FSCI 3400- Exam2
1/80
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
81 Terms
What Is Glass
Glass is a hard, brittle, amorphous substance composed primarily of silicon oxides derived from sand, combined with various metal oxides to achieve desired properties.
Glass Key Additives
Sodium carbonate (soda) — lowers the melting point of sand, making glass production more energy-efficient
Calcium carbonate (lime) — prevents glass from dissolving in water and increases chemical durability
Comprises approximately 90% of manufactured glass products
Glass Composition
Silicon Dioxide (SiO₂) Forms the glass network structure
Sodium Oxide (Na₂O) Reduces melting temperature
Calcium Oxide (CaO) Provides stability and durability
Other Metal Oxides Modifies color and properties
Physical Properties of Glass
Characteristics that can be observed or measured without changing the substance's identity.
Density
• Refractive index
• Color and transparency
• Hardness
• Fracture patterns
physical properties are typically more useful for comparison and identification because they can
be measured non-destructively.
Chemical Properties
Characteristics that describe how a substance interacts with other substances
• Elemental composition
• Chemical reactivity
• Resistance to corrosion
• Thermal stability
Glass Examination
Density: Mass per unit volume — highly discriminating property that varies with glass composition
Refractive Index: Measure of how light bends when passing through glass — precise and reliable for comparisons
Surface Characteristics: Texture, striations, and manufacturing marks that may be unique to a source
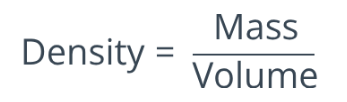
Density
Density is defined as mass per unit volume, typically expressed as grams per cubic centimeter (g/cm³) for glass.
Density is an intensive property — it remains constant regardless of sample size, making it ideal for forensic comparisons.
Flotation Method-Principle of Operation
The flotation method exploits Archimedes' principle to determine density by observing whether a glass fragment floats (Glass density is greater than liquid density), sinks, or remains suspended in liquids of known density.
Measuring Density: Water Displacement Method- A Simple Procedure for Determining the Density of a Solid
Measure Mass
Measure Volume
Calculate Density obtain density in g/cm³
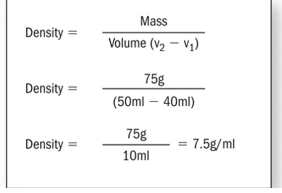
Refraction
Refraction is the bending of light waves as they pass from one transparent medium into another of different optical density. This phenomenon occurs because light travels at different speeds through different materials.
Reflection Key Concepts
• Light travels fastest in a vacuum
• Light slows down when entering denser media
• The degree of bending depends on the difference in optical densities
• Refraction only occurs when light strikes the interface at an angle
Reflection Forensic Significance
Refraction properties are highly specific to glass composition, making them invaluable for distinguishing between different glass sources in forensic investigations.
Understanding Light Behavior and Critical Angle
When light passes from air into glass at an angle, it bends toward the normal (an imaginary line perpendicular to the surface). When exiting glass back into air, light bends away from the normal.
Critical Angle: At steep angles, light may be totally reflected rather than refracted — this is called total internal reflection and is the principle behind fiber optics.
Refraction vs. Refractive Index
Quantifying Refraction
While refraction is the phenomenon of light bending, the refractive index is the numerical value that quantifies this behavior for a specific material.
The refractive index (n) represents the ratio of the speed of light in a vacuum to its speed in the material. Higher refractive indices indicate that light travels more slowly through the material and bends more dramatically.
Temperature Dependence and Wavelength Dependence
Glass Immersion Method
The immersion method is the primary technique for determining the refractive index of glass fragments in forensic laboratories. This method involves immersing glass particles in liquids with known refractive indices.
Glass Immersion Method Process
Sample Preparation: Place glass fragment in a specialized immersion liquid on a microscope slide
Temperature Control: Heat the slide gradually while observing under a microscope with specialized lighting
Match Point Detection: When the glass "disappears" (Becke line vanishes), its refractive index matches the liquid
Index Determination: Record the temperature and calculate the glass refractive index using calibration data
Analyzing Cracks-Fracture Pattern Analysis
When glass breaks, it creates distinctive fracture patterns that reveal critical information about the direction of force, sequence of impacts, and sometimes even the type of object used to break it.
Radial Cracks: Fractures extending outward from the point of impact like spokes on a wheel
Concentric Cracks: Circular fractures connecting radial cracks around the impact point
Stress Marks: Microscopic surface features revealing the direction of crack propagation
Formation Sequence
(a) Radial cracks are formed first, commencing on the side of the glass opposite to the destructive force
(b) Concentric cracks occur afterward, starting on the same side as the force
The 3R Rule
Radial cracks form on the Reverse side
Concentric cracks form on the Contact side (same)
Analyzing Cracks-Determining Impact Sequence
The sequence of impacts (when there are multiple penetrations of the glass) can be determined because a fracture always terminates at an existing line of fracture.
Critical Principle: When glass sustains multiple impacts, subsequent fractures cannot cross pre-existing cracks.
Glass Fragments
Collection: Glass fragments are carefully collected from suspects' clothing, vehicles, or crime scenes
Documentation: Each fragment's location, appearance, and context is meticulously recorded
Analysis: Physical and optical properties are measured and compared to known samples
Comparison: Results determine if questioned fragments match a known source
Collection of Glass - Evidence Collection Procedures
Meticulous collection of glass evidence is critical to maintaining chain of custody and ensuring the integrity of forensic analysis.
Clothing Evidence: Carefully collect clothing from suspects and wrap separately in clean paper to prevent glass transfer
Vehicle Examination: Vacuum carpets and seats; examine tire treads and undercarriage for glass fragments
Crime Scene Glass: Collect representative samples from all broken glass sources for comparison analysis
Packaging: Store glass fragments in rigid containers with secure lids to prevent loss or cross-contamination
Collection of Glass - Best Practices and Considerations
Document Location: Photograph and diagram the exact position of glass fragments before collection
Use Proper Tools : Employ clean tweezers, tape lifts, or vacuum filters to collect microscopic particles
Prevent Contamination: Change gloves between samples and use separate containers for each source
Collect Reference Samples: Always obtain known samples from the suspected source for comparison
Maintain Chain of Custody: Label all evidence with case number, date, time, location, and collector's initials
Hairs and Fibers
Hair and fiber evidence represents one of the most common types of trace evidence encountered at crime scenes.
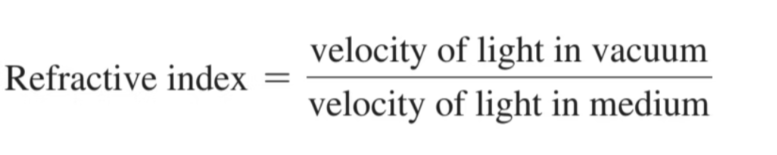
Morphology of Hair
Hair is a complex biological structure composed of three distinct layers, each with unique characteristics that can be observed under microscopic examination.
The cuticle forms a protective outer shell, while the cortex contains the structural proteins and pigments that give hair its strength and color.
Cuticle: The Protective Outer Layer
The cuticle is the outermost covering of the hair shaft, consisting of overlapping scales that point toward the distal end of the hair.
Forensic Significance: Cuticle scale patterns vary significantly between species
Examination Methods: Scale patterns are best observed by making a cast of the hair surface or by electron microscopy
Cuticle scale patterns types-Coronal Scale Pattern
Coronal Scale Pattern: "Crown-like" appearance with distinctive overlapping structure. Overlapping and encircling scales create a stacked appearance
resembling a crown.
This scale pattern is a diagnostic feature that can immediately exclude human origin when observed during microscopic examination.

Cuticle scale patterns types- Spinous Scale pattern
"Petal-like" Scales: Generally triangular in shape, resembling petals or thorns protruding outward.
Distinctive Projection: Scales protrude outward from the hair shaft creating a unique three-dimensional structure
Spinous scale patterns are never found in human hair.
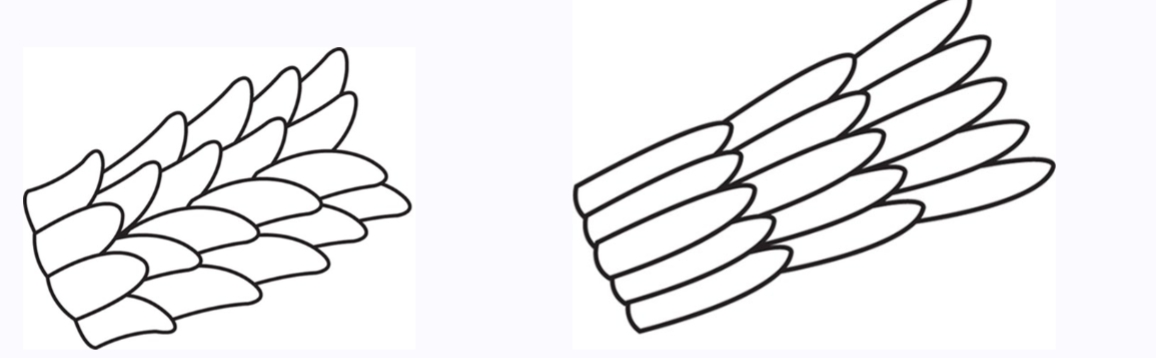
Cuticle scale patterns types- Imbricate Scale Pattern
"Flattened" Configuration. Very narrow, flattened scales that overlap in a shingle-like pattern along the hair shaft
Partial Encirclement. Unlike coronal patterns, imbricate scales do not completely encircle the hair shaft, creating a distinctive asymmetric appearance
Human Hair Indicator, Very common to human hair and serves as a primary identifying characteristic in forensic examinations
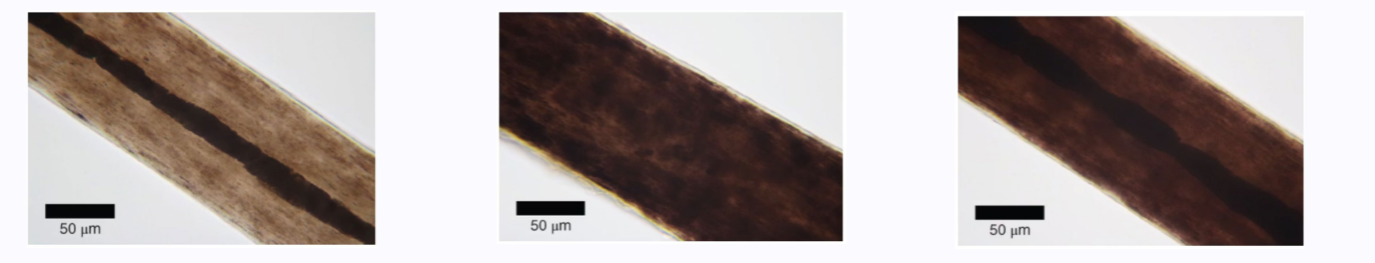
Cortex: The Main Body
The cortex forms the main body of the hair shaft, lying between the cuticle and medulla.
This layer contains pigment granules (melanin) that determine hair color, as well as cortical fusi and ovoid bodies that can be observed microscopically. The cortex provides the hair with its strength, texture, and color, making it crucial for forensic comparisons.
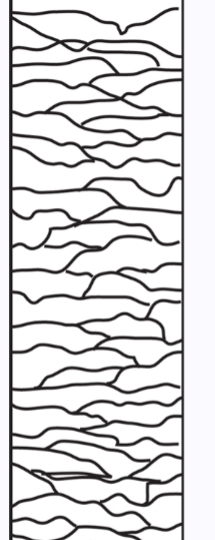
Medulla: The Central Core. Medullary Index; Human Hair and Animal Hair
Medullary Index: Measures the diameter of the medulla relative to the diameter of the hair shaft, providing a key species differentiation tool.
Human Hair: The medulla generally occupies less than one-third the diameter of the shaft.
Animal Hair: The medulla typically occupies one-half or greater of the shaft diameter.
The medulla may be continuous, interrupted, fragmented, or absent entirely.
Medulla Patterns
Continuous: An uninterrupted column running the length of the hair shaft
Interrupted: Regular intervals of presence and absence along the shaft
Fragmented: Irregular, sporadic presence with inconsistent patterns
Absent: No visible medulla present in the hair shaft
The medullary index and pattern type together provide powerful discriminating characteristics.
Root Structure and Growth
Root characteristics can indicate the manner of hair removal and the growth phase at the time of loss.
Growth Phases: Hair grows in cyclical phases—anagen (active growth), catagen (transitional), and telogen (resting)—each producing distinctive root appearances.
Forensic Value: Root structure helps determine if hair was forcibly removed, fell out naturally, or was cut, providing important context for crime scene analysis.
Hair Growth Phases
Anagen Phase: Active growth phase lasting 2-7 years. Root shows an elongated follicular tag with attached tissue. Hair is firmly anchored in the follicle.
Catagen Phase: Transitional phase lasting 2-3 weeks. Growth stops and follicle shrinks. Root becomes club-shaped as follicle detaches.
Telogen Phase: Resting phase lasting 2-4 months. Hair easily detaches naturally. Root appears as a bulbous club with no tissue attached.
Identifying the growth phase helps forensic scientists determine whether hair was forcibly removed or shed naturally, which can have significant implications for case reconstruction.
Comparing Hair Strands
The comparison involves assessing both class characteristics (features common to a group) and individual characteristics (unique features).
Examiners must consider the full range of morphological features including color, length, diameter, cuticle patterns, cortex characteristics, medulla type, and root structure.
Hair Comparison Methodology
Macroscopic Examination: Initial visual assessment of color, length, curl, and overall appearance to identify obvious differences or similarities.
Microscopic Analysis: Detailed comparison of cuticle scales, cortex pigmentation, medulla patterns, and other morphological features using comparison microscopy.
Documentation: Systematic recording of observations, measurements, and photomicrographs to support conclusions and enable peer review.
Conclusion: Determination of whether questioned and known samples could have originated from the same source based on comparison results.
Hair Comparison Methodology Limitation
Microscopic hair comparison cannot positively identify a hair as originating from a specific individual. It can only determine that hairs are consistent with originating from the same source. DNA analysis is required for individualization.
Hair Comparison Methodology Questions
Is the hair of human or animal origin?
From what part of the body does the hair originate?
What is the racial ancestry of the individual?
Determining Body Area of Origin
Head Hair: Generally longest with fairly uniform diameter throughout shaft. Medulla may be continuous, interrupted, or absent. Cut ends are common.
Facial Hair: Coarse and wiry with triangular cross-section. Often shows evidence of cutting or shaving. Medulla usually continuous.
Body Hair: Generally shorter with arc-like shaft. Diameter varies considerably along length with tapered tips. Fine to coarse texture.
Pubic Hair: Coarse with continuous wide medulla. Shaft diameter varies considerably. Often has buckling and twisting characteristics.
Racial Ancestry Determination
Caucasian
Straight to wavy; Oval cross-section; Fine to medium texture; Evenly distributed pigment
African
Curly to kinky; Flattened cross-section; Coarse texture with buckling; Dense, clumped pigment
Asian
Straight configuration; Round cross-section; Coarse texture with thick diameter; Continuous broad medulla
Racial determination from hair is based on population-level characteristics and represents probabilities rather than certainties.
Racial Ancestry Questions
Has the hair been artificially treated?
What is the condition of the root?.
Is there evidence of disease or damage?
Are the questioned and known hairs consistent?
Hair and Mitochondrial DNA Analysis
Mitochondrial DNA (mtDNA) can be extracted from the hair shaft, even when nuclear DNA is not recoverable. mtDNA is located in cellular material outside the
nucleus and is transmitted exclusively from mother to child through maternal inheritance.
Limitations: MtDNA has a relatively high frequency of occurrence in populations.
It cannot be used to individualize a hair to a single person
All positive microscopic hair comparisons must be confirmed by DNA analysis
Collection and Preservation of Hair Evidence
Recognition
Documentation
Collection
Packaging
Labeling
Known Standards: When collecting reference samples from individuals, obtain at least 25-50 full-length hairs from different areas of the scalp by pulling (not cutting) to include root structure. Package separately from questioned samples to prevent cross-contamination.
Fiber Classifications: Natural vs. Man-Made Fibers
Natural Fibers: Derived from plant, animal, or mineral sources. Examples include cotton, wool, silk, and asbestos.
Man-Made Fibers:
Regenerated fibers are manufactured from natural raw materials through chemical processing. Common types include rayon, acetate, and triacetate, which maintain some natural characteristics.
Synthetic fibers are produced entirely from synthetic chemicals, including polymers such as nylons, polyesters, and acrylics. These represent the majority of modern textile fibers.
Synthetic fibers are composed of polymers or macromolecules
Polymer Structure
Monomers: Individual molecular units that serve as building blocks, like individual chain links
Polymerization: Chemical process joining thousands of monomers into long molecular chains
Polymer Fiber: Final product with distinct physical and chemical properties based on monomer composition
The specific arrangement and composition of monomers determines the fiber's physical properties, appearance, and forensic significance.
Fiber Evidence in Criminal Investigations
Fiber evidence can provide crucial links between suspects, victims, and crime scenes through transfer and persistence.
Primary Transfer: Direct transfer of fibers from source to recipient during physical contact between individuals or objects
Secondary Transfer: Subsequent transfer of already-transferred fibers to a third location or person through additional contact
Persistence: Duration that fibers remain on recipient surface, affected by fiber type, contact nature, and subsequent activity
Recovery: Collection of transferred fibers through tape lifting, vacuuming, or manual removal for laboratory analysis
Forensic Fiber Examination Techniques
Purpose: combination to provide comprehensive fiber characterization
Microscopy: Comparison microscopy allows side-by-side evaluation of questioned and known samples.
Microspectrophotometry: Creates spectral fingerprint unique to specific dyes and pigments used in fiber production.
FTIR Spectroscopy: Identifies polymer type by measuring molecular vibrations. Distinguishes between fiber types with similar appearance but different chemical composition.
Thermal Analysis: Determines melting point and thermal decomposition patterns.
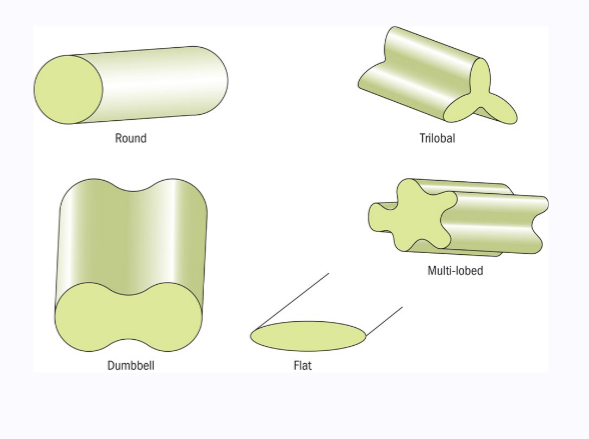
Cross-Sectional Shapes of Fibers
It is a distinctive characteristic determined by the manufacturing process
Natural Fibers: Cotton shows kidney-bean or ribbon-like shape. Wool exhibits circular to oval cross-section with scales. Silk displays triangular morphology.
Synthetic Fibers
Cross-sections vary widely: round, trilobal, pentalobal, dog-bone, or irregular shapes determined by spinneret design during manufacturing.
Collection and Preservation of Fiber Evidence
Unlike hair, fibers are often smaller and more easily lost or contaminated.
Visual Examination
Tape Lifting; Manual Collection
Garment Packaging: Wrap garments individually in clean paper, never allowing items to contact each other.
Documentation
Maintain strict separation between questioned and known samples
Computer Forensics
It represents the scientific analysis of digital evidence to support criminal investigations and legal proceedings.
Recovery: Systematic extraction of digital data from storage
Chain of Custody
Technical Analysis
Hardware VS. Software
Hardware: Physical and tangible computer
Software: Set of instructions complied into programs
Computer Terminology
Computer Case: The house and protects all internal computer components
Power Supply: Convers alternative current from wall outlets to different current at various voltage required by the computer
Motherboard: The primary circuit board containing the system’s core components
System Bus: Electrical pathway on the motherboard that facilitates data transfer
Computer Hardware Components
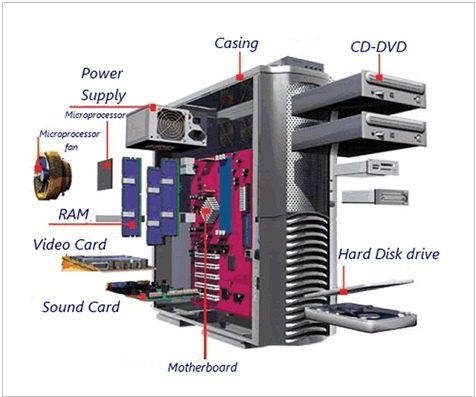
Computer Critical components
Read only memory (ROM) - programs essential for system initialization. those non-volatile storage devices retain their contents even when power is removed.
Central Processing Unit (CPU)- Computer’s processing center, executing instructions and managing system operations. Modern processors contain cache memory that retain certain data.
Random Access Memory (RAM)- system performance enhance , providing high speed temporary storage. Dynamic data management, Computer strategically loads frequently accessed data into RAM for immediate availability. Volatile Evidence Concerns, complete lost when power is removed
Input and Output devices
Input: Keyboard; mouse; joystick; scanner
Output: Monitor; Printer; Speakers
Digital Storage Architecture
Storage Device Types: Hard Disk Drives; Solid State Drives and optical media each employ different storage technologies
File System Structures: Various file system like NTFS organize data differently
Metadata preservation: File creation dates, modification times and assess logs
Hard disk drive data organization
Partitioning: initial division of storage space into logical sections for organization and management
Formatting: Define how data will be stored and assessed
Binary Storage: Data stored as bits (0-1) with 8 bits forming one byte and 512 bytes forming one sector
Logical Division: Organization into sectors, clusters, tracks and cylinders for precise data location
Hard disk drive data partitions
Disk partitioning creates logical divisions within physical storage devices, enabling organized data management and forensic analysis.
Primary: Main bootable section containing operating system and core applications
Extended partitions: hold multiple logical dives within their boundaries
Hidden partitions: Concealed storage areas that many contain deleted or sensitive evidence
Advanced data storage concepts
Critical for forensic investigators to recover deleted files
File allocation tables: track file locations and storage status
Unallocated space: Areas where deleted files may still exist until overwritten
File Fragmentation: When files are split across non-contiguous sections.
Forensic DATA recovery methods
Logical analysis: system level exam
Physical analysis: bit by bit exam of storage media. unallocated and damaged areas
Network analysis: exam network traffic and communication logs
Processing Electronic Crime Scene
Initial assessment: Document, identify potential evidence and establish security
Evidence ID
Preservation decisions
Secure Transportation
Shutdown vs. Pulling the Plug
encryption considerations: Abrupt power loss may trigger encryption protocols
Volatile memory evidence: RAM will be permanently lost if not captured before power removal
Equipment Seizure protocol
Forensic Image Acquisition
Fundamental process of creating exact bit by bit copies of digital storage media while maintaining the integrity of original evidence.
Write Protection: Use hardware write blockers to prevent any modification of the original evidence including imaging
Bit by bit copying: Create exact sector- level duplications of the entire storage device
Hash verification: verify the integrity and authenticity of images.
Advanced Imaging Techniques
Modern digital forensics requires mastery of multiple imaging approaches to handle diverse technology environments and evolving security measures.
Live System Imaging: Capturing system state while running to preserve volatile memory and active processes
Network-based Acquisition: Remote imaging of systems
Mobile Device Imagine
Quality assurance and legal admissibility
Adherence to strict quality assurance protocols.
Legal standard
Documentation
Chain of custody
Technical verification
Computer fingerprinting
Initial Hash Creation
32-character string generation
verification process: Matching string prove the image is comprehensive and unaltered
Visible Data
Active file: Documents, images. videos and applications accessible through the operating system’s file
System file: Operating system components, drivers and configuration files that maintain computer function
User-Created content: Personal document, downloads installed programs
Temporary files and swap space
Temporary file creation: store intermediate data from applications, system processes and user activities
Swap space function: When RAM reaches capacity, the system moves less frequently accessed data to swap space on the hard drive
Forensic significance: contains fragments of deleted files; preserves application sates; stores particle user inputs and maintains system activity logs
Data Swapping process
User switch between applications and perform multiple tasks, data continuously moves between RAM and the computer’s hard drive through sophisticated memory management
Ram storage 2. Memory pressure 3. hard drive swap
Latent Data
Hidden information
Forensic recovery
Investigation value: Often contains the most valuable forensic evidence including deleted files
Latent Data Categories
Deleted files
File slack- unused space within allocated file clusters
Registry Remnants
RAM Artifacts
Unallocated Space Concept
How data can persist even after deletion from the visible file system
Allocated Sectors: Areas of the hard drive actively used by the file system to store current files and system data
Unallocated sectors: Free space that may contain remnants of deleted files
Analysis of Internet Data
Internet Cache- Temporary files storing website content, images and scripts
Cookies: Small data files containing user preferences, login info and tracking data from visited web
Browser History: Chronological record of visited web, search queries and browsing patters
Bookmarks: Saved web links and favorite places and frequently accessed online resources
IP address
Unique ID- internet receives a unique IP address, serving as its digital postal address for network communication
Forensic Tracking: IP addresses (backbone of investigation) enable investigators to trace digital activities back to specific location, devices and internet servicer
Investigation of Internet Communications
Traffic Interception: Monitoring tools capture data packets traveling between computers during active communication sessions
Protocol Analysis: Exam the nature, timing and content of digital conversation
Content reconstruction- Tools reassemble fragmented communications to reconstruct complete messages
Evidence correlation- Multiple communication sources
Internet Communications Process
Source ID: Sending computer packages data with destination IP address info
Network Routing: Examine packet headers and forward data through optimal pathway toward the intended destination address
Delivery Confirmation: Receiving computer acknowledges successful packet receipt
Mobile Forensic
Comprehensive Data sources: Mobile devices provide vast amounts of evidentiary data
Preservation Challenges requires specialized containment methods that block communication signal without powering down the device
Extraction Complexity: Diversity of platforms operating system and security measures
Operating system
Android: Open source platform, making forensic analysis complex
IOS closed ecosystem requiring specialized tool for data extraction
Other platforms: BlackBerry, Windows…
Variability of Mobile Devices
Hardware differences
Security Features
Data storage
Application ecosystems
Connectivity options
Data extraction from Mobile devices
Device isolation: Secure the device in a Faraday container or airplane mode
Access Authentication: Bypass or overcome device security measures
Data Acquisition: Create bit by bit forensic images
Evidence Analysis: Parse extracted data to recover deleted files.