WGU D430 EXAM PREP/COMPREHENSIVE GUIDE 2026 | ALL QUESTIONS AND CORRECT ANSWERS | NEWEST EXAM | GRADED A+ | VERIFIED ANSWERS | WESTERN GOVERNORS UNIVERSITY
1/94
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
95 Terms
Define the confidentiality in the CIA triad.
Our ability to protect data from those who are not authorized to view it.
Examples of confidentiality
A patron using an ATM card wants to keep their PIN number confidential.
An ATM owner wants to keep bank account numbers confidential.
How can confidentiality be broken?
Losing a laptop
An attacker gets access to info
A person can look over your shoulder
Define integrity in the CIA triad.
The ability to prevent people from changing your data and the ability to reverse unwanted changes.
How do you control integrity?
Permissions restrict what users can do (read, write, etc.)
Examples of integrity
Data used by a doctor to make medical decisions needs to be correct or the patient can die.
Define the availability in the CIA triad.
Our data needs to be accessible when we need it.
How can availability be broken?
Loss of power, application problems. If caused by an attacker, this is a Denial of Service attack.
Define information security.
The protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction in order to provide confidentiality, integrity, and availability.
Define the Parkerian Hexad and its principles.
The Parkerian Hexad includes confidentiality, integrity, and availability from the CIA triad. It also includes possession (or control), authenticity, and utility.
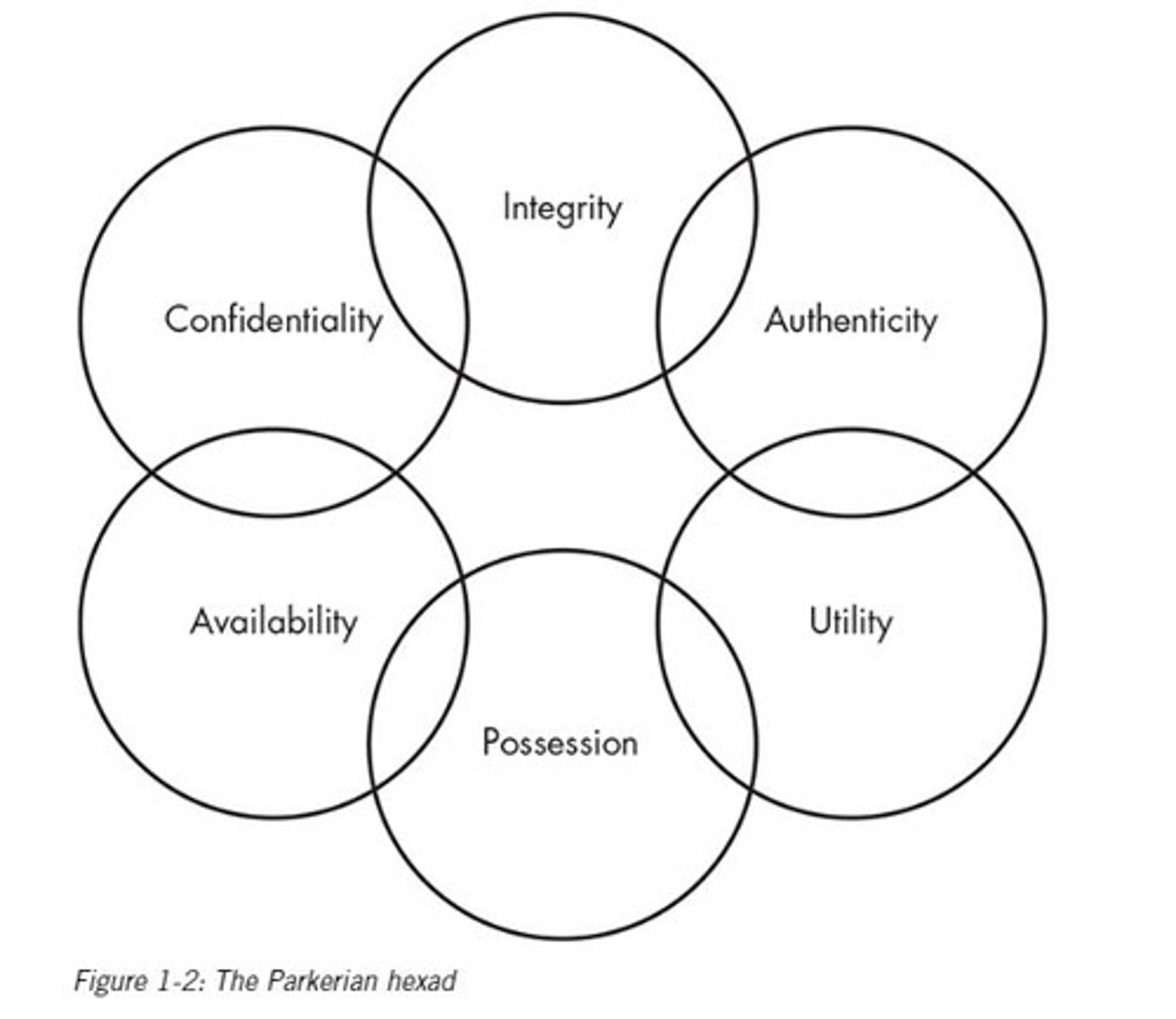
Authenticity
Whether the data in question comes from who or where it says it comes from (i.e. did this person actually send this email?)
Confidentiality is affected by what type of attack?
Interception (eaves dropping)
Integrity is affected by what type of attacks?
Interruption (assets are unusable), modification (tampering with an asset), fabrication (generating false data)
Authenticity is affected by what type of attacks?
Interruption (assets are unusable), modification (tampering with an asset), fabrication (generating false data)
Utility
How useful the data is to you (can be a spectrum, not just yes or no)
Possession
Do you physically have the data in question? Used to describe the scope of a loss
Identify the four types of attacks
interception, interruption, modification, and fabrication
Interception attacks
Make your assets unusable or unavailable
Interruption attacks
cause assets to become unusable or unavailable for our use, on a temporary or permanent basis
Modification attacks
Tampering with an asset
Fabrication attacks
Generating data, process, and communications
Define the risk management process
1. Identify assets
2. Identify threats
3. Assess vulnerabilities
4. Assess risks
5. Mitigate risks
Define the incident response process and its stages.
Preparation
Detection and analysis
Containment
Eradication
Recovery
Preparation in incident response
creating policies and procedures
Detection in incident response
Using tools and humans to decide if an incident is an incident
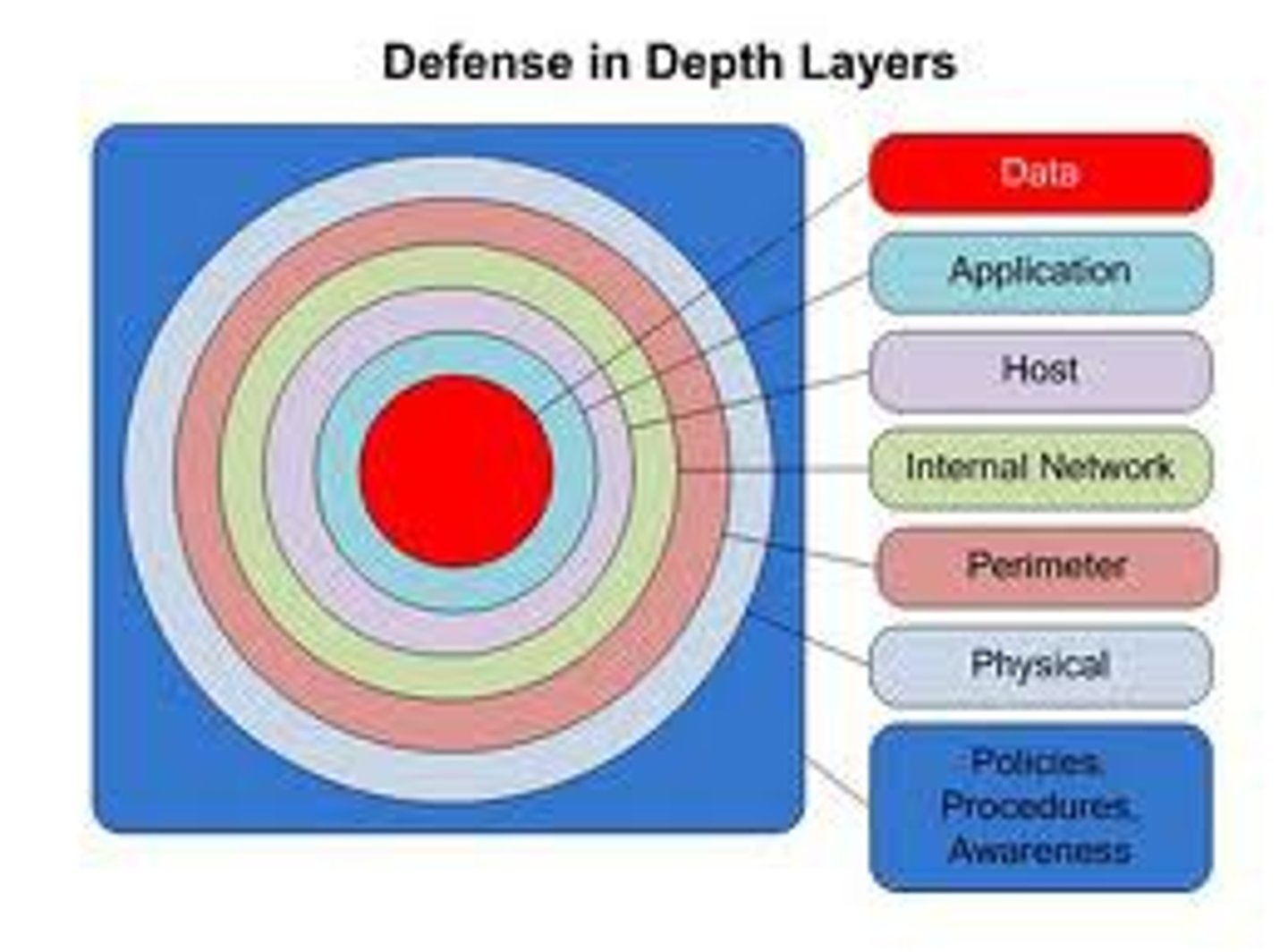
Defense in Depth
employing multiple layers of controls to avoid a single point of failure
Identify types of controls to mitigate risk
physical, logical, administrative
Identify elements of risk management in policies and procedures.
Development of robust policies
Identification of emergent recent
Identify elements of internal weakness
Identify the layers of a defense-in-depth strategy.
External network
Internal network
Host
Application
Data
Define identification
The claim of who we/networks are
Define identity verification.
Someone claims who they are and you take it one step father and ask for ID
Define authentication
A set of methods used to determine if a claim of identity is true.
Compare authentication types.
Multifactor authentication
Mutual authentication
Identify password security best practices.
Upper case
Lower case
Numbers
Symbols
Identify the factors involved in a multifactor authentication technique.
Something you do
Something you have
Where you are
Define accountability and its benefits
nonrepudiation, deterrence, intrusion detection and prevention, and admissibility of records
Auditing
Hold users of your system accountable. A methodical examination and review of an organization's records.
nonrepudiation measures
make it so that someone can't send an email and then deny sending it. usually with a digital signature.
Which standards apply to any financial entity policies?
Gramm-Leech-Bliley
Which standards apply to publicly traded companies doing business in the U.S?
Sarbanes-Oxley Act (SOX)
Which standards apply to credit card industry?
PCI DSS
Which characteristic falls under accountability?
Identity
What company audits other companies for licensing requirements?
BSA
Define cryptography, including its origins and influencers.
The science of protecting the confidentiality and integrity of data
symmetric key cryptography
the sender and receiver use the same key for encryption and decryption
Asymmetric Key Cryptography
Encryption that uses two separate keys- a public key and a private key. Advantage is that you can post the public key and anyone can send you an encrypted message.
Hash functions
mathematical algorithms that generate a message summary or digest (sometimes called a fingerprint) to confirm message identity and integrity
digital signature
a means of electronically signing a document with data that cannot be forged
Digital certificate
Link a public key to an individual
Protecting data at rest
use encryption and physical security
Protecting data in motion
use encryption, protect the connection with a VPN,
Protecting data in use
We are somewhat limited in our ability to protect data while it is being used by those who legitimately have access to it. Authorized users can print files, move them to other machines or storage devices, etc.
Rivest-Shamir-Adleman
encryption algorithm
Which term is synonymous with symmetric cryptography?
Secret key cryptography
Which term is synonymous with asymmetric cryptography?
Public key cryptography
regulatory compliance
Regulations mandated by law usually requiring regular audits and assessments
industry compliance
Regulations or standards designed for specific industries that may impact ability to conduct business (e.g. PCI DSS)
privacy
the right of people not to reveal information about themselves
GLBA
"Graham-Leach-Bliley Act" (Financial Services Modernization Act of 1999) repealed a 1933 law that barred the consolidation of financial institutions and insurance companies. Included within GLBA are multiple sections relating to the privacy of financial information. Companies must provide written notice to consumers of their privacy rights and explain the company's procedures for safeguarding data.
Privacy guidelines
Guidelines to follow to protect private information of patients
FISMA
federal info security management act - US law requires federal agencies to create, document and implement security program
HIPPA
Health Insurance Portability and Accountability Act. Protects patient privacy.
FERPA
Family Educational Rights and Privacy Act
SOX
Sarbanes-Oxley Act. This law requires publicly traded companies and their independent auditors to demonstrate that their numbers are accurate and that they have processes in place to ensure accurate reporting. Several sections of the law have important implications for human resource activities.
Industry compliance vs. Regulatory compliance
Industry compliance isn't enforced by the government, like regulatory compliance. It's a group of stakeholders in the industry that get together and decide what compliance looks like.
COPPA
Children's Online Privacy Protection Act
ECC
Asymmetric Key Algorithm, provides encryption, digital signatures, key exchange, based on the idea of using points on a curve to define the public/private key, used in wireless devices and smart cards
RSA
asymmetric algorithm
SHA
hashing algorithm
DES
block cipher symmetric algorithm
MD5
Message Digest 5. A hashing function used to provide integrity.
PGP
Pretty Good Privacy. Commonly used to secure e-mail communications between two private individuals but is also used in companies. It provides confidentiality, integrity, authentication, and non-repudiation. It can digitally sign and encrypt e-mail. It uses both asymmetric and symmetric encryption.
Operations Security Process
1. Identification of critical information
2. Analysis of threats
3. Analysis of vulnerabilities
4. Assessment of risks
5. Application of countermeasures
Operations Security
A security and risk management process that prevents sensitive information from getting in the wrong hands.
Competitive intelligence
the process of gathering and analyzing information to support business decisions
Haase's Laws: Know the threats
If you don't know the threat, how do you know what to protect? Know the threats for your data based on your location.
Haase's Laws: Know what to protect
If you don't know what to protect, how do you know you're protecting it? Some orgs classify information (top secret).
Hasse's Laws: Protect the information
If you don't protect the information, your adversaries win.
Human Element Security
Security Awareness, Training, and Education (SATE)
Pretexting
a form of social engineering in which one individual lies to obtain confidential data about another individual
Phishing
An attack that sends an email or displays a Web announcement that falsely claims to be from a legitimate enterprise in an attempt to trick the user into surrendering private information
competitive intelligence
the process of intelligence gathering and analysis to support business decisions
Competitive Counterintelligence
the practice of managing the range of intelligence-gathering activities directed at an organization
Network-based IDS (NIDS)
an independent platform that monitors network traffic to identify intruders.
host-based IDS
are used to analyze the activities on or directed at the network interface of a particular asset (host).
Wireshark
a sniffer that is capable of intercepting and troubleshooting traffic from both wired and wireless sources.
Nmap
A network utility designed to scan a network and create a map. Frequently used as a vulnerability scanner.
Which port service needs to be removed when running a webserver?
53
Port 80
provides Hypertext Transfer Protocol (HTTP) services, which serves Web content.
AES
AES is the standard encryption algorithm used by the US Federal government.
SSRF
(Server-Side Request Forgery) An attack that takes advantage of a trusting relationship between web servers. Attacker finds vulnerable web application, sends request to web server, web server performs request on behalf of attacker.
kismet
Kismet is a tool commonly used to detect wireless access points.
Hping3
A tool used to test the security of firewalls and map network topology.
- constructs specially crafted ICMP packets to evade measures to hide devices behind firewall
- scripting functionality to test firewall/IDS
Burp Suite
Burp Suite is a web assessment and analysis tool that looks for issues on websites such as cross-site scripting or SQL injection flaws.
Fuzzer
A type of tool that works by bombarding our applications with all manner of data and inputs from a wide variety of sources, in the hope that we can cause the application to fail or to perform in unexpected ways