Topic 2(Basic Switch and End Device Configuration)
1/83
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
84 Terms
Shell
The user interface that allows users to request specific
tasks from the computer. These requests can be made either through the CLI (Command Line Interface) or GUI (Graphical User Interface).
Kernel
Communicates between the hardware and software of a
computer and manages how hardware resources are used to meet software requirements.
Hardware
The physical part of a computer including underlying electronics.
Command-line interface
What does CLI stand for ?
CLI
enables a network technician to do the
following:
• Use a keyboard to run Command-line based network
programs
• Use a keyboard to enter text and text-based
commands
• View output on a monitor
Console
A physical management port used to access a device in order to provide maintenance, such as performing the initial configurations.
Secure Shell (SSH)
Establishes a secure remote CLI connection to a device,
through a virtual interface, over a network. (Note: This is the recommended method for remotely connecting to a device.)
Telnet
Establishes an insecure remote CLI connection to a device over the
network. (Note: User authentication, passwords and commands are sent over the network in plaintext.)
Terminal emulation programs
are used to connect to a network device
by either a console port or by an
SSH/Telnet connection.
PuTTy
give 1 example of terminal emaulation program
User Exec Mode
Allows access to only a limited
number of basic monitoring
commands
User Exec Mode
Identified by the CLI prompt that ends
with the > symbol
Privileged EXEC Mode
Allows access to all commands and features
Privileged EXEC Mode
Identified by the CLI prompt that ends with the # symbol
Global Configuration Mode
Used to access configuration options on the device
Line and Interface Configuration Mode
What are the two Subconfiguration Modes?
Line Configuration Mode
Used to configure console, SSH, Telnet or AUX access
Interface Configuration Mode
Used to configure a switch port or router interface
enable/en
To move from user EXEC mode to privilege EXEC mode, use the _______command.
configure terminal/conf t
To move in and out of global configuration
mode, use the ______________
command.
exit/end
To close a session in a command line interface.
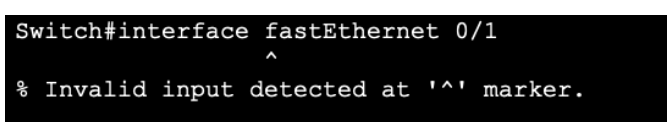
interface FastEthernet 0/1
To move directly from one subconfiguration mode to another, type in the desired subconfiguration mode command. In the example, the command prompt changes from (config-line)# to (config-if)#.
Keyword
This is a specific parameter defined in the operating system.
Argument
This is not predefined; it is a value or variable defined by the user.
Context Sensitive Help
enables you to quickly find answers to these questions:
• Which commands are available in each
command mode?
• Which commands start with specific characters
or group of characters?
• Which arguments and keywords are available
to particular commands?
?
what command to use context sensitive help?
Command syntax check
verifies that a valid command was entered by the user.
• If the interpreter cannot understand the command being entered, it will provide feedback describing what is wrong with the command.
Tab
Completes a partial command name entry.
Backspace
Erases the character to the left of the cursor.
Left Arrow/Ctrl+B
Moves the cursor one character to the left.
Right Arrow/Ctrl+F
Moves the cursor one character to the right.
Up Arrow/Ctrl+P
Recalls the commands in the history buffer, beginning with the most recent commands.
—More—
When a command output produces more text
than can be displayed in a terminal window, the
IOS will display a “______” prompt.
Enter
Displays the next line.
Space Bar
Displays the next screen.
Any other key
Ends the display string, returning to privileged EXEC mode.
Ctrl+C or Z
When in any configuration mode, ends the configuration mode and returns to privileged EXEC mode.
Ctrl+Shift+6
All-purpose break sequence used to
abort DNS lookups, traceroutes,
pings, etc.
Device Names
• The first configuration command on any device should be to give it a unique hostname.
• By default, all devices are assigned a factory default name. For example, a Cisco IOS
switch is "Switch.”
line console 0
To move in and out of line configuration
mode, use the ______ command followed by
the management line type.
en, conf t, line console 0, password cisco, login, end
What are the commands to apply the password for User Exec Mode, in the console.
en, conf t, enable secret class, exit
what are the commands to configure password when entering Privileged Exec Mode?
conf t, line vty 0 15, password cisco, login, end
what are the steps in securing vty line access
VTY lines
enable remote access using Telnet or SSH to the device.
service password-encryption
To encrypt all plaintext passwords, use the _______________ global config command.
Encrypt Passwords
The startup-config and running-config files display most passwords in plaintext.
show running-config
Use the ____________ command to verify that the passwords on the device are now encrypted.
banner messages
is important to warn unauthorized personnel from attempting to access the device.
banner motd #—#
To create a banner message of the day on a network device, use the _______ the message of the day # global config command.
#
in the command syntax is called
the delimiting character. It is entered before
and after the message.
startup-config file
Contains all the commands that will be used by the device upon startup or reboot.
startup-config file
Saved configuration file stored in NVRAM (non volatile RAM – its content is not lost when the device is powered off).
Non volatile ram
NVRM stands for?
running-config file
Current configuration file stored in Random Access Memory (RAM). RAM is volatile memory, its content is lost when the device is powered off or restarted.
True
TRUE OR FALSE:
Changing the running configuration affects the operation of a Cisco device immediately.
copy running-config startup-config
To save changes made to the running configuration to the startup configuration file, use the command ____________________ in the privileged EXEC mode.
show
Use the ____ command to view the configurations files as indicated below.
reload then enter
If changes made to the running config do not have the desired effect and the running-config has
not yet been saved, you can restore the device to its previous configuration:
• Remove the changed commands individually, or
• ______ the device using the ______ command in privilege EXEC mode.
erase startup-config then enter
If the undesired changes were saved to the startup-config, it may be necessary to clear all the configurations
IP address
Locate one another
IP address
Establish end-to-end communication on the internet.
dotted decimal notation
The structure of an IPv4 address is called __________ and is represented by four decimal numbers between 0 and 255.
32 bit
An IPv4 subnet mask is a _____ value
Subnet mask/IPv4 mask
Differentiates the network portion of the address from the host portion
Subnet mask
Determines to which subnet the device is a member.
Default gateway address
is the IP address of the router interface that the host will use to access remote networks, including the Internet.
Dynamic Host Configuration Protocol
What does dhcp stand for
Control panel, network sharing center, change adapter settings, properties, internet protocol 4, properties, Obtain an IP address
automatically, Obtain DNS server address
automatically
To configure DHCP on a Windows PC
Control panel, network sharing center, change adapter settings, properties, internet protocol 4, properties
To manually configure an IPv4 address on a
Windows PC?
conf t, interface vlan 1, ip address ip address subnet mask, no shutdown
To configure an SVI on a switch:
ping
Use the ____ command to test
connectivity to another device.
show ip interface brief
Use command _______ to verify the interfaces and address settings
ipconfig
Use command _____ to display the IP configuration on a Windows PC
Ctrl+Shift+6
interrupts the ping process
Console, Secure Shell (SSH), Telnet
What are the three ways a user can access the Cisco IOS
Privileged Exec Mode
allows access to all commands and features.
Context Sensitive Help
Enables us to quickly find answers to the questions
reload
it causes the device to briefly go offline, leading to network downtime.
IP address
Dotted Decimal, 4 decimal numbers between 0 and 255.
IPv4 mask
a 32 bit that differentiates the network position of the address from the host portion.
DHCP
enables automatic IPv4 address configuration for every end device that are DHCP-enabled.
ping
what command is used to verify the end-to-end commectivity?
to access the switch remotely
What is the purpose of configuring an IP Address and a subnet mask on SVI (VLAN
1) on a Switch?
Default Gateway address
the ip address of the router that the host will use to access remote networks, including the internet.