JUST 405 QUIZ 4
1/64
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
65 Terms
Information Security
the practice of defending information from unauthorized access, use, disclosure, disruption, modification, perusal, inspection, recording, or destruction
2 major aspects of information security
IT Security, Information Assurance
Purpose of information security
to manage risk
What does Security Management entail?
Risk management, Information security policies, Procedures and standards, Guidelines & baselines, Information classification, Security organization, Security education
Facts of Security Management
Helps construct a budget with necessary funds to protect the recognized assets from their identified threats
Has changed due to the shift from centralized network structures to the distributed networks we see today
Vulnerability
Software, hardware, or procedural weakness that may provide an attacker the open door he is looking for to enter a computer or network and have un-authorized access to resources within the environment
Threat
Something or someone that is a potential danger to information or systems
Risk
The likelihood of a threat agent taking advantage of a vulnerability and the corresponding business impact
Risk= (______ * ________)
Threat * Vulnerability
Exposure
an instance of being exposed to losses from a threat agent
Controls/Countermeasures/Safeguards
put into place to mitigate the potential risks
Security officer role is directly responsible for...
monitoring a majority of the facets of a security program
Risk Mitigation (4 Ways)
Attempt to mitigate risk directly,
accept the risk,
transfer the risk (insurance),
ignore and hope for the best
AIC Triad
Availability, Integrity, Confidentiality
(see slide 14 and 15 in Information Security and Business Continuity PowerPoint)
A: insuring systems and data are accessible when needed
I: maintaining data accuracy and trustworthiness (guarantees data remains accurate and unaltered during storage or transmission)
C: restricting access to authorized users
Access Control
Examines mechanisms and methods used to enable administrators to control what subjects can access
Telecommunications and Network Security
Examines internal, external, public, and private communications systems; networking structures; devices; protocols; and remote access and administration.
Information Security and Risk Management
Examines the identification of company assets and what type of budget to develop for security implementations, with the goal of reducing threats and monetary loss.
Application Security
Examines the security components within operating systems and how to best develop and measure their effectiveness. It looks at software life cycles, change control, and application security.
Cryptography
Examines methods and techniques for disguising data for protection purposes. This involves cryptography techniques, approaches, and technologies.
Security Architecture and Design
Examines concepts, principles, and standards for designing and implementing secure applications, and operating systems. This covers international security measurement standards and their meaning for different types of platforms.
Operations Security
Examines controls over personnel, hardware, systems, and auditing and monitoring techniques. It also covers possible abuse channels and how to recognize and address them.
Business Continuity Planning (BCP) & Disaster Recovery Planning (DRP)
Examines the preservation of business activities when faced with disruptions or disasters. It involves the identification of real risks, proper risk assessment, and countermeasure implementation.
Legal Regulations, Compliance, and Investigation
Examines computer crimes, laws, and regulations. It includes techniques for investigating a crime, gathering evidence, and handling procedures. It also covers how to develop and implement an incident-handling program.
Physical (Environmental) Security
Examines threats, risks, and countermeasures to protect facilities, hardware, data, media, and personnel.
This involves facility selection, authorized entry methods, and environmental and safety procedures.
Information Risk Management (IRM)
The process of identifying and assessing risk, reducing it to an acceptable level, and implementing the right mechanisms to maintain that level.
No such thing as a 100% secure environment
Risk Analysis
The method of identifying vulnerabilities and threats and assessing the possible damage to determine where to implement security safeguards
Risk Analysis Steps (5)
1. Assign Value to Assets
2. Estimate Potential Loss per Threat
3. Perform a Threat Analysis
4. Derive the overall annual loss potential per threat
5. Reduce, transfer, avoid, or accept the risk
Quantitative Risk Analysis
Attempts to assign real and meaningful numbers to all elements of the risk analysis process
Qualitative Risk Analysis
Does not assign numbers and monetary values to components and losses
Instead, qualitative methods walk through different scenarios of risk possibilities and ranks the seriousness of the threats and the validity of the different possible countermeasures based on opinions
Risk of System Compromise = ________ X _______
Risk of System Compromise = {Prob} Attack X {Prob} Vulnerability
T or F: Humans are terrible at security
true
The goal of cyber resilience
Return to normal operations quickly after a disturbance
Cryptography
the study of encryption
Cryptanalysis
the study of defeating encryption
SIGNIT
Signals Intelligence
interception and analysis of electronic signals and communications (i.e. radio waves, radar, and satellite transmissions) to gather intelligence on an adversary’s capabilities, intentions, and actions
e.g. intercepting enemy radio traffic, decoding encrypted messages, tracking radar signals to identify weapon systems
National Security Agency (N.S.A.) was developed out of need to do what during WWII?
Out of need to break encrypted communications during WWII
Encryption
Secures data by encoding it, used when confidential information need to be sent by an insecure means, gives reasonable expectation of privacy
T or F: All encryption can be broken
true (just might take forever)
Modern Encryption
performed by computers, occurs in the binary level (1's and 0's)
Encryption does not stop...
traffic analysis, ability for people to see that you are communicating covertly, doesn't hide the fact that encryption was/is used during a forensic exam of the computer
T or F: Web browsers have built in encryption
true
The strength of the encryption is based upon the....
length of its key (and of course its algorithm)
Whats the weakest link in computer security?
Humans
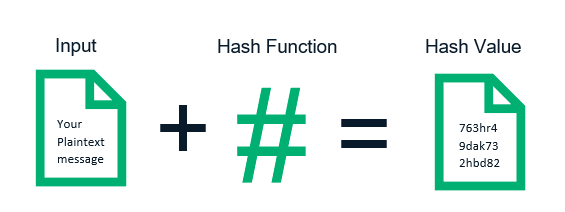
Windows doesn't store your password, it stores the _____ of your password.
HASH (one-way cryptographic process that converts input data of any size into a unique, fixed-length string of characters)
The Surface-layer Web (Clearnet)
Accessible via common search engines
The Deep Web
Accessible via the public internet, but is typically not obtainable through popular search engines
The Dark Web
Layer of the Internet that exists to preserve the anonymity of its users (*alters IP*), Features of the dark web include websites, discussion forums, and marketplaces that trade in legitimate and illicit products and services.
What is known as the "E-Bay of drugs"?
Silk Road
Forensic Analysts
Work in a computer 'lab' environment,
Highly trained to understand
the inner workings of a computer,
Use very specialized tools to extract computer evidence in a forensically sound manner,
Compile evidence to present at court
Subject matter experts
have extremely specialized knowledge for a particular system or segment of forensics
Digital evidence can be either...
physical hardware (computer or hard drive itself) or media that contains relevant data objects or the data itself
To get a search warrant you must have...
probable cause, specify a crime has been committed, evidence of crime exists in the place to be searched, specific evidence must be named, or general evidence facilitating a specific act may be described by function
3 steps to seizing digital evidence
scene safety, digital media identification/minimize crime scene by prioritizing physical media, seizure/transport of storage devices and media
T or F: When seizing digital evidence it is not important to get close up photos of any serial numbers/identifiers on the case of devices.
false
T or F: Information stored in the active memory of a computer (aka the RAM) will be lost once power is cut to the system.
true
If it is apparent that a data destructive program has been launched, you should...
IMMEDIATELY pull the power cord from the back of the system
2 key concepts of digital seizure to consider
There are just not enough forensic technicians to have them attend personally to each seizure & there will come a time when the amount of storage exceeds the ability for LE to seize everything
Investigative process (5 steps)
reported or observed crime
investigation
arrest
charges filed
prosecution
Hashing
creates a unique fingerprint of any data, can be used to authenticate data
Active Files
files that the user can access or create. Can be found easily
Latent Data
not so easily found, it is often "deleted" files. Not recognized by the operating system.
Bit-Stream Copies
reproduce every "bit" of information on a drive, includes active and latent files.
T or F: Wiping a drive eliminates any "contamination" on the drive that may be left over from previous analyses.
true
"Drive Free Space" consists of hard-drive space that...
was never written to
was formerly occupied, but the system now sees as free
Data Carving
where real files and file remnants are recovered from free space