Networking flashcards (copy)
1/96
Earn XP
Description and Tags
ej is a bitch
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
97 Terms
Which protocol does IPv6 use to resolve the MAC address associated with a destination host.
Neighbor Discovery Protocol (NDP)
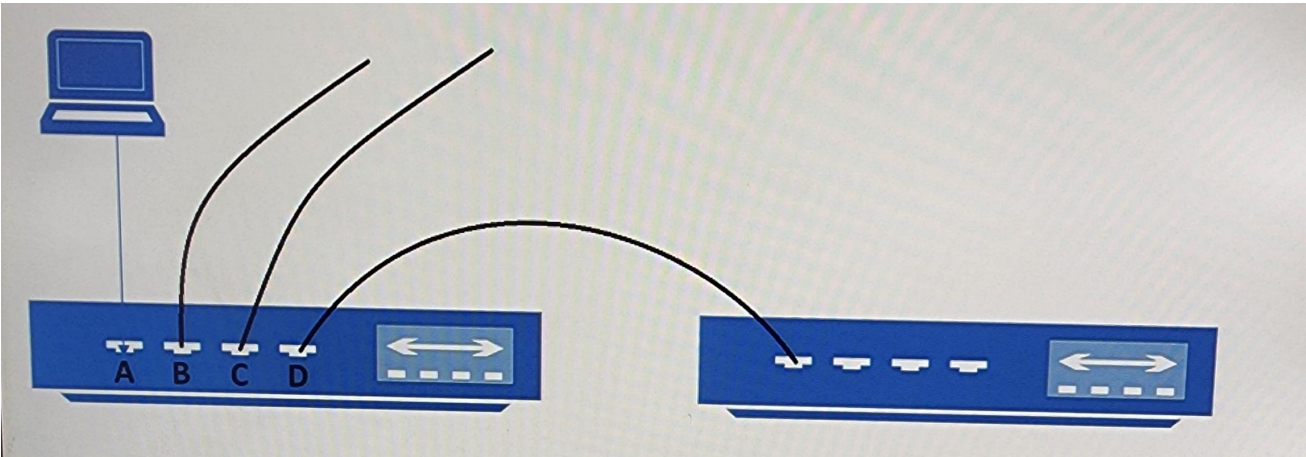
You have two switches that are connected as shown in the image.
The laptop is connected to port A on the 1st switch, The second switch is connected to port D on the first switch. The laptop sends a broadcast frame to the first switch.
• You need to identify the ports through which the broadcast frame are forwarded.
• Which ports should you identify?
B, C and D only
Match the OSI layer with the correct protocol.
OSI Layer - Application
SMTP, HTTP, FTP
Match the OSI layer with the correct protocol.
OSI Layer - Transport
TCP, UDP
Match the OSI layer with the correct protocol.
OSI Layer - Network
Router
Match the OSI layer with the correct protocol.
OSI Layer - Data Link
Layer 2 Switch
Match the OSI layer with the correct protocol.
OSI Layer - Physical
Cable, Hub, NIC
Identify the correct CIA security principle from the example.
You generate a digital signature and attach it to a message.
Integrity
Identify the correct CIA security principle from the example.
You configure 3 redundant web servers at your company
Availability
Identify the correct CIA security principle from the example.
You encrypt sensitive email message.
Confidentiality
Which network technology is not impacted by electromagnectic and radio wave interference.
Fiber
How does a firewall determine which traffic to block?
The firewall matches traffic based on source and destination IP addresses.
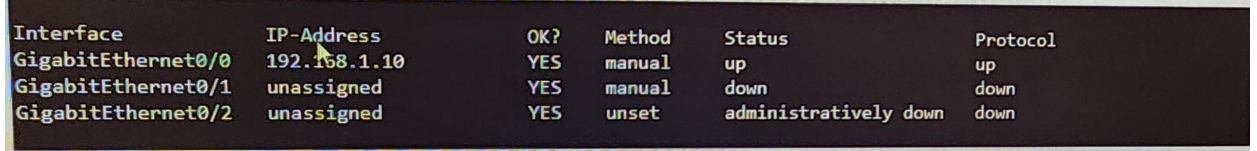
You connect to a cisco switch and run the following command: show ip interface brief, is the below statement true or false according to the partial output?
A technician set the ip address for GigabitEthernet0/0 by using the CLI
True
What is the most compressed valid format of the IPv6 address 2001:0db8:0000:0016:0000:001b:2000:0056?
2001:db8:0:16::1b:2000:56.
Low bandwidth can increase network latency.
True
High levels of network latency decrease network bandwidth.
False
You can increase throughput by decreasing network latency
True
Assign the reserved IP address 10.10.10.200 to a web server at your company.
DHCP (Dynamic Host Configuration Protocol)
Perform a query to translate companypro.net to an IP address
DNS (Domain Name System)
Perform a ping to ensure that a server is responding to network connections
ICMP (Internet Control Message Protocol)
Which protocol allows you to securely upload files to another computer on the internet?
SFTP (Secure File Transfer Protocol)
A local company requires two networks in two new buildings. The addresses used in these networks must be in the private network range. Which two address ranges should the company use?
172.16.0.0 to 172.31.255.255 and 192.168.0.0 to 192.168.255.255

A Cisco PoE switch is shown in the following image. Which type of port will provide both data connectivity and power to an IP phone?
Ports identified with number 6

During the data encapsulation process, which OSI layer adds a header that contains MAC addressing information and a trailer used for error checking?
Data Link
What is the purpose of assigning an IP address to the management VLAN interface on a Layer 2 switch?
To enable access to the CLI on the switch through Telnet or SSH
Which standard contains the specifications for Wi-Fi networks?
IEEE 802.11
You want to store files that will be accessible by every user on your network. Which endpoint device do you need?
Server
What is a hub?
A basic networking device that connects multiple Ethernet devices together, making them act as a single network segment.
What is an access point?
A device that provides wireless connectivity to a network.
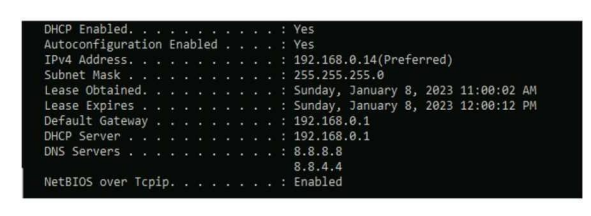
Computers in a small office are unable to access companypro.net You run the ipconfig command on one of the computers. The results are shown in the exhibit. You need to determine if you can reach the router. Which command should you use?
ping 192.168.0.1
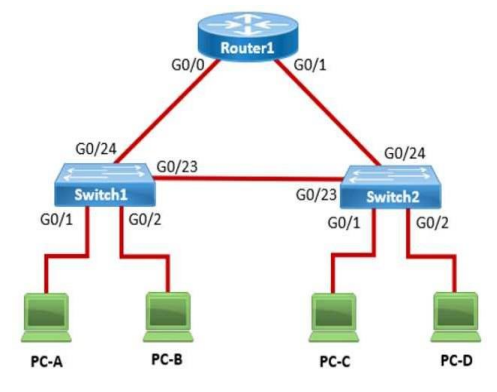
PC-A sends a frame to PC-C. Switch1 does not have a mapping entry for the MAC address of PC-C. Which action does Switch1 take?
Switch1 floods the frame out all active ports except port G0/1.
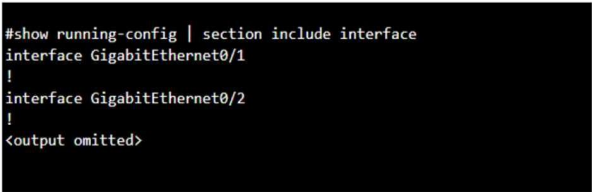
You purchase a new Cisco switch, turn it on, and connect to its console port. You then run the following command:
For each statement about the output, select True or False
The two interfaces are administratively shut down:
False
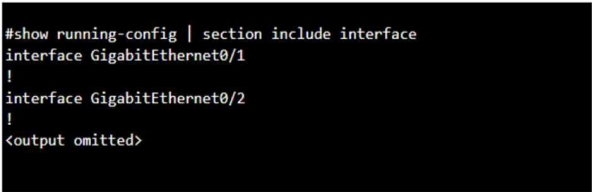
You purchase a new Cisco switch, turn it on, and connect to its console port. You then run the following command:
For each statement about the output, select True or False
The two interfaces have default IP addresses assigned:
False
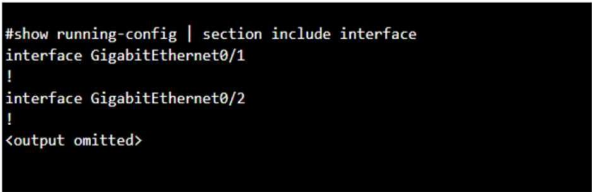
You purchase a new Cisco switch, turn it on, and connect to its console port. You then run the following command:
For each statement about the output, select True or False
The two interfaces can communicate over Layer 2:
True
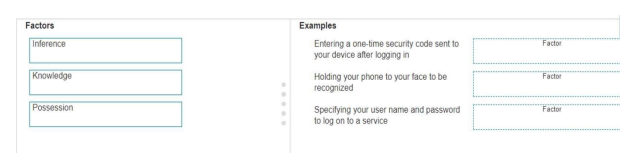
What is the correct MFA factor?
Entering a one-time security code sent to your device after logging in
Possession, This factor is something the user has
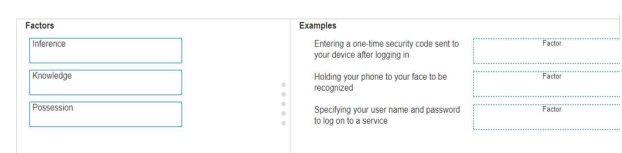
What is the correct MFA factor?
Holding your phone to your face to be recognized
Inherence, This factor is something the user is
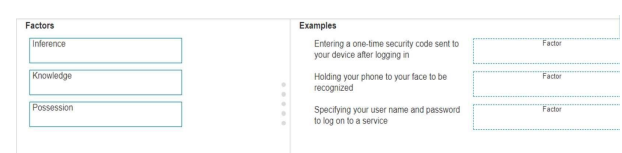
What is the correct MFA factor?
Specifying your user name and password to log on to a service
Knowledge, This factor is something the user knows
A Cisco switch is not accessible from the network. You need to view its running configuration. Which out-of-band method can you use to access it?
Console
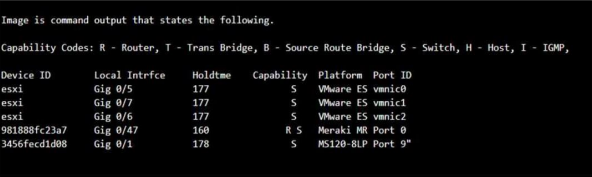
Which command will display the following output?
show cdp neighbor
A support technician examines the front panel of a Cisco switch and sees 4 Ethernet cables connected in the first four ports. Ports 1, 2, and 3 have a green LED. Port 4 has a blinking green light. What is the state of the Port 4?
Link is up and active.
Which component of the AAA service security model provides identity verification?
Authentication
What are the three components of the AAA security service model?
Authentication, Authorization, and Accounting
A help desk technician receives the four trouble tickets listed below. Which ticket should receive the highest priority and be addressed first?
Ticket 2: An online webinar is taking place in the conference room. The video conferencing equipment lost internet access.
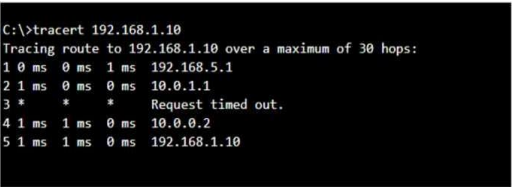
A user reports that a company website is not available. The help desk technician issues a tracert command to determine if the server hosting the website is reachable over the network. The output of the command is shown as follows:
What can you tell from the command output?
The server with the address 192.168.1.10 is reachable over the network
Which wireless security option uses a pre-shared key to authenticate clients?
WPA2-Personal
Which information is included in the header of a UDP (User Datagram Protocol) segment?
Port numbers
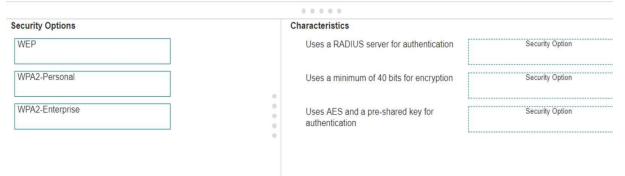
What is the correct security option?
Uses a RADIUS server for authentication:
WPA2-Enterprise
What is the correct security option?
Uses a minimum of 40 bits for encryption:
WEP
What is the correct security option?
Uses AES and a pre-shared key for authentication:
WPA2-Personal

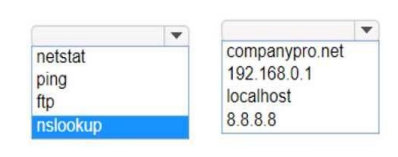
You want to list the IPv4 addresses associated with the host name www.companypro.net. Complete the command by selecting the correct option from each drop-down list.
nslookup www.companypro.net

An app on a user's computer is having problems downloading data
The app uses the following URL to download data: https://www.companypro.net:7100/api
Which Wireshark filter options would you use to filter the results? Complete the command by selecting the correct option from each drop-down list.
(Use hint)
tcp port 7100
An engineer configured a new VLAN named VLAN2 for the Data Center team. When the team tries to ping addresses outside VLAN2 from a computer in VLAN2, they are unable to reach them. What should the engineer configure?
Default gateway
A host is given the IP address 172.16.100.25 and the subnet mask 255.255.252.0. What is the CIDR notation for this address?
172.16.100.25 /22
You need to connect a computer's network adapter to a switch using a 1000BASE-T cable. Which connector should you use?
RJ45 - Used for ethernet cables.
A user initiates a trouble ticket stating that an external web page is not loading. You determine that other resources both internal and external are still reachable.
Which command can you use to help locate where the issue is in the network path to the external web page?
tracert - This command is used to determine the path packets take to reach a destination. It lists all the hops (routers) along the way and can help identify where the delay or failure occurs.
Which two statements are true about the IPv4 address of the default gateway configured on a host?
The same default gateway IPv4 address is configured on each host on the local network, and The default gateway is the IPv4 address of the router interface connected to the same local network as the host.
Which command will display all the current operational settings configured on a Cisco router?
show running-config
Select the appropriate cable type for this connection.
Connects Switch S1 to Router R1 Gi0/0/1 interface
Straight-through UTP Cable - Used to connect different devices (e.g., switch to router, switch to server).
Select the appropriate cable type for this connection.
Connects Router R2 Gi0/0/0 to Router R3 Gi0/0/0 via underground conduit.
Fiber Optic - Used for long-distance and high-speed connections, often between buildings or data centers.
Select the appropriate cable type for this connection.
Connects Router R1 Gi0/0/0 to Router R2 Gi0/0/1.
Crossover UTP Cable - Used to connect similar devices directly (e.g., router to router, switch to switch).
Select the appropriate cable type for this connection.
Connects Switch S3 to Server0 network interface card (NIC)
Straight-through UTP Cable - Used to connect different devices (e.g., switch to router, switch to server).
Choose the correct cloud computing service model from the options,
Three virtual machines are connected by a virtual network in the cloud.
IaaS (Infrastructure as a Service)
Choose the correct cloud computing service model from the options,
Users access a web-based graphics design application in the cloud for a monthly fee
SaaS (Software as a Service)
Choose the correct cloud computing service model from the options,
A company develops applications using cloud-based resources and tools
PaaS (Platform as a Service)
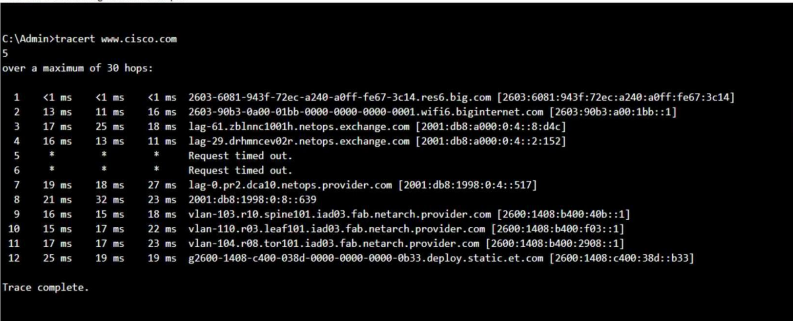
Which two conclusions can you make from the output of the tracert command?
The trace successfully reached the www.cisco.com server, and The IPv6 address associated with the www.cisco.com server is 2600:1408: c400: 38d: : b33.
Which two pieces of information should you include when you initially create a support ticket?
A detailed description of the fault, and A description of the conditions when the fault occurs.
Define the correct network type:
Two home office computers are connected to a switch by Ethernet cables.
LAN (Local Area Network)
Define the correct network type:
Three government buildings in the same city connect to a cable company over coaxial cables.
MAN (Metropolitan Area Network)
Define the correct network type:
A cell phone connects to a Bluetooth headset.
PAN (Personal Area Network)
Define the correct network type:
A financial institution connects its branches through a telecommunications service provider.
WAN (Wide Area Network)
True or False:
A firewall can direct all web traffic to a specific IP address.
True.
True or False:
A firewall can block traffic to specific ports on internal computers.
True.
True or False:
A firewall can prevent specific apps from running on a computer.
False
Which protocol matches the correct TCP/IP layer?
Application layer
FTP (File Transfer Protocol)
Which protocol matches the correct TCP/IP layer?
Transport layer
TCP (Transmission Control Protocol)
Which protocol matches the correct TCP/IP layer?
Internetwork layer
IP (Internet Protocol)
Which protocol matches the correct TCP/IP layer?
Network interface layer
Ethernet
Which address is included in the 192.168.200.0/24 network?
192.168.200.13
Which device protects the network by permitting or denying traffic based on IP address, port number, or application?
Firewall
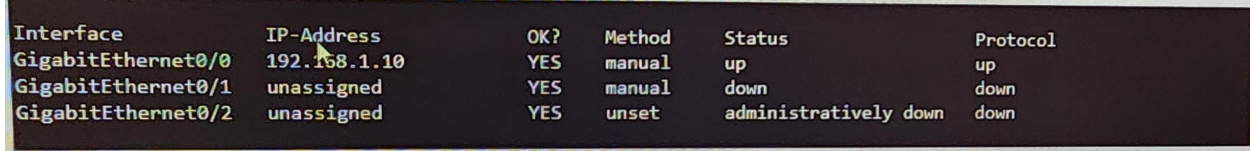
You connect to a cisco switch and run the following command: show ip interface brief, is the below statement true or false according to the partial output?
A device connected to GigabitEthernet0/1 can send out broadcast traffic.
False
You connect to a cisco switch and run the following command: show ip interface brief, is the below statement true or false according to the partial output?
E technician issues the shutdown command on interface GogabitEthernet0/2
True
You plan to use a network firewall to protect computers at a small office. Is this statement about a firewall true or false?
A Firewall can direct web traffic to a specific IP address.
True
You plan to use a network firewall to protect computers at a small office. Is this statement about a firewall true or false?
A firewall can block traffic to specific port on internal computer.
True
You plan to use a network firewall to protect computers at a small office. Is this statement about a firewall true or false?
A firewall can prevent specific apps from running on a computer.
False
Which type of connector should you use to terminate unshielded twisted pair cable?
RJ-45
Which address is a link local IPv6 address?
fe80::261:2eff:fe10:7561
What information is contained in a MAC address table of a Switch?
The MAC addresses of devices communicating on active ports and static MAC addresses configured by the administrator
You need to determine whether a remote host is reachable through the network. Which two commands can you use?
Traceroute or Tracert and Ping
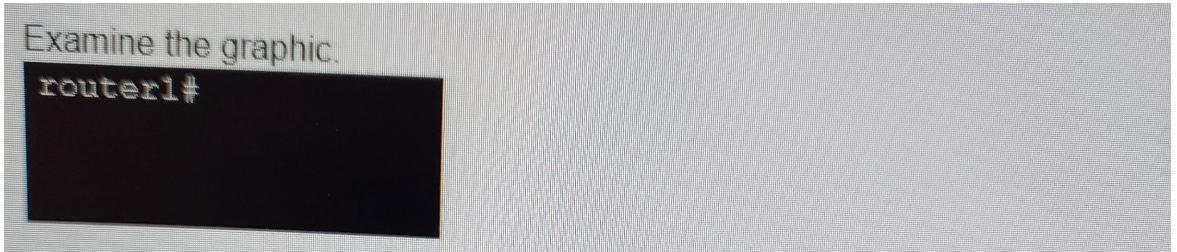
Which action can be run directly from the cisco router’s IOS mode shown?
Show running system information.
Your company has 20 Cisco switches throughout it’s building, you need to view the configuration of each switch from the command line.
What Protocol should you use?
SNMP (Simple Network Management Protocol)
How is the following IP address written when using CIDR notation?
Address: 192.168.0.16, Subnet Mask: 255.255.255.240
192.168.0.16 /28
A network administrator can successfully ping the URL cisco.com, but cannot ping a corporate server located at remote branch in another network. You need to identify the specific router where packets are being dropped in the path.
Which utility (command) should you use?
traceroute
Which statement best describes confidentiality with regards to network security?
Ensures data is kept secret using safeguards to prevent unauthorized access.
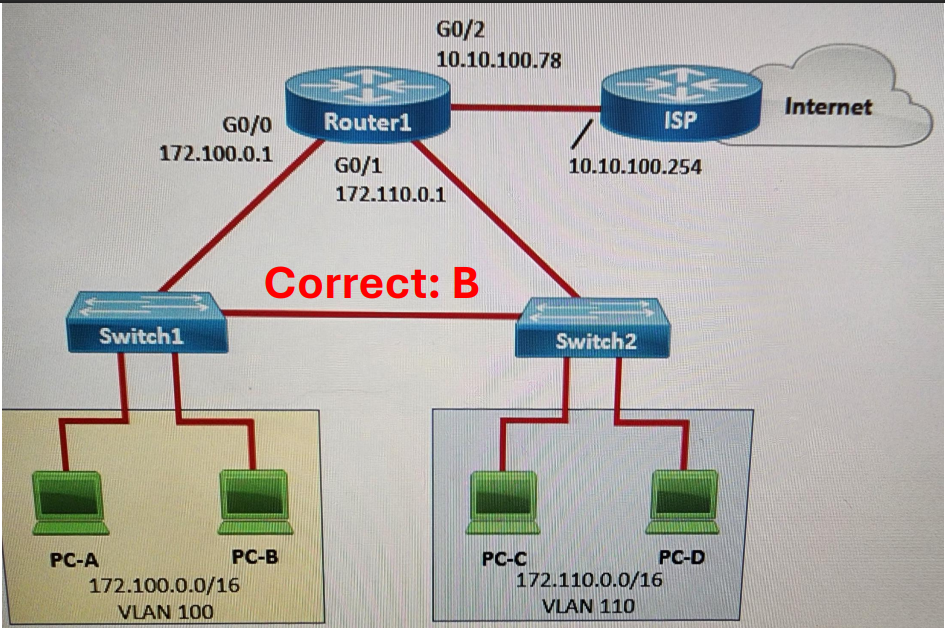
Which address should be assigned as the default gateway to the hosts in VLAN 100 and VLAN 110 so that they can reach the internet?
Hosts in VLAN 100 should be assigned 172.100.0.1 and hosts in VLAN 110 should be assigned 172.110.0.1 as the default gateway.
Which protocol is used by IPV6 enabled hosts to perform automatic stateless address configuration?
DHCPv6 (Dynamic Host Configuration Protocol)
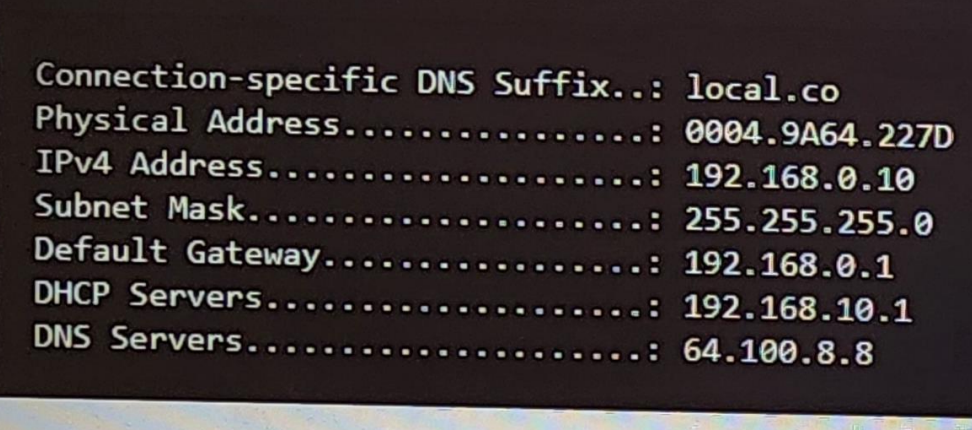
A helpdesk technician is working on a computer that is unable to resolve URLs in the browser. The technician runs the ipconfig /all command and receives the following output.
What is the command that views the network devices in the path from the computer to the server that resolves the hostname?
tracert 64.100.8.8