Prof Messer CompTIA SY0-701 Security+ 1.1 & 1.2
1/55
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
56 Terms
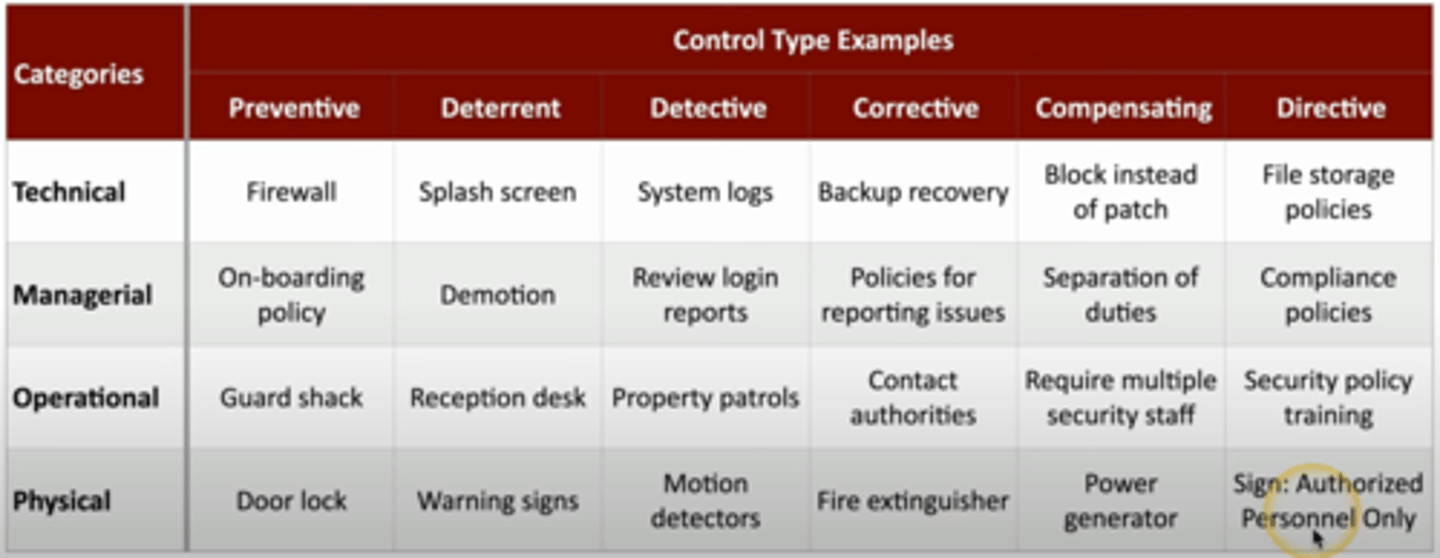
control categories
technical controls
managerial controls
operational controls
physical controls
technical controls
controls implemented using systems/tech
OS controls
firewalls, antivirus, etc
managerial controls
administrative controls associated with security design and implementation
security policies, standard operating procedures, etc
operational controls
controls implemented by people
security guards, etc
physical controls
limit physical access
fences, locks, badge readers, etc
control types
preventive
deterrent
detective
corrective
compensating
directive
preventive control types
block access to a resource
ex: firewall rules, door locks, guards checking ID, etc
deterrent control types
discourage intrusion
threat of demotion, posted warning signs, application splash screens, etc
detective control types
identify and log an intrusion attempt
find issue
- collect and review system logs
- review login reports
- regularly patrol property
- motion detectors
corrective control types
apply a control after event has been detected
reverse impact of event
continue operating with minimal downtime
ex: restoring from backups to mitigate an infection, create policies for reporting security issues, use fire extinguisher
compensating control types
control using other means; current controls arent enough
prevent the exploitation of a weakness
ex:
firewalls block an application while devs work on a patch, generator used after power outage
directive control types
direct a subject towards a security compliance
relatively weak security control
"do this please"
ex: store all sensitive files in a protected folder, post a sign saying "authorized personnel only" etc
control categories and types
The CIA Triad
Confidentiality, Integrity, Availability
Confidentiality
prevent disclosure of info to unauthorized people/systems
some ways to provide it:
encryption
access controls
2 factor auth
Integrity
messages cant be modified without detection
some ways to provide it:
hashing
digital signatures
certificates
non-repudiation
certificates
combined with dig sigs to verify an individual
Availability
systems and networks must be up and running
some ways to provide it:
redundancy
fault tolerance
patching
fault tolerance
the ability for a system to keep running even when a failure occurs
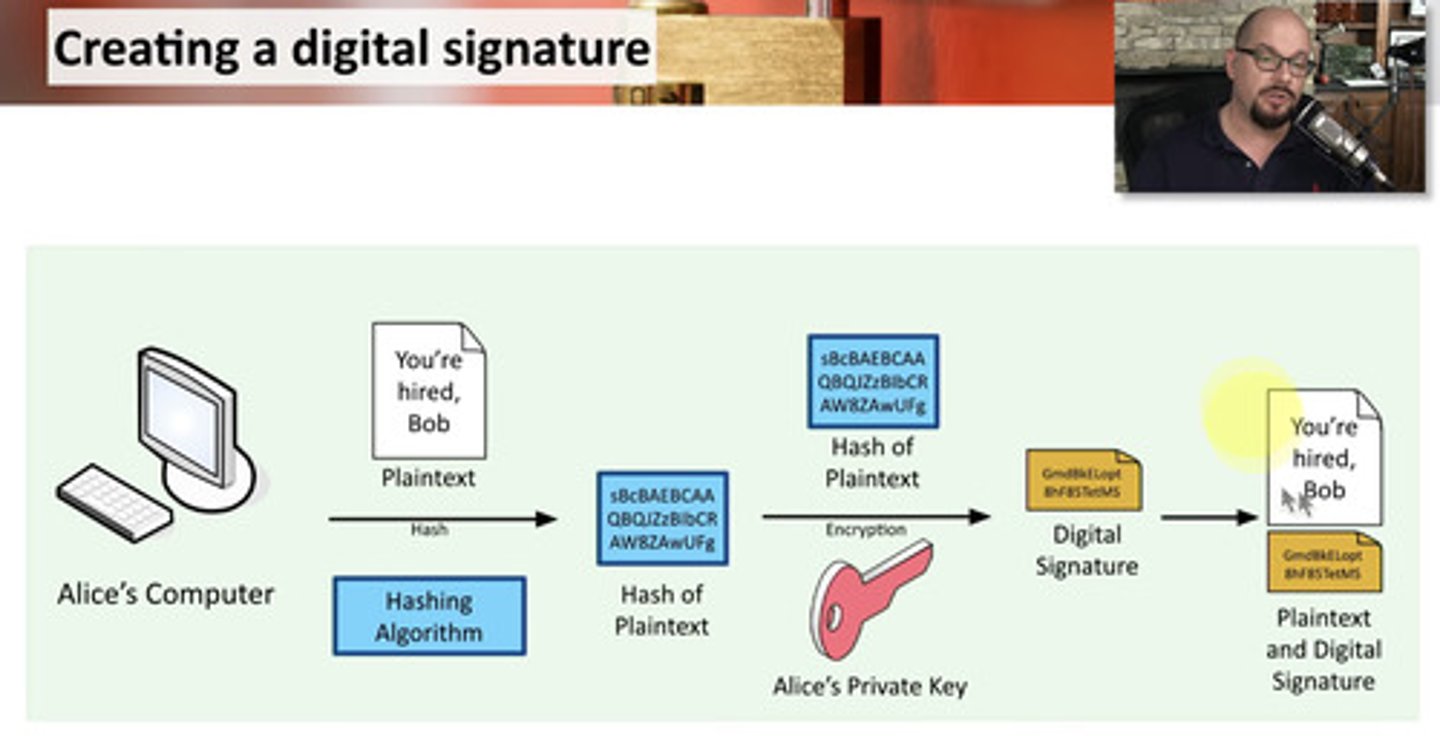
non-repudiation
provides proof of integrity, can be asserted to be genuine
you cant deny what you said - no take backs
proof of integrity
verify data doesnt change - remains accurate and consistent
in cryptography - hash is used
- only tells if data was changed, not linked to an individual
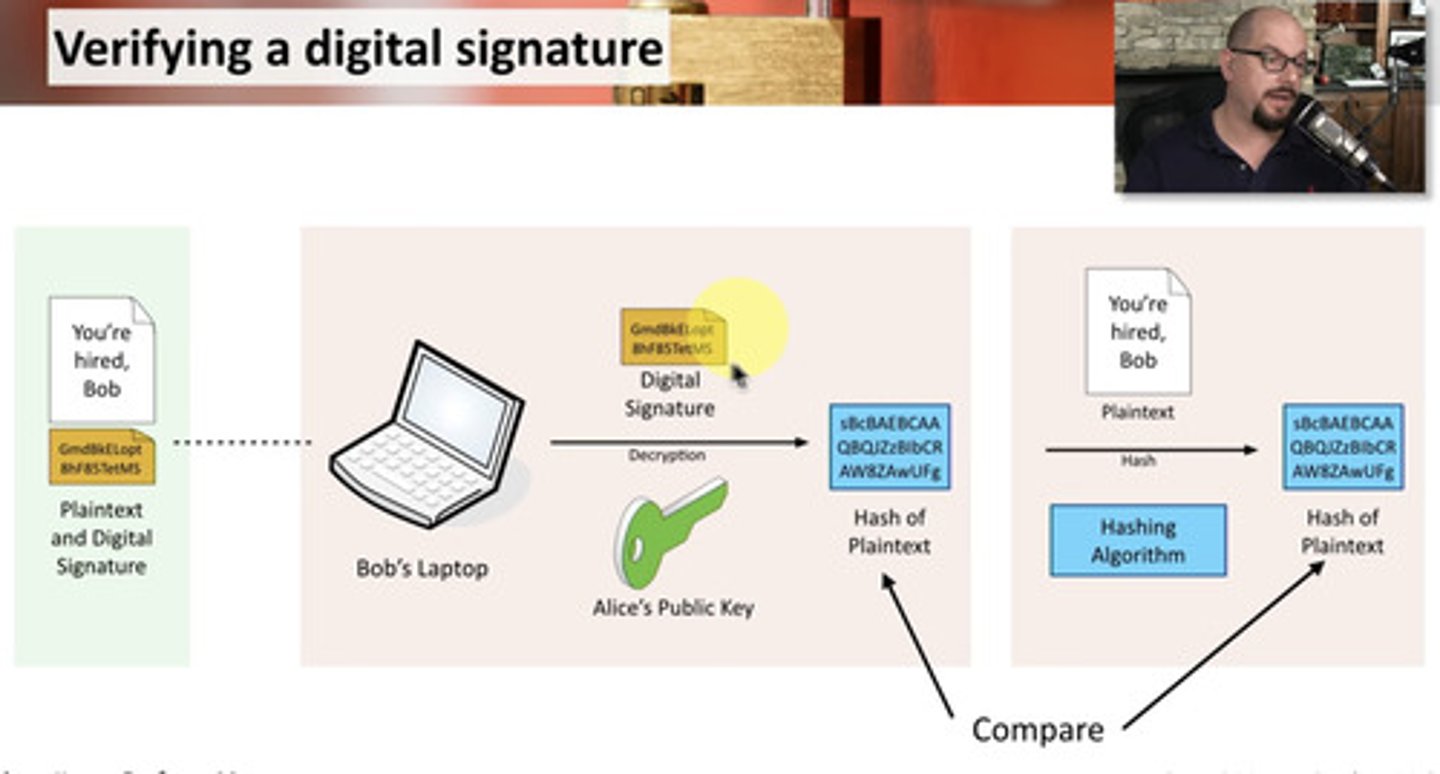
proof of origin
prove source of the message
make sure signature is not fake
sign with the private key
- message doesnt need to be encrypted
- nobody else has the private key (only person sending the data)
verify with the public key associated with the private key
- any change to the message will invalidate the signature
creating a digital signature
verifying a digital signature
AAA Framework
Identification
Authentication
Authorization
Accounting
Identification
this is who you claim to be
(think username)
Authentication
prove who you say you are
(password, etc)
Authorization
based on your identification and authentication
Accounting
login time, data sent and received, logout time, etc
authenticating systems
put a digitally signed certificate on the device
- other business processes rely on the certificate (VPN access, etc)
certificate authentication
Certificate Authority needed
organization creates a cert for the device
- signs it with their CA
cert now able to be added as an authentication factor
- CA's digital signature is used to validate the cert
Certificate Authority (CA)
device/software responsible for managing all the certs in the environment
CA has its own cert signed by root CA
no authorization model
simple relationship
user -> data
does not scale
- manually setting up permissions for lots of people would take forever
authorization models
used to give diff people different access based on role, organization, etc
allows authorization to be much more scalable and easier
reduce complexity
administration is streamlined
gap analysis
where you are vs where you wanna be
may require extensive research
- can take weeks, months, years
choosing framework (gap analysis)
work towards a known baseline
- may be an internal set of goals
- some orgs should use formal standards
determine end goal
evaluate people and processes (gap analysis)
get a baseline of employees
- formal experience
- current training
- their knowledge
examine current processes
compare and contrast (gap analysis)
identify weaknesses
- along with most effective processes
a detailed analysis
- examine broad security categories
- break those into smaller segments
the analysis and report (gap analysis)
final comparison
- clear view of current state
- detailed baseline objectives
need a path to get from current security to goal
zero trust
authenticate every time you want access to a resource
everything must be verified
planes of operation
splitting network into functional planes
data plane
control plane
data plane (planes of operation)
- process the frames, packet and network data
- anything that helps data move from one part of the network to another
part of device that performs the actual security process
control plane (planes of operation)
manages actions of data plane
- defines policies and rules
- determines how packets should be forwarded
etc
adaptive identity
consider the source and requested resources
multiple risk indicators (location, type of connection, etc)
make authentication stronger if needed
threat scope reduction
-decrease number of entry points
policy driven access control
combine adaptive identity with a redefined set of rules
looks at everything, and decides what type of authentication process is best
security zones
looks at where you are trying to connect from and where you are trying to connect to
- trusted, untrusted network
- internal/external network
define what zones have access to other zones
policy enforcement point (PEP)
any subjects and systems that are communicating through this will be evaluated by the PEP
a "gatekeeper"
can be multiple devices
doesnt make the decision, just allows/disallows
Policy Decision Point (PDP)
info from PEP is given to PDP to make an authentication decision
made up of:
policy engine
policy administrator
policy engine
evaluates each access decision based on policy and info sources
- grant, deny, revoke
policy administrator
takes decision from policy engine and gives it to PEP
- generates access tokens or credentials
physical security
barricades/bollards
access control vestibules
fencing
video surveillance (CCTV)
guards and access badges
lighting
sensors
honeypots
attract bad guys and trap them there
create a virtual world for them to explore, fake systems for them to attack
honeynets
combine honeypots into honeynets
- a larger deception network
fake networks to trap attackers
honeyfiles
fake files to attract attackers
bait for honeypots
honeytokens
traceable data that you put in honeynets
- if its stolen you know where it came from
can be any type of data
Still learning (1)
You've started learning these terms. Keep it up!