IDSC Topics 9 and 10
1/60
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
61 Terms
Data harvesters
Cybercriminals who infiltrate systems and collect data for illegal resale.
Cash-out fraudsters
Criminals that purchase assets from data harvesters to be used for illegal financial gain. They might buy goods using stolen credit cards or create false accounts.
Botnets
Hordes of surreptitiously infiltrated computers, controlled remotely.
Distributed Denial of Service (DDos) attacks
An attack where a firm’s computer systems are flooded with thousands of seemingly legitimate requests, the sheer volume of which will slow or shut down the site’s use.
Ransomware Attacks
Criminals infiltrate networks and encrypt an organization’s data.
Holding data assets hostage and irrecoverable unless the organization forks over a ransom in untraceable crypto to receive the decryption key.
Hacktivists
Protester seeking to make a political point by leveraging technology tools, often through system infiltration, defacement, or damage.
Griefers or trolls are malicious pranksters.
And as power and responsibility are concentrated in the hands of a few, revenge-seeking employees can do great damage.
What is cyberwarfare? Relation to corporate espionage? Stuxnet?
Cyberwarfare- the use of computer technology to disrupt the activities of a state or organization, especially the deliberate attacking of information systems for strategic or military purposes.
Corporate espionage- the act of stealing a company's confidential information without authorization for financial or commercial gain. The goal is to gain a competitive advantage over the victim company.
Stuxnet- Notorious cyberwarfare attack that infiltrated Iranian nuclear facilities and reprogrammed their software.
hacker
A term that may be applied to either 1) someone who breaks into a computer, or 2) to a particularly clever programmer.
hack
A term that may be applied to either 1) breaking into a computer system, or 2) to a particularly clever solution.
white hat hackers
Someone who uncovers computer weaknesses without exploiting them. Contributes to improving system security.
black hat hackers
cybercriminals who gain unauthorized access to computer systems and networks with the intent to cause harm
Red Team
Offensive- Attacks the blue teams defenses
When a firm employs a group to act like bad actors in an attempt to uncover weaknesses before they are exploited.
Blue Team
Defensive- defends against Red Team attacks
Defensive security professionals responsible for maintaining internal network defenses against cyberattacks and threats.
Social Engineering
The tactic of manipulating, influencing, or deceiving a victim in order to gain control over a computer system, or to steal personal and financial information. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.
Spear phising vs phising
Spear phising- Phishing attacks that specifically target a given organization or group of users.
Phising- Cons executed using technology, in order to acquire sensitive information or trick someone into installing malicious software.
Spoofed
E-mail transmissions and packets that have been altered to forge or disguise their origin or identity
Zero-day exploits
New attacks that haven’t been clearly identified and haven’t been incorporated into security screening systems.
Cyberattack vector that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. "Zero day" refers to the fact that the software or device vendor has zero days to fix the flaw because malicious actors can already use it to access vulnerable systems.
Deepfakes
Sophisticated media (audio, image, video) created by AI that attempts to look or sound like a real person or event.
Script Kiddies
Pejorative term for an unsophisticated hacker that relies on scripts or downloaded programs to perpetrate hacking, rather than develop original exploits.
Biometrics
Measure and analyze human body characteristics for identification or authentication.
2FA
Two-factor authentication, a type of security that requires two separate forms of identification order to gain access.
Multi-factor authentication
When identity is proven by presenting more than one item for proof of credentials
Malware
Seeks to compromise a computing system without permission.
Methods of infection:
Viruses: Infect other software or files.
Worms: Take advantage of security vulnerability to automatically spread.
Trojans: Attempt to sneak in by masquerading as something they’re not.
Malicious Adware
Installed without full user consent or knowledge, later serve unwanted advertisements.
Spyware
Monitors user actions, network traffic, or scans for files.
Keylogger
Records user keystrokes.
Screen Capture
Records pixels that appear on a user’s screen to identify proprietary information
Card skimmer
Captures data from a card’s magnetic strip.
RAM scraping or storage scanning software
Malicious code that scans for sensitive data.
Ransomware
Malware that encrypts user’s files with demands that a user pay to regain control of their data and/or device.
Blended Threats
Attacks combining multiple malware or hacking exploits.
SQL injection
Technique that targets sloppy programming practices that do not validate user input.
SQL injection and other application weaknesses are particularly problematic because there’s not a commercial software patch or easily deployed piece of security software that can protect a firm.
Push-Button Hacking
tools designed to easily automate attacks.
Encryption
Scrambling data using a code, thereby hiding it from those who do not have the unlocking key.
Key
Code that unlocks encryption.
Brute-force attacks
Exhausts all possible password combinations to break into an account
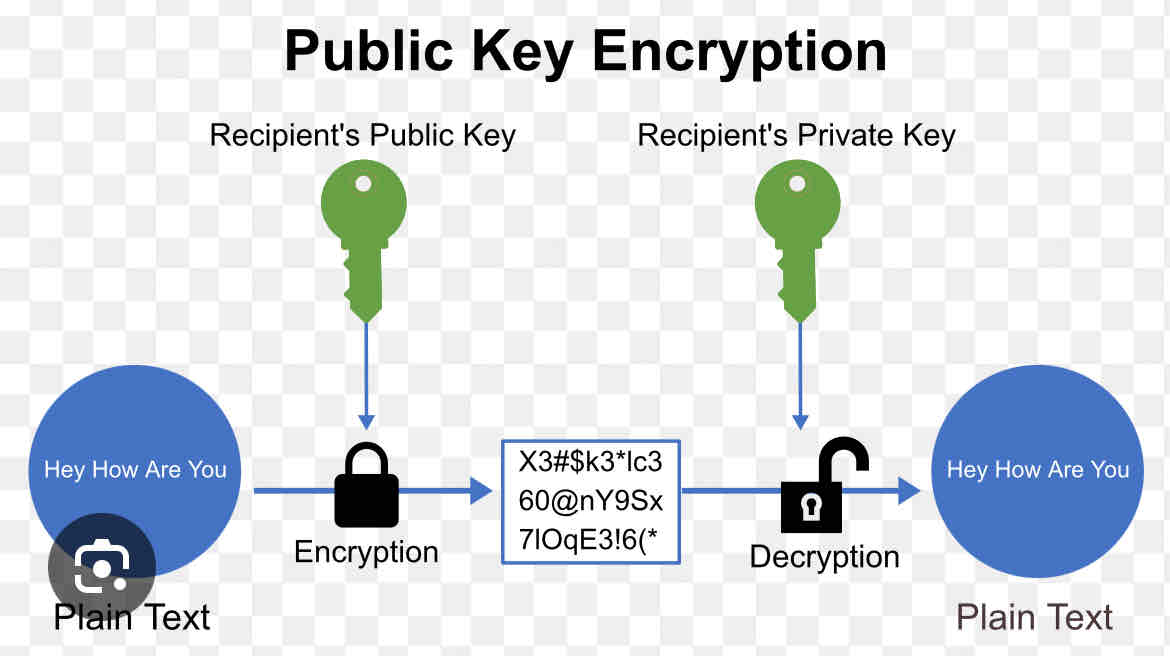
Public Key Encryption
Two key system used for securing electronic transmissions.
Certificate Authority
Trusted third party that provides authentication services in public key encryption schemes.
ISO27k or ISO 27000
ISO- International Organization for Standardation
Series of standards for following frameworks, standards, and compliance .
Series provides “a model for establishing, implementing, operating, monitoring, reviewing, maintaining, and improving an Information Security Management System.”
Firewalls
Control network traffic, block unauthorized traffic.
Intrusion Detection Systems
Monitor network use for hacking attempts and take preventive action.
Honeypots
Tempting, bogus targets meant to lure hackers.
Blacklists
Deny the entry of specific IP addresses and other entities.
Whitelists
Permit communication only with approved entities or in an approved manner.
Single Sign on Tools
An authentication method that enables users to securely authenticate with multiple applications and websites by using just one set of credentials.
Web 2.0
Internet services that foster collaboration and information sharing. Often categorized as social media
Peer Production
Collaboration between users to create content, products, and services.
Leveraged to create open-source software that supports many of the Internet’s largest sites.
Collaborative Consumption
Participants share access to products and services, rather than having ownership
Uber, Airbnb
Social Proof
The positive influence created when someone finds out that others are doing something.
Social Networks
An online community that allows users to establish a personal profile and communicate with others. Large public social networks include Facebook, LinkedIn, Instagram, TikTok, and Pinterest.
4 foundations of the Digital Workplace Ecosystem
Coordination, Project Management, Communication, Content Sharing.
Natural Language Processing
Collaborating with bots or intelligent agents, as not all customer interface will be between just humans.
Visual Collaboration
Communicating about projects through multiple collaboration tools are simplifying this previously complex process
Wisdom of Crowds
Idea that a group of individuals, often consisting of untrained amateurs, will collectively have more insight than a single or small group of trained professionals.
Best selling author, James Surowiecki, states that a crowd must be diverse, decentralized, independent, and offer a collective verdict; to be smart.
Prediction Market
Polling a diverse crowd and aggregating opinions in order to form a forecast of an eventual outcome.
Crowdsourcing
The act of taking a job traditionally performed by a designated agent and outsourcing it to an undefined, generally large group of people in the form of an open call.
Sharing Economy
En economic system in which assets or services are shared between private individuals, either free or for a fee, typically by means of the internet.
Lock Down Hardware
Prevent unapproved software installation.
• Force file saving to hardened, backed-up, and monitored servers.
• Re-image hard drives of end-user PCs.
• Disable boot capability of removable media.
• Prevent Wi-Fi use and require VPN encryption for network
transmissions
Lock Down Networks
Firewalls, Intrusion Detection Systems, Honeypots, Blacklists, Whitelists
Lock Down Systems
• Audit for SQL injection and other application exploits.
• Use access controls to control data access on a need-to-know
basis.
• Use recording, monitoring, and auditing to hunt for patterns of
abuse.
• Maintain multiple administrators to jointly control key systems.
Types of Malware (extended)
Botnets, Malicious Adware, Spyware, Screen Capture, Ram Scraping or storage scanning software, Ransomware, Blended Threats