Pentest Practice Exam 1
1/79
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
80 Terms
You have been asked to perform a penetration test for a mediumsized organization that sells after-market motorcycle parts online.
What is the first task you should complete?
A. Research the organization's product offerings.
B. Determine the budget available for the test.
C. Identify the scope of the test.
D. Gain authorization to perform the test.
C. The first step in the penetration testing process is to work with the client to clearly define the scope of the test. The scope determines what penetration testers will do and how their time will be spent. Researching the organization's products is a task that will probably be done after the scope of work has been defined. Determining the budget and gaining authorization are subtasks that are usually completed as a part of the overall scoping process.
A consultant has been hired to perform a penetration test for an
organization. The target of the test is the organization's proprietary
design documents. The aim is to circumvent security measures and
gain unauthorized access to these documents. What type of
assessment is being conducted in this scenario?
A. Objective-based assessment
B. Goal-based assessment
C. Compliance-based assessment
D. Red team assessment
D. Red team assessments are typically more targeted than normal penetration tests. The red team acts like an attacker, targeting sensitive data or systems with the goal of acquiring access. Goalbased or objective-based assessments are usually designed to assess the overallsecurity of an organization. Compliance-based assessments are designed to test compliance with specific laws.
A consultant has been hired to perform a penetration test for an
organization in the healthcare industry. The target of the test is a
public-facing self-service website that users can access to view their
health records. The aim is to circumvent security measures and gain
unauthorized access to this information. What type of assessment is
being conducted in this scenario?
A. Objective-based assessment
B. Gray box assessment
C. Compliance-based assessment
D. White box assessment
C. Because patient records are protected by the HIPPA law in the United States, this is an example of a compliance assessment. Compliance-based assessments are designed to test compliance with specific laws. Objective-based assessments are usually designed to assess the overall security of an organization. Gray box and white box assessments identify the level of knowledge the attacker has of the organization.
A consultant has been hired to perform a penetration test for an
organization in the healthcare industry. The target of the test is a
public-facing self-service website that users can access to view their
health records. The penetration tester has been given full knowledge
of the organization's underlying network. What type of test is being
conducted in this example?
A. Goal-based assessment
B. Black box assessment
C. Objective-based assessment
D. White box assessment
D. A white box test is performed with full knowledge of the
underlying technology, configuration, and settings of the target organization's network. In a black box test, the testers are not provided with access to or information about the target environment. Goalsbased or objective-based assessments are usually designed to assess the overall security of an organization.
In which type of penetration test does the tester have a limited
amount of information about the target environment but is not
granted full access?
A. Gray box assessment
B. Black box assessment
C. Compliance-based assessment
D. White box assessment
A. A gray box test may provide some information about the
environment to the penetration testers without giving full access, credentials, or configuration details. A white box test is performed with full knowledge of the underlying network. In a black box test, the testers are not provided with access to or information about the target environment. Compliancebased assessments are designed to test
compliance with specific laws.
You have been asked to perform a black box penetration test for a
medium-sized organization that sells imported motorcycles and
ATVs online. In which phase of this assessment will you likely spend
most of your time?
A. Planning and scoping
B. Information gathering and vulnerability identification
C. Attacking and exploiting
D. Reporting and communicating results
B. A black box penetration test is called for in this scenario, so you will likely spend most of your time in the information gathering and vulnerability identification phase of the assessment. This is because, by definition, you should have little or no knowledge of the organization or its network prior to running the test.
You are performing a black box penetration test for a mediumsized organization that sells imported motorcycles and ATVs through
its online storefront. You need to discover who owns the
organization's domain. Which tool in your penetration testing toolkit
should you use?
A. nslookup
B. whois
C. Shodan
D. Maltego
B. The whois command can be used to gather information from public records about who owns a particular domain.
You are performing a black box penetration test for a mediumsized organization that sells imported clothing through its online
storefront. You need to discover which IP addresses are associated
with the organization's domain. Which tool in your penetration testing
toolkit should you use?
A. nslookup
B. whois
C. theHarvester
D. Fingerprinting Organizations with Collected Archives (FOCA)
A. The nslookup command is included with most operating
systems, including Windows and Linux, and can be used to resolve an organization's domain name into its associated IP addresses.
You are performing a black box penetration test for a mediumsized organization that sells imported clothing through its online
storefront. You want to query search engines and other resources to
discover email addresses, employee names, and other details about
the target. Which tool in your penetration testing toolkit should you
use?
A. nmap
B. Shodan
C. theHarvester
D. Fingerprinting Organizations with Collected Archives (FOCA)
C. theHarvester is a tool available on some Linux distributions, such as Kali Linux, that can be used to query search engines to discover email addresses, employee names, and other details about the target organization.
You are performing a black box penetration test for a large
organization that wholesales imported electronic devices in the
United States. You need to uncover any information you can find
about the organization using open source intelligence (OSINT).
Which tool in your penetration testing toolkit could you use to do
this?
A. Censys
B. whois
C. recon-ng
D. Shodan
E. All of the above
E. The recon-ng utility provides a web reconnaissance
framework that allows you to conduct open source reconnaissance about an organization on the Web. Censys is a webbased tool that probes a given IP address. The whois command can be used to gather information from public records about who owns a particular domain. Shodan is a specialized tool that a penetration tester can use to search public sources for evidence of an Internet of Things
(IoT) device that a target organization may have deployed in their network.
You are conducting a black box penetration test for a client. You
have used reconnaissance tools to create a list of employee email
addresses within the target organization. You craft an email
addressed to all of the employees warning them that they must
change their password within 24 hours or they will lose access.
When they click the link provided in the email, they are redirected to
your own website where their credentials are captured to a text file.
What kind of exploit did you use?
A. Phishing
B. Vishing
C. Smishing
D. Whaling
A. A phishing attack was used in this scenario because the
malicious email was sent indiscriminately to all the employees within the organization.
You are performing a gray box penetration test for a mediumsized organization. You have used reconnaissance techniques to
identify a help desk employee and a payroll employee. You craft an
email to the payroll employee that appears to come from the help
desk employee directing the payroll employee to reset her password.
When she clicks the link provided in the email, she is redirected to
your own website where her credentials are captured to a text file.
What kind of exploit did you use?
A. Phishing
B. Interrogation
C. Spear phishing
D. Whaling
C. A spear phishing attack was used in this scenario because the malicious email was specifically crafted for a specific employee. A generic phishing attack, on the other hand, would have been sent indiscriminately to a large group of employees within the organization.
You are performing a black box penetration test for a mediumsized organization. You have used reconnaissance techniques to
identify the CEO's email address as well as the email address
belonging to a help desk employee. You craft an email to the CEO
that appears to come from the help desk employee directing the
CEO to reset her password. When she clicks the link provided in the
email, she is redirected to your own website where her credentials
are captured to a text file. What kind of exploit did you use?
A. Smishing
B. Vishing
C. Spear phishing
D. Whaling
D. A whaling attack is essentially a form of spear phishing attack that is aimed specifically at C-suite employees, such as the CEO, CFO, COO, CIO, and so on. A standard spear phishing attack, on the other hand, would have been sent to a lower-level employee within the organization.
You are performing a black box penetration test for a mediumsized organization that sells imported clothing. You have used
reconnaissance techniques to identify a key software developer. You
send this employee a personalized text message containing a Bitly
URL that points to your own website where you capture information
to a text file.
What kind of exploit did you use in this scenario?
A. Phishing
B. Smishing
C. Vishing
D. Whaling
B. A SMS phishing attack (also called a smishing attack) was
used in this scenario. A smishing attack leverages text messaging instead of email to conduct a phishing exploit.
You are performing a black box penetration test for a small
organization that wholesales imported electronic devices in the
United States. You have used reconnaissance techniques to identify
a receptionist's phone number as well as the organization's printer
vendor. You call this receptionist, pretending to be a sales rep from
the vendor. You ask the receptionist for information about their
printers, workstations, operating systems, and so on, to learn more
about the organization's network infrastructure. What kind of exploit
did you use in this scenario?
A. Smishing
B. Vishing
C. Spear phishing
D. Whaling
B. A voice phishing attack (also called a vishing attack) was used in this scenario. A vishing attack leverages a telephone call instead of email to conduct a phishing exploit. Essentially, the attacker callsa particular employee pretending to be someone else in order to get information.
You are conducting a gray box penetration test for a client. You
have identified an internal host with an IP address of 192.168.1.1 as
a potential target. You need to use the nmap utility on your laptop to
run a SYN port scan of this host. Which command should you use to
do this?
A. nmap 192.168.1.1 -sS
B. nmap 192.168.1.1 -sT
C. nmap 192.168.1.1 -sU
D. nmap 192.168.1.1 -sA
A. The -sS option causes the nmap utility to conduct a SYN port scan of the specified target system.
You are conducting a white box penetration test for a client. You
need to use the nmap utility on your laptop to run a scan of every
host on the 192.168.1.0 subnet (which uses a subnet mask of
255.255.255.0). Which commands could you use to do this?
(Choose two.)
A. nmap 192.168.1.0
B. nmap 192.168.1.0-255
C. nmap 192.168.1.0 -m:255.255.255.0
D. nmap 192.168.1.0/24
E. nmap 192.168.1.1-254
D and E. The nmap 192.168.1.0/24 command causes the nmap
utility to scan every system on the subnet, from .1 to .254. Likewise, the nmap 192.168.1.1-254 command causes the nmap utility to scan every system on the subnet, from .1 to .254.
You are conducting a gray box penetration test for a client. You
have identified an internal host with an IP address of 192.168.1.1 as
a potential target. You need to use the nmap utility on your laptop torun a SYN port scan of this host. Which commands could you use to
do this? (Choose two.)
A. nmap 192.168.1.1 -sS
B. nmap 192.168.1.1
C. nmap 192.168.1.1 -sV
D. nmap 192.168.1.1 -O
E. nmap 192.168.1.1 -T0
A and B. The nmap 192.168.1.1 -sS command causes the nmap
utility to conduct a SYN port scan of the specified target system. Likewise, the nmap 192.168.1.1 command also causes the nmap utility to conduct a SYN port scan of the specified target system because a SYN scan is the default used if no other scan type is specified.
You are conducting a gray box penetration test for a client. You
have identified an internal host with an IP address of 192.168.1.1 as
a potential target. You need to use the nmap utility on your laptop to
determine the operating system running on this host. Which
command should you use to do this?
A. nmap 192.168.1.1 -sS
B. nmap 192.168.1.1 -sL
C. nmap 192.168.1.1 -sV
D. nmap 192.168.1.1 -O
D. The nmap 192.168.1.1 -O command causes the nmap utility
to use TCP/IP stack fingerprinting to determine the operating system installed on the remote host.
You are conducting a gray box penetration test for a client. You
have identified an internal host with an IP address of 192.168.1.1 as
a potential target. You need to use the nmap utility on your laptop to
determine the operating system running on this host. Which
command could you use to do this?
A. nmap 192.168.1.1 -A
B. nmap 192.168.1.1 -T1
C. nmap 192.168.1.1 -sT
D. nmap 192.168.1.1 -f
A. The nmap 192.168.1.1 -A command enables OS detection,
service version detection, script scanning, and traceroute to the remote host.
You have just completed a penetration test for a client. During
the test, you used a variety of different tools to collect data and
conduct exploits. Now you need to aggregate all of the data
generated by these tools into a format that is consistent, correlated,
and readable. What is this process called?
A. Attestation of findings
B. Normalization of data
C. De-escalation
D. De-confliction
B. When you normalize the data from a penetration test, you
aggregate all the data generated by all of the different tools and processes you used during the test and format it such that it is consistent and correlated. The goal is to make it such that the client can read the aggregated data and understand what happened during the test and when.
You have just completed a penetration test for a client and are
now creating a written report of your findings. You need to make sure
the reader understands that you followed the PCI DSS standard
while conducting the test. In which part of the report should you
include this information?
A. Findings
B. Remediation
C. Metrics and Measures
D. Methodology
D. The final report you write for a penetration test should include a section entitled Methodology. In this section, you describe the penetration testing methodology you used to conduct the test. In this scenario, this would be the appropriate place to indicate that the PCI DSS standard was followed to conduct the test.
One of the goals of communication between the tester and the
client during a penetration test is to ensure that both parties clearly
understand the current security state of the network. Which of the
following terms best describes this shared understanding?
A. Situational awareness
B. De-escalation
C. De-confliction
D. Goal reprioritization
A. Among other things, the term situational awareness refers to a state of shared understanding between the client and the tester regarding the security posture of the client's network.
During a penetration test, the client organization's network
administrator discovers a distributed denial of service (DDoS) attack
underway that is aimed at the company's web server. The
administrator calls the penetration tester to verify that the attack is
part of the penetration test and not coming from a real attacker. What
is this process called?
A. Normalization of data
B. Situational awareness
C. De-confliction
D. Goal reprioritization
C. The term de-confliction refers to the process of
communicating between the client and the tester to determine whether an attack detected during a penetration test is coming from an authorized penetration tester or whether it is a real attack instigated by some third-party hacker.
During a penetration test, the client organization begins to
receive complaints from customers indicating that the organization's
web server is very slow to respond or even crashes at times. The
network administrator discovers a distributed denial of service
(DDoS) attack underway that is aimed at the company's web server.
Sales are being lost, so the administrator calls the penetration tester
and asks them to stop the attack. What is this communication path
called?
A. Situational awareness
B. De-escalation
C. De-confliction
D. Goal reprioritization
B. The term de-escalation refers to the process of
communicating between the client and the tester to cease exploits used during the penetration test because of the adverse effects they may be having on the network.
An organization's network was recently hacked. The attackers
first compromised the weak security used by one of the
organization's contractors. Then they used the contractor's
authentication credentials to gain access to the organization itself.
Which type of penetration assessment could have prevented this?
A. Objective-based
B. Pre-merger
C. Goal-based
D. Supply chain
D. In a supply chain assessment, a penetration test is conducted on an organization's vendors to ensure their networks are secure and can't be used as a pivot point to compromise the organization itself. A goal-based assessment is designed to test a specific aspect of an organization's security. A premerger test is usually conducted on an organization prior to it merging with another.
You work on the security team for a large organization. Your
team has been tasked with conducting an internal penetration test to
verify whether your organization's IT staff can adequately defend
against it. What type of assessment is being used in this scenario?
A. Goal-based
B. Compliance-based
C. Supply chain
D. Red team
D. A red team assessment is usually conducted by internal
testers to ensure an organization's IT staff (the blue team) can adequately defend the network. A goal-based assessment is designed to test a specific aspect of an organization's security. A supply chain test involves testing an organization's vendors. A compliance-based test is performed to ensure that an organization remains in compliance with governmental regulations or corporate
policies.
Which of the following tiers of adversaries ranks threat actors,
generally speaking, from least threatening to most threatening?
A. Script kiddie, hacktivist, malicious insider, organized crime, nationstate
B. Script kiddie, malicious insider, hacktivist, organized crime, nationstate
C. Hacktivist, script kiddie, malicious insider, nation-state, organized
crime
D. Nation-state, organized crime, malicious insider, hacktivist, script
kiddie
A. Generally speaking, if you were to rank threat actors into tiers from least threatening to most threatening, it would look something like the following: script kiddie > hacktivist > malicious insider > organized crime > nation-state.
One of your clients is a public advocacy group. Some of its
political stances are very unpopular with several fringe activists, and
they are concerned that a hacktivist may try to hijack their publicfacing website. They have asked you to run a penetration test usingthe same tools and techniques that a typical hacktivist would have
the technical aptitude and funds to use. What process has occurred
in this scenario?
A. Due diligence
B. Risk acceptance
C. Threat modeling
D. Scope creep
C. This is an example of threat modeling. Using threat modeling, you determine the type of threat you want to emulate during thepenetration test. Then you use the same tools, techniques, and approaches that type of threat would typically use.
You are meeting with a new client to scope out the parameters of
a future penetration test. During the course of the discussion, you
ask the client if they are willing to accept the fact that a penetration
test could cause service disruptions within their organization. The
client responds affirmatively. What process has occurred in this
scenario?
A. Risk acceptance
B. Due diligence
C. Threat modeling
D. Risk transfer
A. This is an example of risk acceptance. You have evaluated
the client's tolerance of the impacts a penetration test could bring to the organization. It is important that the client be ready and able to accept the fact that a penetration test could cause a network outage or a service disruption.
As the part of information gathering process during a gray box
penetration test, you need to perform a certificate inspection on the
target organization's internal web server. Which utility could you use
on your Kali Linux laptop to do this?
A. sslyze
B. Zenmap
C. nmap
D. hping
A. The sslyze tool is a penetration testing tool that is commonly used to perform certificate inspection.
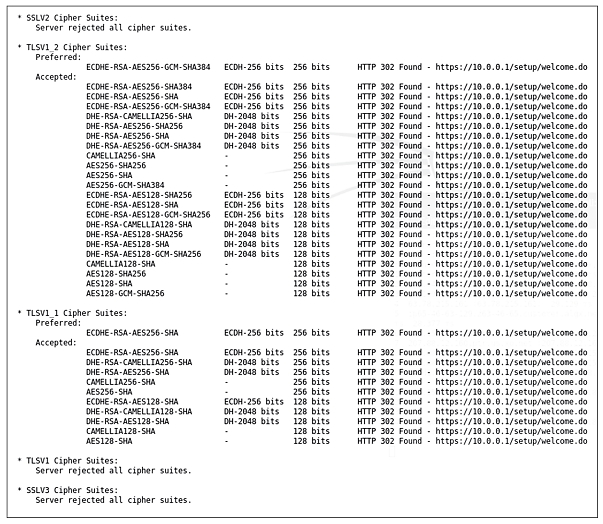
During a gray box penetration test, you have used a utility on
your Kali Linux laptop to inspect the certificate used by the target
organization's internal web server. The output is shown here:What can you learn from this output? (Choose two.)
A. SSLv2 is supported by the web server.
B. TLSv1_1 is supported by the web server.
C. TLSv1_2 is supported by the web server.
D. TLSv1 is supported by the web server.
E. SSLv3 is supported by the web server.
B and C. The output of the sslyze command in this example
shows that the web server responded to TLSv1.1 and TLSv1.2
queries but did not respond to SSLv2, SSLv3, or TLSv1 queries.
You need to capture packets on a wired network during the
information gathering phase of a gray box penetration test. Which
utilities could you use on your laptop to accomplish this? (Choose
two.)
A. tcpdump
B. nmap
C. WiresharkD. Zenmap
E. aircrack-ng
A and C. You can use either tcpdump or Wireshark to capture packets on a wired network. Of the two, Wireshark is usually considered to have the most user-friendly interface.
During the information gathering phase of a black box
penetration test, you need to eavesdrop on radio frequency
emissions emanating from the target's facility and attempt to capture
data from their wireless network. Before you can do this, you must
break the encryption used on the Wi-Fi network. You are parked in
the organization's parking lot. Which utility could you use on your
Linux laptop to do this?
A. aircrack-ng
B. tcpdump
C. Wireshark
D. nmap
A. The Aircrack-ng utility can be used to discover wireless
networks in range and then crack their encryption. This process is very fast for old WEP networks, harder but doable for WPA networks, and quite challenging for WPA2 networks.
During the information gathering phase of a black box
penetration test, you need to eavesdrop on radio frequency
emissions emanating from the target's facility and attempt to capture
data from its wireless network. You are parked in the organization's
parking lot. How must the wireless network interface in your laptop
be configured to do this?
A. Set to monitor mode.
B. Set to promiscuous mode.
C. Set to capture mode.
D. Set to IEEE 802.1x mode.
A. Before a wireless network interface can be used to capture wireless network traffic, it must be configured to run in monitor mode on the specific channel used by the transmitting access point.
A penetration tester impersonates a heating and cooling repair
person to gain physical access to the target organization's facility.
Once inside, she requests access to the server room to investigate a
problem with the cold air return. As she is leaving the server room,
she surreptitiously places a small wooden wedge into the door jam,
preventing the door from closing completely. This allows her to return
into the room later without authorization. What is this technique
called?
A. Lock picking
B. Lock bypass
C. Fence jumping
D. Badge cloning
B. Lock bypass occurs when an attacker prevents a door's
locking mechanism from working. In this example, this was done by placing a wooden wedge in the door jamb, preventing the door from closing completely and preventing the locking mechanism from
engaging.
Which of the following features of an egress sensor can be
manipulated to allow a penetration tester to enter a building without
authorization?
A. Emergency fail open
B. Automatic locking
C. Automatic unlocking via motion sensor for egress
D. Automatic unlocking via light sensor for egress
A. Most automatically locking door systems have some type of emergency fail open mechanism. The idea behind this is that if there is an emergency of some sort, such as a fire, then the doors must automatically unlock to prevent people from being trapped inside or preventing emergency personnel from entering. If you can figure outwhat fail open mechanism is used, you may be able to manually
trigger it to open a locked door.
A penetration tester rummages through the target organization's
garbage and finds a discarded access badge. She replicates a new
badge with her picture using the discarded badge as a model. She
uses a device to read the discarded badge's magnetic stripe and
replicate it on the fake badge. Which techniques were used by the
tester in this scenario?
(Choose two.)
A. Lock picking
B. Dumpster diving
C. Fence jumping
D. Badge cloning
E. Lock bypass
B and D. In this scenario, dumpster diving was used to find the discarded access badge. Then badge cloning was used to create a fake badge.
Using reconnaissance, a penetration tester learns that the target
organization's employees use RFID access badges to unlock doors
within the facility. Using the company's website, he identifies highlevel employees within the organization. Then he waits in the parking
lot until he sees one of these individuals heading toward the front
doors. He walks behind them into the reception area with a small
RFID reader hidden in his coat. He captures the RFID signature from
the individual's badge and then creates his own fake access badge
and encodes it with that RFID signature. What is this technique
called?
A. Piggybacking
B. Tailgating
C. Lock bypass
D. Badge cloning
D. Badge cloning occurs when an attacker makes a copy of a
valid access badge to enter a facility. By copying a valid badge's RFID signature, the penetration tester in this scenario can use the fake badge to access the target organization's facility using the authorized employee's credentials. Because he carefully selected a high-level employee's badge for cloning, he may be able to access
more sensitive areas of the facility.
A penetration tester is performing a gray box test for a client.
During a network scan, she notices a host that has TCP port 139open. She suspects this is a Windows system, so she runs the NBTSTAT command and discovers key information about the host. Which protocol on the remote host allowed the tester to gather this information?
A. NetBIOS
B. SNMP
C. NAC
D. SMTP
A. NetBIOS is a transport protocol used by Windows systems to share resources, such as shared folders or printers. Once an attacker identifies that port 139 is open on a device, NBTSTAT can be used to footprint the device. For example, you could discover the device's computer name and identify whether it is a workstation or a server. All of this information can be gathered without any kind of authentication.
As a part of a penetration test, you need to perform
reconnaissance on the target organization to passively gather
information. Which tools could you use to do this? (Choose two.)
A. whois
B. Metasploit Framework
C. OpenVAS
D. nslookup
E. Nessus
A and D. The whois and nslookup utilities can be used to
passively conduct reconnaissance on the target organization. Because they report information that is available to the general public, using these tools is highly unlikely to arouse any suspicion.
As a part of a penetration test, you need to establish an active
connection to the computer systems and devices at the target
organization to enumerate and fingerprint them. Which tools could
you use to do this? (Choose two.)
A. whois
B. nmap
C. hping
D. Aircrack-ng
E. John the Ripper
B and C. The nmap and hping utilities can be used to actively enumerate and fingerprint target systems.
As a part of a penetration test, you need to gather user account
names and passwords from the passwd and shadow files from a
Linux server. Which utilities could you use to do this? (Choose two.)
A. John the Ripper
B. Cain and Abel
C. Kismet
D. Censys
E. Recon-ng
A and B. John the Ripper as well as Cain and Abel can be used to crack passwords from an offline database of user accounts, such as the shadow and passwd files from a Linux system.
As a part of a penetration test, you need to perform an in-depth
scan of a target to identify vulnerabilities, such as missing updates ormisconfigured security settings. Which utilities could you use to do
this?
A. Censys
B. theHarvester
C. Shodan
D. OWASP ZAP
E. Nessus
D and E. OWASP ZAP as well as Nessus can be used to scan a target for vulnerabilities.
A penetration tester is performing a gray box test for a client. The
tester decides to run a brute-force attack against a SQL database.
Which utility could be used to do this?
A. John the Ripper
B. SQLmap
C. WiFite
D. Nikto
B. SQLmap can be used to brute-force crack the password for an SQL database.
You have just concluded a penetration test for a client. The client
has more than 2,000 employees, but only two of them are network
administrators. During the test, you were able to quickly overwhelm
them with the sheer volume of your attacks. To address this
vulnerability, you recommend that the client hire additional network
administrators who have cybersecurity credentials and experience.
What type of solution is this?
A. Technological
B. People
C. Process
D. Scalable
B. Hiring additional IT staff members who have experience with cyber security is an example of a people-based mitigation strategy.
You have just concluded a penetration test for a client. During
the test, you discovered that the organization's employees made
extensive use of a shared Google Drive account to collaborate. You
were able to use a social engineering exploit to get access to the
shared account and access sensitive files. To address this
vulnerability, you recommend that the client disallow this practice
among employees. What type of solution is this?
A. Technological
B. People
C. Process
D. Scalable
C. Forbidding employees from using external cloud-based
services such as Google Drive is an example of a process-based mitigation strategy.
You have just concluded a penetration test for a client. During
the test, you were able to gain access to the client's physical facility
by tailgating with a group of employees. To address this vulnerability,
you recommend that the client implement a man-trap locking door at
the entrance to the facility. What type of solution is this?
A. Technological
B. People
C. Process
D. Scalable
A. Implementing a mantrap at the main entrance is an example of a technological mitigation strategy.
You have just concluded a penetration test for a client. During
the test, you were able to gain access to the client's wireless network
using Aircrack-ng while sitting in your car in a parking lot across the
street. To address this vulnerability, you recommend that the client
implement directional wireless network antennas and also
manipulate the power level of the access points to prevent signal
emanation. What type of solution is this?
A. Technological
B. People
C. Process
D. Scalable
A. Implementing directional wireless antennas and manipulating access point power levels to prevent signal emanation are examples of technological mitigation strategies.
You have just concluded a penetration test for a client. During
the test, you were able to use social engineering to convince the
organization's accounts payable clerk to send a large ACH payment
to a fictitious bank account. To address this vulnerability, you
recommend that the client implement division of duties such that two
individuals must sign off on all payouts. What type of solution is this?
A. Technological
B. People
C. Process
D. Scalable
C. Requiring multiple sign-offs on payouts is an example of a process-based mitigation strategy.
You are the CIO for a mid-sized corporation. You are putting
together a plan to implement regular penetration tests and are
considering using an internal penetration testing team consisting ofyour own employees. Which of the following are benefits of using an
internal team? (Choose two.)
A. They have contextual knowledge of the organization.
B. They are less biased than an external contractor.
C. They have the independence required to perform a thorough test.
D. They have in-depth experience performing penetration tests for
many organizations.
E. It's usually less expensive than using an external contractor.
A and E . There are two major benefits of using internal teams to conduct penetration tests. First, they have contextual knowledge of the organization that can improve the effectiveness of the tests. Second, it's usually less expensive to conduct testing using internal employees than it is to hire a penetration testing contractor. When the internal staff isn't involved in a penetration test, they can work on other projects for the organization.
You are the CIO for a mid-sized corporation. You are putting
together a plan to implement regular penetration tests and are
considering using an external penetration testing contractor. Which
of the following are benefits of using an external team? (Choose
two.)
A. They have contextual knowledge of the organization.
B. They are less biased than an internal team.
C. They have the independence required to perform a thorough test.
D. They are intimately familiar with the security controls within the
organization.
E. It's usually less expensive than using an internal team.
B and C. External penetration testing teams are hired for the
express purpose of performing penetration tests. Because they aren't directly employed by the organization, they tend to have a higher degree of independence. They don't have to worry about upsetting a manager or director if vulnerabilities are discovered. In fact, they usually delight in such an event. Also, they tend to be less biased because they don't participate in the design or ongoing
maintenance of the organization's network infrastructure.
You are the CIO for a mid-sized corporation. You are putting
together a plan to implement regular penetration tests and are
considering using an internal penetration testing team consisting of
your own employees. Which of the following are disadvantages of
using an internal team? (Choose two.)
A. Maintaining an internal team is very expensive.
B. There is a potential conflict of interest if they also perform testing
for one of your competitors.
C. They may feel that a vulnerability discovered may reflect poorly
on them.
D. They may lack objectivity.
C and D. An internal penetration testing team may be too closely affiliated with the organization. For example, they may worry that a vulnerability discovered during a penetration test may reflect poorly on their team because they likely designed and continue to maintain the network being tested. This could cause a lack of objectivity when
conducting penetration tests.
You are the CIO for a mid-sized corporation. You are putting
together a plan to implement regular penetration tests and are
considering using an external penetration testing contractor. Which
of the following are disadvantages of using an external team?
(Choose two.)
A. There is a potential conflict of interest if they also perform testing
for one of your competitors.
B. They lack the technical talent of an internal team.
C. They are usually more expensive than an internal team.
D. They may bring their personal biases into the test.
A and C. Using an external team of contractors to perform
penetration testing has several drawbacks that should be
considered. First, there could be a potential for a conflict of interest if they also perform penetration testing for one of your competitors. Second, they tend to be quite expensive.
Which of the following best describes the term the hacker's
mindset within the context of penetration testing?
A. A penetration tester must adopt a defensive mind-set, trying to
protect against all threats.
B. A penetration tester must think like a security professional,
assessing the strength and value of every security control in use.
C. A penetration tester must think like an adversary who might attack
the system in the real world.
D. A penetration tester must think like a military leader, organizing an
open attack on many fronts by many attackers.
C. Penetration testers must take a different approach in their
thinking. Instead of trying to defend against all possible threats, they only need to find a single vulnerability that they can exploit to achieve their goals. To find these vulnerabilities, they must think like an adversary who might attack the system in the real world. This approach is commonly known as adopting the hacker mind-set.
You are performing a gray box penetration test. You need to run
a vulnerability scan on a fragile internal server system? How should
you configure the scan?
A. Use the -T5 option with the nmap command.
B. Use the -T3 option with the nmap command.
C. Use the -T2 option with the nmap command.
D. Use the -T0 option with the nmap command.
C. Because the server is considered a fragile system, you should throttle the bandwidth used by the vulnerability scan. If you don't, you could easily consume all the server's resources with the scan and not leave any for critical business operations. You can use the - Tn option with the nmap command to throttle down the scans. In this
scenario, you should consider using either the -T2 or possibly even the -T1 option with the nmap command. The -T0 option would probably throttle the scan too much, making it take an inordinate amount of time to complete.
Which of the following are issues you may need to consider
when performing a vulnerability scan within an organization that runs
network applications within containers? (Choose two.)
A. Applications running within a container environment may not be
detectable by traditional vulnerability scans.
B. Container hosts may slow down vulnerability scans.
C. Scanning a container host may crash applications running within
its containers.
D. Scanning a container host may cause it to crash, taking critical
network applications offline.
E. Vulnerabilities associated with the base operating system of the
container host may be inherited by its containers.
A and E. A container can be used to create an isolated
environment, much like a virtual machine. As a result, any
applications running within a container environment may not be detectable by traditional vulnerability scans. Unlike a virtual machine, a container shares much of the base operating system with the container host. Therefore, vulnerabilities associated with the base operating system of the container host may be inherited by its containers.
Which of the following application scanning techniques is
performed by reviewing an application's source code?
A. Static code analysis
B. Dynamic code analysis
C. Fuzzing
D. None of the above
A. Static code analysis is conducted by analyzing an
application's source code. Obviously, this type of testing is usually performed only during a white box penetration test. Static code analysis does not involve actually running the program. Instead, it is focused on analyzing how the application is written.
Which of the following application scanning techniques are
performed on running applications? (Choose two.)
A. Static code analysis
B. Dynamic code analysis
C. Fuzzing
D. Source code analysis
B and C. Dynamic code analysis as well as fuzz testing are both performed on running code. Because the source code is not required to perform these tests, they can be performed during gray box or black box penetration tests.
Which of the following application scanning techniques is
performed by sending random, unexpected, or invalid data to the
inputs of an application to see how it responds?
A. Static code analysis
B. Fuzzing
C. Source code analysis
D. None of the above
B. Fuzz testing involves sending random, unexpected, or invalid data to the inputs of an application to test how it handles that data. This is called exception handling. Many attacks can be deployed that exploit an application's inability to properly handle unexpected data.
A penetration tester impersonates a vending machine repair
person to gain access to the target organization's facility. While
inside, the tester hides a wireless device behind a vending machine
that captures the organization's wireless network radio signal and
rebroadcasts it with high gain towards the parking lot. Which wireless
exploit did the tester employ in this scenario?
A. Karma attack
B. Repeating attack
C. Downgrade attack
D. Jamming attack
B. In a repeating attack, the penetration tester captures the
target organization's wireless network radio signal and rebroadcasts it with high gain to extend its range. In this scenario, the organization's wireless network can now be accessed by the penetration tester from the parking lot.
A penetration tester is searching for vulnerabilities within a web
application used by the target organization. In the login page, she
enters the following string of text in the Password field:
UNION SELECT Username, Password FROM Users;
What type of exploit is being used in this example?
A. SQL injection
B. HTML injection
C. Command injection
D. Code injection
A. This is an example of a SQL injection attack. Instead of
entering a password into the Password field, the tester inserts a SQL statement. If the web application in this example was poorly written, then it is possible that it would pull usernames and passwords for every user in the hypothetical database. The UNION SELECT statement is used to combine two unrelated SELECT queries to
retrieve data from different database tables. A wellwritten application will use input validation to prevent SQL statements from being submitted within a user form. The same principles apply to HTML injection, command injection, and code injection attacks.
A penetration tester reviews social media accounts owned by the
target organization's CIO and makes a list of possible passwords
such as her spouse's name, pet's name, favorite sports teams, and
so on. The tester tries to log on to the CIO's account using one
possible password after another, trying to find one that works. What
type of authentication exploit is this?
A. Credential brute-forcing
B. Session hijacking
C. Redirect attack
D. Password cracking
A. This is an example of a credential brute-forcing attack. In a true brute-force attack, all possible letter, number, and special character combinations would be tried one after another until the right one is found. However, by creating a list of likely passwords based on the user's personal interests, the probability of success is greatly increased.
During a gray box penetration test, the tester uses Wireshark to
sniff the network traffic between an employee's web browser and a
website and is able to capture the session cookie. The tester is then
able to impersonate the victim without capturing the user's actual
authentication credentials. What type of authentication exploit was
used in this scenario?
A. Kerberos exploit
B. Session hijacking
C. Redirect attack
D. Password cracking
B. This is an example of session hijacking. The tester was able
to exploit the session key (the cookie) to gain access to the user's session. This type of exploit can be used for web applications where an HTTP cookie is used to maintain a session. Even though the site may have used TLS/SSL to encrypt authentication credentials, thesession cookie is many times not encrypted. If it is captured, it allows
the tester to hijack the user's session.
During a gray box penetration test, the tester uses phishing
emails to send users to a logon page that looks like the target
organization's human resources self-service page. The fake page is
used to capture employees' credentials. What type of authentication
exploit was used in this scenario?
A. Kerberos exploit
B. Session hijacking
C. Redirect attack
D. Credential brute forcing
C. This is an example of a redirect attack because users are
redirected to a fake website by the phishing emails.
As a part of a gray box penetration test, you need to create a
Bash script to run an exploit against the target organization. As a
part of the script, you need to insert a value of FS1 into an elementnamed HostName within an associative array named Target. Which
of the following lines of code will do this?
A. Target[HostName] = FS1
B. Target = [{"HostName":"FS1"}]
C. $Target.HostName = 'FS1'
D. _Target = {"HostName" => "FS1"}
A. When creating an associative array in a Bash script, you use the following syntax: array_name[element_name] = value. In this example, the line Target[HostName] = FS1 assigns a value of FS1 to the element named HostName within the Target array.
As a part of a gray box penetration test, you need to create a
Ruby script to run an exploit against the target organization. As a
part of the script, you need to insert a value of FS1 into an element
named HostName within an associative array named Target. Which
of the following lines of code will do this?
A. Target[HostName] = FS1
B. Target = [{"HostName":"FS1"}]
C. $Target.HostName = 'FS1'
D. _Target = {"HostName" => "FS1"}
D. When creating an associative array in a Ruby script, you use the following syntax: _array_name = {"element_name" => "value"} . In this example, the line _Target = {"HostName" => "FS1"} assigns a value of FS1 to the element named HostName within the Target array.
As a part of a gray box penetration test, you need to create a
PowerShell script to run an exploit against the target organization.
As a part of the script, you need to insert a value of FS1 into an
element named HostName within an associative array named
Target. Which of the following lines of code will do this?
A. Target[HostName] = FS1
B. Target = [{"HostName":"FS1"}]
C. $Target.HostName = 'FS1'
D. _Target = {"HostName" => "FS1"}
C. When creating an associative array in a PowerShell script,
you use the following syntax: $array_name.element_name = "value". In this example, the line $Target.HostName = 'FS1' assigns a value of FS1 to the element named HostName within the Target array.
As a part of a gray box penetration test, you need to create a
Python script to run an exploit against the target organization. As a
part of the script, you need to insert a value of FS1 into an element
named HostName within an associative array named Target. Which
of the following lines of code will do this?
A. Target[HostName] = FS1
B. Target = [{"HostName":"FS1"}]
C. $Target.HostName = 'FS1'
D. _Target = {"HostName" => "FS1"}
B. When creating an associative array in a PowerShell script,
you use the following syntax: array_name = [{"element_name":"value"}]. In this example, the line Target =
[{"HostName":"FS1"}] assigns a value of FS1 to the element named HostName within the Target array.
As a part of a gray box penetration test, you need to create a
Ruby script to run an exploit against the target organization. As apart of the script, you need to make a comparison between two
variables to test whether they are equal. Which relational operator
should you use?
A. =
B. ==
C. -eq
D. !=
B. When making a comparison between two values in a Ruby
script to see whether they are equal, you use the == relational operator.
You have just concluded a penetration test for a client. During
the test, you discovered that one of the Linux system administrators
uses Telnet to remotely access Linux servers. In your final report,
what should you recommend the client do to remediate this issue?
A. Prohibit remote server access.
B. Use SFTP for remote server access.
C. Use rsh for remote server access.
D. Use SSH for remote server access.
D. The Telnet protocol does not use encryption to protect
network transmissions, which means authentication credentials to the remote system as well as the data being transferred are sent as plain text. To remedy this, you should recommend that the client use the Secure Shell (SSH) server and client for remote server access. SSH encrypts authentication information as well as data transfers
between systems.
You have just concluded a penetration test for a client. During
the test, you discovered that one of Linux system administrators
uses rcp to copy files between Linux servers. In your final report,
what should you recommend the client do to remediate this issue?
A. Use the scp command for file transfers.
B. Prohibit file transfers between servers.
C. Use the rsh command for file transfers.
D. Use the ftp command for file transfers.
A. The rcp utility does not use encryption to protect network
transmissions, which means authentication credentials to the remote system as well as the data being transferred are sent as plain text. To remedy this, you should recommend that the client use the scp command to copy files between servers. The scp utility is part of the SSH suite of utilities, which encrypts authentication information as well as data transfers between systems.
You have just concluded a gray box penetration test for a client.
During the test, you were able to access the organization's wireless
network controller device using a default administrator username
and password. In your final report, what should you recommend the
client do to remediate this issue?
A. Eliminate the transmission of plain text passwords by using SSH
for remote connections.
B. Change the default administrative username and password on the
controller.
C. Use directional antennae on all access points.
D. Implement MAC address filtering on the wireless network.
B. In this scenario, the wireless network can be hardened by
changing the default administrative username and password on the wireless controller. Lists of default usernames and passwords are readily available on the Internet and should not be used.
You have just concluded a black box penetration test for a client.
The organization's wireless network uses preshared keys. During the
test, you were able to access the organization's wireless network
from the parking lot using your laptop running Aircrack-ng. In your
final report, what should you recommend the client do to remediate
this issue? (Choose two.)
A. Implement MAC address filtering.
B. Implement 802.1x authentication.
C. Upgrade to newer Wi-Fi equipment that supports modern
encryption methods.
D. Change the default administrative username and password on the
access point.
E. Reconfigure the Wi-Fi equipment to use WPA encryption.
A and B. In this scenario, the wireless network can be hardened by implementing MAC address filtering. This provides a basic layer of protection by preventing unauthorized systems from connecting to the wireless network. However, MAC addresses are easy to spoof
once a known-good address has been identified. So, the wireless network can be further hardened by implementing 802.1x authentication. This eliminates the weakness associated with preshared keys by implementing a separate authentication server (such as a RADIUS server).
You have just concluded a black box penetration test for a client.
During the test, you were able to access the organization's wireless
network from the parking lot using your laptop running Aircrack-ng.
In your final report, what should you recommend the client do to
remediate this issue? (Choose two.)
A. Use directional antennae on all access points.
B. Reconfigure the Wi-Fi equipment to use WEP encryption.
C. Upgrade to newer Wi-Fi equipment that supports modern
encryption methods.
D. Disable DHCP on the wireless network.
A and D. In this scenario, the wireless network can be hardened by using directional access points. This will help prevent the signal from emanating into the parking lot. In addition, DHCP should be disabled on the wireless network. While this makes administration much more difficult, it also prevents attackers who compromise the wireless network from automatically receiving all the configuration
information they need to access network resources.
You were able to successfully mount an NFS share over the
network with restricted privileges. When going through the network
file system, you notice that the files and directories are not showing
the owner or group name of the files and directories. What is the
likely cause of this?
A. You are not mounting the file system with root permission, so your
system can't interpret the UID values.
B. The NFS file system is not configured correctly, which means you
could probably take advantage of the weakness.
C. The UID and GID values assigned to the files and directories on
the NFS share are not mapping to your local host.
D. The NFS server only knows that the UID 0 maps to the root
account. If you create an account on your local host with a UID valueof one of the NFS files, the NFS server will no longer be able to read
the file.
C. NFSv3 and earlier will map numeric UIDs and GIDs to files
and directories on an NFS file system. When you mount an NFS share from a client using NFSv3, you may see a UID or GID in place of a username or group, because your local operating system cannot map to them, either because you are not on the domain (i.e., LDAP) or the user does not exist.
Open mail relay servers with VRFY and EXPN enabled that allow
anonymous users to connect can be used to do what? (Select all
that apply.)
A. Enumerate valid user accounts
B. Send email to internal email addresses
C. Send email to external email addresses
D. Determine the operating system version of the target host
A, B, C. Open mail relay servers configured for anonymous
access can allow an attacker to impersonate both an internal and external destination address. The VRFY command is used to ask the server for information about an address, and EXPN is used to ask the server for the membership of a mailing list. If the VRFY command against a local account address is successful, it could allow the attacker to enumerate local user accounts. If the EXPN
command is successful, the server will show each subscriber to the mailing list. This information can assist an attacker with future spear phishing campaigns.
The evil twin access point is a type of attack used to duplicate
the existence of a legitimate access point in order to entice victims to
connect for the purpose of targeting end-user devices or
communications. Another way to imitate all possible access points
from client beacon requests is called what?
A. Karma attack
B. Replay attack
C. AP replay attack
D. Social engineering attack
A. The Karma attack will target any SSID it discovers in order to increase the likelihood for exploitation.
This command can be used to execute a type of "ping of death"
against Bluetooth devices.
A. L2PP
B. L2TP
C. L2PING
D. LPING
C. L2PING provides a method that can be used to identify
Bluetooth devices, as well as target them for DoS attacks, using the target MAC address.
All of the following are layers in the Bluetooth protocol stack
except for which one?
A. LMP
B. SDP
C. L2CAP
D. TC2
E. RCOMM
D. TC2 is not a valid layer of the Bluetooth protocol stack.
Telephony Control Protocol Specification (TCS) is, however, a valid layer in the protocol stack and is used for controlling telephone functions on the mobile device.