Fundamentals of Information Security - D430 CH 5 (Actual Exam) Questions with verified Answers (Latest Update 2026) UPDATE!!-WGU
1/26
There's no tags or description
Looks like no tags are added yet.
Name | Mastery | Learn | Test | Matching | Spaced | Call with Kai |
|---|
No analytics yet
Send a link to your students to track their progress
27 Terms
Cryptography
science of protecting the confidentiality & integrity of data & a key part of the vast set of transactions that take place over devices daily.
Encryption
process of transforming readable data, called platext or cleartext, to an unreadable form called ciphertext.
Decryption
process of recovering the plaintext from a ciphertext.
cryptographic algorithm
encrypting plaintext or decrypting the ciphertext through computational procedure. Use a key, or multiple keys, to encrypt or decrypt message.
The Caesar Cipher
ancient cryptography used by Julius Caesar. Involves shifting each letter of plaintext message by a certain number of spaces in alphabet, historically 3. After shift you would write letter A as D, letter B as E.. etc.
Substitution cipher
encryption method that substitutes each letter in alphabet for a different one.
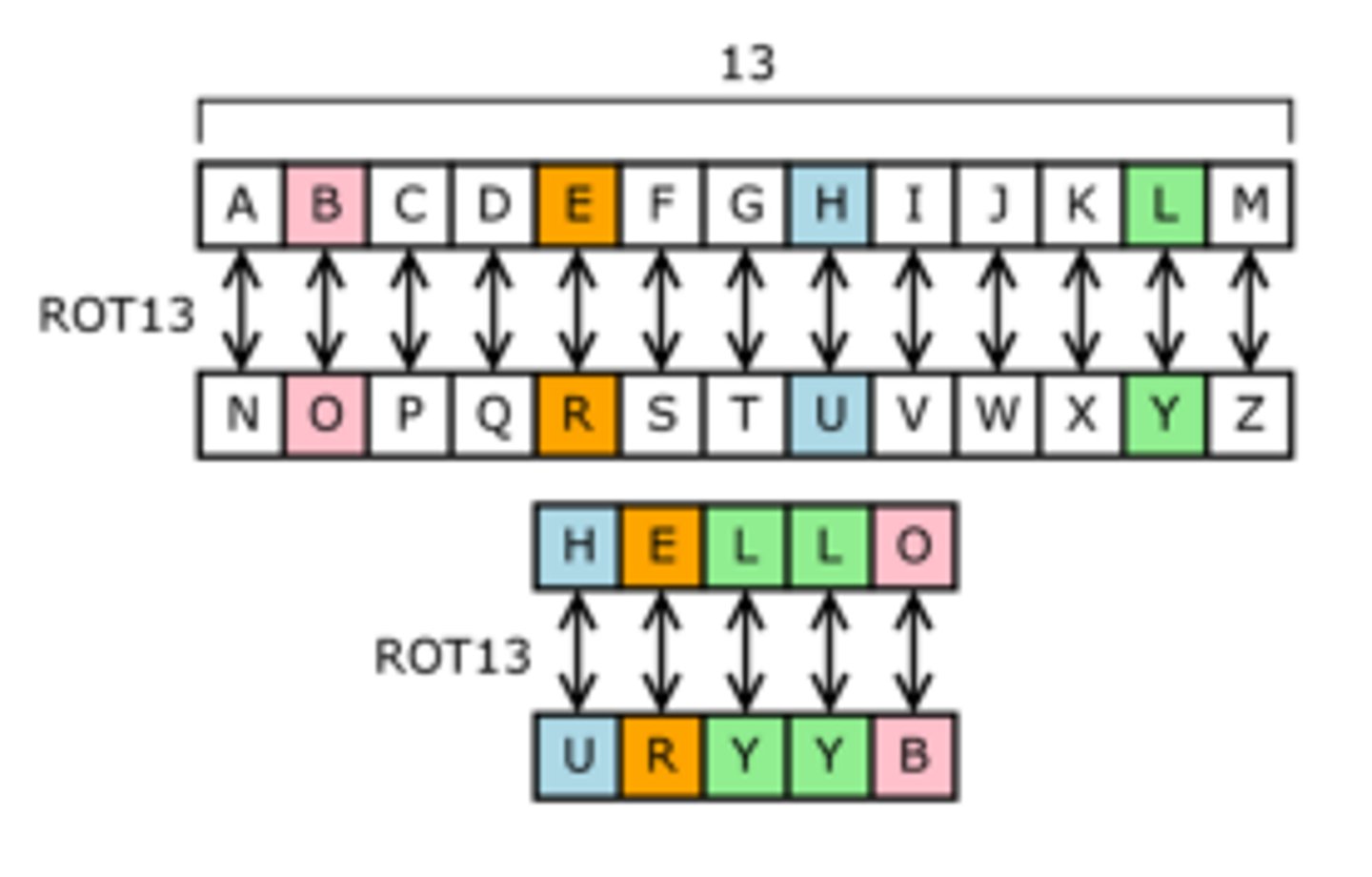
ROT13 cipher
same mechanism as caesar cipher but moves each letter 13 spaces forward in alphabet.
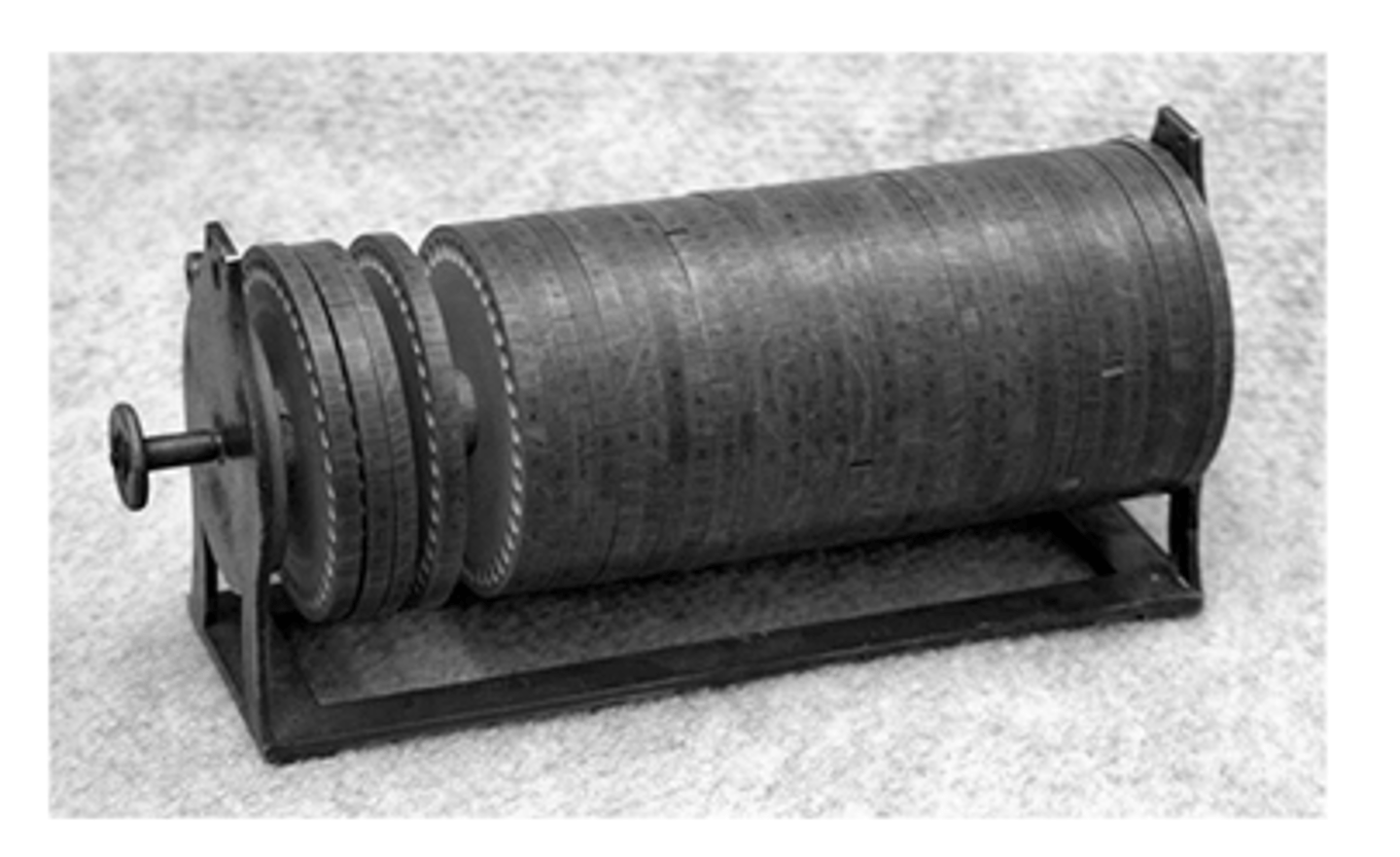
The Jefferson Disk
Invented by Thomas Jefferson in 1795, purely mechanical cryptography machine. composed of 36 disk, marked a-z in a circle around rim
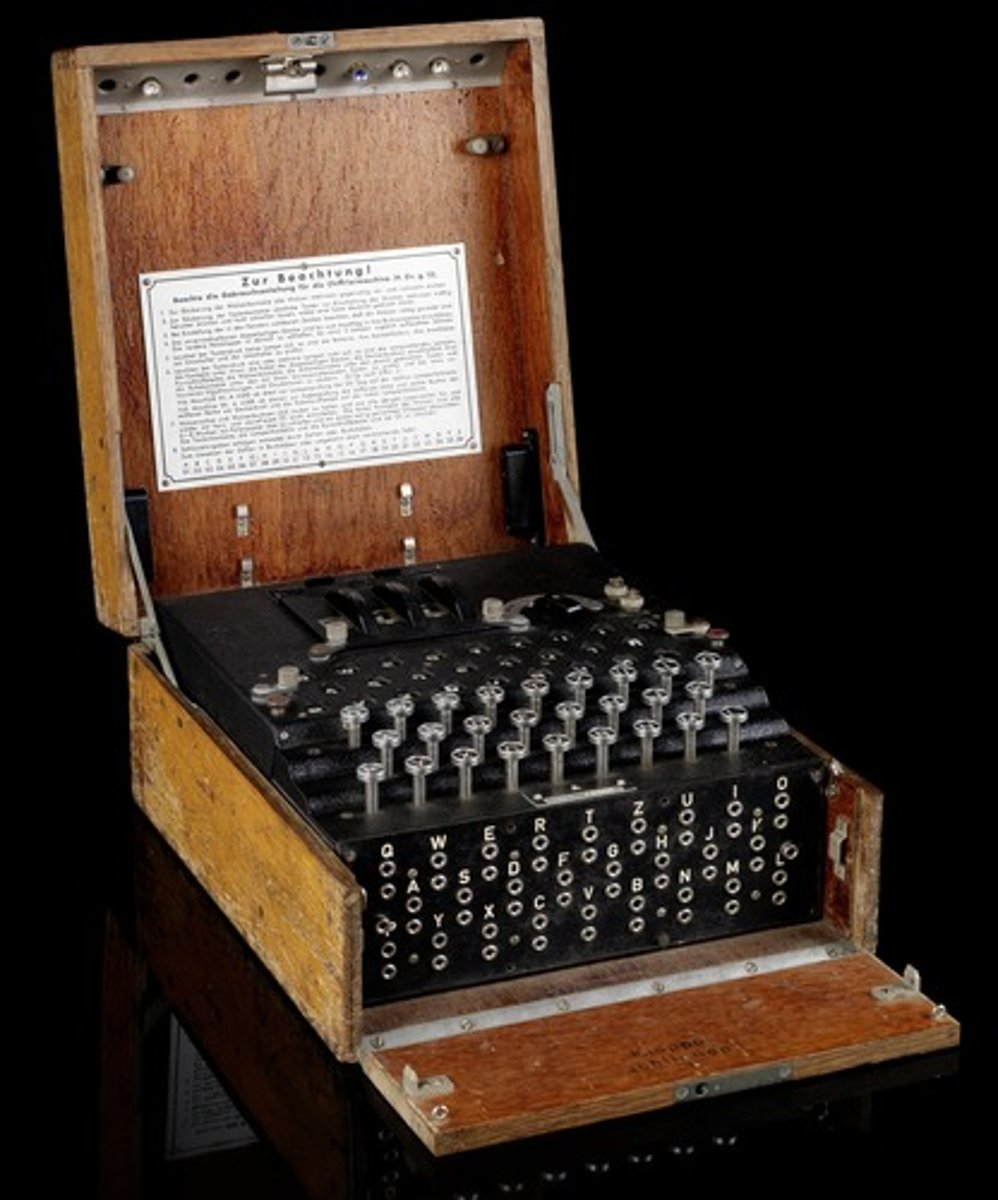
Enigma machine
intricate cryptographic machine created by Arthur Scherbius in 1923. For two Enigma machines to communicate they need to have same configuration. Enigma machine made it difficult for attempting to break messages generated by it.
Keyword Ciphers
substitution ciphers that use a key to determine what to substitute for each letter of the message.
Frequency Analysis
you can make guesses about what message contents might be based on the frequency of characters used
One-time pad
AKA Vernam Cipher. Unbreakable cioher when used properly. To use you create two copies of same pad of paper containing completely random set of #s (shifts) & give one copy to each party. To encrpyt you use the shifts to move each letter of message forward.
Symmetric Cryptography
AKA Private Key cryptography uses single key to both encrypt the plaintext and decrypt the ciphertext. You must share a single key among all users of the system which is chief weakness of symmetric key cryptography.
Key Exchange
Sharing a key between sender & reciever.
Block Cipher (one type of symmetric cryptography)
takes predetermined number of bits (binary digits 0 or 1) known as block & encrpyts the block. Majority of encryption algorithms currently in use are block ciphers. Slower but more versatile than stream ciphers
Stream Cipher
encrypts each bit in the plaintext message one bit at a time. You can make a block cipher as a stream cipher by setting block size to one bit
Block Mode
Defines specific processes and operations that the cipher uses
DES
first came in 1976 in the USA & since spread globally. block cipher that uses 56 bit key.
3DES
DES used to encrypt each block 3 times with 3 different keys
AES
set of symmetric block ciphers that replaced DES. Uses 3 different ciphers. one with 128 bit key, one with 192 bit key, and one with 256 bit key, all of which encrypt blocks of 128 bits
asymmetric key cryptography
AKA public key cryptography uses two keys: public key & private key. Public key is used to encrpyt data & anyone can access. Private keys are used to decrypt messages & are guarded.
RSA algorithm
an asymmetric key algorithm used across the world, named after creators Ron Rivest, Adi Shamir & Leonard Adleman
Elliptic Curve Cryptography (ECC)
class of cryptographic algorithms with several advantages. Can use short keys while maintaining a higher cryptographic strength. Fast & efficient type of algorithm that allows easy implementation on hardware/ less processing power & memory.
PGP
Created by Phil Zimmerman was on of first strong encryption tools to reach public eye. Created in 1900, & a symmetric algorithm, could be used to secure data such as communications & files. at time of release, was regulated by (ITAR)
Hash Functions
3rd type of modern cryptography AKA keyless cryptography. Converts the plaintext into a largely unique and fixed-length value called hash
PKI (public key infrastructure)
usually has 2 main components: the certificate autorities that issuue and verify certificates and the registration authorities that verify identity of individual associate. Can revoke certificates if they reach their expiration date.
Digital Signatures
an extension of hash functions to an identity so that you can ensure an excrypted message really represents communication from a particular individual.