless network possible. Which of the following should the technician configure?
A. WPA2 with TKIP
B. WPA2 with AES
C. WPA3 with AES-256
D. WPA3 with AES-128
B. WPA2 with AES
A technician is troubleshooting an issue involving programs on a Windows 10 machine that are loading on startup but causing excessive boot times. Which of the following should the technician do to selectively prevent programs from loading?
A. Right-click the Windows button, then select Run... entering shell:startup and clicking OK, and then move items one by one to the Recycle Bin.
B. Remark out entries listed HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows>CurrentVersion>Run.
C. Manually disable all startup tasks currently listed as enabled and reboot, checking for issue resolution at startup.
D. Open the Startup tab and methodically disable items currently listed as enabled and reboot, checking for issue resolution at each startup.
D. Open the Startup tab and methodically disable items currently listed as enabled and reboot, checking for issue resolution at each startup.
A call center technician receives a call from a user asking how to update Windows. Which of the following describes what the technician should do?
A. Have the user consider using an iPad if the user is unable to complete updates.
B. Have the user text the user's password to the technician.
C. Ask the user to click in the Search field, type Check for Updates, and then press the Enter key.
D. Advise the user to wait for an upcoming, automatic patch.
C. Ask the user to click in the Search field, type Check for Updates, and then press the Enter key.
When a user calls in to report an issue, a technician submits a ticket on the user's behalf. Which of the following practices should the technician use to make sure the ticket is associated with the correct user?
A. Have the user provide a callback phone number to be added to the ticket.
B. Assign the ticket to the department's power user.
C. Register the ticket with a unique user identifier.
D. Provide the user with a unique ticket number that can be referenced on subsequent calls.
C. Register the ticket with a unique user identifier.
Which of the following is the MOST important environmental concern inside a data center?
A. Battery disposal
B. Electrostatic discharge mats
C. Toner disposal
D. Humidity levels
D. Humidity levels
A user is unable to log in to the network. The network uses 802.1X with EAP-TLS to authenticate on the wired network. The user has been on an extended leave and has not logged in to the computer in several months. Which of the following is causing the log-in issue?
A. Expired certificate
B. OS update failure
C. Service not started
D. Application crash
E. Profile rebuild needed
A. Expired certificate
A technician needs to format a USB drive to transfer 20GB of data from a Linux computer to a Windows computer. Which of the following filesystems will the technician MOST likely use?
A. FAT32
B. ext4
C. NTFS
D. exFAT
D. exFAT
Following the latest Windows update, PDF files are opening in Microsoft Edge instead of Adobe Reader. Which of the following utilities should be used to ensure all PDF files open in Adobe Reader?
A. Network and Sharing Center
B. Programs and Features
C. Default Apps
D. Add or Remove Programs
C. Default Apps
A technician needs to exclude an application folder from being cataloged by a Windows 10 search. Which of the following utilities should be used?
A. Privacy
B. Indexing Options
C. System
D. Device Manager
B. Indexing Options
As part of a CYOD policy, a systems administrator needs to configure each user's Windows device to require a password when resuming from a period of sleep or inactivity. Which of the following paths will lead the administrator to the correct settings?
A. Use Settings to access Screensaver settings.
B. Use Settings to access Screen Timeout settings.
C. Use Settings to access General.
D. Use Settings to access Display.
A. Use Settings to access Screensaver settings
A technician is working with a company to determine the best way to transfer sensitive personal information between offices when conducting business. The company currently uses USB drives and is resistant to change. The company's compliance officer states that all media at rest must be encrypted. Which of the following would be the BEST way to secure the current workflow?
A. Deploy a secondary hard drive with encryption on the appropriate workstation.
B. Configure a hardened SFTP portal for file transfers between file servers.
C. Require files to be individually password protected with unique passwords.
D. Enable BitLocker To Go with a password that meets corporate requirements.
D. Enable BitLocker To Go with a password that meets corporate requirements
The command cat comptia.txt was issued on a Linux terminal. Which of the following results should be expected?
A. The contents of the text comptia.txt will be replaced with a new blank document.
B. The contents of the text comptia.txt would be displayed.
C. The contents of the text comptia.txt would be categorized in alphabetical order.
D. The contents of the text comptia.txt would be copied to another comptia.txt file.
B. The contents of the text comptia.txt would be displayed
An incident handler needs to preserve evidence for possible litigation. Which of the following will the incident handler MOST likely do to preserve the evidence?
A. Encrypt the files.
B. Clone any impacted hard drives.
C. Contact the cyber insurance company.
D. Inform law enforcement.
B. Clone any impacted hard drives
A technician needs to recommend the best backup method that will mitigate ransomware attacks. Only a few files are regularly modified; however, storage space is a concern. Which of the following backup methods would BEST address these concerns?
A. Full
B. Differential
C. Off-site
D. Grandfather-father-son
B. Differential
A technician is troubleshooting a customer's PC and receives a phone call. The technician does not take the call and sets the phone to silent. Which of the following BEST describes the technician's actions?
A. Avoid distractions
B. Deal appropriately with customer's confidential material
C. Adhere to user privacy policy
D. Set and meet timelines
A. Avoid distractions
A technician needs to transfer a large number of files over an unreliable connection. The technician should be able to resume the process if the connection is interrupted. Which of the following tools can be used?
A. sfc
B. chkdsk
C. git clone
D. robocopy
D. robocopy
A company installed a new backup and recovery system. Which of the following types of backups should be completed FIRST?
A. Full
B. Non-parity
C. Differential
D. Incremental
A. Full