Ch 8 Network segmnetation (Total)
1/70
Earn XP
Description and Tags
This set of flashcards covers key concepts and definitions related to network segmentation and VLANs based on the lecture notes provided.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
71 Terms
What is network segmentation and why is it used?
Network segmentation is the process of separating a network's broadcast domain into smaller portions.
What is a subnet?
A group of IP addresses created when physcially subnetting a network
What is a Vlan?
A group of Ports on a Manged switch that become their own Virtual Lan.
True OR false: Each segment has its own broadcast domain?
True
What are the benefits of segmenting a network?
to enhance security, improve network performance, and simplify troubleshooting.
What are common criteria for segmenting networks?
Networks are commonly segmented according to geographic locations, departmental boundaries, or device types.
What OSI layers do Vlans work on?
Layer 2 Data link layer ( Remember: Vlan switches use Ethernet protocol tags)
What layer of the OSI model do Subnets work in?
Layer 3 Network Layer (rememeber: Subnets use IP addresses)
How can virtual LANs (VLANs) be created?
At layer 2, VLANs can be created using physical devices such as switches.
What is the role of a router in network segmentation?
Routers act as broadcast boundaries that can break up large broadcast domains into smaller ones.
What is the purpose of a subnet mask?
A subnet mask helps a device determine how much of the IP address is netowrk ID and how much is Host ID
How does taking a bit from the host ID and giving it to the network ID effect the network?
All of the above (increase number of Bits to represent Network ID, Increase the number of networks (Lans & Vlans) & decrease the number of usable Host IP addresses per subnet )
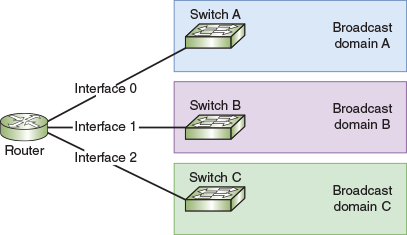
What kind of Subnetting is this?
Subnets (Physical)
Which Ip address of a subnet is assigned to the router port that the lan connects to?
The First Ip address, the netowrk ID
What problem does subnetting solve in classful addressing?
Subnetting addresses the problem of too many node addresses assigned to each classful network.
What must be configured on a router to allow DHCP dynamic Ip addressing?
UDP Forwarding
What is UDP Forwarding on a router?
UDP forwarding, Allows routers to forward UDP traffic. Icluding DHCP broadcasts
What is a Relay Device?
A Networking device configured to allow UDP Forwarding
What is the IP helper address
A command Configuraion on the relay agent, Helps relay agent know where to send network service transmissions.
tells relay agent “ if you get [network service broadcast] from [ port ] then forward the message to [IP address]”
What is static IP addressing and where is it used?
Static IP addressing involves manually assigning IP addresses to devices in a network, often used in smaller or more controlled environments.
What is VLSM and why is it beneficial?
Variable Length Subnet Mask (VLSM) allows subnets to be subdivided into smaller groups, which can optimize IP address usage.
What does VLSM stand for?
Variable Length subnet mask
(easy to remember, variable = can be different & change, length of subnet mask)
How many bits do IPV6 addresses have?
128 bits. (1 hexadecimal number (16 bits) per block x 8 blocks = 128)
True or false, Do IPV6 Ip addresses use subnet masks?
False
What is the Network Prefix?
The First 64 Bits of a IPV6 address. (aka global routing prefix, or site prefix) It identifies the network
What is the Interface ID?
The Last 64 Bits of the IPV6 address. It ID's the Port
Vlans abstract ____ From the ____
Vlans abstract the broadcast domain from the networking hardware
How many switches do you need to make 4 Vlans?
Only 1. Multiple Vlans can be created on One switch
What can you use to Configure Vlans on a managed switch?
CLI (command line interface) or a web-based GUI
True or False: IPV6 IP addresses use Classes?
Flase
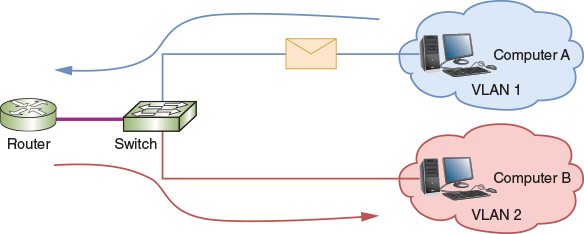
What kind of Subnetting is this?
Logical (VLAN)
If a device on Vlan 1 wants to communicate with another device on Vlan 1, what networking devices does the message need to go through?
Because these devices are on the same vlan, the message only needs to go through the switch.
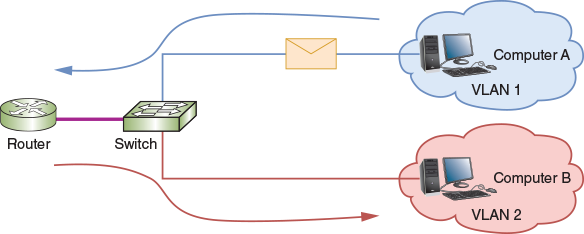
If a device on Vlan 1 wahts to communicate with another device on vlan 2, what networking devices will the messge need to cross.
The message needs to go through the router, even tho both vlans are on the same switch
What is a Tag?
A frame header added by the switch, so that networking devices know which VLAN the meassage came from. Specified by IEEE 802.1Q Standard
Whats another name for the 802.1Q standard?
dot1q
How long does the tag stay with a message?
D) Option A & C
Until the message reaches the switch port connected to the destination device
OR
If the desitnation device is in a different network, so the message reaches a router first. The tag is stripped and given a new one. The new tag will be stripped when the message arrives to the final switch port
What is a VLAN and how does it function?
A VLAN (Virtual Local Area Network) groups ports on switches that limit broadcast traffic to smaller broadcast domains, guiding some traffic through a router.
What are access ports in VLAN configurations?
Access ports connect switches to hosts and carry traffic for only one VLAN
What are trunk ports in Vlan Configurations?
trunk ports connect switches to other networking devices and manage traffic for multiple VLANs.
What is a trunk line?
A single connection medium (cable or wire) that connects two trunk ports
What is Trunking?
The tramsission of data from multiple vlans between two networking devices, using trunk ports and a trunk line
What is ciso’s VTP?
VTP, Vlan trunk protocol.
Chooses one switch in the network to be the “stack master”. Network admin can use the stack master to centrally manage all of the Vlans,
What is a Subinterface?
The logical division of all the data of multiple broadcast domains (vlans & subinterfaces), that enter one router port
What is VLAN hopping?
VLAN hopping is an attack type related to VLAN configurations that can allow unauthorized access between VLANs.
How can devices be assigned to a VLAN?
Devices can be assigned to a VLAN Static-ly ( by which switch port the device is connected to) or Dynamically based on various criteria.
What is a default Vlan?
A vlan that comes preconfigures on a managed switch. Cannot be deleted or renamed, but ports can be redistributed to different vlans
What is a Native Vlan?
A Vlan that revieves all untagge frames from untagged ports
DANGEROUS: Should be changed to unused vlan
What is a Native Vlan mismatch?
When both ends of a connection line both use native vlans, but different individual native vlans (like vlan 1 & 3)
Data Vlan (aka user vlan)
carries user gen traffic (email, web, database updates)
management Vlan
Used to provide administrative access to a switch
Voice Vlan
Designed to support VOIP traffic. So it requires high bandwidth, priority over other traffic, flexable routing, & minimized latency
Private Vlan
A vlan divided into smaller broadcast somains called secondary vlans
Can connect a server, load balancer, or defailt gateway to the primary vlan, so it can communicate with all the secondary vlans
True or false secondary vlans cannot communicate outside of their broadcast domain
What are the two types of secondary vlans
Islotated & Community (both cannot communicte with other vlans), may or may not be able to use trunk line to communicate with other networks
What is static Vlan assignment?
When Clients are assigned to a Vlan based on the switch port they’re connected to
What is Dynamic Vlan assignment?
When a client is chosen for a vlan based on various criteria
, like mac address, location, results of an authentication process by an RADIUS server, deivices that failed to be authenticated, or which WLAN its in
What is Vlan Hopping?
A common VLAN attack that takes advantage of how vlans are tagged.
Creates a transmittion that tricks the switch to believing that it belongs to a protected VLAN of the network. Once within the network the hacker can steal sensitive info or inject harmful software.
Two approahes:
1) Double Tagging
2) Switch Spoofing
What is Double Tagging?
A type of Vlan hopping, a VLAN Cyberattack.
Stacks a fake enterhnet tag below a real ethernet tag. At the real tag is removed by the switch, the fake tag underneath tricks the switch into sending the transmisson to a restricted Vlan.
Switch Spoofing
Attacker connects to Switch, making the connection look like a trunkline.
switch auto configs the port into a trunk port to match the transmission.
Hacker now has access to network & where it can inject harmful trafic into the port
What formula can be used to calculate how many subnets a number of bits make?
2n = y
y= subnets created
n = bits taken
which standard defines how VlAN info aprears in frames & how switches interpret that info?
802.1Q (aka dot1q)
What is the VLAN configuration, where one router connects to a switch that supports multiple VLANs called?
Router on a stick
How many bits of a Class A adress is used for host information?
Class A subnet: 255.0.0.0
24 bits
Whats the number for determining the number of possible hosts?
2n - 2 = z
n = bits taken from host
z = total possible hosts
(total ip addresses - 2 (for network id & broadcast address) )
Which of the following is NOT a good reason to segment a network?
c. To increase the number of networkindg devices on the network
What is the greatest number of bits you can borrow from the host portion of the class B submask, and still have at least 130 hosts per subnet?
b) 8 bits
Which hexademcial block in an IPV^ adress is used for the subnet ID?
c) The forth
Which assignment technique requires a RADIUS server?
Dynamic VLAN
Which port mode on the switch enables that port to manage traffic for multiple vlans?
Trunk
Which IEEE standard determines how VLANs work on a network?
802.1Q