Mark IC34 Flashcards
1/113
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
114 Terms
What is the IACS Security Lifecycle?
A. Assess, Develop & Implement, Maintain
B. Assess, Develop & Implement, Forget
C. Maintain, Assess, Develop & Implement
D. Develop & Implement, Assess, Maintain
A. Assess, Develop & Implement, Maintain
How do you Implement Security Levels?
Assign a Target Security Level (SL-T) [Assess]
Implement to meet Achieved Security Level (SL-A) [Develop & Implement]
Ensure that SL-A >= SL-T [Maintain]
Which comes after the High-Level Cyber Risk Assessment of the Assess Phase?
A. High-Level Cyber Risk Assessment (ISA 62443-3-2)
B. Allocation of IACS Assets to Security Zones or Conduits (ISA 62443-3-2)
C. Detailed Cyber Risk Assessment (ISA 62443-3-2)
D. Cybersecurity Requirements Specification (ISA 62443-3-2)
B. Allocation of IACS Assets to Security Zones or Conduits (ISA 62443-3-2)
Which comes after the Allocation of IACS Assets to Security Zones or Conduits of the Assess Phase?
A. High-Level Cyber Risk Assessment (ISA 62443-3-2)
B. Allocation of IACS Assets to Security Zones or Conduits (ISA 62443-3-2)
C. Detailed Cyber Risk Assessment (ISA 62443-3-2)
D. Cybersecurity Requirements Specification (ISA 62443-3-2)
C. Detailed Cyber Risk Assessment (ISA 62443-3-2)
Which comes after the Detailed Cyber Risk Assessment of the Assess Phase?
A. Installation, commissioning and validation of Cybersecurity
B. Allocation of IACS Assets to Security Zones or Conduits (ISA 62443-3-2)
C. Design and engineering of Cybersecurity countermeasures (ISA 62443-3-3)
D. Cybersecurity Requirements Specification (ISA 62443-3-2)
D. Cybersecurity Requirements Specification (ISA 62443-3-2)
What document is the Cybersecurity Requirements Specification?
A. ISA 62443-3-2
B. ISA 62443-4-2
C. ISA 62443-2-1
D. ISA 62443-3-3
A. ISA 62443-3-2
What is the last part of the IACS Cybersecurity Lifecycle in the Maintain Phase?
A. Periodic Cybersecurity Audits (ISA 62443-2-1)
B. High-Level Cyber Risk Assessment (ISA 62443-3-2)
C. Cyber Incident Response & Recovery (ISA 62443-2-1)
D. Cybersecurity Maintenance Monitoring and Management of Change (ISA 62443-2-1)
C. Cyber Incident Response & Recovery (ISA 62443-2-1)
What are the Continuous Processes for the IACS Security Lifecycle?
A. Periodic Cybersecurity Audits (ISA 62443-2-1)
B. Cybersecurity Management System: Policies, Procedures, Training & Awareness (ISA 62443-2-1)
C. Cyber Incident Response & Recovery (ISA 62443-2-1)
D. Both A & B
D. Both A & B
What is the information needed for a good risk assessment?
A. Lowest Severity Consequences, Threat/Vulnerabilities leading to highest risk, Target Security Levels, Recommendations
B. Risk Profile, Highest Severity Consequences, Threat/Vulnerabilities leading to lowest risk, Target Security Levels
C. Risk Profile, Highest Severity Consequences, Threat/Vulnerabilities leading to highest risk, Target Security Levels, Recommendations
D. Network Profile, No Consequences, Threat/Vulnerabilities leading to highest risk, Target Security Levels, Recommendations
C. Risk Profile, Highest Severity Consequences, Threat/Vulnerabilities leading to highest risk, Target Security Levels, Recommendations
Cybersecurity Requirements Specification requires at a minimum:
A. Regulatory Requirements, Tolerable Risk, Organizational Security Policies, Threat Environment, Operating environment assumptions, Zone and Conduit drawings & Characteristics, SUC Description
B. Tolerable Risk, Organizational Security Policies, Threat Environment, Zone and Conduit drawings & Characteristics, SUC Name
C. Regulatory Requirements, Threat Environment, Operating environment assumptions, Zone and Conduit drawings & Characteristics, SUC Description, Light Scanning, Certified Operator
D. Regulatory Requirements, Tolerable Risk, Organizational Security Policies, Zone and Conduit Assumptions, Management Policy Decision Matrix
A. Regulatory Requirements, Tolerable Risk, Organizational Security Policies, Threat Environment, Operating environment assumptions, Zone and Conduit drawings & Characteristics, SUC Description
Which is a Cybersecurity Requirements Specification?
A. Management Policy Decision Matrix
B. Certified Operator
C. Detailed Cybersecurity Risk Assessment
D. Regulatory Requirements
D. Regulatory Requirements
What should you Document Per Zone / Conduit?
A. Logical/Physical Boundaries & Access Points, Data Flow for Access Points, Connected Zones & Conduits, Asset List, SL-T Policy & Requirement, External Dependencies, Past Issues
B. Name/Identifier, Logical/Physical Boundaries & Access Points, Data Flow for Access Points, Connected Zones & Conduits, Asset List, SL-T Policy & Requirement, Assumptions and External Dependencies
C. Name/Identifier, Physical Cable routing, Type of communication protocols, Flat Networking, Connected Zones & Conduits, Asset List, SL-T Policy & Requirement, Assumptions and External Dependencies
D. Name/Identifier, Logical/Physical Boundaries & Access Points, Data Flow for Access Points, Connected Cables and ISP, IP Range List, Highest SL in Zone
B. Name/Identifier, Logical/Physical Boundaries & Access Points, Data Flow for Access Points, Connected Zones & Conduits, Asset List, SL-T Policy & Requirement, Assumptions and External Dependencies
SL 0 (Security Level Zero)
No specific requirements or security protection necessary
SL 1 (Security Level One)
Protection against casual or coincidental violation
SL 2 (Security Level Two)
Protection against intentional violation using simple means with low resources, generic skills and low motivation
SL 3 (Security Level Three)
Protection against intentional violation using sophisticated means with moderate resources, IACS specific skills and moderate motivation
SL 4 (Security Level Four)
Protection against intentional violation using sophisticated means with extended resources, IACS specific skills and high motivation
SL-A (Achieved Security Level)
The achieved security level of the zone or conduit.
SL-C (Capability Security Level)
The highest security level obtainable by the zone, conduit, or component. If component, the vendor documentation may define the configuration to meet the security level.
Verified by the ISASecure group EDSA/CSA Certifications
Mapping of the SL-C can be found in:
– ISA-62443-3-3 (for Operators / Owners)
– ISA-62443-4-2 (for Product Suppliers / ISASecure)
How can a Product Supplier maintain SL-C of a device?
A. ISA-62443-3-3
B. ISA-62443-2-1
C. ISA-62443-4-2
D. ISA-62443-3-2
C. ISA-62443-4-2
How can a Owner maintain SL-C of a device?
A. ISA-62443-3-3
B. ISA-62443-2-1
C. ISA-62443-4-2
D. ISA-62443-3-2
A. ISA-62443-3-3
SL-T (Target Security Level)
The desired target of the zone or conduit. (Assigned as part of the CRS documentation)
SL-T may be expressed as a single value or a vector. Refer to ISA-62443-3-3, Annex A for a discussion of the SL vector approach. (This is covered in the Detailed Design Module)
Which is NOT a way you should develop a security strategy?
A. Identify Zones
B. Evaluate all Zones simultaneously
C. Establish SL-T & Physical/Digital Access Points
D. Develop 5D Cybersecurity Strategy
B. Evaluate all Zones simultaneously (ONLY Evaluate 1 Zone at a time)
What are the Four “T’s” of Managing Risk?
A. Tank, Towering, Terminate, Trying
B. Transmit, Tank, Terminate, Towing
C. Tolerate, Transfer, Terminate, Treat
D. Tight, Transfer, Tank, Treat
C. Tolerate, Transfer, Terminate, Treat
Tolerate
The risk is known and accepted by the organization.
Transfer
The risk is passed to a third party, for example an insurer or an outsourcer, to manage although this does not eliminate the risk.
Terminate
We stop the process, activity etc. or stop using the premises, IT system etc. which is at risk and hence the risk is no longer relevant.
Treat
We aim to reduce the likelihood of the threat materializing or else reduce the resultant impact through introducing relevant controls and continuity strategies
What are the Five “D’s” of Treating Risk?
A. Deter, Detect, Delay, Deny, Defeat
B. Deter, Drain, Dig, Deny, Drop
C. Down, Drain, Delay, Deny, Defeat
D. Down, Detect, Dig, Deny, Drop
A. Deter, Detect, Delay, Deny, Defeat
What is an example of a method to Delay a Cyberattack?
A. Honey Pot Systems
B. Default Passwords
C. Flat Network
D. Badly Configured Firewall
A. Honey Pot Systems
What is an example of a method to Deny a Cyberattack?
A. Honey Pot Systems
B. Access Control Technology (Biometric or Card Access) or a Manned Security Gate
C. Layer 2 Switch
D. Unlocked Server Room
B. Access Control Technology (Biometric or Card Access) or a Manned Security Gate
How shall you Address Physical and Cybersecurity measures?
A. Establish complementary physical and Cybersecurity policies & Physical Security Perimeters with entry controls
B. Just have Physical Barriers
C. Just have Policies
D. Establish dissociative physical and Cybersecurity policies & Physical Security Perimeters without entry controls
A. Establish complementary physical and Cybersecurity policies & Physical Security Perimeters with entry controls
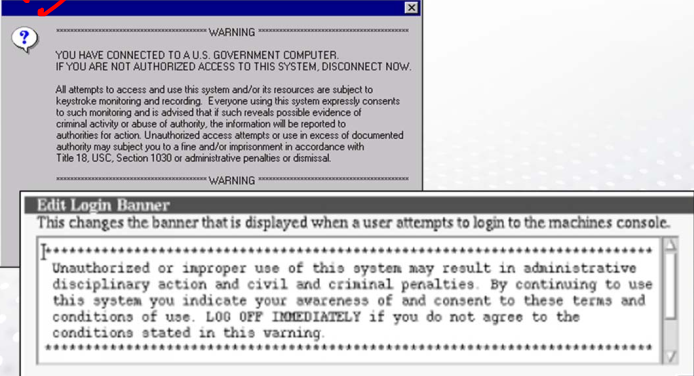
What is this an example of?
A. Detect
B. Deny
C. Deter
D. Defeat
C. Deter
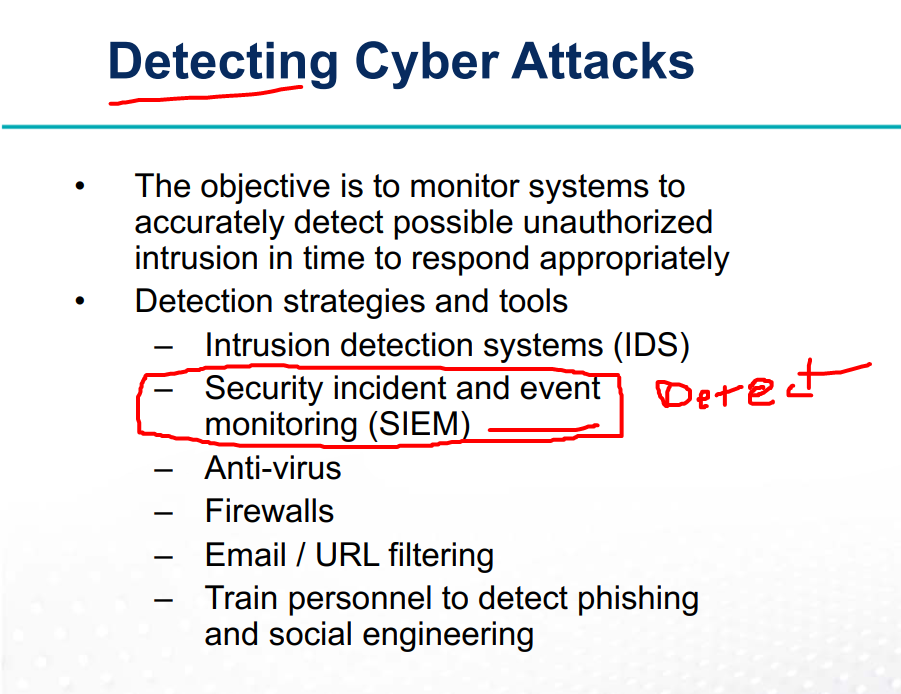
What is a tool of Detecting a cybersecurity event?
A. Obscure Port Use
B. Security incident and event monitoring (SIEM)
C. Studio 5000
D. PLCNeXt Engineer
B. Security incident and event monitoring (SIEM)
Which of the following helps Deter malware entering via a USB Port?
A. Anti-Virus
B. Physical Port Blocking
C. Disable “autoplay”
D. Host Intrusion Detection System
B. Physical Port Blocking
What are the elements of a Conceptual Cybersecurity Design Specification?
Scope of work
Conceptual system architecture
Budgetary cost and schedule estimates
What is NOT a compensating countermeasure for a control system?
A. External Resource
B. Insurance
C. Additional Physical Security measures
D. Enhanced personal background checks
B. Insurance
FR 1 (Foundational Requirement One)
Identification and authentication control (IAC)
SR1.01 - Human user identification and authentication
SR1.02 - Software process and device identification and authentication
SR1.03 - Account management
SR1.04 - Identifier management
SR1.05 - Authenticator management
SR1.06 - Wireless access management
SR1.07 - Strength of password-based authentication
SR1.08 - Public key infrastructure certificates
SR1.09 - Strength of public key authentication
SR1.10 - Authenticator feedback
SR1.11 - Unsuccessful login attempts
SR1.12 - System use notification
SR1.13 - Access via untrusted networks
FR 2 (Foundational Requirement Two)
Use Control (UC)
SR2.01 - Authorization enforcement
SR2.02 - Wireless use control
SR2.03 - Use control for portable and mobile devices
SR2.04 - Mobile code
SR2.05 - Session lock
SR2.06 - Remote session termination
SR2.07 - Concurrent session control
SR2.08 - Auditable events
SR2.09 - Audit storage capacity
SR2.10 - Response to audit processing failures
SR2.11 - Timestamps
SR2.12 - Non-repudiation
Which is NOT an Access Control Technology?
A. Active Directory
B. RADIUS / LDAP
C. TACACS+
D. Host Intrusion Detection System
D. Host Intrusion Detection System
FR 3 (Foundational Requirement Three)
System Integrity (SI)
SR3.01 - Communication integrity
SR3.02 - Malicious code protection
SR3.03 - Security functionality verification
SR3.04 - Software and information integrity
SR3.05 - Input validation
SR3.06 - Deterministic output
SR3.07 - Error handling
SR3.08 - Session integrity
SR3.09 - Protection of audit information
What is the Security requirement for FR3 - Use Control (UC) SR3.02?
A. Communication integrity
B. Software and information integrity
C. Session integrity
D. Malicious code protection
D. Malicious code protection
Which is a System Integrity Technology?
A. Physical Security
B. Secure Programming and Protocols
C. Malware and antivirus software
D. All of the Above
D. All of the Above
FR 4 (Foundational Requirement Four)
Data Confidentiality (DC)
SR4.01 - Information confidentiality
SR4.02 - Information persistence
SR4.03 - Use of cryptography
What is the Security requirement for FR4 - Data Confidentiality (DC) SR4.03?
A. Use of Cryptography
B. Information confidentiality
C. Information persistence
D. Malicious code protection
A. Use of Cryptography
Which is NOT a Data Confidentiality Technology?
A. Physical Security
B. Encryption / Cryptography
C. Error handling
D. Secure Protocols
C. Error handling
FR 5 (Foundational Requirement Five)
Restricted Data Flow (RDF)
SR5.01 - Network segmentation
SR5.02 - Zone boundary protection
SR5.03 - General purpose person-to-person communication restrictions
SR5.04 - Application partitioning
What is one way to Restricted Data Flow (FR5)?
A. DMZ
B. Unmanaged Switch
C. PLC
D. Combine IT and OT Networks
A. DMZ
SR5.01 Restricted Data Flow (FR5) does what?
A. Zone Boundary protection
B. Network segmentation
C. Application partitioning
D. General purpose person-to-person communication restrictions
B. Network segmentation
Which is NOT a Restricted Data Flow Technology?
A. Physical network cables
B. Virtual LANs (VLAN)
C. Firewalls
D. Data diodes
E. None of the Above
E. None of the Above
FR 6 (Foundational Requirement Six)
Timely Response to Events (TRE)
SR6.01 - Audit log accessibility
SR6.02 - Continuous monitoring
Which is a Timely Response to Events Technology?
A. Security Incident and Event Monitoring (SIEM)
B. High-Level Risk Assessment
C. SL-T
D. Malware
A. Security Incident and Event Monitoring (SIEM)
Continuous Monitoring
– Logfiles
– Syslogs
– SNMP
Intrusion Detection Systems (IDS)
Intrusion Prevention Systems (IPS)
FR 7 (Foundational Requirement Seven)
Resource Availability (RA)
SR7.01 - Denial of service protection
SR7.02 - Resource management
SR7.03 - Control system backup
SR7.04 - Control system recovery and reconstitution
SR7.05 - Emergency power
SR7.06 - Network and security configuration settings
SR7.07 - Least functionality
SR7.08 - Control system component inventory
Which security requirement for FR7 keeps a plant running when the power goes out?
A. SR7.08 - Control system component inventory
B. SR7.05 - Emergency power
C. SR7.02 - Resource management
D. SR7.01 - Denial of service protection
B. SR7.05 - Emergency power
Which is NOT a Resource Availability Technology?
A. Rate limiting firewalls
B. Backup/Restore tools & Source code management systems
C. Active Directory
D. Uninterruptible Power Supply (UPS)
C. Active Directory
ISA-62443-4-1
A. Framework for the development of components
B. Provides component requirements
C. System Requirements and Requirement Enhancements
D. System requirements for owners
A. Framework for the development of components
ISA-62443-4-2
A. Framework for the development of components
B. Provides component requirements
C. System Requirements and Requirement Enhancements
D. System requirements for owners
B. Provides component requirements
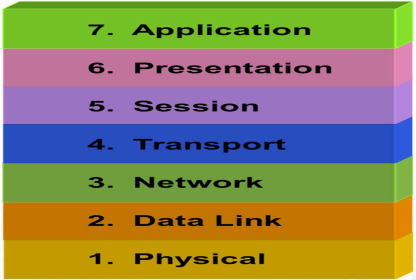
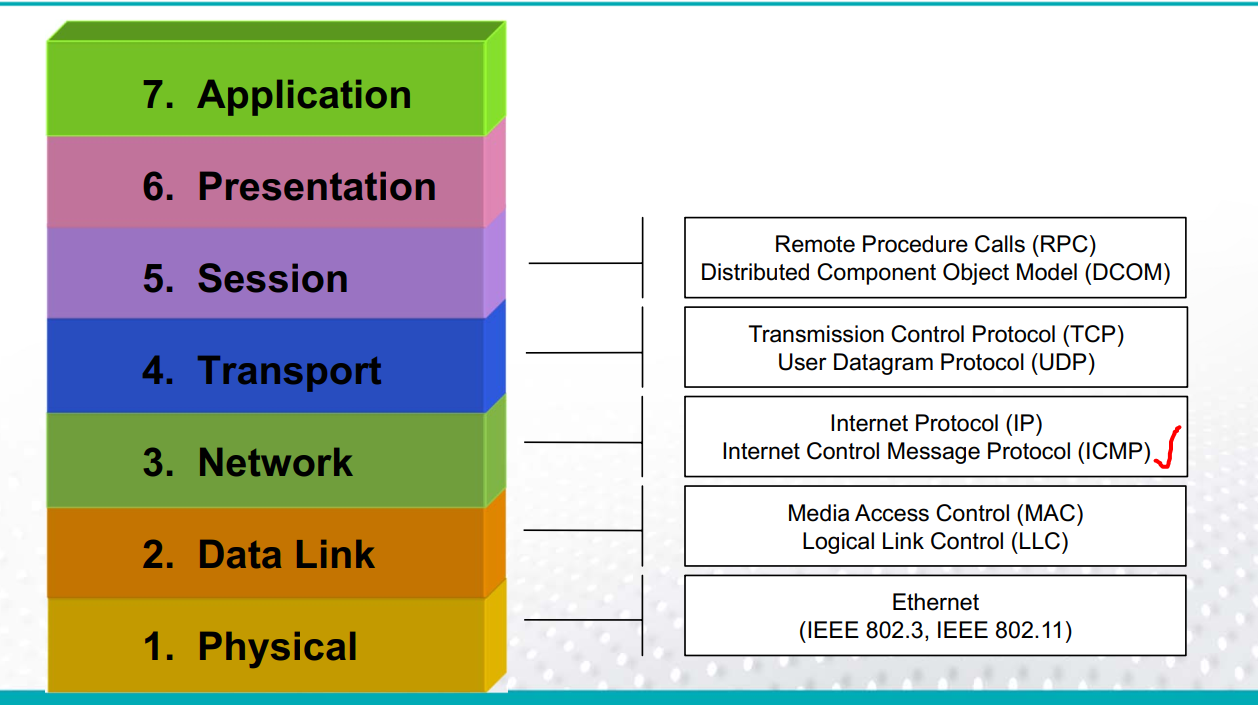
In the ISO OSI/Reference Model, which layer is responsible for data flow control and end-to-end error recovery?
A. Physical
B. Network (IPv4 / ICMP / BGP)
C. Transport (TCP / UDP)
D. Data Link (MAC / ARP)
C. Transport (TCP / UDP)
Internet Engineering Task Force (IETF) uses a simplified OSI Layer model, How is it simplified?
A. Layers 5-6-7 as a single layer
B. Layers 1-2-3 as a single layer
C. Layers 2-3-4 as a single layer
D. Layers 4-5-6 as a single layer
A. Layers 5-6-7 as a single layer
Layer 1: Physical Layer
The physical protocols define the physics of getting a message between devices like:
– Frequencies Voltages Connectors
– Modulation Topologies Cables
Layer 2: Data Link Layer
Provides the rules for framing, converting electrical signals to data, error checking, physical and media access control (MAC) addressing
Layer 3: Network Layer
The network layer is responsible for packet forwarding including routing through intermediate routers
Layer 4: Transport Layer
Provides transparent transfer of data between end systems, or hosts, and is responsible for end-to-end error recovery and flow control.
Layer 5: Session Layer
Provides the mechanism for opening, closing and managing a session between end-user application processes
Layer 6: Presentation Layer
Deals with data format conversion and possibly with encryption and security
Layer 7: Application Layer
Interacts with software applications that implement a communicating component
Protocols specific to network applications such as email, file transfer, reading data registers in a PLC
What is a Network Discovery Tool to map assets?
A. nmap
B. Legion
C. Metasploit
D. Kali
A. nmap
What is a Three-tier network design between the enterprise and process control networks.
A. Firewall
B. Demilitarized Zone (DMZ)
C. Router
D. Switch
B. Demilitarized Zone (DMZ)
What type of security design is created from network segmentations?
A. IT Anti-Virus
B. HIDS
C. Access Controls
D. Defense-in-Depth
D. Defense-in-Depth
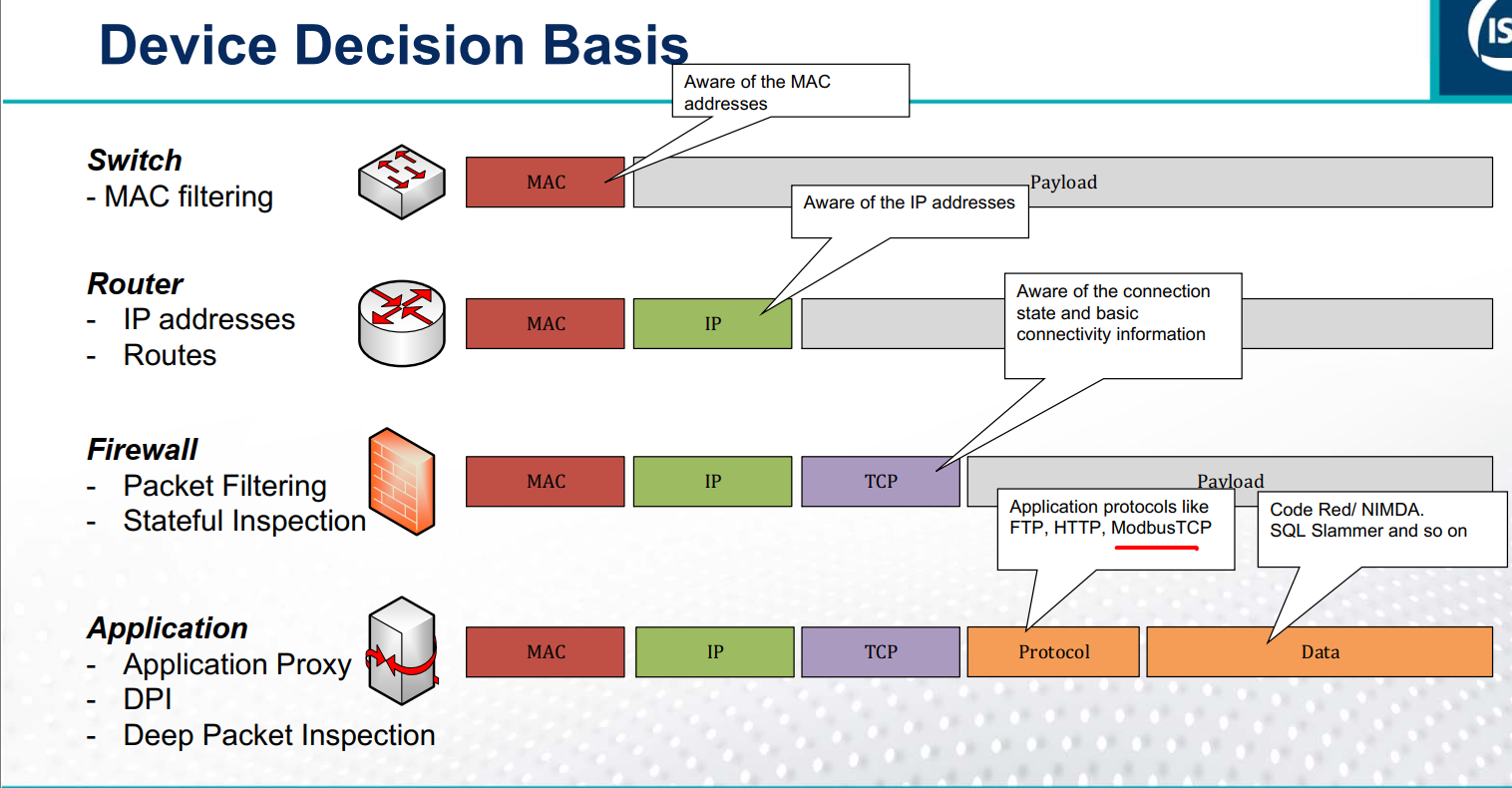
How many types of firewalls are there?
A. 3 types
B. 2 types
C. 4 types
D. 1 type
B. 2 types
Network Firewalls
Host-based firewalls
How many classes of firewalls are there?
A. 3 types
B. 2 types
C. 4 types
D. 1 type
A. 3 types
Packet Filter
Stateful Inspection
Deep packet inspection (application firewalls)
What does not get considered when packet filtering?
A. Source and destination MAC address
B. Source and destination IP address
C. network or transport protocol
D. payload of packets
D. payload of packets
What is required to block specific protocol functions?
A. Source and destination IP address
B. Stateful Inspection
C. Deep Packet Inspection
D. Packet Filtering
C. Deep Packet Inspection
What is the main difference between IT Firewalls and an IACS specific firewall?
A. Bandwidth and ports
B. Knowledge of industrial protocols
C. Inbound rules
D. Outbound rules
B. Knowledge of industrial protocols
What is the cycle for Firewall Planning and Implementation?
A. Plan, Deploy, Install & Configure, Test, Manage
B. Manage, Plan, Install & Configure, Test, Deploy
C. Deploy, Plan, Install & Configure, Test, Manage
D. Plan, Install & Configure, Test, Deploy, Manage
D. Plan, Install & Configure, Test, Deploy, Manage
Which one is NOT a good policy for configuring a firewall?
A. Comment the configuration
B. Understand syntax and how firewall processes the rules
C. What types of traffic (protocols, source and destination addresses, etc.) are required by approved applications for the organization.
D. Any Any Allow All
D. Any Any Allow All
What is the policy or rules it will use to determine if packets will be passed?
A. Intrusion Detection System
B. Intrusion Prevention System
C. Access Control Lists (ACLs)
D. Host Intrusion Detection System
C. Access Control Lists (ACLs)
What is one IACS Firewall Configuration Best Practice?
A. Default rule should be ANY - ANY - DENY ALL
B. Allow traffic directly from the IACS network to the enterprise network
C. IACS devices should be allowed to access the Internet
D. Permit rules should be broad to work correctly
A. Default rule should be ANY - ANY - DENY ALL
At what step should you create a backup for your firewall configuration?
A. Test
B. Deploy
C. Install & Configure
D. Manage
B. Deploy
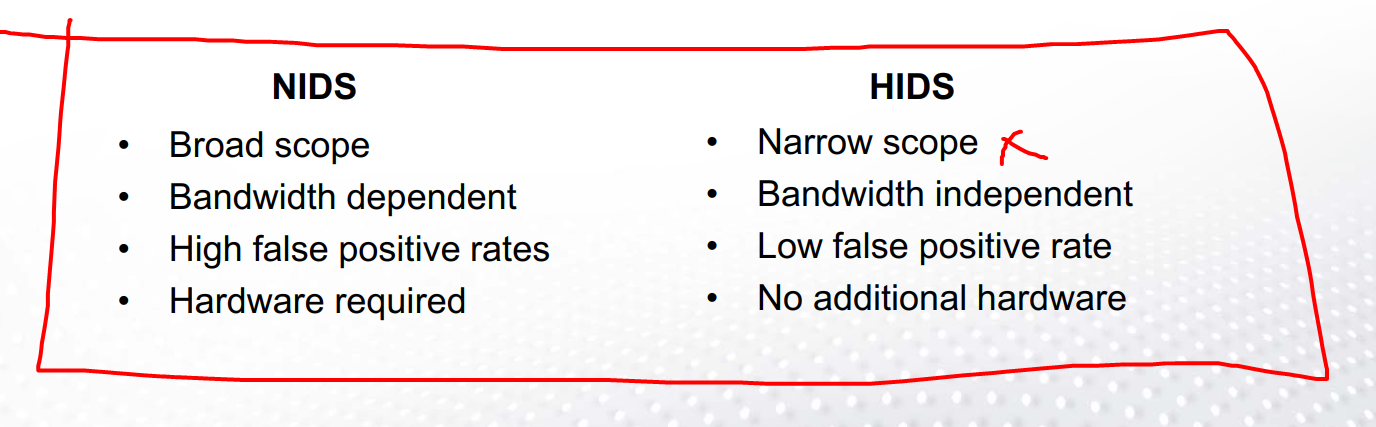
How many types of Intrusion Detection Systems are there?
A. 3 types
B. 2 types
C. 4 types
D. 1 type
B. 2 types
Network Intrusion Detection Systems (NID)
Host Intrusion Detection Systems (HID)
Which detection system can detect rootkit attacks?
A. Network Intrusion Detection Systems (NID)
B. Host Intrusion Detection Systems (HID)
C. None of the above
D. All of the above
B. Host Intrusion Detection Systems (HID)
Why use Host Intrusion Detection System for a local PC?
A. Broad scope
B. Narrow scope
C. High false positive rates
D. Additional Hardware required
B. Narrow scope
What is System Hardening?
A. The process of securing a system by reducing its attack surface
B. The process of securing a system by increasing its attack surface
C. Download Bloatware
D. Allowing http
A. The process of securing a system by reducing its attack surface
Where can you find OS Hardening Guidance?
A. NIST SP 800-123 “Guide to General Server Security”
B. Center for Internet Security’s (CIS) Security Benchmarks
C. Security Guides from Microsoft & Automation suppliers
D. All of the Above
D. All of the Above
Which OS has a CIS hardened security image?
A. Amazon Linux
B. Android 16
C. Chromebook OS
D. Windows XP
A. Amazon Linux
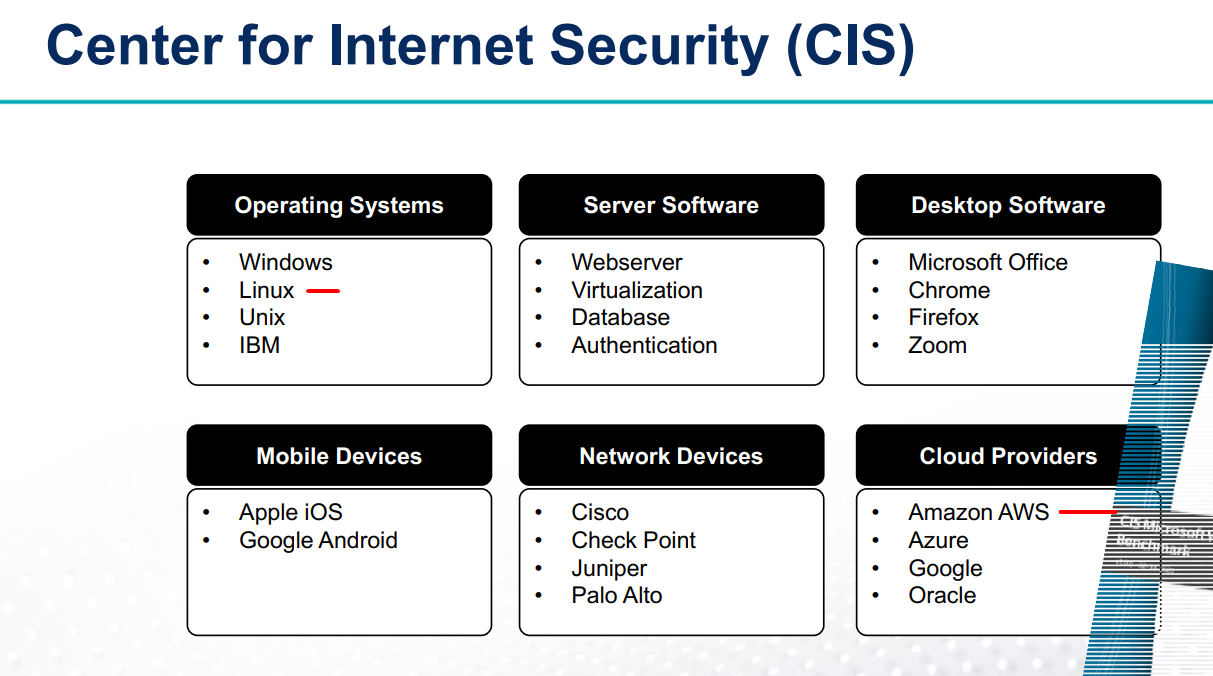
Where can you go for IACS Hardening Guidance?
A. NIST
B. Vendor specific guidance
C. Independent test reports
D. All of the Above
D. All of the Above
What are the Three Functional Planes of a Network?
A. Southwest Plane, Sandwich Plane, Data Plane
B. Management Plane, American Plane, Data Plane
C. Management Plane, Control Plane, Data Plane
D. Delta Plane, Jog Plane, Data Plane
C. Management Plane, Control Plane, Data Plane
Where can you go for Network Hardening Guidance?
A. NIST
B. National Security Agency (NSA)
C. Cisco
D. SANS Institute
E. All of the Above
E. All of the Above
Which is NOT a Network Device Hardening Best Practice?
A. Install firmware updates
B. Give out the admin password
C. Use secure protocols
D. Shut down unused physical interfaces on network devices
B. Give out the admin password
Which FR defines Access Controls?
A. FR1
B. FR2
C. FR1 & FR2
D. FR5
C. FR1 & FR2
Acronym - IUSDRTR
"I Usually Suspect DNS, Rarely Trust Results."
FR 1 - I
FR 2 - UC
FR 3 - SI
FR 4 - DC
FR 5 - RDF
FR 6 - TRE
FR 7 - RA
• FR 1 – Identification and authentication control (IAC)
Identify and authenticate all users before allowing them to access to the control system.
• FR 2 – Use control (UC)
Enforce the assigned privileges of an authenticated user
• FR 3 – System integrity (SI)
Ensure the integrity of the IACS to prevent unauthorized manipulation.
• FR 4 – Data confidentiality (DC)
Protection against eavesdropping and unauthorized access
• FR 5 – Restricted data flow (RDF)
Segment the control system via zones and conduits to limit the unnecessary flow of data.
• FR 6 – Timely response to events (TRE)
Be able to respond quickly to events and should not adversely affect IACS
• FR 7 – Resource availability (RA)
Ensure the availability of the control system against the degradation or denial of essential services
What stands for AAA for access controls?
A. Authentication, Authorization, Accounting
B. Authentication, Allow, Accounting
C. Always, Authorization, Allow
D. Authentication, Always, Accounting
A. Authentication, Authorization, Accounting
In a Public Key Infrastructure (PKI), which component is responsible for checking whether a presented digital certificate and its signature are still valid (for example by consulting revocation information) before telling the receiver that the signature is OK?
A. Certification Authority (CA)
B. Registration Authority (RA)
C. Validation Authority (VA)
D. Key Escrow Server
C. Validation Authority (VA)
In Public Key Infrastructure (PKI), what is the most commonly used certificate format for representing digital certificates?
A. PGP
B. SSH
C. X.509
D. PEM
C. X.509
What are the differences of a Self Signed certificate?
A. Root CA no validation (Like using a printed badge instead of an official passport)
B. Different structure as public key certificates
C. certificate authority (CA) issues
D. None of the Above
A. Root CA no validation (Like using a printed badge instead of an official passport)
Where can you find access control guidance?
A. ISA/IEC
B. NIST
C. Public Safety Canada & US Department of Homeland Security (DHS)
D. All of the Above
D. All of the Above
Which is an Access Control Best Practice?
A. Don’t have an access control policy
B. Employ multiple authentication methods for critical ICSs
C. Have every device in one zone
D. Centralize all information
B. Employ multiple authentication methods for critical ICSs
One endpoint is a host computing device, and the other endpoint is an intermediate device that passes traffic from the host to the trusted network behind the security gateway while relying on the VPN technology to secure the traffic on the untrusted network.
A. Site-to-site VPN
B. Remote Access Service (RAS) VPN
C. VNC
D. RDP
B. Remote Access Service (RAS) VPN
Remote to RAS, RDP to _________ , _________ connects to control network
Jump Host