9: Incident Handling Response and Governance
1/17
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
18 Terms
Security Event
Any observable occurrence in a system or network. Ex: User login, file access
Security Incident
An event that violates or threatens to violate security policy or standard practice. Ex: malware infection, DoS
Security Breach
A confirmed incident resulting in unauthorised access to sensitive data. Ex: Credentials stole, records leaked
Incident Response Lifecycle : NIST SP 800-61
1) Preparation
2) Detection & Analysis
3) Containment
4) Eradication
5) Recovery
6) Post-Incident Activity
Preparation
Policies & Procedures -
IRP, Playbooks & Runbooks, Communication protocols
Team & Tools -
Assign roles: manager, analyst, Deploy SIEM, IDS/IPS, Establish secure comm channels
Training & Testing -
Red team/Blue team drills, User awareness training, Test backup & recovery systems
Detection & Analysis
Detection Sources -
SIEM alerts and correlation rules, IDS/IPS signature & anomaly alerts, Antivirus notifications, User & helpdesk reports
Analysis Steps -
Validate Alert : eliminate false positives
Gather context : 4W
Classify severity : Low/Med/High/Critical
Determine scope : isolated/widespread
Preserve evidence : system logs, snapshots
Notify stakeholders per the escalation matrix
Containment
Short-term containment -
Isolate affected systems, Block malicious IPs at firewall, Disable compromised accounts
Long-term containment -
Apply temporary patches, Implement additional monitoring, Prepare clean systems for restoration
Eradication
Remove root cause completely:
Delete malware, rootkits, backdoors.
Patch exploited vulnerabilities, Reset all compromised credentials, Verify the integrity of critical files, Conduct antivirus scan
Recovery
Restore systems from clean backups
Gradually reconnect to production network
Monitor closely for signs of re-infection
Validate restoration
Change all passwords and rotate keys
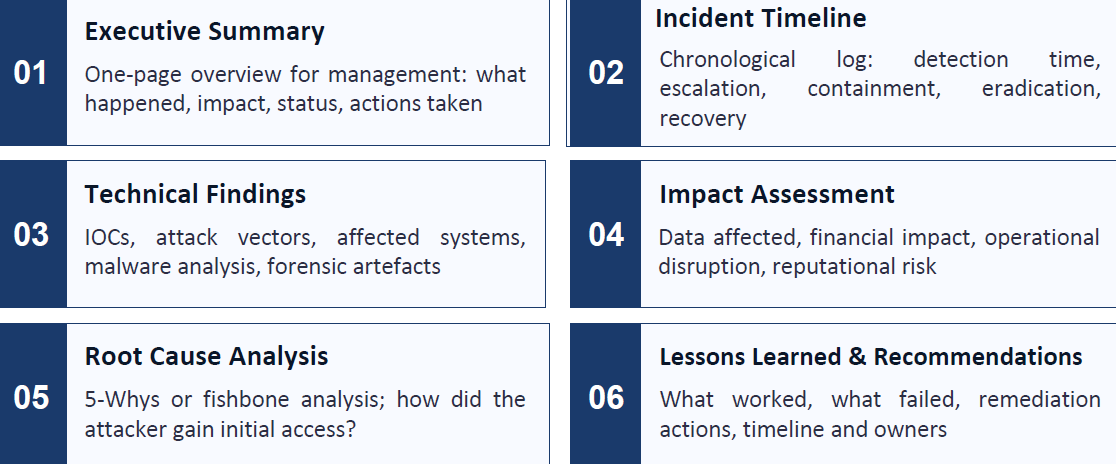
Post-Incident Activity
Produce formal incident report
Update IR plan based on findings
Improve detection rules & playbooks
Conduct lessons-learned meeting
Management & board-level briefings
Incident Response Team Structure
IR Manager = Leads response, authorises containment decisions, executive communication
SOC Analyst = Monitors alerts, triages events, performs initial investigation
Forensic Analyst = Evidence preservation, disk & memory forensics, chain of custody
Threat Intel = Provides TTP context, threat actor profiling
Legal/Compliance = Regulatory obligations, disclosure requirements
Communications = Internal & external messaging, PS, Customer notification
Governance Frameworks for Incident Response
NIST SP 800-61 Rev.2 = US NIST Standard, 6 phase lifecycle, adopted globally, free and detailed guidance.
ISO/IEC 27035 = International standard, 5 phase model, integrates with ISO 27001, risk-based approach.
SANS PICERL = Preparation ID Containment, Eradication Recovery Lessons, Practitioner focused
GDPR (Art. 33 & 34) = 72 hour breach notification, notify supervisory authority, applies to EU personal data
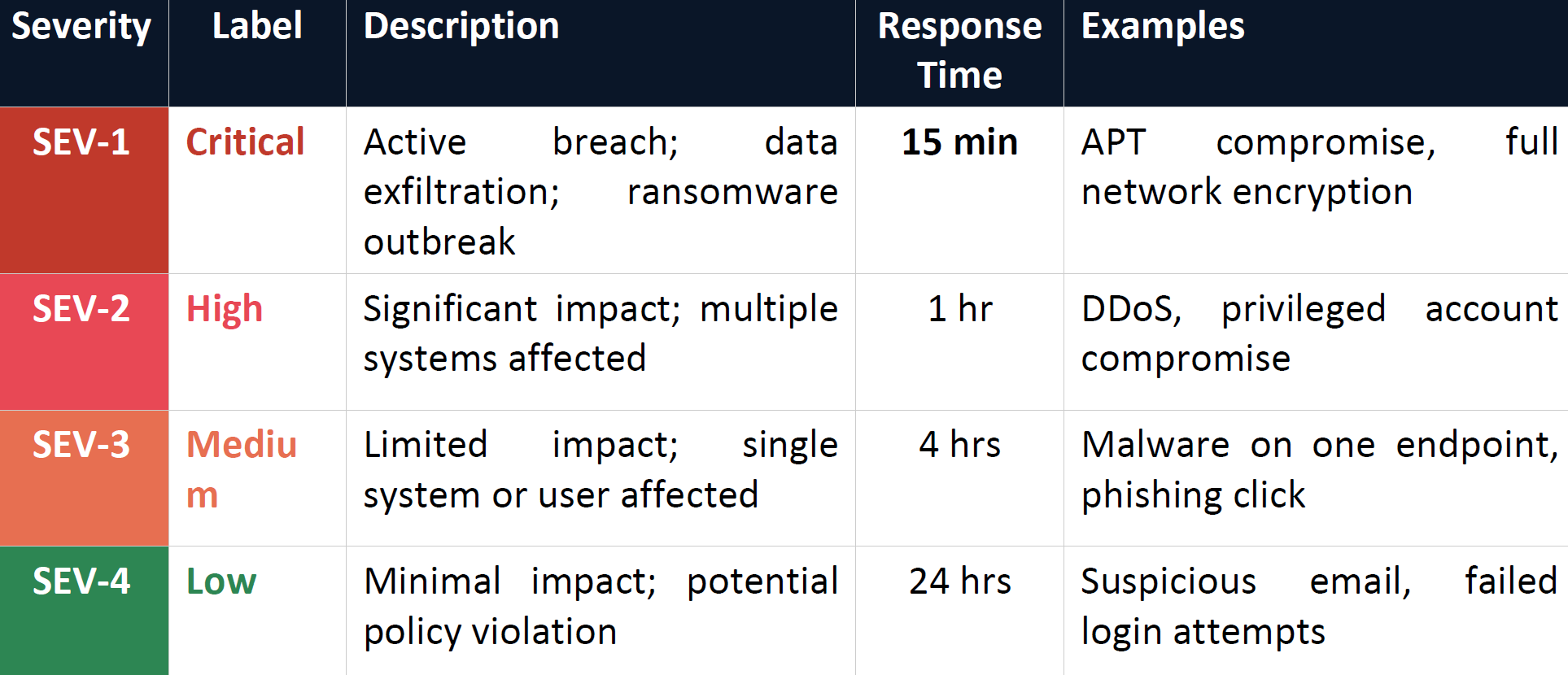
Incident Severity Classification
Types of Digital Evidence
Volatile (Collect 1st) - RAM, running processes, network connections
Semi-volatile - Temp files, registry
Non-volatile - Hard disk, SSD
Network - Firewall logs, Proxy logs
Application - Log files, Database records, Audit trails
Chain of Custody
Documents who handled evidence, when ,and how
Required fields: date/time, handler name, description, hash value
Use write-blockers for disk imaging (prevent modification)
Store evidence in tamper-evident containers/bags
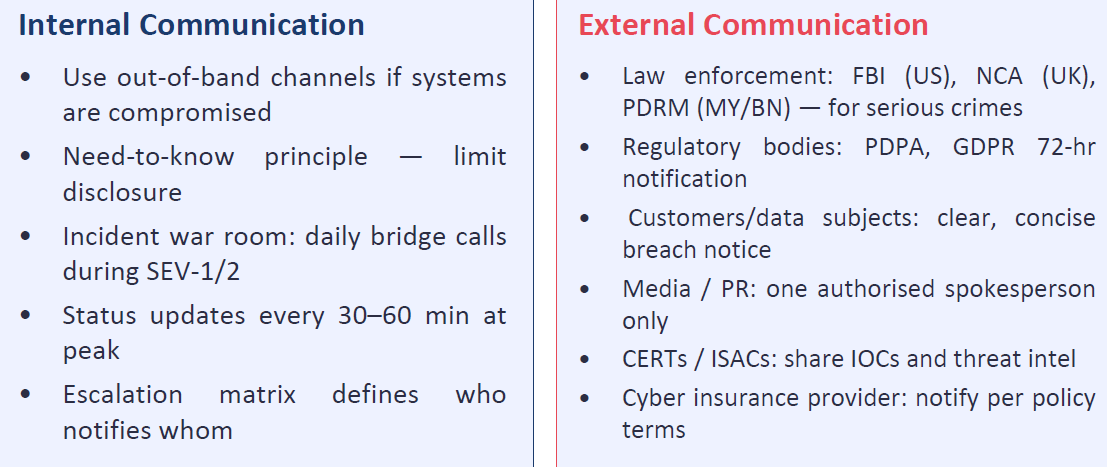
Communication & Escalation during Incidents
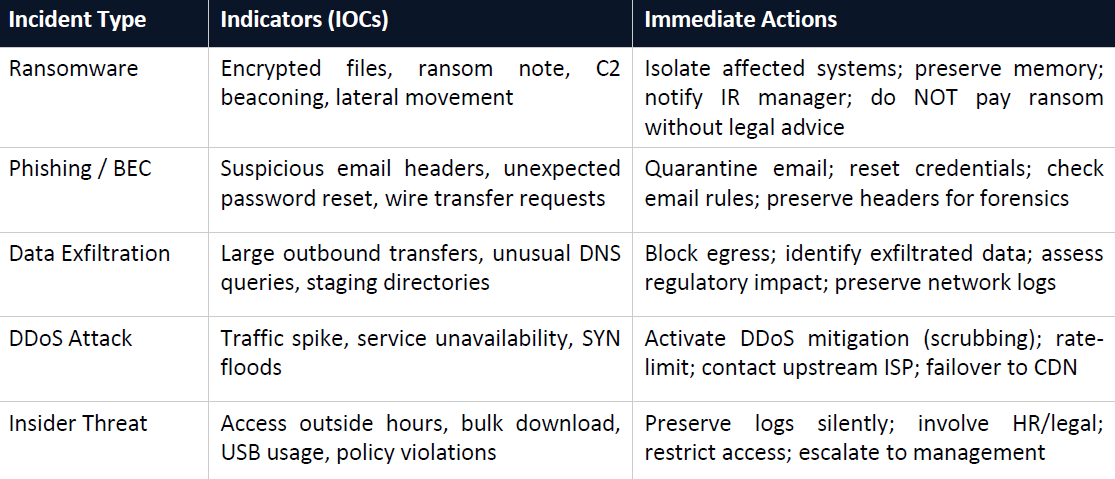
Common Incident Scenarios and Response Actions
Key Components of Incident Report