Week 4: Risk Treatment
1/59
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
60 Terms
Risk Treatment
The process of addressing a risk after it has been identified, assessed, and evaluated.
Residual Risk
The remaining risk that has not been completely removed when vulnerabilities have been controlled to the degree possible.
Risk Appetite
The quantity and nature of risk that organizations are willing to accept.
Goal of Cybersecurity
To bring residual risk in line with the organization's risk appetite.
Risk Treatment Strategy Options
Mitigation, Transference, Acceptance, Termination.
Risk Mitigation
Eliminate or reduce risk through the application of additional controls and safeguards.
Types of Mitigation Plans
Incident response (IR) plan, Disaster recovery (DR) plan, Business continuity (BC) plan, Crisis management (CM) plan.
Risk Transference
Shift risk to other assets, processes, or organizations.
Examples of Risk Transference
Outsourcing the security function, Purchasing cybersecurity insurance, Revising deployment models.
Risk Acceptance
Organization decides to do nothing more and accepts the current level of residual risk.
Termination Strategy
The organization chooses not to use a digital asset, removing the need to protect it.
Cost-Benefit Analysis (CBA)
An economic feasibility study done to determine whether the value of an asset warrants its protection.
Cost Avoidance
Spend money on a defense strategy via the implementation of a control to eliminate the financial ramifications of an incident.
The RM Process
Guided by the RM framework, it includes Risk Assessment & Risk Treatment as essential processes.
Role of Process Communication
Continuous feedback from the process team to the framework team about the success and challenges of its RM activities.
Monitoring in RM Process
Ongoing collection of information about issues arising at each stage of the RM process.
Review in RM Process
Establishing formal performance measures and analyzing performance metric data to assess the relative success of the RM program.
Managing Risk Goal
Balancing the expense against the possible losses if vulnerabilities are exploited successfully.
Application of Technology in Risk Mitigation
To reduce risk by deploying preventative controls, detective controls, and response controls.
Outsourcing
Hiring individuals or firms to provide expertise in areas where an organization lacks adequate security management.
Effective Service Level Agreement (SLA)
A key requirement for risk transference strategy.
Cost of development or acquisition
An item that affects the cost of a control or safeguard.
Training fees
An item that affects the cost of a control or safeguard.
Cost of implementation
An item that affects the cost of a control or safeguard.
Service costs
An item that affects the cost of a control or safeguard.
Cost of maintenance
An item that affects the cost of a control or safeguard.
Potential cost from the loss of the asset
An item that affects the cost of a control or safeguard.
Benefit
The value gained by using controls to prevent losses associated with a specific vulnerability.
Asset valuation
Assigning financial value to each information asset.
Components of asset valuation
Includes value to owners, value of intellectual property, value to adversaries, loss of productivity, loss of revenue, and total cost of ownership.
SLE (Single Loss Expectancy)
The calculated value associated with the most likely loss from a single occurrence of a specific attack.
SLE formula
SLE = asset value (AV) × exposure factor (EF).
ARO (Annualised Rate of Occurrence)
Expected frequency of a specific type of attack to occur per year.
ALE (Annualised Loss Expectancy)
Overall loss potential per risk, calculated using ARO and SLE.
CBA purpose
To determine whether the benefit of a control justifies its cost.
CBA formula
CBA = ALE (precontrol) − ALE (postcontrol) − ACS.
Benchmarking
Comparing organizational security effectiveness, efficiency, and productivity against an established measure.
Exercise due care
Adopts a certain minimum level of security.
Qualitative assessment
Risk assessment steps using qualitative estimates.
Hybrid asset valuation
A more granular approach that creates a value for an asset reducing ambiguity of qualitative measures.
Delphi Technique
A process whereby a group of experts rates or ranks a set of information through iterative feedback.
Organizational feasibility
Examines how well the proposed cybersecurity alternatives will contribute to efficiency, effectiveness, and overall operation of an organization.
Operational feasibility
User acceptance and support, management acceptance and support, and the system's compatibility with the requirements of the organization's stakeholders.
Behavioral feasibility
Also known as organizational feasibility.
Technical feasibility
Determines whether required technology and expertise exist or can be acquired.
Political feasibility
Defines what can and cannot occur based on the consensus and relationships between the communities of interest.
Risk Treatment Practices
Includes valuing information assets and handling changes, with standards and best industry practices as better alternatives.
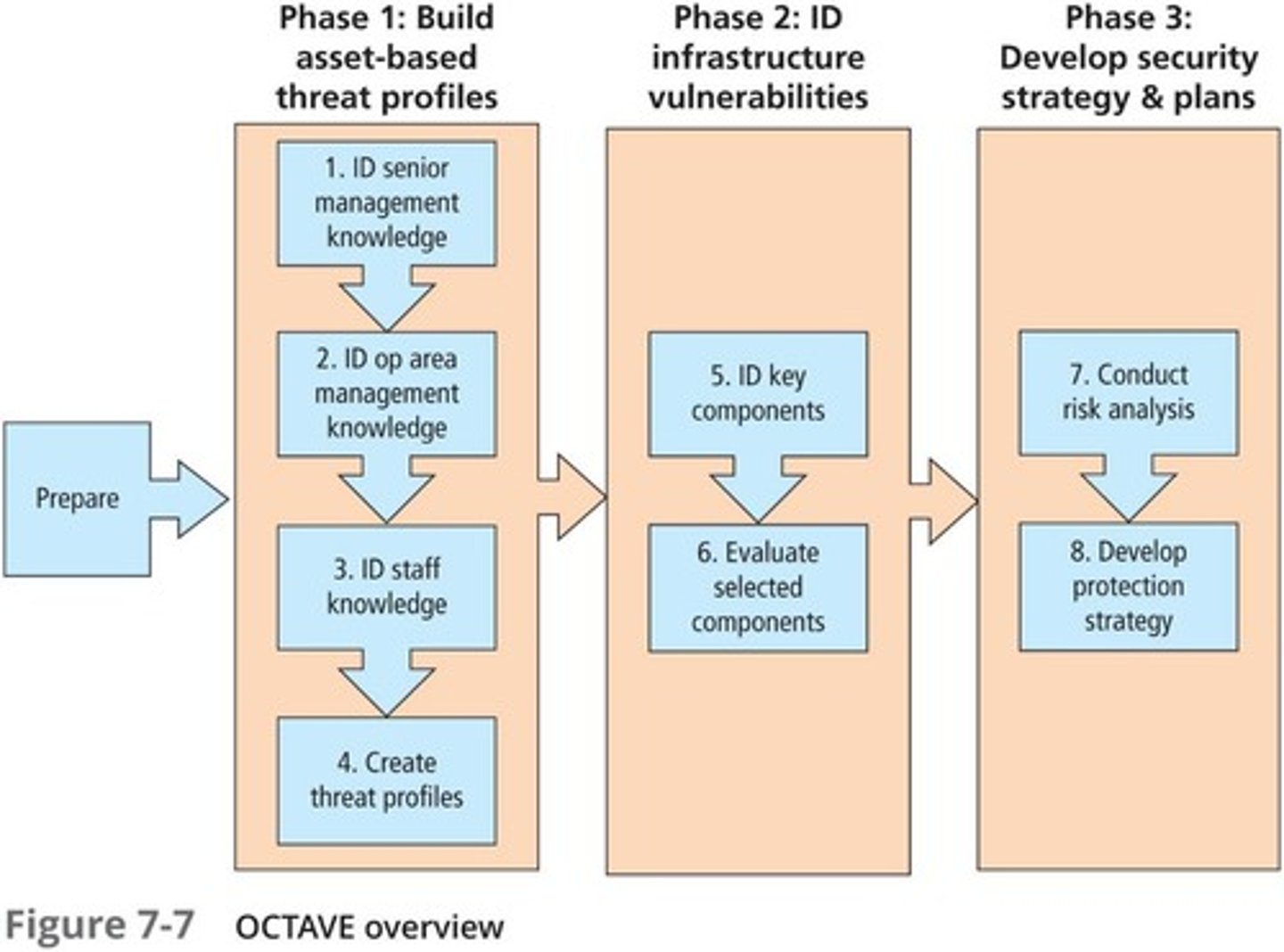
OCTAVE method
Operationally Critical Threat, Asset, and Vulnerability Evaluation; a risk evaluation methodology for balancing protection of critical information assets vs. the costs of providing protective and detection controls.
FAIR (Factor Analysis of Information Risk)
Supports understanding, analyzing, and measuring information risk.
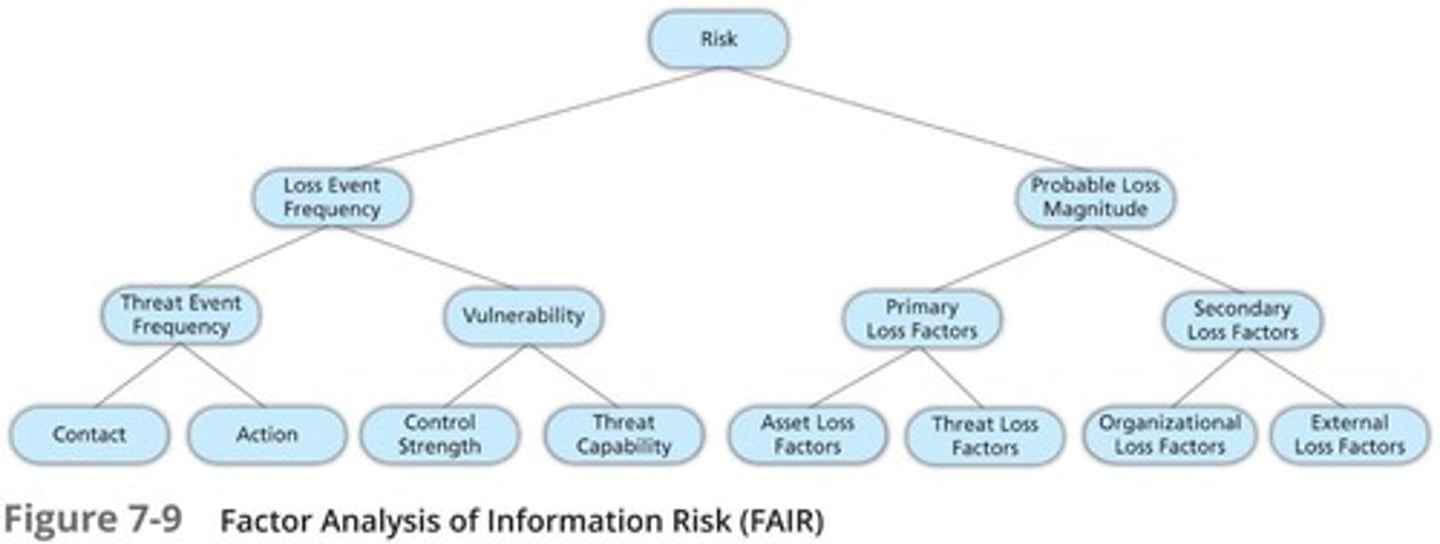
FAIR outcomes
More cost-effective risk management, greater professional credibility, and a basis for a scientific, repeatable risk management approach.
FAIR framework components
Includes a taxonomy for information risk, standard nomenclature for information risk terms, a framework for establishing data collection criteria, measurement scales for risk factors, a computational engine for calculating risk, and a modeling construct for analyzing complex risk scenarios.
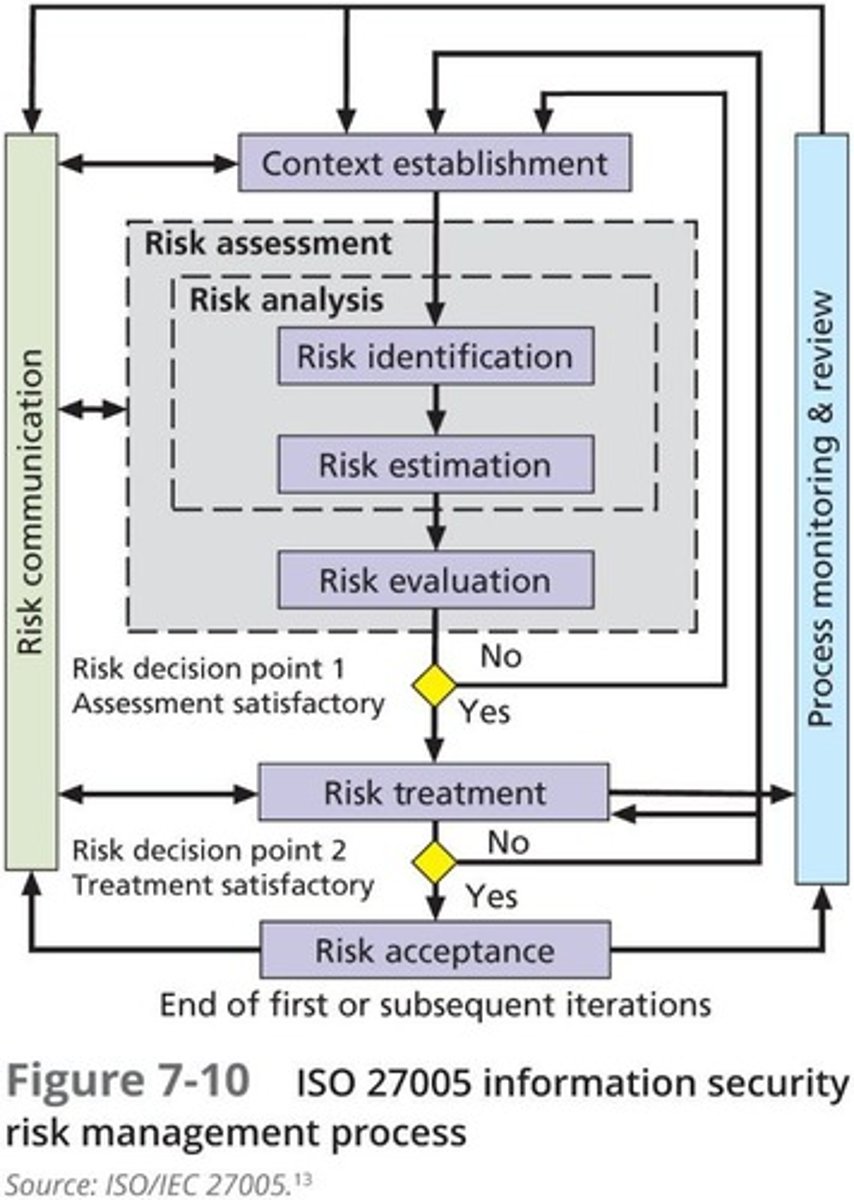
ISO 27000 series
Includes a standard for the performance of Risk Management, ISO 27005.
ISO 27005 methodology stages
Risk Assessment, Risk Treatment, Risk Acceptance, Risk Communication, Risk Monitoring and Review.
ISO 31000
Risk management principles, framework, and process.
NIST Risk Management Approach
An organization-wide risk management approach.
NIST Risk Management Framework
A structured approach to risk management.
Selecting the Best Risk Management Model
Involves studying established RM models and identifying what each offers to the envisioned process.
Engaging with security professionals
Important when building a risk management program from scratch.
Professional security organization meetings
Like ISS, can be useful for networking and knowledge sharing.
Still learning (4)
You've begun learning these terms. Keep up the good work!