CS351 - Final Exam
1/192
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
193 Terms
Password is something the individual ____.
knows
Physical key is something the individual _____.
possesses
Fingerprint is something the individual ______.
is
Handwriting is something the individual ________.
does
Where does Microsoft store user passwords?
SAM file
How does Kerberos differ from NTLM?
Kerberos uses tickets for authentication, allowing for mutual authentication, while NTLM relies on a challenge-response mechanism and does not provide mutual authentication.
What is user authentication?
The process of establishing confidence in user identities that are presented electronically to an information system
What are the basic security requirements?
1. Identify information system users
2. Authenticate the identities of those users
What are some examples of derived security requirements?
1. multifactor authentication
2. replay-resistant authentication
3. prevent reuse of identifiers for a period
4. disable identifiers after period of inactivity
5. enforce minimum password complexity
6. prohibit password reuse
7. allow temp password use for system logons
8. store and transmit only crypto-protected passwords
9. obscure feedback of authentication info
What does Microsoft use to store all users and their hash passwords?
SAM file
How are passwords hashed in a SAM file?
NTLM Authentication Process
What does kerberos authentication use?
A ticketing granting server (TGS)
What is a passive online attack? Provide an example.
Attacker performs password hacking without communicating with the authorized party
ex: wire sniffing, replay
What is an active online attack? Provide an example.
Attacker tries a list of passwords one by one
ex: hash injection, password guessing, phishing
What is an offline attack? Provide an example.
Attacker copies the target's password file and then tries to crack passwords in his own system
ex: pre-computed hashes, rainbow table
What is a non-electronic attack? Provide an example.
Attacker need not posses technical knowledge to crack password, hence known as non-technical attack
ex: shoulder surfing, social engineering, dumpster diving
What is the most accurate but costly form of password?
A. Hand
B. Signature
C. Retina
D. Iris
E. Finger
D. Iris
What is the least accurate but cheapest form of password?
A. Hand
B. Signature
C. Retina
D. Iris
E. Finger
B. Signature
What is a dictionary attack?
Develop a large dictionary of possible passwords and try each against the password file
What is a rainbow table attack?
Trying to discover a password from a hash by comparing it to a database of precomputed hashes
What are the drawbacks of memory cards?
1. Require special reader
2. Loss of token
3. User dissatisfaction for computer use
What is an example of where memory cards are used?
Hotel Room, ATMs
What is remote user authentication?
Authentication over a network, the internet, or communications link
What are the security threats in remote user authentication?
1. eavesdropping
2. replay
What is a Client attack?
Adversary attempts to achieve user authentication without access to the remote host or the intervening communications path
What is a host attack?
Directed at the user file at the host where passwords, token passcodes, or biometric templates are stored
What is the typical defense against client attack?
large entropy (too many possible values to guess)
What is the typical defense against replay attack?
challenge-response protocol
What is the block size used by AES?
128 bits
What key lengths does AES support?
128, 192, and 256 bits
What algorithm was selected for AES?
Rijndael Algorithm
How many rounds does the AES cipher perform?
10 rounds, with the first 9 rounds including all 4 stages and the 10th round including 3 stages
What are the four stages used in each round of AES?
Substitute Bytes, ShiftRows, MixColumns, AddRoundKey
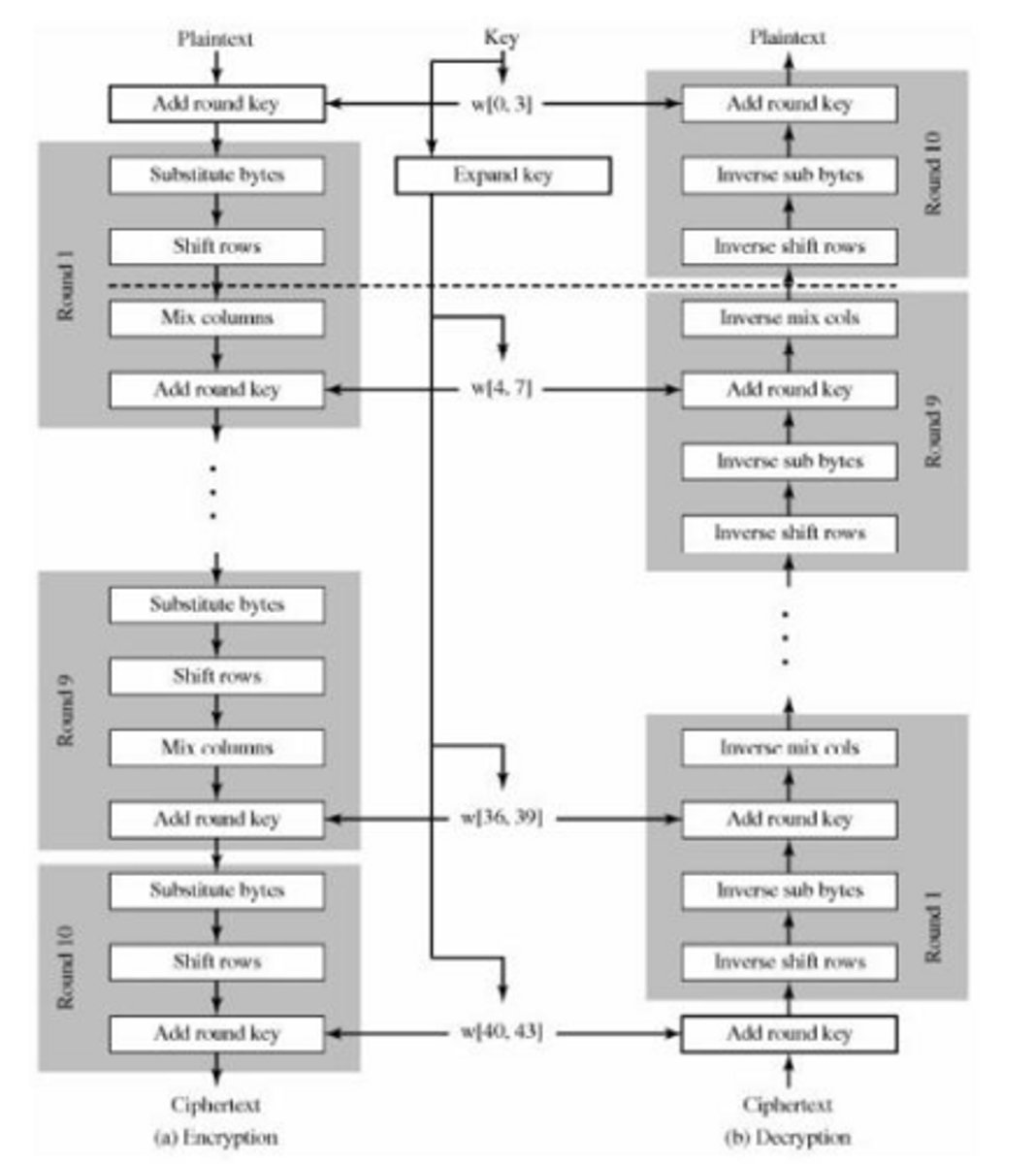
What is the first stage of the AES cipher?
AddRoundKey
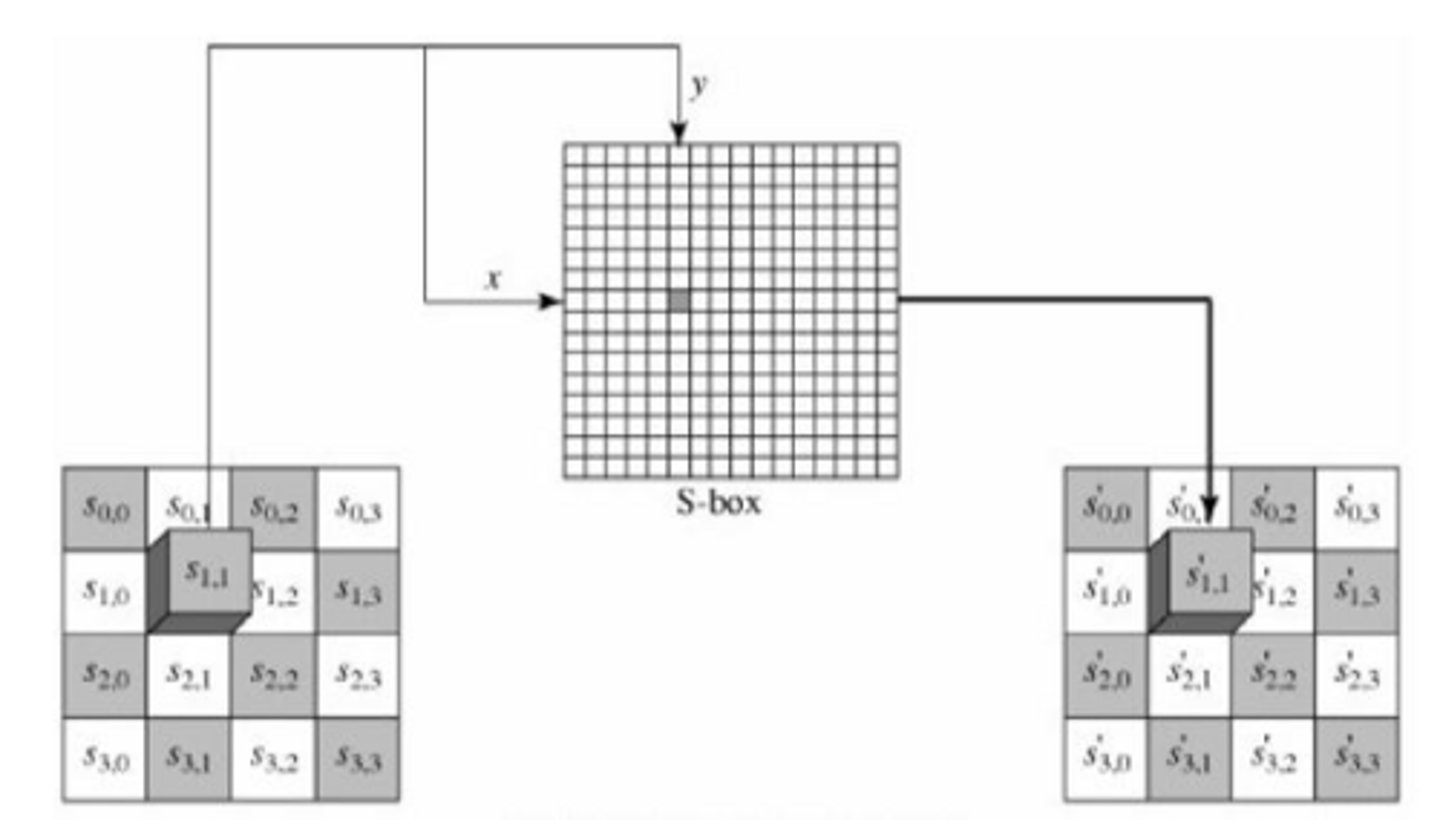
What transformation does the Substitute Byte stage use?
A 16 x 16 matrix of byte values called an S-box
How does the ShiftRow transformation alter the rows?
The first row is unchanged, the second row shifts left by 1 byte, the third by 2 bytes, and the fourth by 3 bytes.
What does the MixColumns transformation do?
Operates on each column individually, mapping each byte of a column into a new value.
What is the purpose of the AES key expansion algorithm?
To create new keys from the original key for each round.
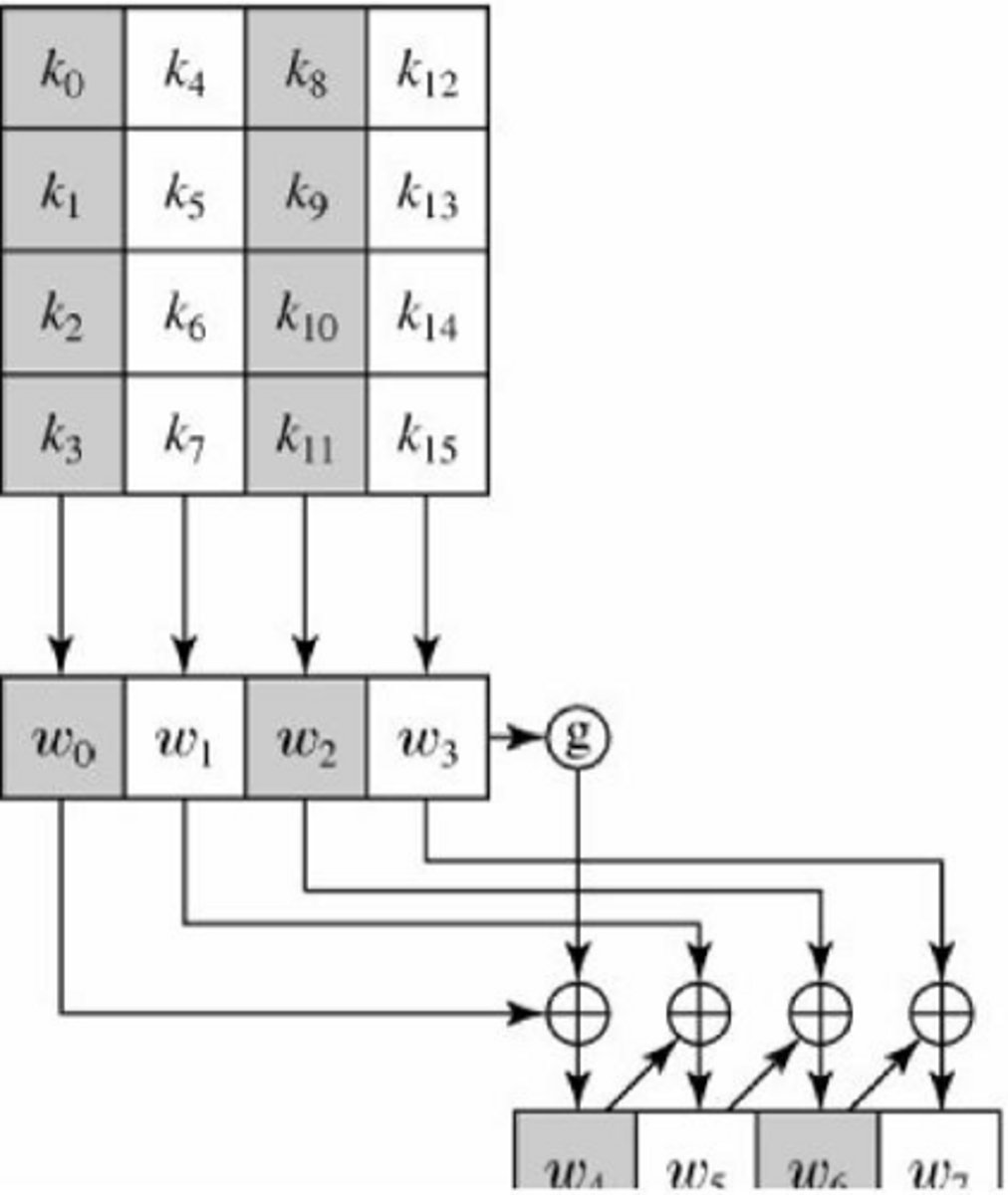
What is the first step in the key expansion process?
RotWord, which performs a one-byte circular left shift on a word.
What does the SubWord function do?
Performs a byte substitution on each byte of its input word using the S-box.
What is added to the result of SubWord in the key expansion?
A round constant, Rcon[j].
![<p>A round constant, Rcon[j].</p>](https://knowt-user-attachments.s3.amazonaws.com/caffd442-6398-451c-b613-25261b3e308a.jpg)
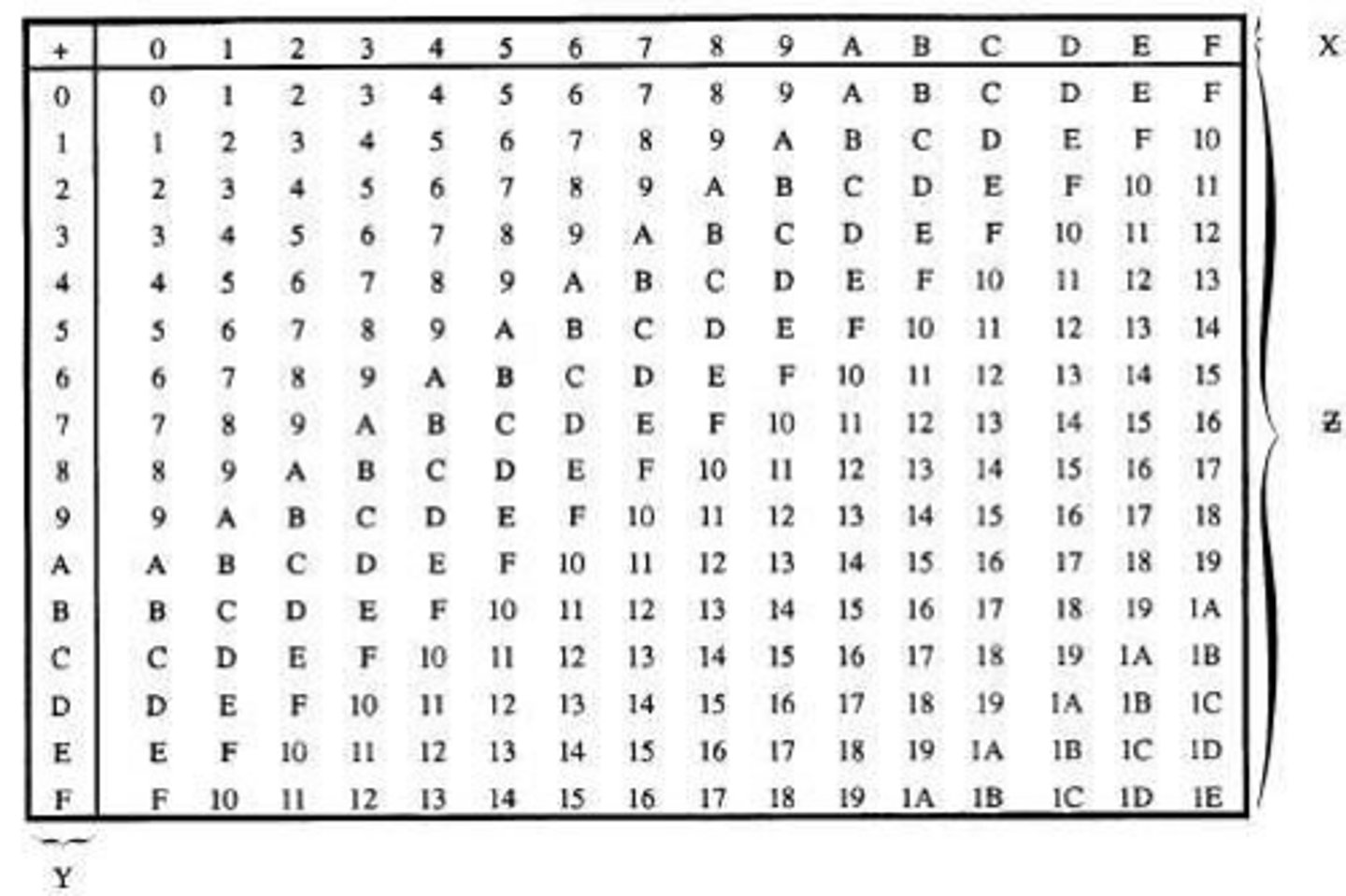
What is the result of the multiplication in the MixColumn transformation?
The sum of products of elements of one row and one column.
What is the significance of the hexadecimal addition table in AES?
It is used for the addition of results during the MixColumns transformation.
What happens to the first 4 bytes during key expansion?
They are shifted, substituted with the S-box, and XORed with a round dependent constant.
What does the term 'AddRoundKey' refer to in AES?
A stage where the round key is added to the state using XOR operation.
What is the final output of the AES encryption process?
The transformed state after the last round.
What is the main purpose of AES?
To provide a secure encryption standard to replace 3DES.
What is the primary difference between block ciphers and stream ciphers?
Block ciphers process messages in blocks, while stream ciphers process messages one bit or byte at a time.
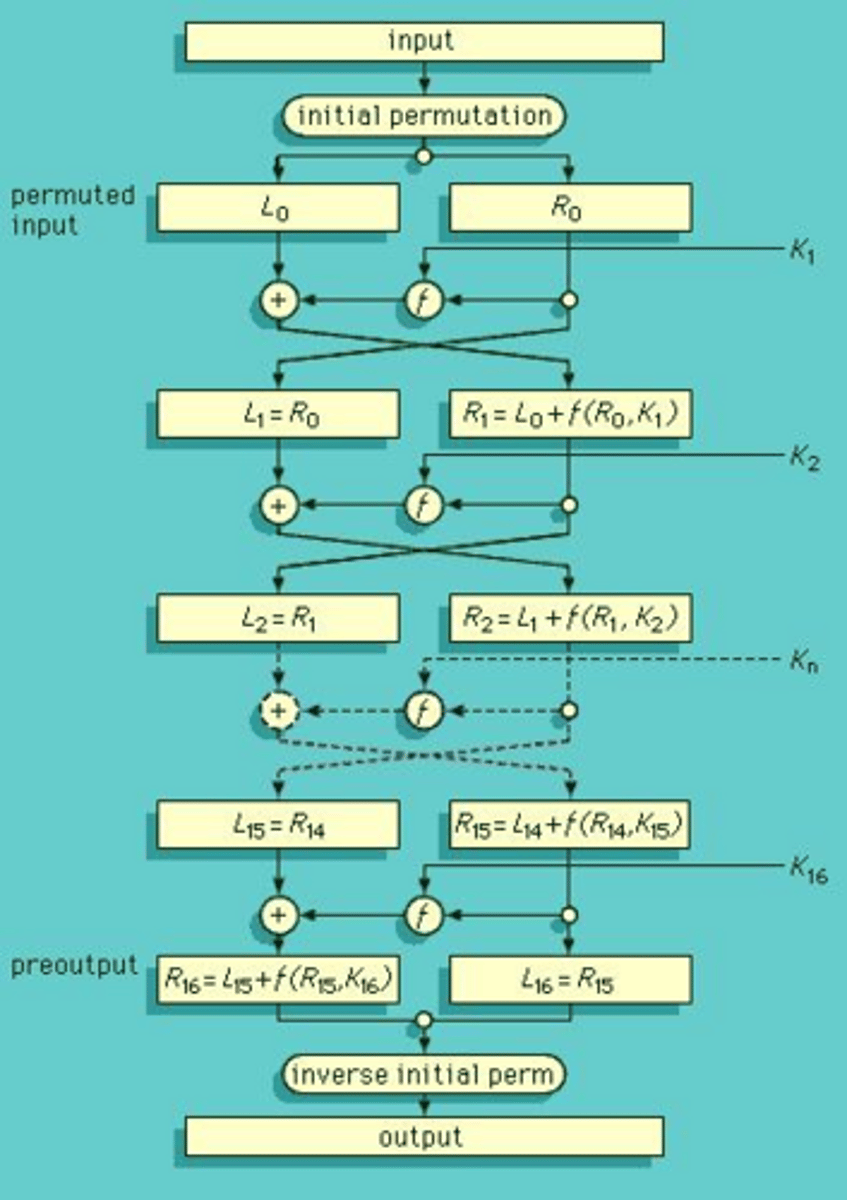
What is the purpose of the Feistel structure in block ciphers?
It partitions the input block into two halves and processes them through multiple rounds with substitutions and permutations.
What are the key factors that contribute to the security of a Feistel cipher?
Block size, key size, number of rounds, subkey generation algorithm, and speed of encryption/decryption.
What does DES stand for?
Data Encryption Standard
What is the block size used in DES?
64 bits
What is the key length used in DES?
56 bits
Describe the initial permutation (IP) in DES.
The initial permutation reorders the input data bits, distributing even bits to the left half and odd bits to the right half.
What is the function of the E-box in DES?
The E-box expands the 32-bit input to 48 bits, changing the order of bits and repeating certain bits.
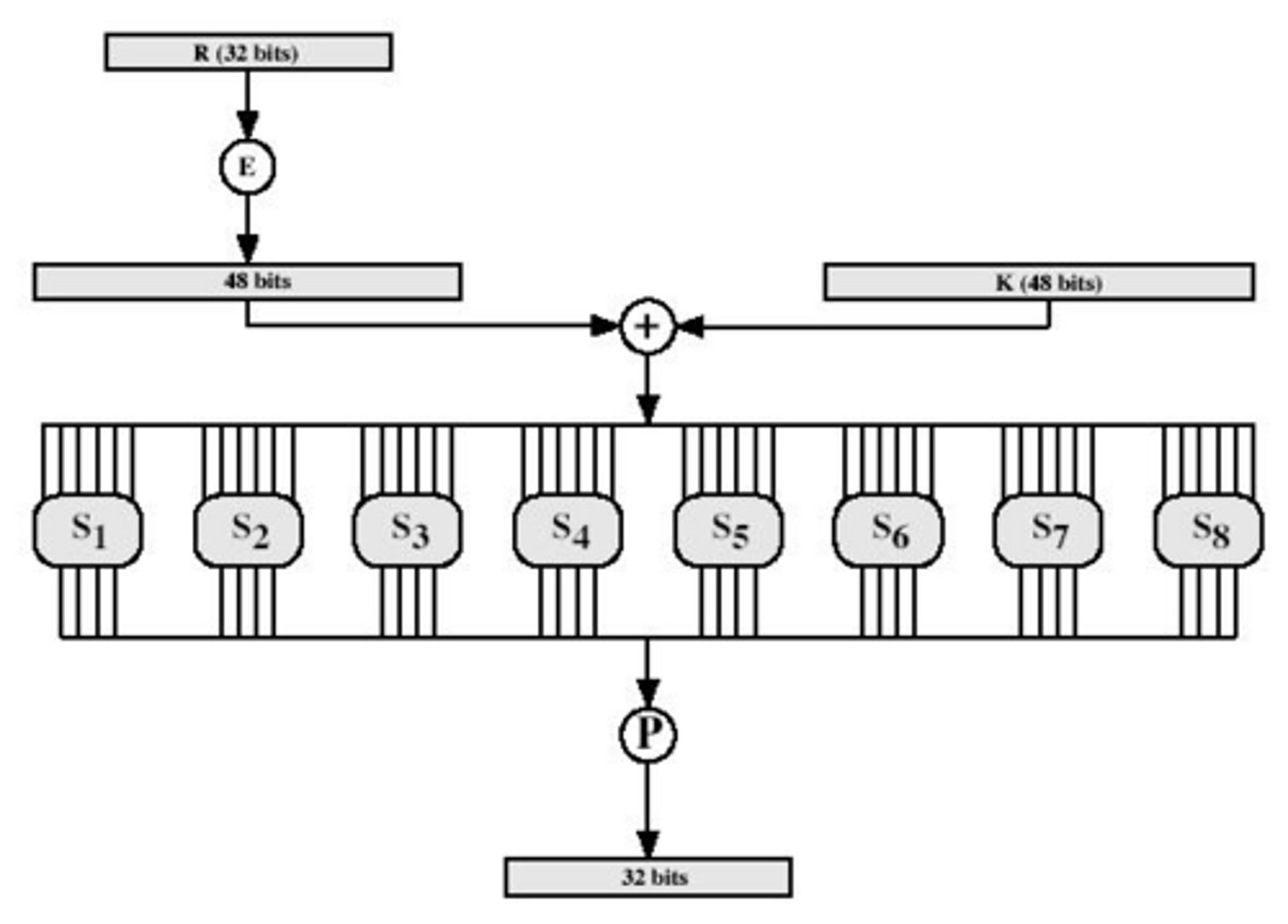
How many S-boxes are used in DES and what is their function?
Eight S-boxes are used to map 6 bits to 4 bits, providing substitution based on input bits.
What is the output of the S-box operation in DES?
The output is a 32-bit result after processing through all eight S-boxes.
What is the role of the P-box in DES?
The P-box performs a permutation on the output from the S-boxes, ensuring no bits are reused or ignored.
What is the key schedule in DES?
The key schedule forms subkeys for each round, involving initial permutation and rotations of key halves.
What is the brute force attack time estimated for breaking DES with a 56-bit key?
Approximately 1000 years.
What are the proposed solutions to enhance the security of DES?
Double DES and Triple DES.
What is the Electronic Codebook (ECB) mode?
A mode where messages are divided into independent blocks, each encrypted separately.
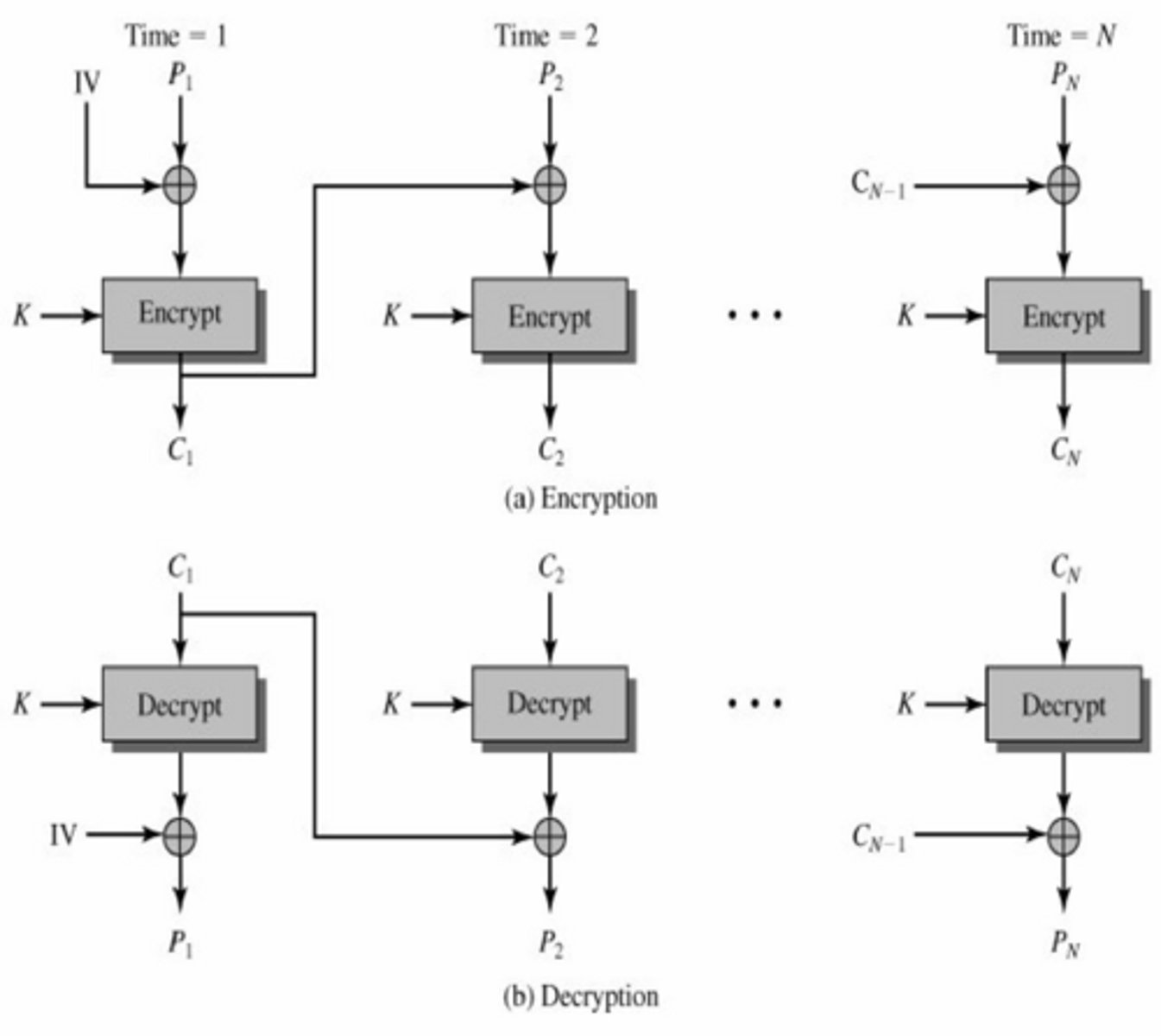
How does Cipher Block Chaining (CBC) mode work?
In CBC mode, each plaintext block is chained with the previous ciphertext block, using an initial vector (IV).
What is the main feature of Cipher Feedback (CFB) mode?
CFB treats the message as a stream of bits, feeding back the output of the block cipher for the next stage.
What distinguishes Output Feedback (OFB) mode from other modes?
OFB mode allows the output of the cipher to be computed in advance and is independent of the message.
What is the Counter Mode (CTR) in encryption?
CTR mode encrypts a counter value instead of feedback, requiring a unique key and counter for each plaintext block.
What is the significance of the Avalanche effect in cryptography?
The Avalanche effect ensures that a small change in input results in a significant change in output, enhancing security.
What is the relationship between the number of rounds in a Feistel cipher and its security?
More rounds generally increase security by making cryptanalysis more difficult.
What is the function of the subkey generation algorithm in DES?
It generates subkeys for each round, contributing to the overall complexity and security of the cipher.
What is the expected time to break DES using dedicated hardware, as demonstrated in 1998?
It took about 3 days.
What is the main advantage of using larger block sizes in block ciphers?
Larger block sizes generally provide greater security.
What does the term 'autoclaving' refer to in the context of S-boxes?
Autoclaving refers to the feature where row selection in S-boxes depends on both the data and the key.
What is the output of the DES encryption process after one complete round?
The output consists of the left and right halves after applying the round function and permutations.
How does the initial permutation affect the input data in DES?
It reorders the bits, distributing them into left and right halves for further processing.
What are the two main components of cryptography?
Encryption and Authentication & Integrity.
What does authentication ensure in cryptography?
That users of data/resources are who they claim to be and that a message has not been altered.
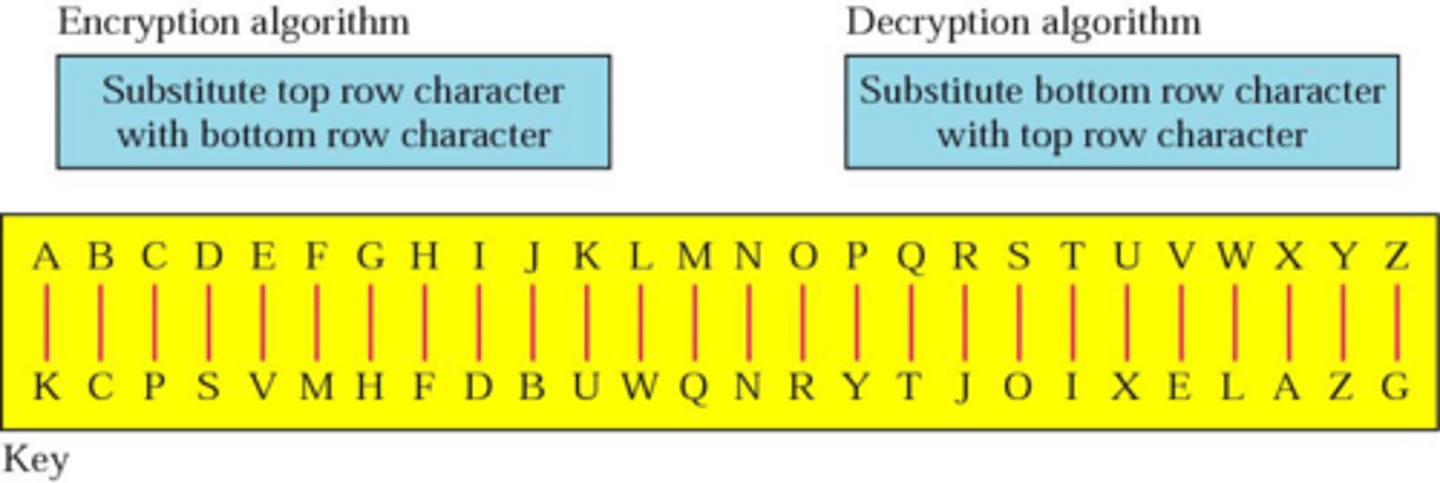
Name the categories of classical substitution ciphers.
Monoalphabetic, Polyalphabetic, Homophonic, and Polygram Ciphers.
What is a Monoalphabetic Substitution Cipher?
A cipher where each letter in the plaintext is replaced by a letter with a fixed relationship.
How does the Caesar Cipher work?
CT = E(pt, k) = (pt + k) mod 26 for encryption and PT = D(CT, k) = (CT - k) mod 26 for decryption.
What many tries are needed to decrypt caesar cipher?
25
What is a reciprocal cipher?
A cipher where if x -> Y, then y -> X, with the same procedure for encryption and decryption.
How many tries will it take to brute force Reciprocal Cipher?
25 x 23 x 21 x 19 ....
How many tries will it take to brute force a Random Cipher?
26!
What is a Polygram Cipher?
A cipher that performs multi-element encryption instead of element-by-element encryption.
How does the Playfair Cipher encrypt plaintext?
By constructing a 5x5 matrix and encrypting plaintext digrams according to specific rules.
What are polyalphabetic ciphers?
A PT letter maps to multiple CT letters
What is the Vigenere Cipher?
A polyalphabetic cipher that uses multiple monoalphabetic substitutions defined by a key.
What is the Vernam Cipher?
Choose a keyword that is as long as plaintext and has no statistical relationship to it
What is the One-Time Pad?
A polyalphabetic cipher that uses a random key as long as the message with no repetitions.
What is a classical transposition cipher?
A cipher that hides the message by rearranging the letter order without altering the actual letters.
How does the Railfence Cipher work?
Plaintext is written down as a sequence of diagonals and read off as a sequence of rows.
What is a Row Transposition Cipher?
A cipher where the message is written row-wise and read column-wise in a specific order.
What is the main problem with the One-Time Pad?
Generating large quantities of random keys and secure key distribution and storage.
What is the significance of the keyword in the Playfair Cipher?
It is used to fill the 5x5 matrix and determine the encryption of plaintext digrams.
What is the difference between symmetric and asymmetric encryption?
A symmetric encryption uses the same key for encryption as it does for decryption.
An asymmetric key uses different encryption keys for encryption and decryption.
What is the challenge of finding security weaknesses?
Attackers only need to find a single weakness, while the designer must eliminate all weaknesses for perfect security.
What are the key components of incident response for information systems?
Preparation, detection, analysis, containment, recovery, and reporting of incidents.
What are the categories of attack surfaces?
Network, software, and human attack surfaces.
Which organization deals with measurement science and standards in the U.S.?
National Institute of Standards and Technology (NIST).
What is the role of the Internet Society (ISOC)?
To provide leadership on issues affecting the future of the Internet.