Systems Final Exam Review
1/97
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
98 Terms
read() syscall
Calling convention: sizze_t __(sizet count; int fd, void buf[count], size_t count)
Description: attempts to read up to count bytes from file descriptor fd into the buffer starting at buf
returns: on success: number of bytes read, 0 if EOF, on error: -1 and errno is set for the error
write() syscall
calling convention: ssize_t ___(sizet count; int fd, const void buf[count], size_t count);
Description: writes up to count bytes from the buffer starting at buf to the file refereed to by the file descriptor fd
returns: on success: the number of bytes written; on error, -1 and errno is set for the error
open() syscall
return: on success, the lowest numbered file descriptor not currently open for the process, on error -1
calling convention: int ___(const char *path, int flags, modet mode)
opens a file based on the specified path and may create a file based on the provided flags
close() syscall
calling convention: int _(int fd)
Description: closes a file descriptor so that it no longer refers to any file and may be reused
Returns: On success, 0, on error, -1 and errno is set to indicate the error
exit() syscall
calling convention: void ___(int status)
description: causes normal process termination and the least significant byte of status is returned to the parent
Returns: does not return
pipe() syscall
calling conventtion: int ____(int fd[2]);
description: creates a unidirectional data channel that can be used for interprocess communication
Returns: on success, 0, on error -1 and errno is set for the error and the fd is unchanged
fork() syscall
calling convention: pid_t ____(void)
Description: creates a new process by duplicating the calling process, the new process is refered to ad the child process, the calling process is referred to as the parent process
returns: on success, the PID of the child process is returned in the parent, and 0 is returned in the child. On failure, -1 in the prent, no child, and errno is set for the error
sleep() syscall
Callinf convention: unsigned int ____(unsigned int seconds)
Description: causes the calling threat to sleep either until the number od real-time seconds specified in seconds have alapsed or until a signal arrives which is not ignored
returns: on success: 0 if the time has elapsed or the number os seconds left tot sleep if the call was interrupted by a sig handler
kill() syscall
Calling convention: int ___(pid pid, int sig)
Description: can be used to send any signal to any process group or process.
If pid is positive, then sig is sent wit the ID specified by pid
if pid is 0, then sig is sent to every process in the process group of the calling process
if pid is -1 then sig is sent to every process for which the calling process has permission to send signals, except for process 1
if sig is 0, then no signal is sent
returns: on success 0, on error -1 and errno is set
signal() syscall
calling convention: sighandlert (int signum, sighandlert handler);
description: sets the disposition of the signal signum to handler, which is either SIGIGN, SIGDFL, or the addresss of a programmer defines function(sig handler)
returns: on success: the previous value of the signal handler, On fail, SIG_ERR and errno is set for the error
wait() syscall
calling convention: pid_t ___(int *Nullable wstatus);
Description: suspends execution of the calling threat until one of its children terminates, equivalent to waitpid(-1, &wstatus, 0);
Returns: on success, the process ID of the terminated child, on fail -1
getpid() syscall
calling convention: pid_t ____(void)
Description: retuurns the process ID (PID) of the calling process
does not error
getppid() syscall
Calling convention: pidt (void)
descriptions: returns the process ID of the parent of the calling process. This will be either the ID of the process that created this process using fork(), or, if that process has already terminated, the ID of the process to which this process has been reparented.
does not error
setpgid() syscall
Calling convention: int (pidt pid, pid_pgid);
Description: sets the PGID of the process specified by pid to pgid. If pid is zero, then the PGID of the process specified by pid is made the same as its process ID
returns: on success 0, on error -1 and errno is set to indicate the error
socket() syscall
Calling convention: int ___(int domain, int type, int protocol
Description: creates an endpoint for communication and returns a file descriptor that refers to that endpoint. The fd returned oby a successful call will be the lowest numbered fd not currently open for the process. Domain specifies communication domain AFUNIX, AFINET, type specified semantics: SOCKSTREAM SOCK_DGRAM
Returns: on success, a file descriptor for the new socket , on error -1 and errno is set
bind() syscall
calling convention: int ___(int sockfd, const struct sockaddr *addr, socklent addrlen);
description: when a socket is created it exists in a name space but has no assigned address, this syscall assigns the address specified by addr to the socket referred to by the file descriptor sockfd, addrlen specifies the size, in bytes of the address structure pointed to by addr, aka ”assigning a name to a socket”
returns: on success 0, on error, -1 and errno is set
listen() syscall
calling convention: int _(int sockfd, int backlog)
description: marks to socket referred to by sockfd as a passive socket, that us a socket that will be used to accept incoming connection requests using accept
returns: on success 0, on error -1 and errno is set
accept() syscall
calling convention: int (int sockfd, struct sockaddr NUllable restrict addr, socklent NULLable restrict addrlen)
description: used with connection-based socket types. it extracts the first connection request on the queue of pending connections for the listening socket, sockfd, created a new connected socket and returns a new file descriptor referring to that socket. The newly created socket is not in the lintedning state. The original socket sockfd is unaffectd by this call
returns: on success: returns a fd for the accepted socket(nonnegative). On error, -1, errno is set and addrlen is left unchanged
connect() syscall
calling convention: int (int sockfd, const struct sockaddr *addr, socklent addrLen_;
description: connects the socket referred to by the file descriptor sockfd to the address specified by addr. The addrLen argument specified the size of the addr. the format of the address in addr is determined by the address space of the socket sockfd
returns: on success 0, on error -1 and errno is set
mmap() syscall
calling convention: void *__(sizet length; void addr[length], sizet length, int port, int flags, int fd, offt offset);
Description: created a new mapping in the virtual address space of the calling process. The starting address for the new mapping is specified in addr. The length argument specififed the length of the mapping(must be > 0). The offset must be a multiple of the page size as returned by sysconf
returns: on success, returns a pointer to the mapped area. On error, the value MAP_FAILED is returned and errno is set fot the error
mprotect() syscall
Calling convention: int (sizet size; void addr[size], sizet size, int prot);
Description: changes the access protections for the calling processes memory pages containing any part of the address range in the interval , addr must be aligned to a page boundary,
returns: on success 0, on error -1 and errno is set
munmap() syscall
calling convention: int ___(sizet length; void addr[length], size_t length)
Description: call deleted the mappings for the specififed address range, and causes further refrences to addresses with the range to generate invalid memory refrences. The region is also automatically unmapped when the process is terminated. On the other hand, closing the file descriptor does not umap the region
Returns: un success, 0, on fail -1 and errno is set to indicate the error(EINVAL)
permissions for 0000
u-none
g-none
o-none
0700 permissions
u-r,w,e
g-none
o-none
0644 permissions
u-r,w
g-r
o-r
0755 permissions
u-r,w,e
g-r,e
o-r,e
what permissions do directories normally have
0755
0111 permissions
u-e
g-e
o-e
0066 permissions
u-none
g-r,w
o-r,w
SOCK_DGRAM
connectionless variant, less overhead, faster, less reliable, no guaranteed connection from server to client, m→m can have any number of servers and clients
SOCK_DGRAM
UDP, sending packets and hoping they make it to the client, information is not guaranteed to make it to the client
SOCK_STREAM
connection communication, more overhead, slower, more reliable, all information guaranteed to make it to the client, 1→1 one server, one client
SOCK_STREAM
TCP, sends in a stream, not just individual packets, information is making it to the client
AF_UNIX
communicates with its own system/ local to the machine
AF_UNIX
its address is a file descriptor, basically a socket with files
AF_INET
communicated with the internet w/ IP addresses
AF_INET
its addresses are IPs and needs a port number to see where the data is read and written to
How is the ORDER guaranteed when sending data using a SOCK_STREAM socket
its guaranteed to to be the same as it was sent, FIFO
How is the TIMING guaranteed when sending data using a SOCK_STREAM socket
it’s not, you don’t know what the network connection is like
How is the SPEED guaranteed when sending data using a SOCK_STREAM socket
it’s not, it will be faster than SOCK_DGRAM
How is the OVERHEAD guaranteed when sending data using a SOCK_STREAM socket
more than DGRAM, must be a bit to know that packets are received leading to increased setup cost
How is the UNIT of Delivery guaranteed when sending data using a SOCK_STREAM socket
byte stream
How is the DATA INTEGRITY guaranteed when sending data using a SOCK_STREAM socket
each packet is guaranteed to always eventually arrive
How is the RELIABILITY guaranteed when sending data using a SOCK_STREAM socket
good reliability, it will eventually always send all the data
What is the underlying data type of AF_INET?
unsigned integer: 32bits→4bytes→IPv4 address
How is the underlying data type of AF_INET represented?
IP address: ex 127.0.0.1→ local host, 4bytes
What would the following sequence generate?
$ echo “abcdefg” > a.file
$ ln –s a.file a.link
$ cat a.link
$ rm a.file
$ cat a.link
error: no such file or directory
Reasoning: the file that held the original soft/symbolic link was removed which means that the pointer from the link no longer points to anything, so it errors
4 properties of pipes
the writing end of the pipe blocks when the pipe is full, so that it won’t write into a full pipe
If the pipe is empty, then the read from the pipe will block; read won’t read from an empty pipe
If there’s no way for the pipe to be written, i.e. the write end is closed, read gives EOF
If there’s no way for the pipe to be read, i.e. read end is closed, write gives SIGPIPE
If a pipe is full, what does the write end do
blocks, won’t write into a full pipe
If a pipe is empty, what does the read end do
blocks, won’t read from an empty pipe
If there is no way for a pipe to be written, what does the read end give
gives EOF
If there’s no way for a pipe to be read, what does the write end do
gives SIGPIPE signal
Given the following code, what is represented by fd?
int main(){
int fd[2];
pipe(fd);
…
}
fd represents a pipe where fd[0] is read end and fd[1] is the write end
what is the read end of the pipe
0
what is the write end of a pipe
1
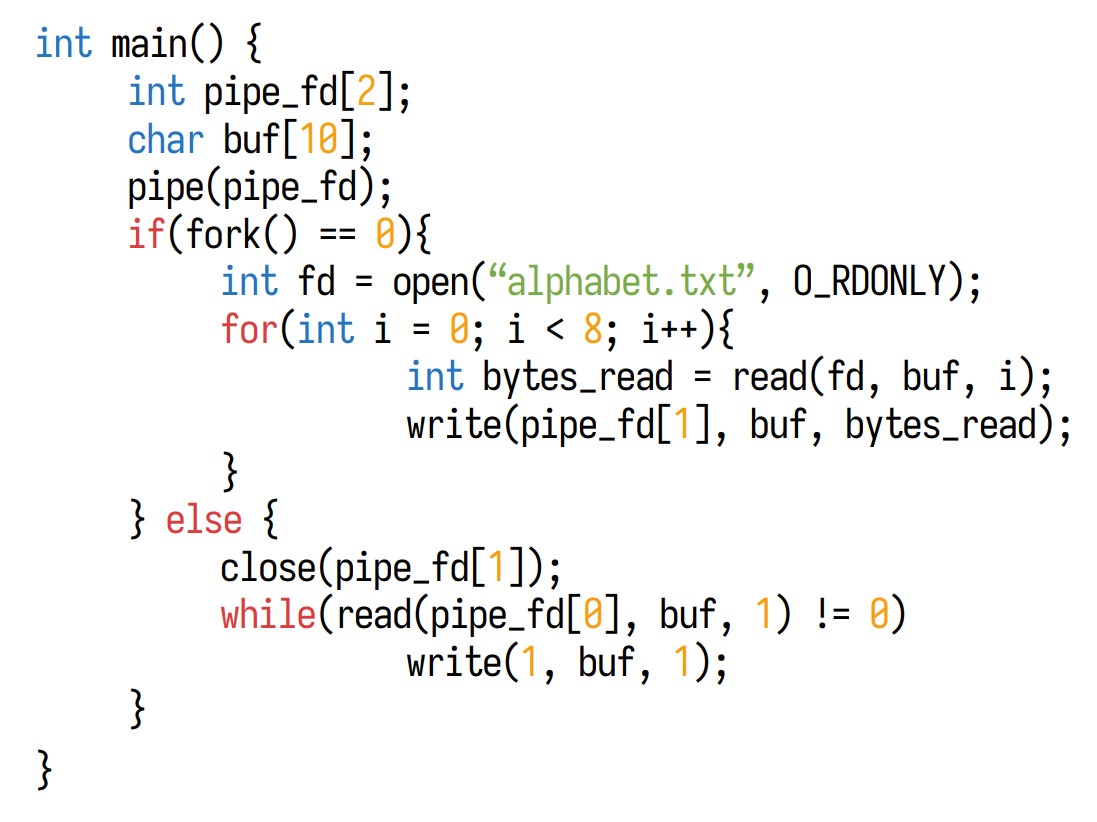
What is the behavior of the following program? Assume alphabet.txt contains the lowercase alphabet characters
Results: “abcdefghijklmnpoqrstuvwxyz”
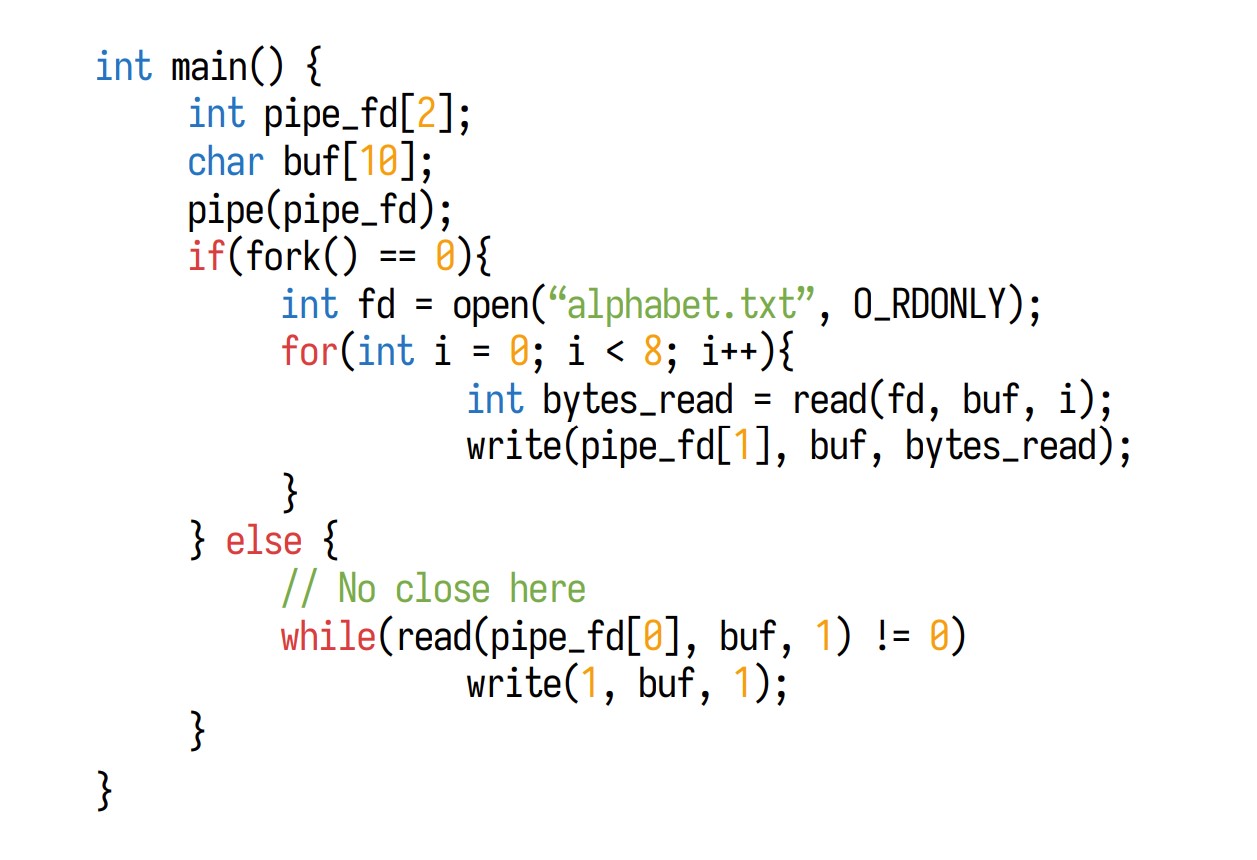
What is the behavior of the following program? Assume alphabet.txt contains the lowercase alphabet characters
Results: will hang, it is forever waiting for EOF from the child, so it never goes into the read
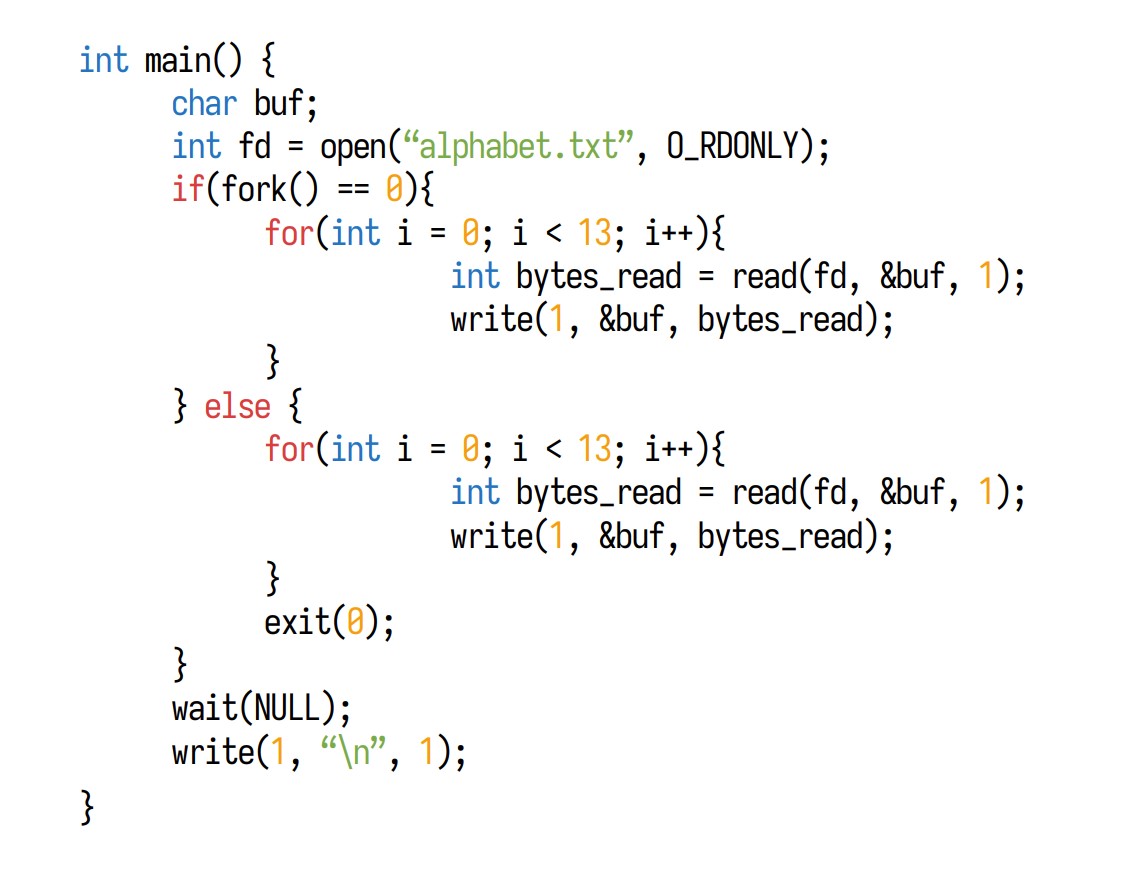
What is the behavior of the following program? Assume alphabet.txt contains the lowercase alphabet characters
Results: “abcdefghijklmnpoqrstuvwxyz”
What happens to the cursor when a parent and a child read from the same file descriptor created before the fork?
they share the cursor, so when one of them moves it, it moves for both parent and child
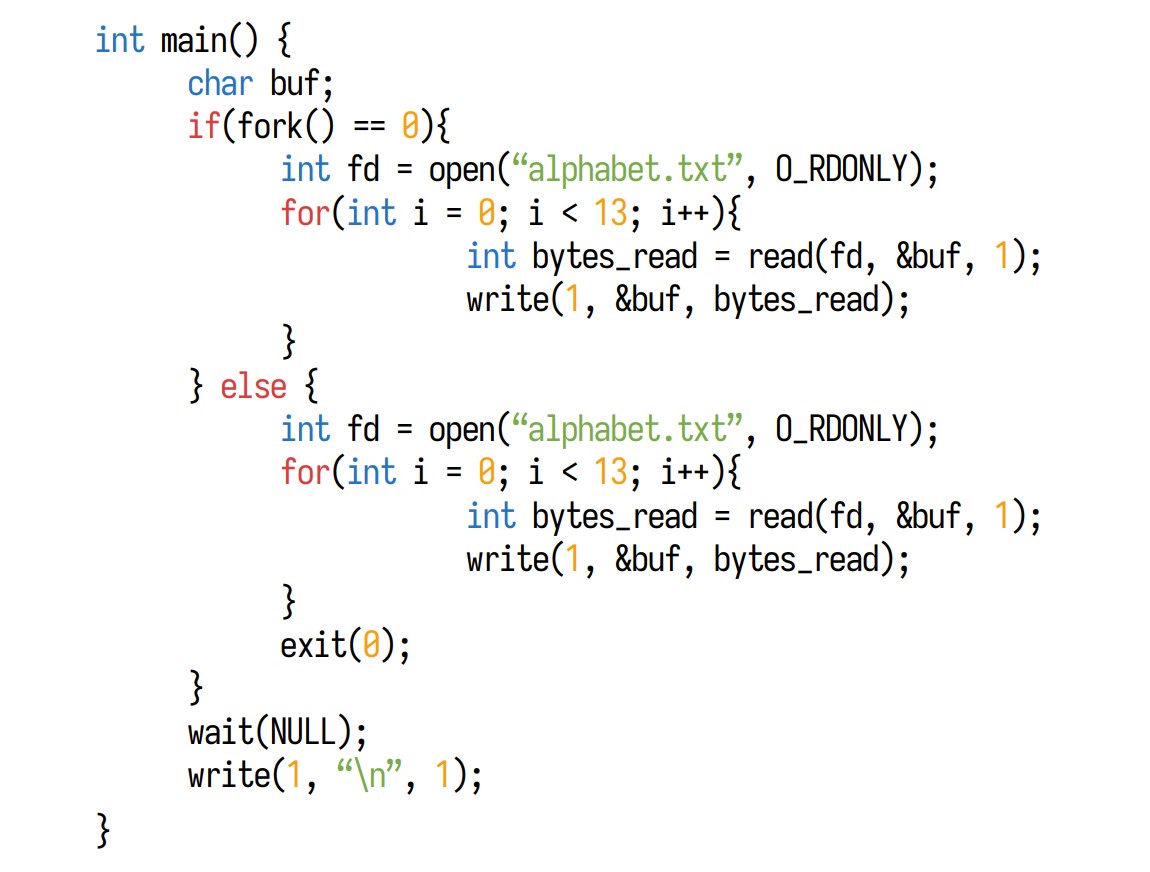
What is the behavior of the following program? Assume alphabet.txt contains the lowercase alphabet characters
Result: the first 13 letters of the alphabet file in any order
What happens to the cursor when a parent and a child read from file descriptors created after a fork?
The cursor is not shared, so it moves separately based on the child's and parents’ behavior, respectively
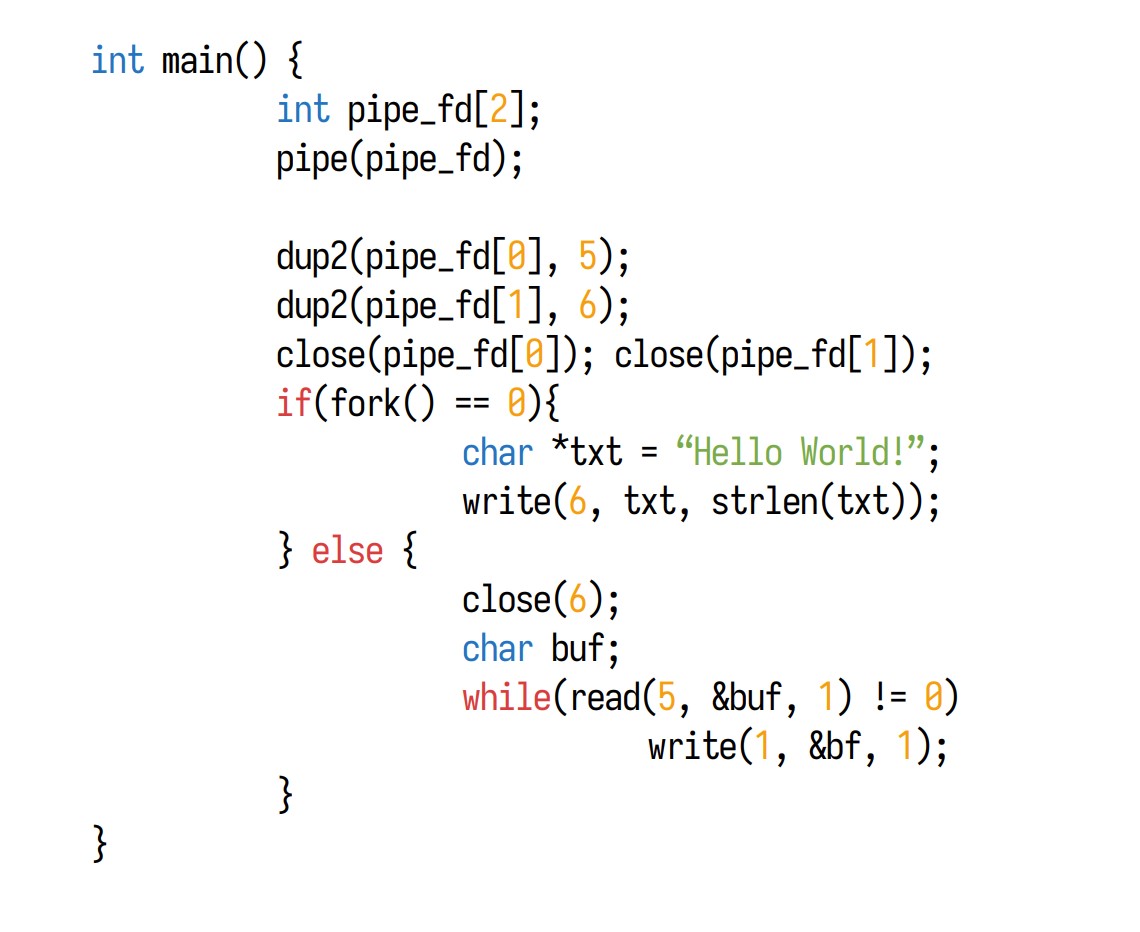
What is the output of the following program?
Results: "Hello World”
Can processes in the foreground write to the terminal device
yes
can processes in the background write to the terminal device
no
Can a session have multiple foreground groups?
No
Can a session have multiple background groups
yes
How many processes can be in a foreground group?
as many as you want
How many processes can be in a background group?
as many as you want
Can signals be sent to a foreground process group
yes
can signals be sent to a background process group
yes
dup() syscall
calling convention: int ___(int oldfd)
description: allocates a new file descriptor that refers to the same open file descriptor as the descriptor oldfd. The new fd is the lowest numbered fd that was unused in the calling process, does not close the oldfd, and can be used interchangeably with the new fd
returns: on success: the new fd, on error -1 and errno is set.
dup2() syscall
calling convention: int ____(int oldfd, int newfd)
Description: allocates a new file descriptor that refers to the same open file descriptor as the descriptor oldfd, but sets the newfd to be the number set in newfd, if newfd was previously open it is now closed before being reused and the close is performed silently
returns: on success: the new fd, on error -1 and errno is set.
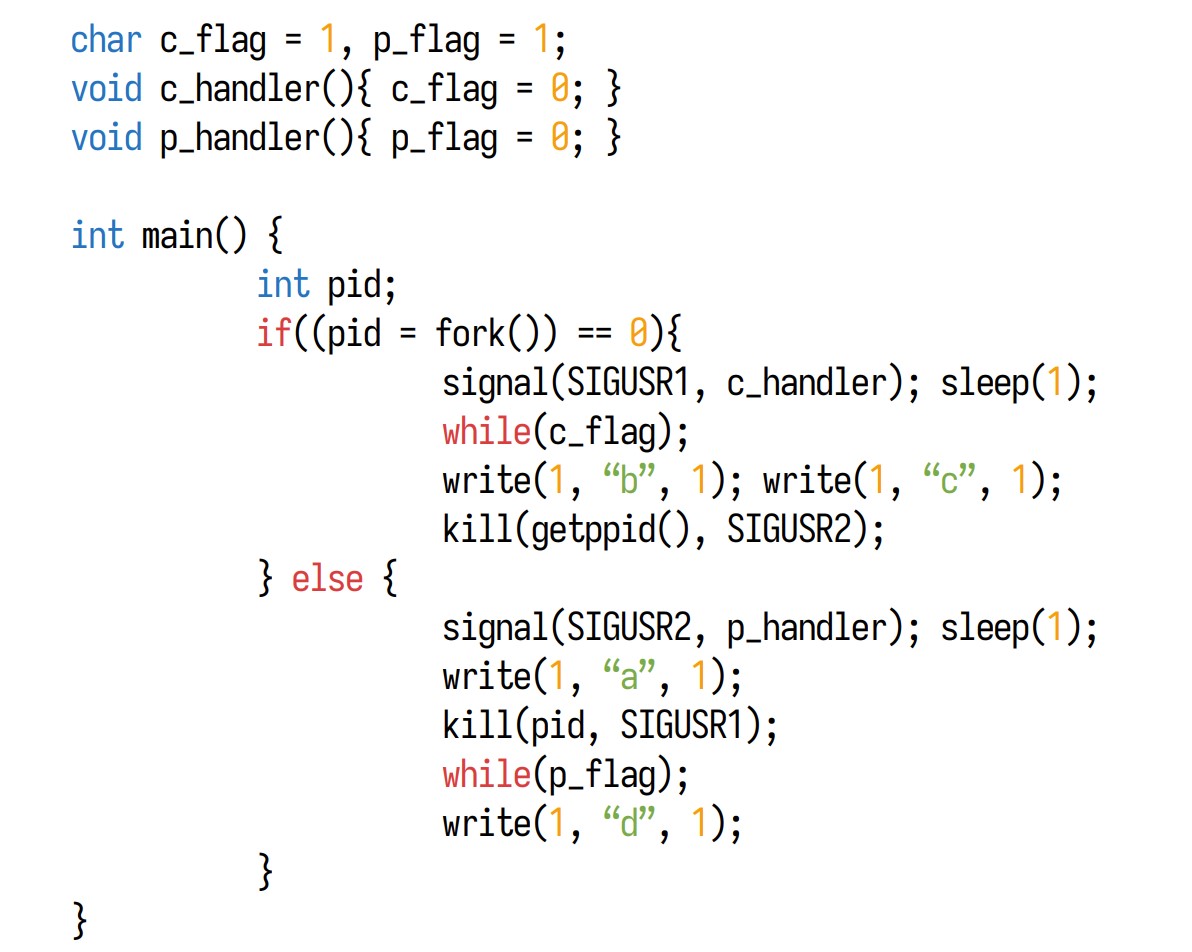
What is the output of the following program?
Results: abcd
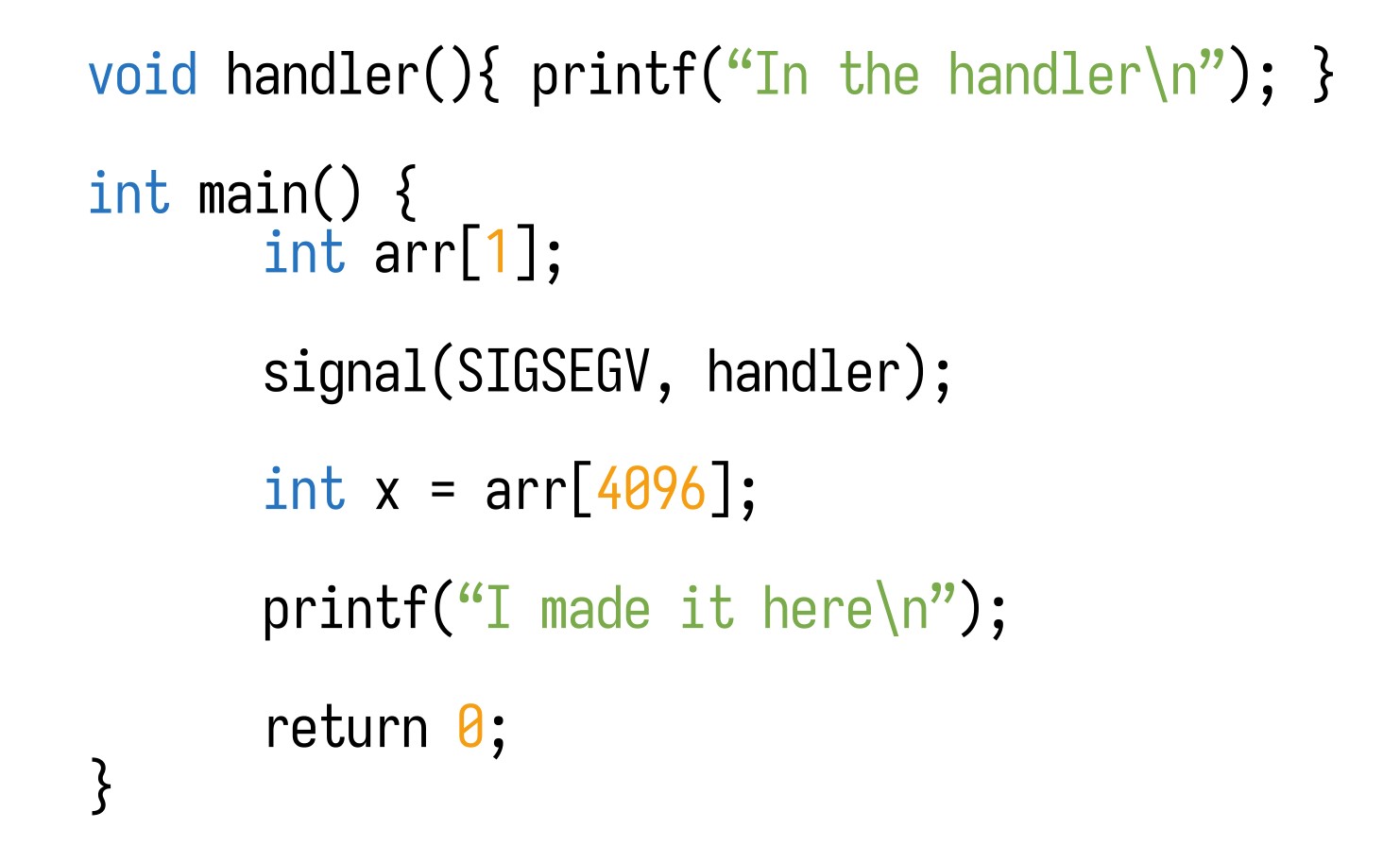
What does the following code print?
Results: “In the Handler” infinitely
What are the high-level steps to go from power-on to shell prompt?
BIOS
Bootloader
Kernel
inti program
getty
login shell
Accept credentials
shell
What is the first step to go from power-on to shell prompt
BIOS
What is the second step to go from power-on to shell prompt
Bootloader
What is the third step to go from power-on to shell prompt
kernel
What is the fourth step to go from power-on to shell prompt
init program
What is the fifth step to go from power-on to shell prompt
getty
What is the sixth step to go from power-on to shell prompt
login shell
What is the seventh step to go from power-on to shell prompt
accept credentials
What is the eighth step to go from power-on to shell prompt
shell
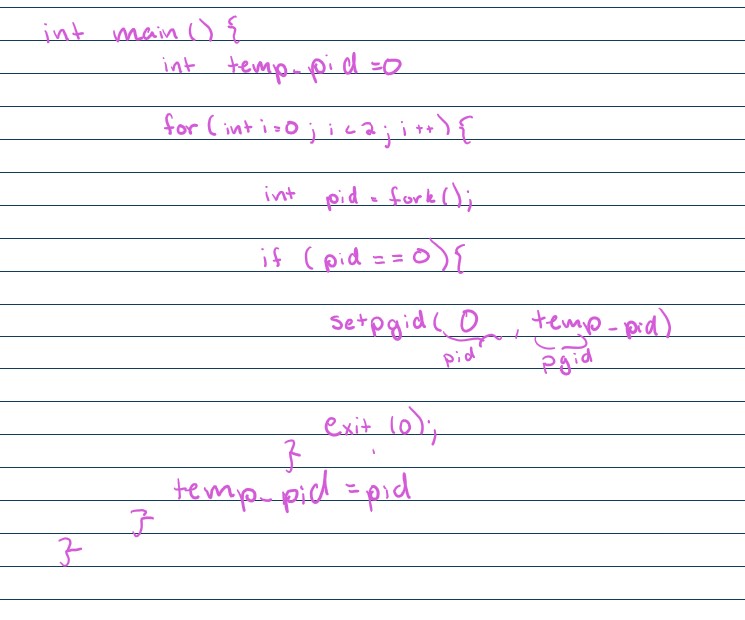
What does this code do?
creates a parent with two children which are in their own process group
Assuming a declaration of int **x; Which of the following are equivalent to x[0][0]
1.**x
2.*&**x
3. &&x
4.*&x
5.*x[0]
6.*x&*
1,2,5
PROT_READ
mmap flag: sets the read perms per process
PROT_WRITE
mmap flag: sets to write perms per process
PROT_EXEC
mmap flag: sets the execute perms per process
PROT_NONE
mmap flag: clears the existing permissions
MAP_SHARED
mmap flag: other processes are allowed to access the map
MAP_PRIVATE
mmap flag: other processes can not access the map
MAP_ANONYMOUS
mmap flag: mapping is not backed by a file, allocating extra memory
Where does mmap allocate memory?
virtual address space of the process, not in the stack or the heap it’s a different part entirely
How many bites minimum can mmap allocate?
4096 bytes, mmap always at minimum allocates a page(4096 bytes) of memory and sets the permissions on a page basis
Does mmap require a file to back the memory contents?
No(MAP_ANONYMOUS)
Why do we use mmap?
it allows us to share memory between multiple processes and set permissions
what is a soft/symbolic link?
a pointer to the original file, no data is stored from the link
What is a hard link?
a pointer to the same data as the original file, basically creating multiple names for the same file