AIS Final Prt 3
1/72
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
73 Terms
Inaccurate financial statements
Processing integrity controls
Use of packaged software
Training and experience in applying accounting standards and XBRL
Audits
Fraudulent financial reporting
audits
Poorly designed reports and graphs
Responsibility accounting
Balanced scorecard
Training on proper graph design
Inaccurate adjusting entries
Data entry processing integrity controls
Spreadsheet error protection controls
Standard adjusting entries
Reconciliations and control reports
Audit trail creation and review
Unauthorized adjusting entries
Access controls
Reconciliations and control reports
Audit trail creation and review
Inaccurate updating of general ledger
Data processing integrity controls
Reconciliations and control reports
Audit trail creation and review
Inaccurate or invalid general ledger data
Data processing integrity controls
Restriction of access to the general ledger (“G/L”)
Review of all changes to G/L data
Unauthorized disclosure of financial statement
Access controls
Encryption
*Loss or destruction of data
Backup and disaster recovery procedures
Inaccurate payments
Process integrity controls
Supervisory review
Employee review of earnings statement
Failure to make required payments
& Untimely payments
Configuration of system to make required payments using current instructions from IRS
(Publication Circular E)
Theft or fraudulent distribution of paychecks
Restriction of physical access to blank payroll checks and the check signature machine
Restriction of access to the EFT system
Prenumbering and periodically accounting for all payroll checks and review of all EFT direct deposit transactions
Require proper supporting documentation for all paychecks
Use of a separate checking account for payroll, maintained as an imprest fund
Segregation of duties (cashier versus accounts payable; check distribution from hiring/firing; independent reconciliation of the payroll checking account)
Restriction of access to payroll master database
Verification of identity of all employees receiving paychecks
Redepositing unclaimed paychecks and investigating cause
Errors in payroll processing
Data processing integrity controls: batch totals, crossfooting of the payroll register, use of a payroll clearing account and a zero-balance check
Supervisory review of payroll registers and other reports
Issuing earnings statements to employees
Review of IRS guidelines to ensure proper classification of workers as either employees or independent contractors
Inaccurate time and attendance data
Biometric authentication
Segregation of duties (reconciliation of job-time tickets to timecards)
Supervisory review
Inaccurate updating of master data
Data processing integrity controls
Regular review of all changes to master payroll data
Unauthorized changes to payroll master data
Segregation of duties: HRM department updates master data, but only payroll department issues paychecks
Access controls
Violations of employment laws
Thorough documentation of hiring, performance evaluation, and dismissal procedures
Continuing education on changes to employment laws
Hiring unqualified or larcenous employees
Sound hiring procedures, including verification of job applicants’ credentials, skills, references, & employment history
Criminal background investigation checks of all applicants for finance-related positions
*Inaccurate/Invalid master data
Data processing integrity controls
Restriction of access to master data
Review of all changes to master data
*Unauthorized disclosure of sensitive information
Access controls
Encryption
Tokenization (of customer personal information)
Disruption of operations
Backup and disaster recovery plans
Network and logical access controls
Loss of inventory or fixed assets due to fire or disasters
Physical safeguards
Insurance
Sub optional investments in fixed assets
Proper approval of fixed-asset acquisitions, including use of requests for proposals to solicit multiple competitive bids
Poor performance
Training
Performance/managerial reports
Theft of Fixed Assets
Physical inventory of all fixed assets
Restriction of physical access to fixed assets
Maintaining detailed records of fixed assets, including disposal
Over & under production
Production planning systems
Restriction of access to production orders & schedules
Review and approval of production orders & schedules
Poor product design resulting in excess costs
Analysis of costs arising from product design choices
Analysis of warranty and repair costs
Incomplete or inaccurate orders
Data entry edit controls (see Chapter 13)
Restriction of access to master data
Invalid orders
Digital or written signatures
Uncollectable accounts
Credit limits checked and if sale exceeds limit, specific authorization needed
Specific authorization to approve sales to new customers or sales that exceed a customer’s credit limit
Review aging of accounts receivable reports
Stockouts and excess inventory
Perpetual inventory control system
Use of bar codes or RFID
Training
Periodic physical counts of inventory
Sales forecasts and activity reports
Loss of customers
CRM systems, self-help websites, and proper evaluation of customer service ratings
Picking the wrong items or the wrong quantity
Automation of picking using bar-code and RFID technology
Reconciliation of picking lists to sales order details
Theft of inventory
Restriction of physical access to inventory
Documentation of all transfers of inventory between
receiving and inventory employees
RFID and bar-code technology
Restrict ability to cancel sales
Control creation of and shipments to “one-time” customers
Periodic physical counts of inventory and reconciliation to recorded quantities
Segregate custody versus receiving of inventory
Shipping errors
(fail to ship the goods, wrong quantities, wrong items, ship to wrong address, duplication)
Reconciliation of shipping documents with sales orders, picking lists, and packing slips
Use RFID systems to identify delays
Data entry via bar-code scanners and RFID edit controls
Data entry edit controls (if shipping data entered on terminals)
Configuration of ERP system to prevent duplicate shipments
Failure to bill the customer
Separation of shipping and billing functions
Periodic reconciliation of invoices with sales orders, picking tickets, and shipping documents
Billing Errors
Configuration of system to automatically enter pricing data
Restriction of access to pricing master data
Data entry edit controls
Reconciliation of shipping documents (picking tickets, bills of lading, & packing list) to sales orders
Posting errors in accounts receivable
Data entry edit controls
Reconciliation of batch totals
Mail monthly statements to customers
Reconciliation of subsidiary accounts to general ledger
Inaccurate or invalid credit memos
Segregation of duties of credit memo authorization from both sales order entry and customer account maintenance
Configuration of system to block credit memos unless there is either corresponding documentation of return of damaged goods or specific authorization by management
Cash flow problems
Lockbox arrangements, EFT, or credit cards
Discounts for prompt payment by customers
Cash flow budgeting
Purchasing items not needed
Perpetual inventory system
Review and approval of purchase requisitions
Centralized purchasing function
Purchasing items at inflated prices
Price lists
Competitive bidding
Review of purchase orders
Budgets
Purchasing goods of poor quality
Purchasing only from approved suppliers
Review and approval of purchases from new suppliers
Tracking and monitoring product quality by suppliers
Holding purchasing managers responsible for rework & scrap costs
Unreliable suppliers
Requiring suppliers to possess quality certification (e.g., ISO 9000)
Collecting and Monitoring supplier delivery performance data
Purchasing from unauthorized suppliers
Maintaining a list of approved suppliers and configuring the system to permit purchase orders only to approved suppliers
Review and approval of purchases from new suppliers
EDI specific controls (access, review of orders, encryption, policy)
Kickbacks
Prohibit acceptance of gifts from suppliers
Job rotation and mandatory vacations
Requiring purchasing agents to disclose financial & personal interests in suppliers
Supplier audits
Accepting unordered items
Requiring existence of approved purchase order prior to accepting any delivery
Mistakes in counting
Do not inform receiving employees about quantity ordered
Require receiving employees to sign receiving report
Incentives
Use of bar codes and RFID tags
Configuration of the ERP system to flag discrepancies between received & ordered quantities that exceed tolerance threshold for investigation
Not verifying receipt of services
Budgetary controls
Audits
Errors in supplier invoice
Verification of invoice accuracy
Requiring detailed receipts for procurement card purchases
ERS
Verification of freight bill and use of approved delivery channels
Mistakes in posting to accounts payable
Data entry edit controls
Reconciliation of detailed accounts payable records with the general ledger control account
Failure to take advantage of discounts for prompt payments
Filing of invoices by due date for discounts
Cash flow budgets
Paying for items not received
Requiring that all supplier invoices be matched to supporting documents acknowledged by both receiving & inventory control
Budgets (for services)
Verification of all receipts for travel expenses
Use of corporate credit cards for travel expenses
Duplicate payments
Requiring a complete voucher package for all payments
Policy to pay only from original copies of supplier invoices
Cancelling all supporting documents when payment is made
Theft of Cash *@2
Physical security of blank checks and check-signing machine
Periodic accounting of all sequentially numbered checks by cashier
Access controls to EFT terminals
Use of dedicated computer and browser for online banking
ACH blocks on accounts not used for payments
Separation of check-writing function from accounts payable
Requiring dual signatures on checks greater than a specific amount
Regular reconciliation of bank account with recorded amounts by someone independent of cash disbursements procedures
Restriction of access to supplier master file
Limiting the number of employees with ability to create one-time suppliers and to process invoices from one-time suppliers
Running petty cash as an imprest fund
Surprise audits of petty cash fund
Check alteration
Check-protection machines
Use of special inks and papers
”Positive Pay” arrangements with banks
start / end

End (of a process)

activity in process
gateway
flow
annotation info
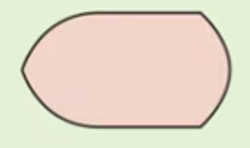
doc

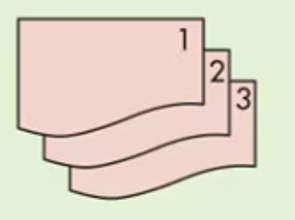
multiple copies of one paper doc
electronic output
electronic data entry

electronic input and output device
computer processing
manual operation

database
magnetic tape

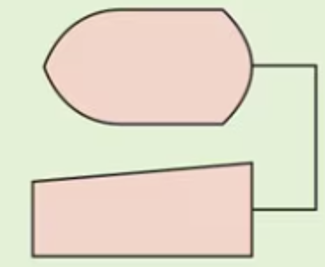
paper document file
n = numberically
a = alphabetically
d = date

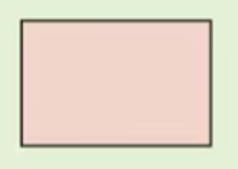
journal / ledger
