Processes
1/35
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
36 Terms
What is a simple Mini-OS?
user programs
use system call interface (API)
API connects to kernel
kernel manages:
process management
memory management
file system management
I/O control
kernel controls hardware:
CPU
RAM
devices
What are CPU registers?
very small, very fast storage inside CPU
faster than main memory
used during program execution
each register has a specific role
OS uses them in process management and system control
What are the main types of CPU registers?
general-purpose registers
temporary data
arithmetic
addresses
calculation results
special-purpose registers
PC / IP = address of next instruction
SP = top of stack
BP = references variables in stack
flags register (FR) = stores status flags like zero, carry, overflow
What are the different sets of CPU registers?
segment registers
store addresses of memory segments
e.g. code CS, data DS, stack SS
floating-point registers
used for decimal / floating-point arithmetic
vector registers (SIMD)
process multiple data values at the same time
control registers
control CPU/system behavior
used for system control, interrupts, modes
What are the main general-purpose registers and their roles?
EAX (Extended Accumulator Register)= main accumulator, arithmetic default register
EBX (Extended Base Register)= base register, memory addressing
ECX (Extended Counter Register)= counter register, loops/iterations
EDX (Extended Data Register) = data register, extra arithmetic data/results
What are the additional general-purpose registers?
ESI (Extended Source Index)= source index
EDI (Extended Destination Index) = destination index
EBP (Extended Base Pointer) = base/frame pointer
ESP (Extended Stack Pointer)= stack pointer (top of stack)
What are protection rings, user mode/kernel mode, and system calls?
2 modes:
user mode = applications run here
kernel mode = OS/kernel runs here
privileged operations
only allowed in kernel mode
if a user program tries them → CPU fault/error
protection rings (x86)
Ring 0 = highest privilege, kernel
Ring 3 = lowest privilege, applications
Rings 1 and 2 exist, but modern OSs mainly use Ring 0 and Ring 3
system calls
way for a program to request services from the kernel
interface between process and operating system
examples:
hardware access
create/run processes
scheduling / kernel services
**A process is a program that is currently running.
How do system calls work?
application runs in Ring 3
when it needs OS service, it makes a system call
CPU switches to Ring 0 / kernel mode
kernel dispatcher/handler executes the request
control returns to the application
What are Linux system calls used for?
read data
write data
open file
close file
get file information
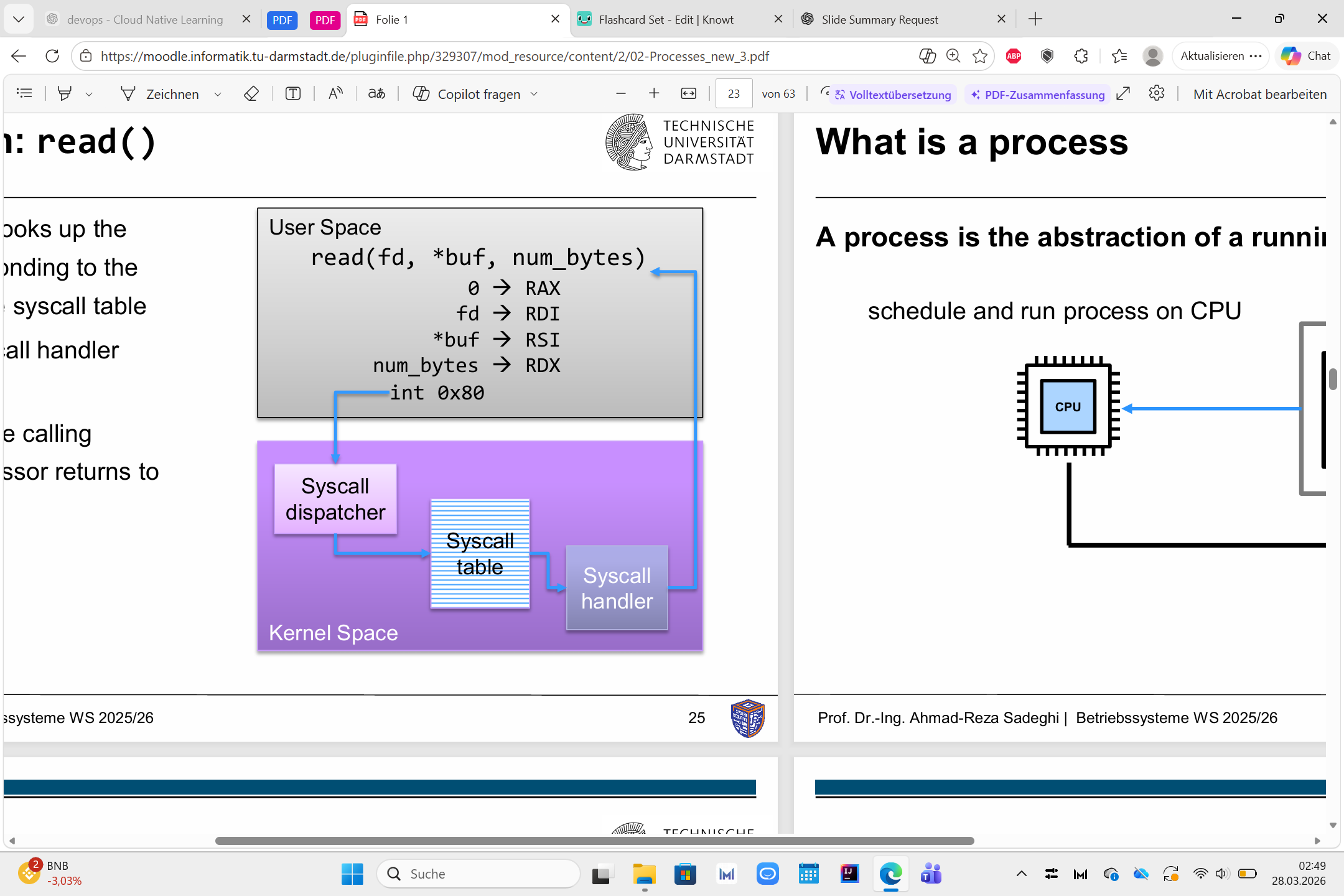
How is a syscall invoked? (read() example)
user program calls read()
wrapper puts:
syscall number in RAX
arguments in registers like RDI, RSI, RDX
special instruction / trap enters kernel
kernel syscall dispatcher handles it
result is returned to user space
What is a process and what is its structure?
process = abstraction of a running program
program is loaded into memory
OS schedules the process on the CPU
process structure / address space:
text = program code
data = static variables/data
heap = dynamic memory created during execution
stack = function calls, local variables, LIFO
process address space:
process uses virtual memory
mapped to physical memory
mapping done via page table
handled by MMU and OS memory management
What are process states, PCB, multiprogramming, and context switching?
process states:
new = process created
ready = waiting for CPU
running = currently executing
blocked = waiting for I/O/event
terminated = finished
PCB (Process Control Block):
stores important process infoprogram counter
registers
stack pointer
program status word
process ID
file descriptors
multiprogramming:
multiple processes in system at same time
CPU switches quickly between them
creates illusion of parallelism
context switching:
OS saves state of one process
loads state of another process
CPU changes from one process to another
What are POSIX and the main POSIX process-creation functions?
POSIX = Portable Operating System Interface
standard interface for Unix-like OSs
gives compatibility/portability
helps software run on different systems with similar system calls
process creation (POSIX):
fork() = creates a child process
exec() = replaces process memory with a new program
wait() = parent waits for child to finish
exit() = terminates process
fork() return values:
< 0 = error
= 0 = child process
> 0 = parent gets child PID
What is a process tree?
parent-child hierarchy of processes
root often init (pid 1)
children can create more children
How does a process terminate?
exit() after finishing
exit due to handled error
exit due to unhandled error
parent can terminate child with kill()
OS removes process and frees resources
What are the process memory segments?
text = program instructions, read-only
data = initialized global/static data
bss = uninitialized global/static data
heap = dynamic memory, grows up
stack = local variables/function calls, LIFO, grows down
top area also has command-line arguments and environment variables
What is the stack segment?
RAM region used during function calls
LIFO structure
uses PUSH and POP
stores:
function arguments
local variables
return address
divided into stack frames
grows toward lower addresses
stack pointer (SP) stores address of top element
What is a stack frame?
memory block for one function call
created on top of the stack
contains:
arguments
return address
base pointer (BP)
local variables
What is the base pointer (BP)?
CPU register: BP / EBP / RBP
points to a fixed position in current stack frame
used as reference for:
function parameters
local variables
helps with organized stack access
useful for debugging/backtracking
How do function calls and returns work on x86
call instruction starts function
pushes return address onto stack
return address = instruction after the call
ret instruction pops return address
execution continues in calling function
How are function parameters and local variables stored on the stack?
arguments are above EBP
local variables are below EBP
return address and old base pointer are also in stack frame
EBP is fixed reference point inside the frame
What is a buffer overflow?
writing more data than a buffer can hold
can overwrite nearby stack data
may affect:
local variables
base pointer
return address
dangerous security problem
What are the basic types of inter-process communication (IPC)?
message passing
shared memory
What is message-passing IPC?
processes communicate with send() and receive()
messages go through a message queue
OS/kernel controls the communication
needs system calls for each message
slower, but simpler and more isolated
What is shared-memory IPC?
both processes access the same shared memory region
memory is mapped into both processes’ virtual memory
after setup, OS is less involved in communication
faster
but more complex and more error-prone
Message passing vs. shared memory?
message passing: send/receive, slower, simpler, isolation yes, easier
shared memory: write/read shared area, faster, more complex, isolation no
1. What is the primary purpose of an Operating System?
A) To translate source code into machine code
B) To manage system resources and ensure process isolation
C) To execute only user programs
D) To control user access levels
Correct answer: B
OS manages system resources
OS ensures process isolation
A = compiler job
C too limited / wrong
D is only one part, not the main purpose
2. Why are processes divided into user mode and kernel mode?
A) To improve application performance
B) To reduce memory consumption
C) To protect the system from unauthorized access by applications
D) To allow direct access to hardware
Correct answer: C
user mode / kernel mode exist for protection
apps in user mode cannot do privileged operations directly
this prevents unauthorized or dangerous access to the system/hardware
A not the main reason
B wrong
D opposite: modes exist to restrict direct hardware access
What is the main function of the EAX register in x86 architecture?
A) Manages function pointers B) Serves as an accumulator for arithmetic operations
C) Holds the next instruction address
D) Stores system parameters
Correct answer: B
EAX = main accumulator register
commonly used for arithmetic operations
C would be IP / EIP / RIP
D not its main role
A wrong
4. What is the purpose of the wait() system call in POSIX systems?
A) To create a new process
B) To terminate the parent process
C) To block the parent process until the child processes complete
D) To replace the memory space of the process
Correct answer: C
wait()makes the parent process block/waitit waits until the child process finishes
A =
fork()B wrong
D =
exec()
5. Which memory segment grows toward lower addresses?
A) Heap
B) Stack
C) Data segment
D) Text segment
Correct answer: B
stack grows toward lower addresses
heap usually grows toward higher addresses
data and text do not grow like that in normal execution
6. During a context switch, what is the most critical operation performed by the OS?
A) Pausing CPU clock temporarily
B) Saving only the heap data
C) Saving CPU registers and the stack pointer into the Process Control Block (PCB)
D) Restarting the process from the beginning
Correct answer: C
during a context switch, the OS must save the process CPU state
especially registers and stack pointer in the PCB
later it can restore them and continue the process
A wrong
B not enough
D wrong, process continues, not restarts
7. Which statement correctly describes the behavior of exec() in UNIX?
A) Creates a new process without affecting the parent
B) Replaces the current process memory space with a new program
C) Suspends the parent process D) Forces a transition to kernel mode
Correct answer: B
exec()does not create a new processit replaces the current process memory/image with a new program
usually used after
fork()A = more like
fork()C wrong
D not its meaning
8. Which memory segment holds uninitialized global variables?
A) Heap
B) Data segment
C) BSS (Block Started by Symbol)
D) Stack
Correct answer: C
BSS stores uninitialized global/static variables
data segment stores initialized global/static variables
heap = dynamic memory
stack = local variables / function calls
9. When does a buffer overflow occur?
A) When a variable is unused
B) When a program writes more data than the allocated buffer size
C) When a process fails to call exec()
D) When fork() completes without wait()
Correct answer: B
buffer overflow happens when a program writes more data than the buffer can hold
this can overwrite nearby memory
dangerous because it may affect variables, base pointer, or return address
A, C, D are unrelated
10. What is the main advantage of shared-memory IPC over message-passing IPC?
A) It is safer because the OS controls all communication
B) It is faster since it avoids repeated system calls for every data exchange
C) It requires no synchronization
D) It is simpler to implement
Correct answer: B
shared memory is faster
after setup, processes can exchange data without a system call for every message
message passing is usually slower because the OS/kernel is involved each time
A describes message passing more
C false, shared memory does need synchronization
D false, shared memory is usually more complex