ICT: Theory and Blockly Concepts
0.0(0)
Studied by 4 peopleCard Sorting
1/65
Earn XP
Description and Tags
Last updated 11:19 PM on 11/15/22
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
66 Terms
1
New cards
Bit
The smallest unit of digital data which models two possibilities (0 or 1).
They are used to model numbers.
They are used to model numbers.
2
New cards
Byte
A group of 8 bits that models 2^8 = 256 possibilities.
3
New cards
Files
A collection of data where bits and bytes are organized in.
4
New cards
File size
[Property of a file] The number of bytes within a file.
5
New cards
File name
[Property of a file] A unique name for a file; is usually a descriptive name of the contents.
6
New cards
File extension
[Property of a file] The part of the file name that indicates what is stored in the file (.pdf, .png, .mp4)
7
New cards
Archive files
Files that can contain multiple files.
They are useful for transporting many files and also helps to reduce file size via compression.
They are useful for transporting many files and also helps to reduce file size via compression.
8
New cards
Software Applications
Programs (not systems) that can read, process, and write files.
9
New cards
Text-based Format
Designed in a way that humans can read them
Ex. HTML, CSV, XML
Ex. HTML, CSV, XML
10
New cards
Binary Format
Not readable by humans but can be efficiently processed by computers
They require less space and can be processed a bit faster
Ex. videos (.mp4), images (.png), audio (.mp3)
They require less space and can be processed a bit faster
Ex. videos (.mp4), images (.png), audio (.mp3)
11
New cards
The Internet
A network of computer networks that communicate short messages routed via many computers in the network.
12
New cards
Packet-switching
How communication over the Internet happens.
1. Messages are divided in small packets that are sent one by one
2. Every packet follows a different route via different computers
1. Messages are divided in small packets that are sent one by one
2. Every packet follows a different route via different computers
13
New cards
Properties of Packets
1. The address of a sender
2. The address of a receiver
3. Other properties related to time
4. The contents of the packet
2. The address of a receiver
3. Other properties related to time
4. The contents of the packet
14
New cards
Internet Protocol (IP) Addresses
How addresses in the internet are described
Their two main functions are:
1. Host or network interface identification
2. Location addressing
Their two main functions are:
1. Host or network interface identification
2. Location addressing
15
New cards
IPv4 Address
A unique 32-bit address with 2^32 different possibilities
Ex. 130.115.158.254
Ex. 130.115.158.254
16
New cards
IPv6 Address
A unique 128-bit address with 2^128 different possibilities
Ex. fe80::c118:3329:ca70:eccc%12
Ex. fe80::c118:3329:ca70:eccc%12
17
New cards
Domain Name System (DNS)
The system administered by the Internet Corporation for Assigned Names (ICANN) that assigns names to each site on the Internet.
Big sites may want to rotate machines to serve customers in order to spread out demand over the available capacity.
Big sites may want to rotate machines to serve customers in order to spread out demand over the available capacity.
18
New cards
Authentication
Checking someone's identity; knowing that you're communicating with the intended party.
19
New cards
Two-factor (multi-factor) authentication
An authentication method that uses multiple proofs of your identity to be able to log in
Ex. SMS, Push notifications in mobile apps
Ex. SMS, Push notifications in mobile apps
20
New cards
Token-based authentication
An authentication method that uses a special software/application to generate a number unique to that device.
21
New cards
Advanced Encryption Standard (AES)
A symmetric block cipher that is used to encrypt and decrypt messages.
The AES-256 works with keys of 256-bits.
The AES-256 works with keys of 256-bits.
22
New cards
Public Key/Certificate Encryption
A method of paired key encryption in which the key used to encrypt data is made available to anybody and its corresponding decryption key is kept secret.
23
New cards
Hypertext Transfer Protocol Secure (HTTPS) Protocol
An encrypted form of information transfer on the Internet that combines HTTP and a Secure Sockets Layer (SSL).
The protocol uses public keys/certificates to check whether a party you communicate with is trustworthy, then it encrypts the connection.
The protocol uses public keys/certificates to check whether a party you communicate with is trustworthy, then it encrypts the connection.
24
New cards
Redundancy
To duplicate files/software/hardware between users and/or machines to prevent or recover from the failure of a specific component or system.
25
New cards
Cases in which redundancy is desired
1. Archiving data
2. Having backup systems when software/hardware breaks
2. Having backup systems when software/hardware breaks
26
New cards
Cases in which redundancy is undesirable
When collaborating on a document with multiple users in which only one version must be used.
Ex. Google Docs
Ex. Google Docs
27
New cards
Synchronization
The coordination of hardware devices such that the data they contain or provide is made to be identical.
28
New cards
Centralization
Connecting all users to a central server/repository that stores complete and "true" network data and user information.
29
New cards
Conflicts that can occur when synchronizing
1. Two people modify the same file at the same time.
2. You modified a file, but it turns out another user sent a new file to the central repository in the meantime.
2. You modified a file, but it turns out another user sent a new file to the central repository in the meantime.
30
New cards
Local Applications
Applications that run on a local device and interact with data on that device.
31
New cards
Client-server Applications
Tasks and/or responsibilities are divided between a client application that typically runs on a local device and a server application that typically runs on an external server.
Ex. web browser (client application) and web server (server application)
Ex. web browser (client application) and web server (server application)
32
New cards
Advantage of Client-server Applications
Data is often centralized automatically on the server.
33
New cards
Risk of Client-server Applications
If the server has a problem, the application is not available for any user.
34
New cards
Infrastructure as a Service (IaaS)
Delivers hardware networking capabilities, including the use of servers, networking, and storage, over the cloud using a pay-per-use revenue model
35
New cards
Platform as a Service (PaaS)
Supports the deployment of entire systems including hardware, networking, and applications using a pay-per-use revenue model
36
New cards
Software as a Service (SaaS)
Delivers applications over the cloud using a pay-per-use revenue model
Ex. Google Suite and Office 365 (within a browser)
Ex. Google Suite and Office 365 (within a browser)
37
New cards
Data/Source Code Escrow
If the software vendor goes bankrupt, a third party inherits the important properties and provides them to the original customers.
38
New cards
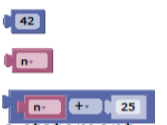
Expression (Blockly)
A block or group of blocks that have a value as a result.
39
New cards
Statement (Blockly)
A block that performs something.
40
New cards
Program
A sequence of instructions that specifies how to perform a computation to a computer.
41
New cards
[Program] Input
Getting data from a keyboard, a file, the network, some other device, etc.
42
New cards
[Program] Output
Displaying data on the screen, saving it in a file, sending it over the network, etc.
43
New cards
[Program] Math
Performing basic mathematical operations such as addition and multiplication.
44
New cards
[Program] Repetition
Performing some action repeatedly, usually with some variation.
45
New cards
[Program] Conditional Execution
Checking for certain conditions and running the appropriate code.
46
New cards
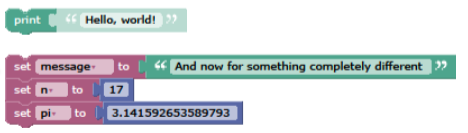
Print Statement
An instruction that causes Blockly to display a value on the screen.
47
New cards
Operator Blocks
Special blocks in Blockly that represent computations like addition, multiplication, or string concatenation.
48
New cards
Variable
A name that refers to a value.
49
New cards
Operand
An element that identifies one of the values on which an operator operates.
50
New cards
[Function block] Header
The name of the function and which possible input can be given.
51
New cards
[Function block] Body
The sequence of statements that make up/are within the function block.
52
New cards
[Function block] Parameter
A name used inside a function to refer to the value passed as an argument.
53
New cards
[Function Block] Argument
A value provided to a function when the function is called.
This value is assigned to the corresponding parameter in the function.
This value is assigned to the corresponding parameter in the function.
54
New cards
Logical Operator
One of the operators that combines boolean expressions: and, or, and not.
55
New cards
Relational Operator
Used to compare two values. Operators include =,
56
New cards
Branches of a Conditional Statement
The different alternatives of a conditional statement.
Ex. else if, else
Ex. else if, else
57
New cards
Flow of Execution
The order in which statements are executed during a program run, which in Blockly is from top to bottom.
58
New cards
Fruitful Function
A function that returns a result.
59
New cards
Void Function
A function that performs an action but does not return a value.
60
New cards
Runtime errors
Errors that occur while your program runs.
61
New cards
Semantic errors
Errors that occur as a result of an incorrect output, despite the working program.
62
New cards
Numeric data
Type of data that is formatted as numbers and can be used in a calculation.
63
New cards
Textual/string data
Type of data that is formatted as a string; letters, symbols, numbers.
64
New cards
Boolean data
Type of data that is formatted as "truth" values; true or false.
65
New cards
Dictionary Attack
A password attack that creates encrypted versions of common dictionary words and compares them against those in a stolen password file.
66
New cards
Brute Force attack
An attack on passwords or encryption that tries every possible password or encryption key.