7: Information Security Policies
1/16
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
17 Terms
Security Policy
Policies establish the rules where organizations can direct funding, people, processes, and technology in a secure manner.
Security Standard
Information security standards are the measurable metrics that can be used to determine an organization’s compliance with policies.
Security Procedure
Procedures specify the step-by-step instructions that are created in support of the policy.
Security Guideline
Guidelines are guidance about how to achieve the goals of the security policy. (Suggestions)
Security Policy Development & Phases
Focus on the why, who, where, and what during the policy development process.
Phases:
Regulatory requirements (industry specific)
Advisory requirements (best practices)
Informative requirements (organization specific)
Frameworks
Topics included in a security policy vary from organization to organization according to regulatory and business requirements.
Organizations may prefer a control objective-based approach to create a security policy framework.
Gov agencies may take FISMA-based approach (Federal Info Sec Management Act).
NIST SP 800-53 is a good starting point for any org in making sure all basic control objectives are met.
Security Policy Audience
All the individuals who handle the organization’s information:
Employees
Contractors and temporary workers
Consultants, system integrators, and service providers
Business partners and third-party vendors
Security Policy Categories
3 primary categories:
Regulatory Policies: Focus on audit and compliance, containing legal statements about requirements and their reasons.
Advisory Policies: Provide guidance on business-specific practices, including computer systems, networks, personnel, and physical security, based on best practices.
Informative Policies: Serve as a catch-all for policies not covered by Regulatory or Advisory. Addressing specific needs of business units, partners, vendors, and customers.
Security Awareness
Include communications and periodic reminders to employees about what they should and should not divulge to outside parties.
Training and education help mitigate the threats of social engineering and information leakage.
May fail if: not changed frequently, does not include performance evaluations and additional tracking.
Security Enforcement for People
Policy Enforcement for Vendors: The organization's Board of Directors is responsible for managing relationships, deals, contracts, and statements of intent with business partners and non-corporate entities to ensure security compliance.
Policy Enforcement for Employees: Human Resources oversees corporate security policy enforcement for all employees and temporary workers, ensuring consistent standards for everyone.
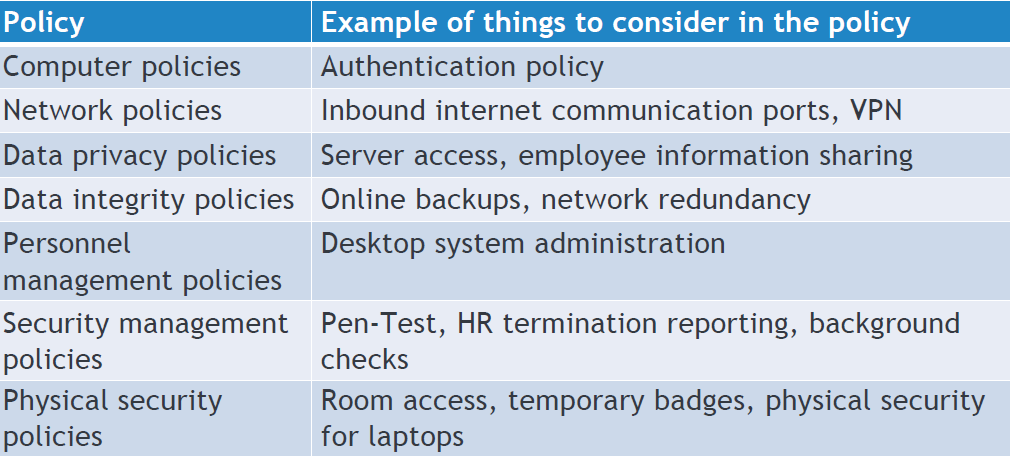
Security Policy Topics
Maintenance
Once the security policies, standards, procedures, and guidelines are in place, well-established, and in a position to dictate daily operations, an audit may be performed by outside agencies or internal departments.
Types of Information Security Policy
Enterprise Information Security Program Policies (EISP)
Issue-Specific Information Security Policies (ISSP)
Systems-Specific Security Policies (SSSP)
EISP
A high-level, management-approved document that outlines an organization's security philosophy, roles, and strategy to protect data confidentiality, integrity, and availability.
It serves as a compliance blueprint, guiding the creation of specific security policies, assigning responsibilities for information security, and directing the development, implementation, and management of the security program.
ISSP
A targeted policy outlining rules for using specific technologies or addressing particular risks within an org, such as BYOD, AUP, Access Control Policy.
Provides detailed guidance on employee behavior, access, and sec reqs to mitigate risks.
Protects org from inefficiency and ambiguity.
SSSP
A detailed document that describes security procedures, settings, and access rules for a particular system or technology (like a database, server, or application).
Unlike general security policies, SSSPs are customized for one specific asset to address its unique risks and operations.
SSSPs can include management guidance, technical details, or both, either as separate sections or combined in one document.
Examples: VPN policy, Firewall config policy, Database Access policy.
Top 10 Security Policies
Acceptable Use Policy (AUP) = All users who access the organisation’s assets
Network Security Policy = Secure network access and protection
Data Management Policy = All users, data storage, access, processing & sharing
Access Control Policy = All users and third parties with access to data
Password management Policy = All users and third parties possessing credentials
Remote Access Policy = All users and devices access the network from outside
Vendor Management Policy = All vendors (suppliers, customers, third parties) to access data
Removal Media Policy = All users
Incident response Policy = All employees
Awareness and Training Policy = Security officers should conduct training to all employees