IB Computer Science Topic 3 Networks
1/66
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
67 Terms
Circuit Switching
A dedicated connection created between two parties where data is sent along that dedicated channel in one go
Technologies required for VPN
- VPN Client software
- encryption protocol
- tunneling protocol
-VPN-aware routers and firewalls (to permit VPN traffic to pass)
-VPN server (to handle incoming VPN traffic)
advantage of VPN
- resources such as files can be shared over remote hosts without having to provide dedicate lines between them
- reduces costs
disadvantages of VPN
-Performance is outside organisation control
-Needs technical expertise
Tunnelling protocol
an encrypted link between the user and the public network
SAN (storage area network)
A network not normally accessible from the main LAN on which the hosts are predominantly high-capacity storage devices, such as tape drives.
PAN (Personal Area Network)
A short-range network of personal devices, such as cellphones, tablets and audio headsets, often utilizing Bluetooth short-range radio.
Network
a group of computer systems and other computing hardware devices that are linked together through communication channels to facilitate communication and resource sharing among a rage of users
Firewall
a program that restricts data allowed into and out of a network, on the basis of a set of rules.
Packet
The unit of data that is routed on a packet-switched network.
LAN (Local Area Network)
A connection of two or more computers in close proximity, such as a school or business. Uses wired communication protocols E.G ethernet.
MAC address
A Media Access Control address is a hardware address that uniquely identifies each node on a network.
IP Address (Internet Protocol)
A number assigned to any node that is connected to the Internet. It provides a standard set of rules for sending and receiving data through the Internet.
Intranet
Private internet, it is made up of webpages and viewed through a browser, but access is restricted to users within an organisation.
Extranet
An intranet that has been opened up to provide limited access to a selection of users outside the organisation.
Port number
A identical number used to identify the specific sever which was linked to a specific IP address.
Proxy
Machine that brokers the communication between two other machines.
Server
A server is a computer / software which manages access to a centralized resource or service in a network.
A server is a computer/software that provides data to other computers/clients in a network;
Packet Switching
Designed to allow data transmission on unreliable networks. Large files are split into smaller data packets and may take different paths to the target computer. The split packets are re-assembled at the target machine.
VPN "Virtual Private Network"
A connection that uses the public internet to access a private network using encryption and tunneling
Data packet
A unit of data for transmission;
With a format;
Accept answers that expresses the idea that the packet is the fundamental unit of data transmission on a network (IP is assumed).
Accept answers that suggest the student understands there is a format for the packet, including
"contains address and data".
Client
A client is a simple application or a whole system that accesses services being provided by a (remote) computer/server;
Internet
A network of networks connected using IP (Internet Protocol). It powers a large range of communication media such as the World-Wide Web (documents connected by hyperlinks), email, chat, gaming, newsgroups, etc)
WLAN
Same as LAN but uses wireless connection.
Protocol
An internationally agreed set of rules to ensure transfer of data between devices (HTTP, TCP, IP, SMTP, ASCII)
transmission mediums
copper wire, fibre optic cable, wireless, satellite
length of line
all data travels at some speed less than the speed of light, therefore the distance that the data has to travel effects the speed
network traffic
a measure of how much data is being sent on the network. Networks can get congested just like roads
characteristics of a copper cable
a physical connection, fast speed, reliable, medium cost and high security
characteristics of fibre optic cables
a physical connection, very fast speed, very reliable, high cost and high security
characteristics of Wi-Fi
radio signals, slower speed, can be patchy, low cost and low security
things that cause network traffic
Malware and viruses which make unauthorised connections to other hosts. A denial-of-service attack is deliberately designed to overload a portion of a network to stop it from functioning properly
Bandwidth
the maximum theoretical amount of data that can be sent or recieved over a particular connection in a given time
peer-to-peer network
A type of network architecture where each computer is linked to one another without the use of a server. While they can be faster due to the lack of servers, they are less secure as security is delegated to each peer
WAN (Wide Area Network)
Communications network that connects geographically dispersed hosts, usually across regional or national boundaries. Often a network of LANs belonging to a multinational company linked by leased lines.
HTTP (hypertext transfer protocol)
a set of rules that defines how a pages transfer on the web
Symmetric key encryption
Once the text is encrypted it also can be decrypted. The same key is used to encrypt and decrypt data.
Asymmetric key encryption
system in which two keys are used to scramble messages: a public key used only to encrypt data, and a private key used only to decrypt it.
Hashing
One-way encryption. Once text is encrypted, it cannot be decrypted. It is used to verify downloads of any size input and outputs a specific size.
Lossless Compression
Data compression techniques in which no data is lost. e.g. run-length-encoding
Lossy Compression
Data compression techniques in which some amount of data is lost. This technique attempts to eliminate redundant information.
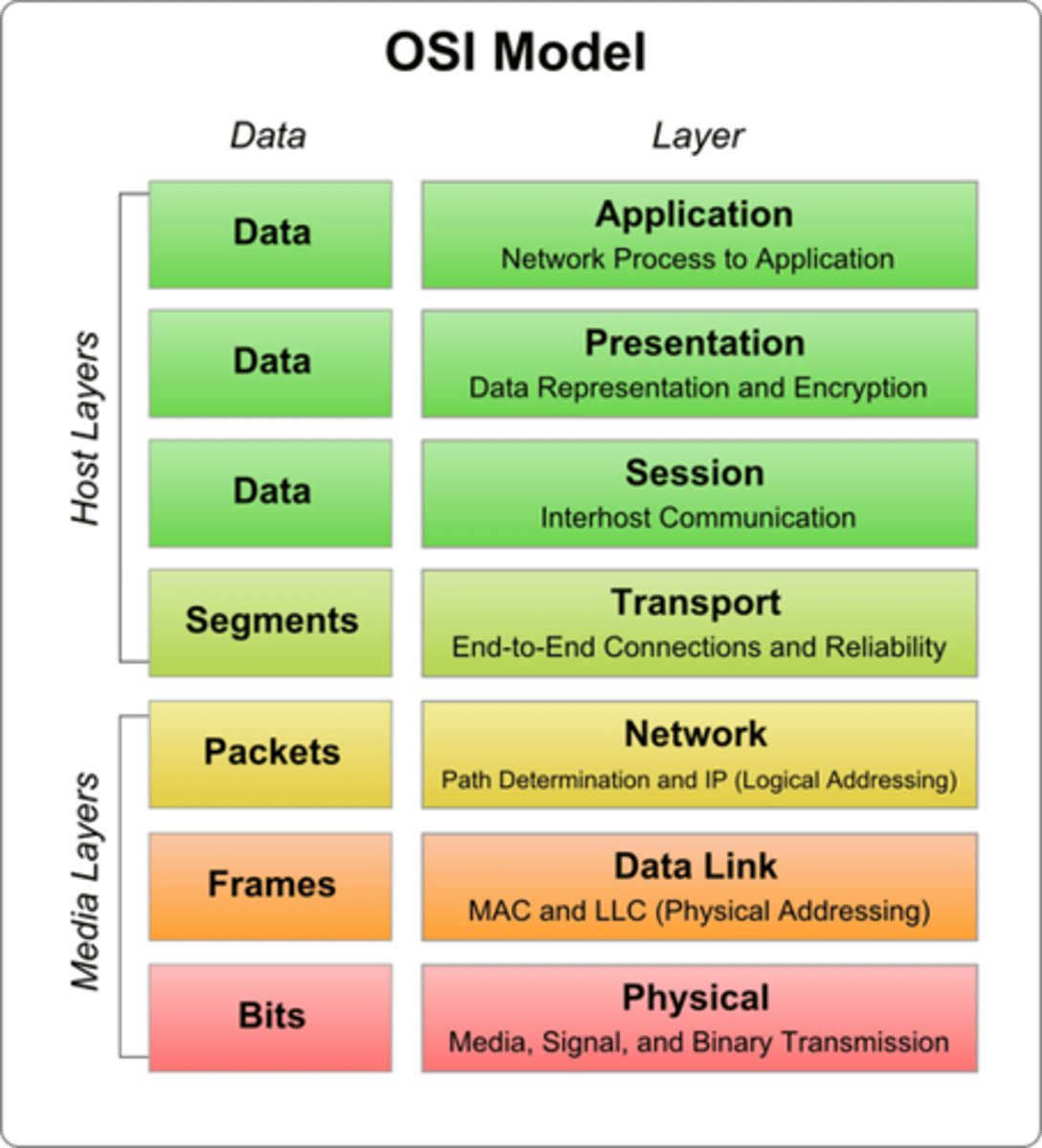
Open Systems Interconnection (OSI) model
A seven-layer architecture for defining how data is transmitted from computer to computer in a network, from the physical connection to the network to the applications that users run. It also standardizes interactions between network computers exchanging information.
Types of Hacking
Denial of service attack (DOS), Man-in-the-Middle, Phishing, Trojan Horse, Spoofing, Spyware
OSI Networking Model Layers
Physical Layer.
Data Link Layer.
Network Layer.
Transport Layer.
Session Layer.
Presentation Layer.
Application Layer.
Denial of Service
An attack designed to overload a server by making many simmultaneous requests for resources
ADSL
A fast way of sending computer data over an ordinary phone line - usually used to provide broadband internet access to homes, schools and offices. An alternative to a cable modem.
Phishing
a technique to gain personal information for the purpose of identity theft, usually by means of fraudulent (fake) e-mails
Necessities of protocols 1
Data integrity: Ensures data is not changed or corrupted during transmission
Flow control: Controlling flow/load of resources due to limited bandwidth. Transport layer
uses protocols, e.g. to request sending applications to slow down data flow rate
Necessities of protocols 2
Deadlock prevention: Prevents situation where two or more competing programs or actions are sharing a resource and preventing each other from using it
Congestion management: Prevents requests on network resources exceeding capacity
Error checking
Factors affecting speed of data transmission
-Different parts of a network use different media- e.g. fibre optics are faster than coax cable.
-Bandwidth of network.
-Data transfer rate and read speed of storage devices.
-No. of connected devices can increase the amount of traffic (demand and requests made), leading to congestion
-Time required for security and authentication checks
-Packet loss and retransmission- delayed by congestion
Network Traffic
a measure of how much data is being sent on the network
Private key
One of the keys used in asymmetric encryption systems. This instead is only available to the receiver, and is kept secret in order to make sure nobody else can decrypt the data sent.
MAC (Media Access Control) address
a hardware identifier that uniquely identifies each device on a network
Public key
One of the keys used in asymmetric encryption systems. It is widely distributed and available to everyone to use.
Advantages of Packet Switching
Full use of available bandwidth
Resilient to communications hardware failure
Devices of different speeds can communicate easily
Client-Server
A network architecture in which a system is divided between server tasks performed on the instructions received from clients, requesting information.
Advantages of protocols
Data integrity, flow control, deadlock, congestion, error checking
distributed denial-of-service (DDoS) attack
This is when many computers collaborate to shut down a target, usually by keeping it busy or overwhelming it with incoming requests, aiming to crash the targets system.
Wireless Router
A central hub for all the computers to connect to which
enables wireless network packet forwarding and routing
Network Interface Card
Network interface cards are used to connect each computer to the network;
so they can communicate with the network router to receive information packets;
Interface cards determine the infrastructure of a local area network;
and allow all of the computers to connect to the network;
Wireless access point
Allows Wi-Fi devices to connect to a wired network
Wireless repeater
Devices which expand the reach of wireless networks
Network Authentification
Securing a network by requiring a username and password or biometrics to access a network
Network User Roles
Setting up network accounts so that they are only allowed specific access to certain network resources and are only able to perform certain actions e.g. normal users not allowed to delete network resources
Advantages of Fibre Optic Cable over Wifi
allow faster transmission speedsmore secure/harder to break into
is more reliable/less likely to suffer interference
allow transmission over longer distance
allow greater bandwidth
Router
controls the flow of data in the network
inspects address of data packets
directs to the appropriate network path/ selects a path between networks (by inspecting address of data packets)
securely transmits data packets (across that path toward the intended destination)
Encryption
Process of converting readable data into unreadable characters to prevent unauthorized access. The encoded message can be decoded to return to its original readable data.